Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
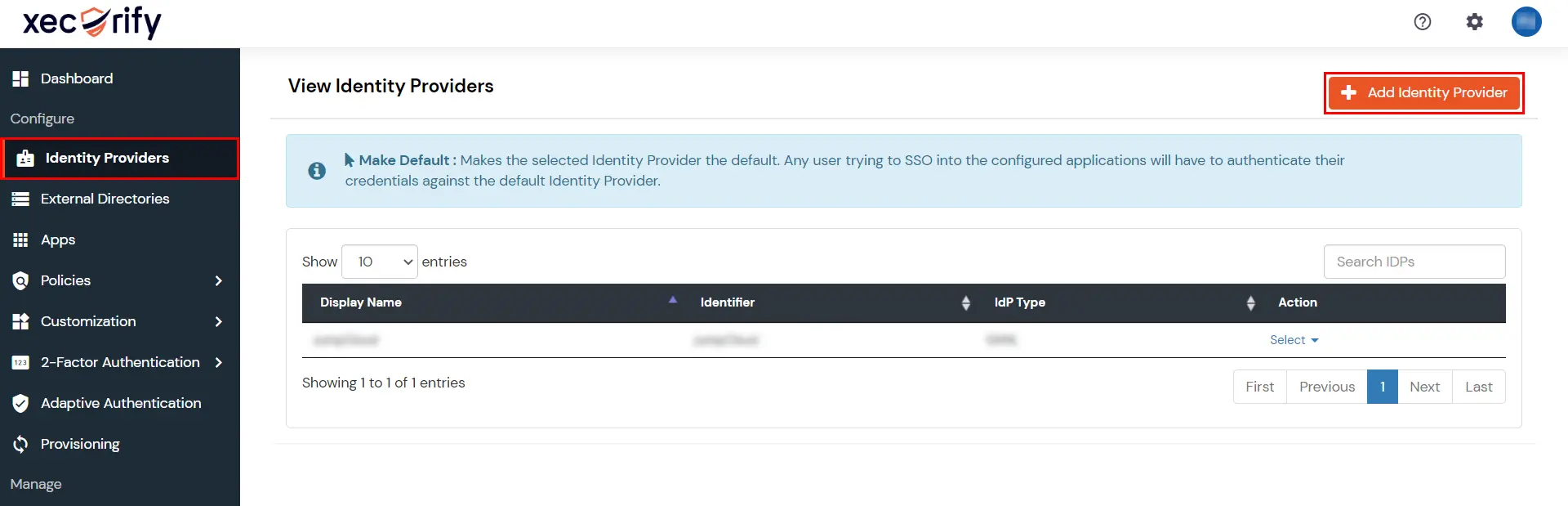
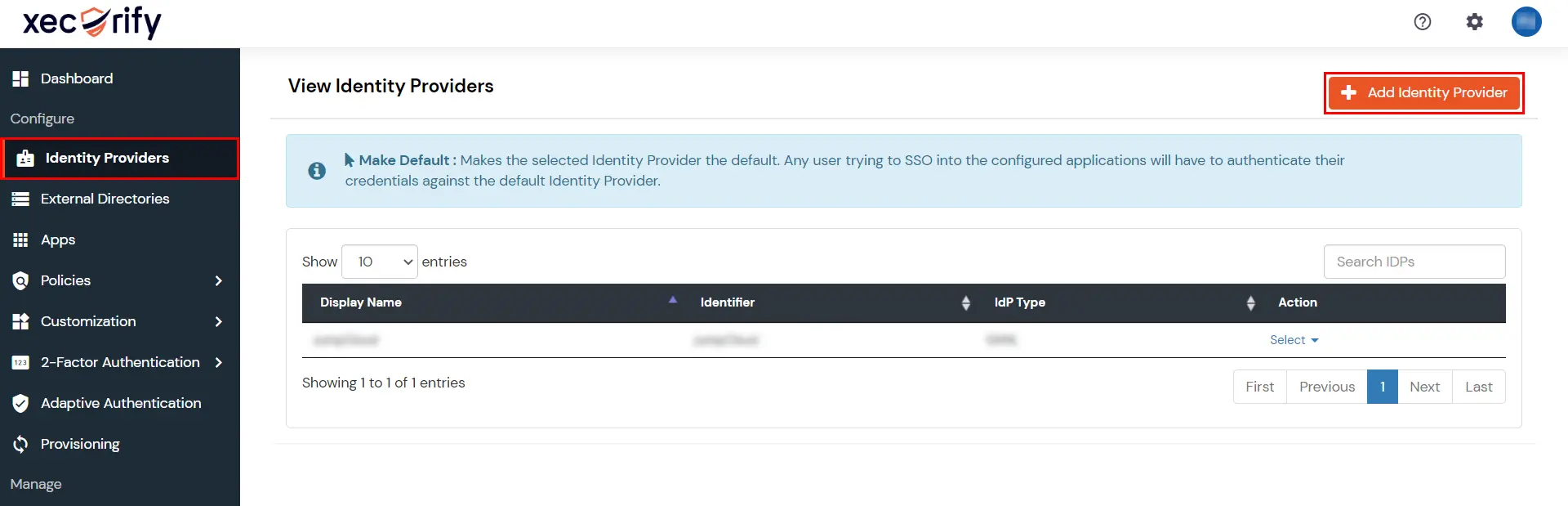
×Configure Okta as an IDP for Single Sign-On (SSO) login into your application. miniOrange offers a pre-built solution for integrating Okta Single Sign On (SSO), making it easy to implement. Here Okta will act as an Identity Provider (IDP) and miniOrange will act as a broker, and other multiple applications will act as Service Provider (SP). Enabling SSO for your domain within help of miniOrange allows your Users to easily and securely log in to their accounts.
Whereas, you can setup Okta as SAML IdP to Single Sign-On into apps that support protocols like OAuth, OpenID Connect, JWT, etc. Our Identity Broker service enables cross protocol authentication.
miniOrange offers free help through a consultation call with our System Engineers to configure SSO for different apps using OpenAthens as IDP in your environment with 30-day free trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you in no time.
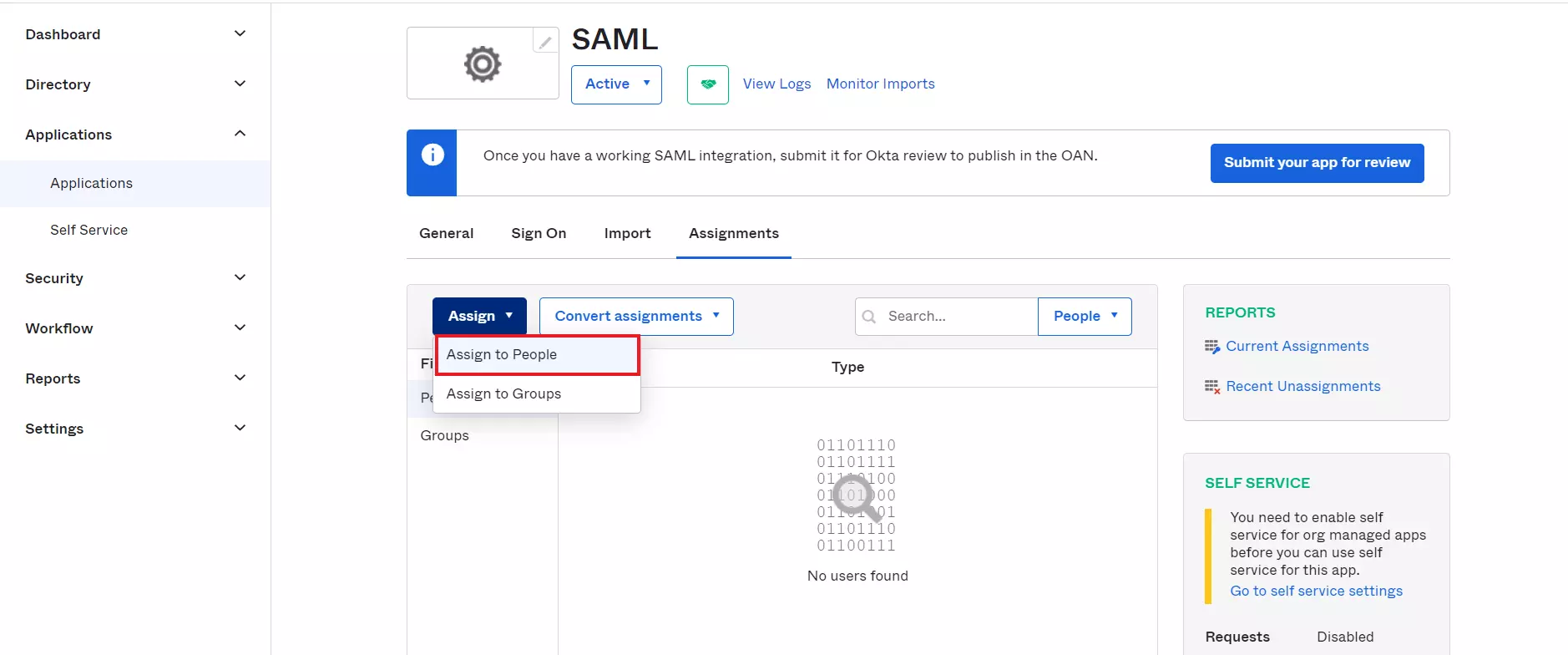
Mentioned below are steps to configure Okta as IDP via SAML and OAuth configuration. Follow the steps accordingly based on your requirement (SAML or OAuth).
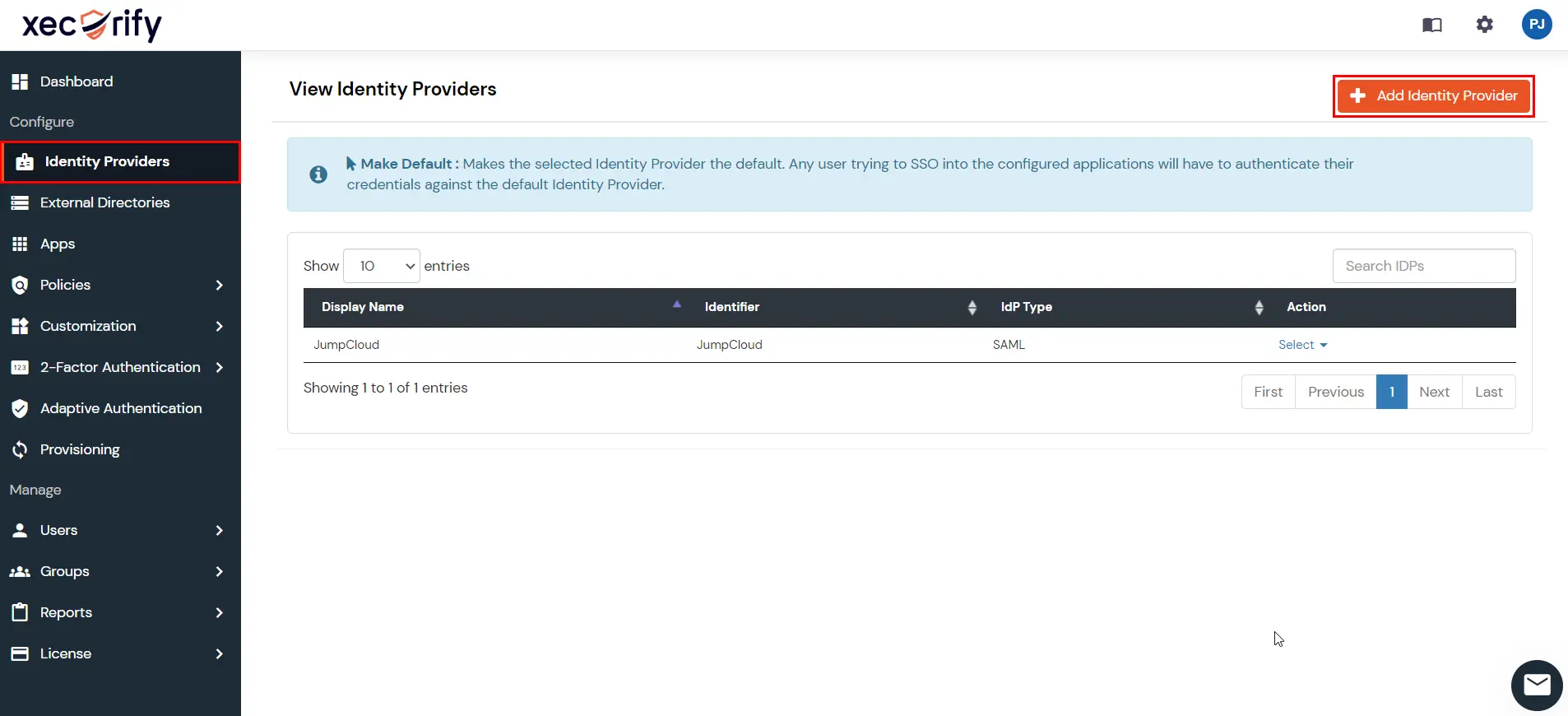
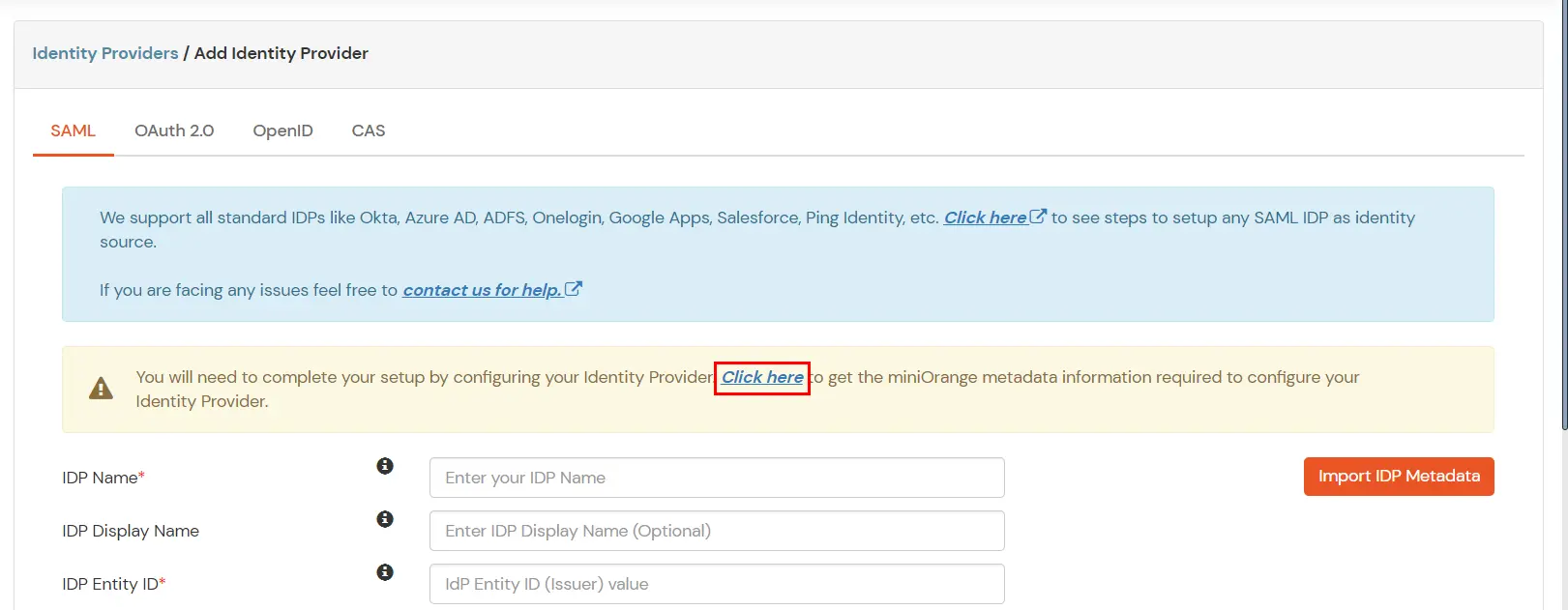
Follow the steps to configure Okta as SAML IdP configuration.
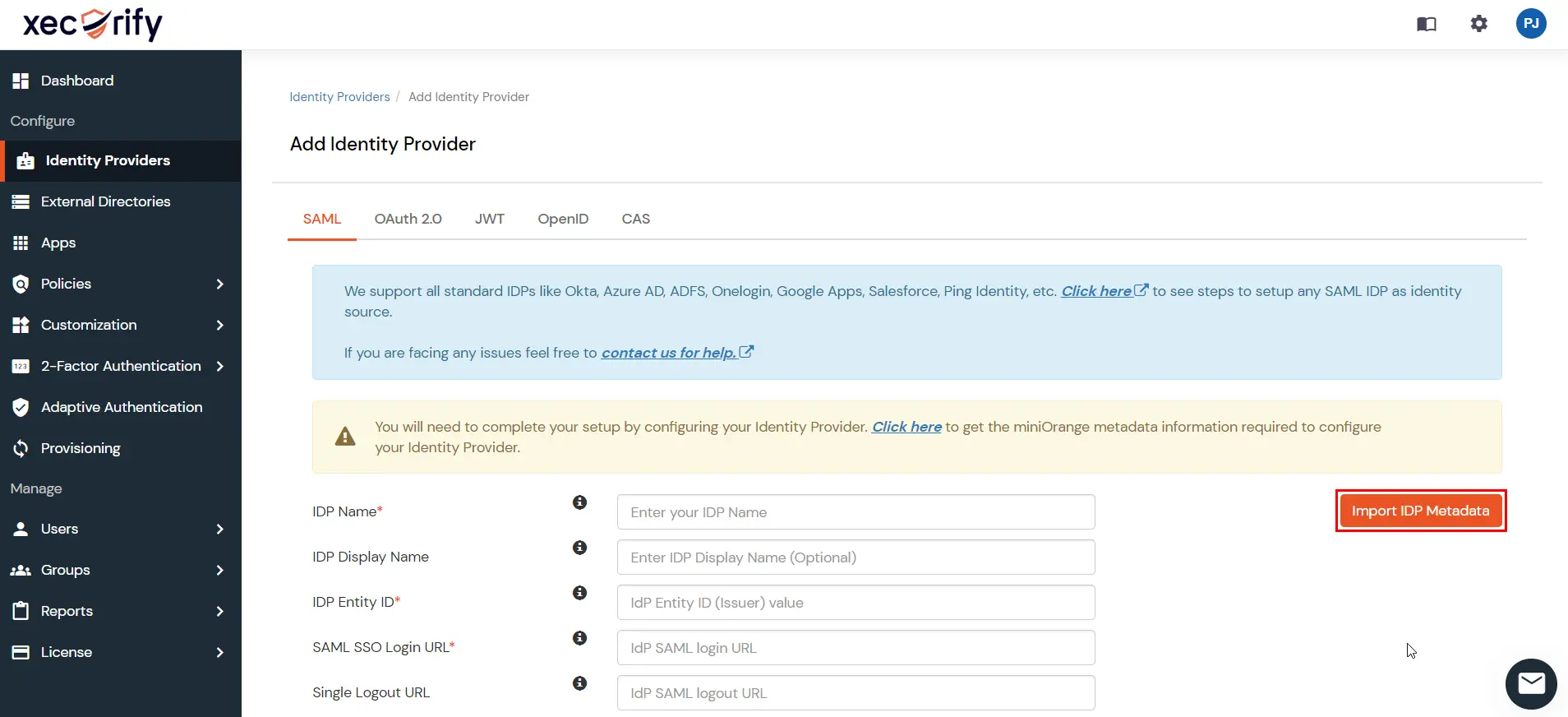
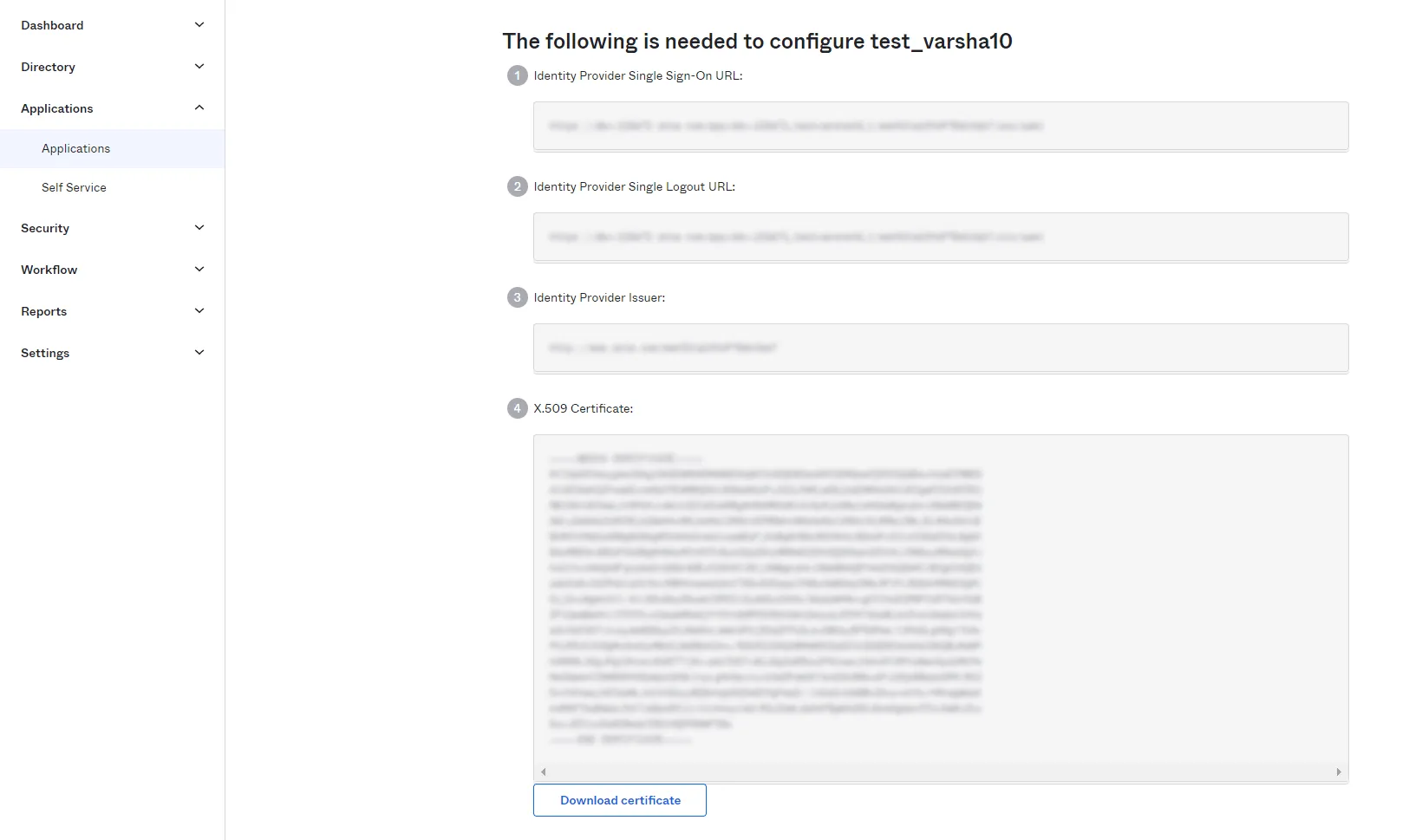
| IdP Entity ID | Identity Provider Issuer from Okta |
| SAML SSO Login URL | Identity Provider Single Sign-On URL from Okta |
| X.509 Certificate | X.509 Certificate from Okta |
| Single Logout URL [Optional] | Single Logout URL from Okta |
| Domain Mapping | Can be used to redirect specific domain user to specific IDP |
| Show IdP to Users | Enable this if you want to show this IDP to all users during Login |
| Send Configured Attributes | Enabling this would allow you to add attributes to be sent from IDP |
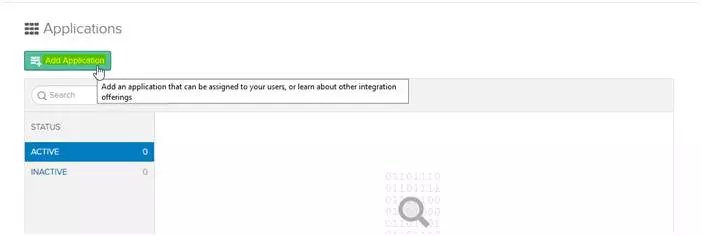
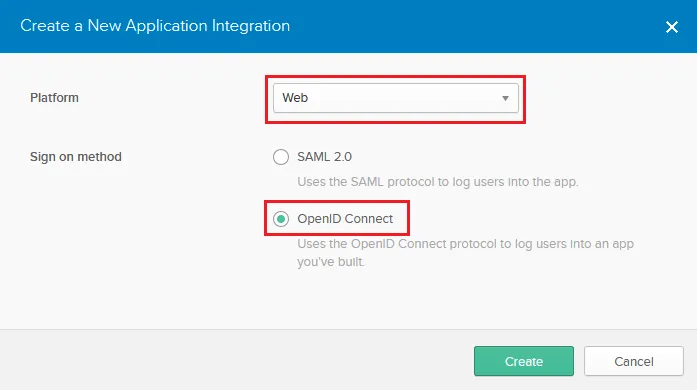
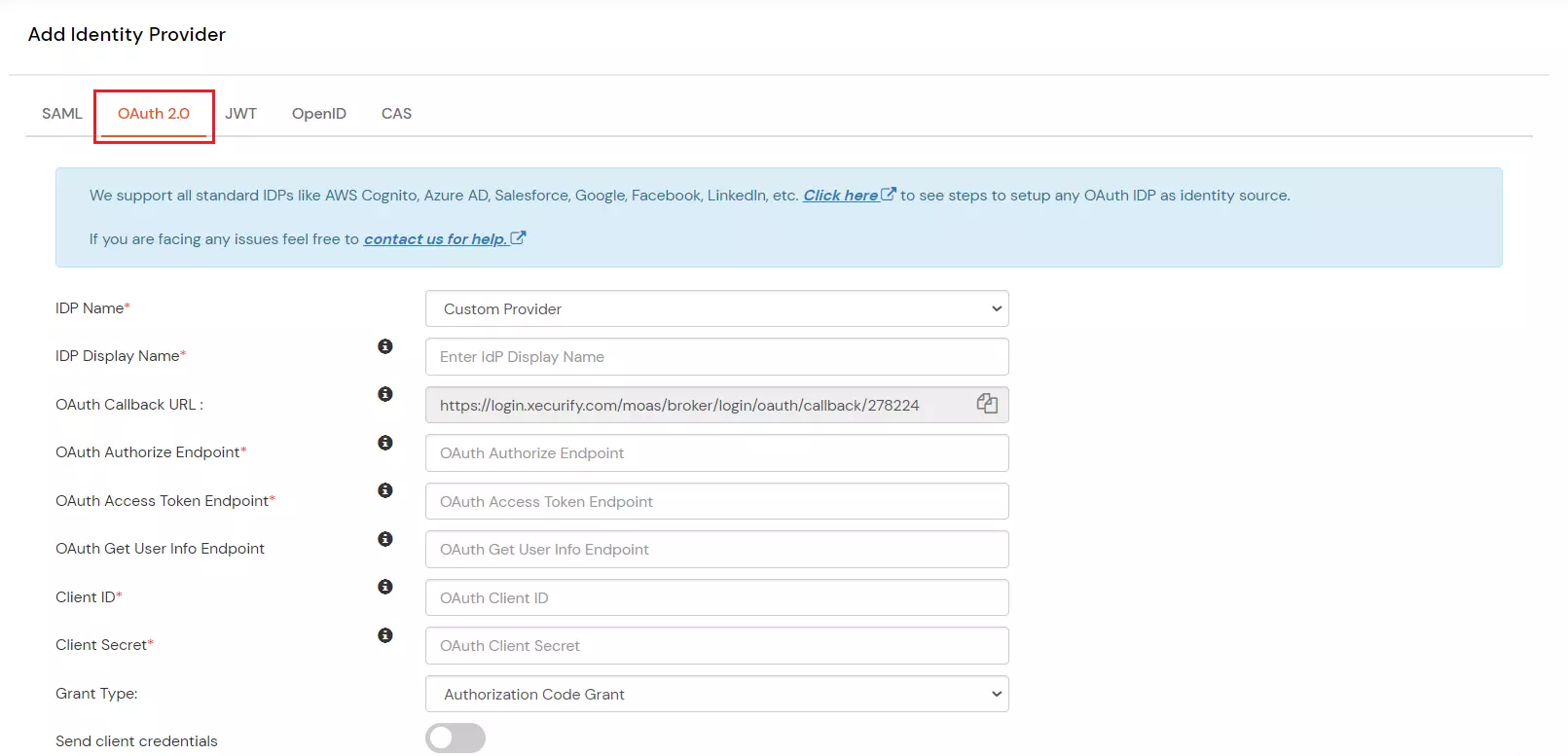
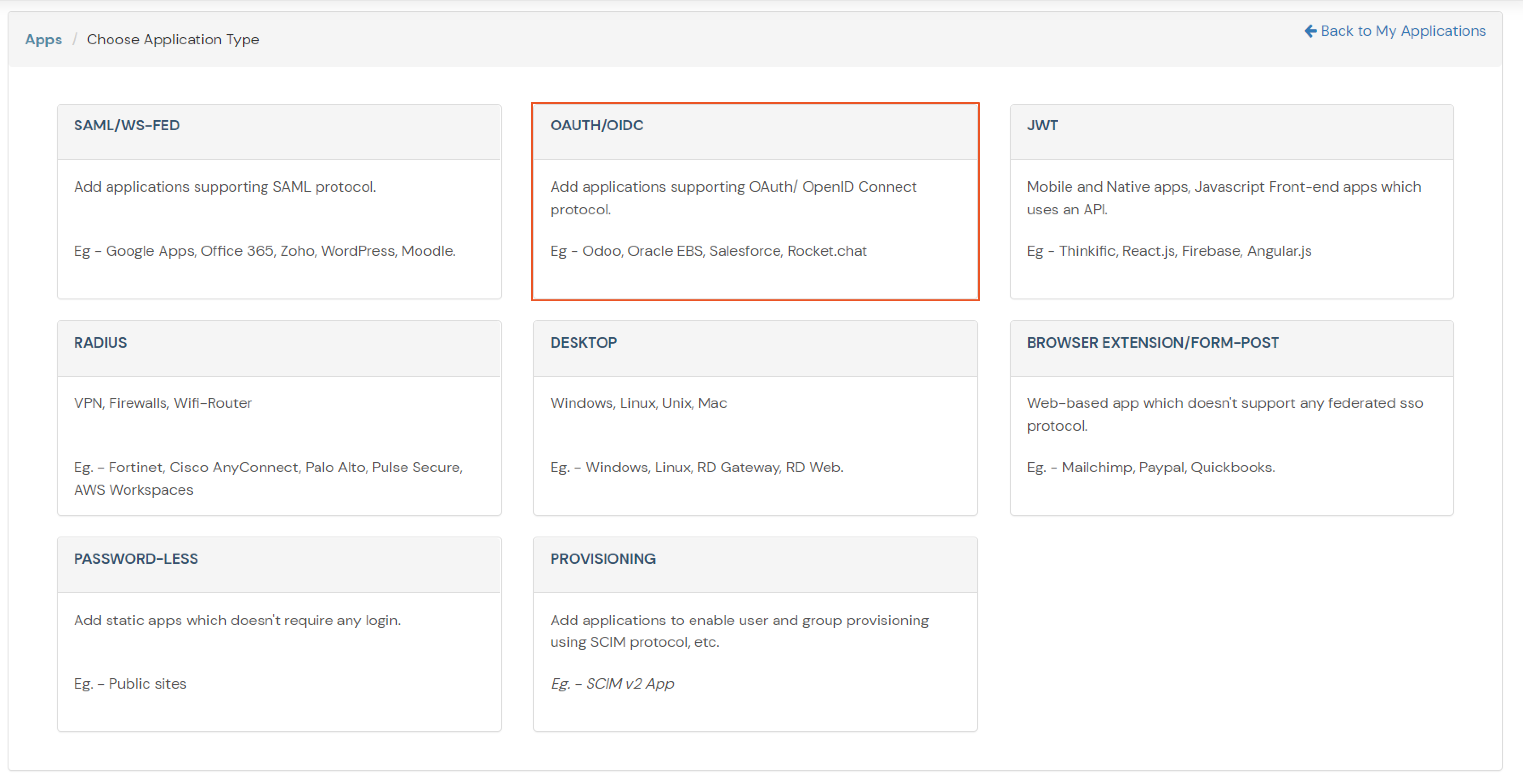
Follow the steps to configure Okta as IdP by OAuth configuration.
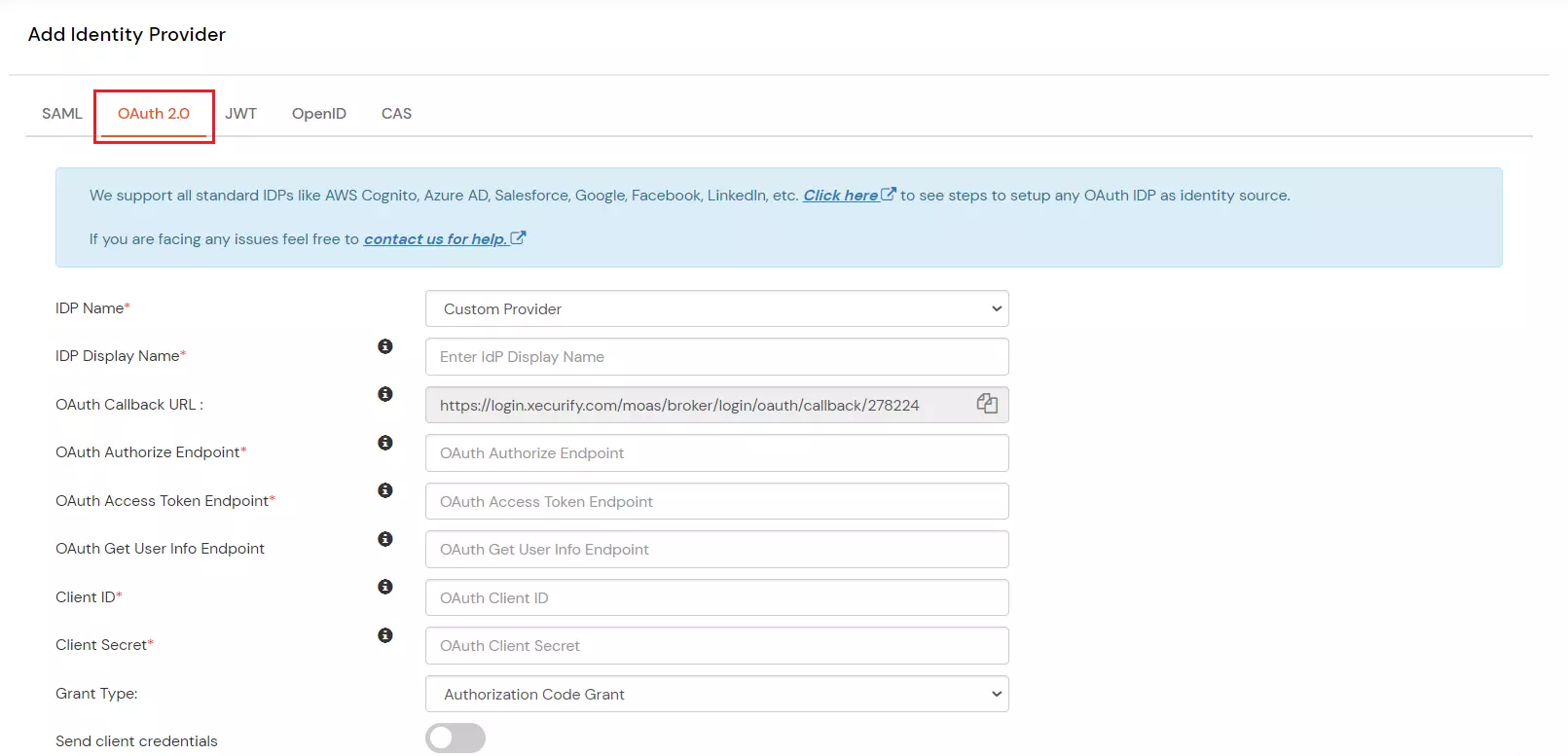
| IdP Name | Custom Provider |
| IdP Display Name | Choose appropriate Name |
| OAuth Authorize Endpoint | https://{yourOktaDomain}.com/oauth2/default/v1/authorize | OAuth Access Token Endpoint | https://{yourOktaDomain}.com/oauth2/default/v1/token | OAuth Get User Info Endpoint | https://{yourOktaDomain}/oauth2/default/v1/userinfo |
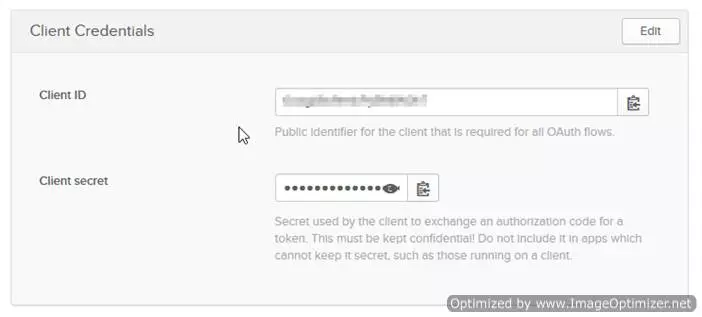
| Client ID | From step 2 |
| Client secret | From step 2 |
| Scope | openid profile email |
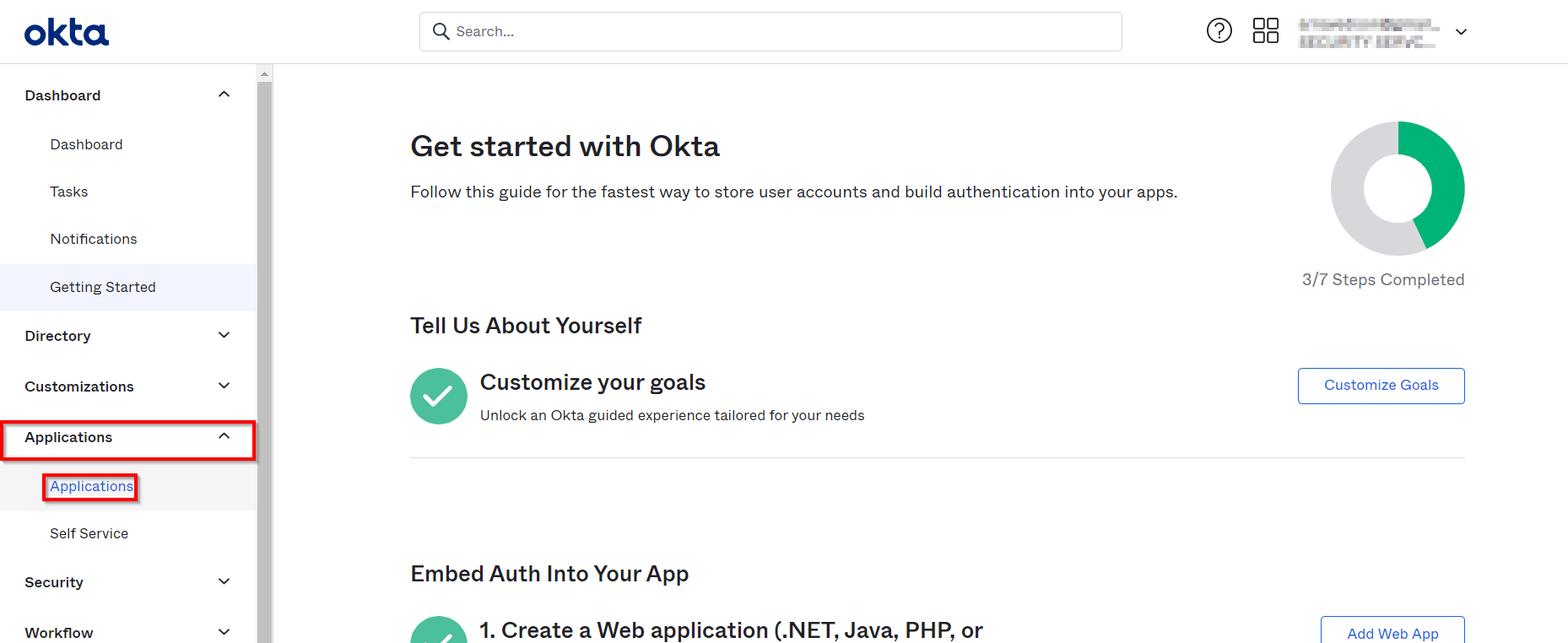
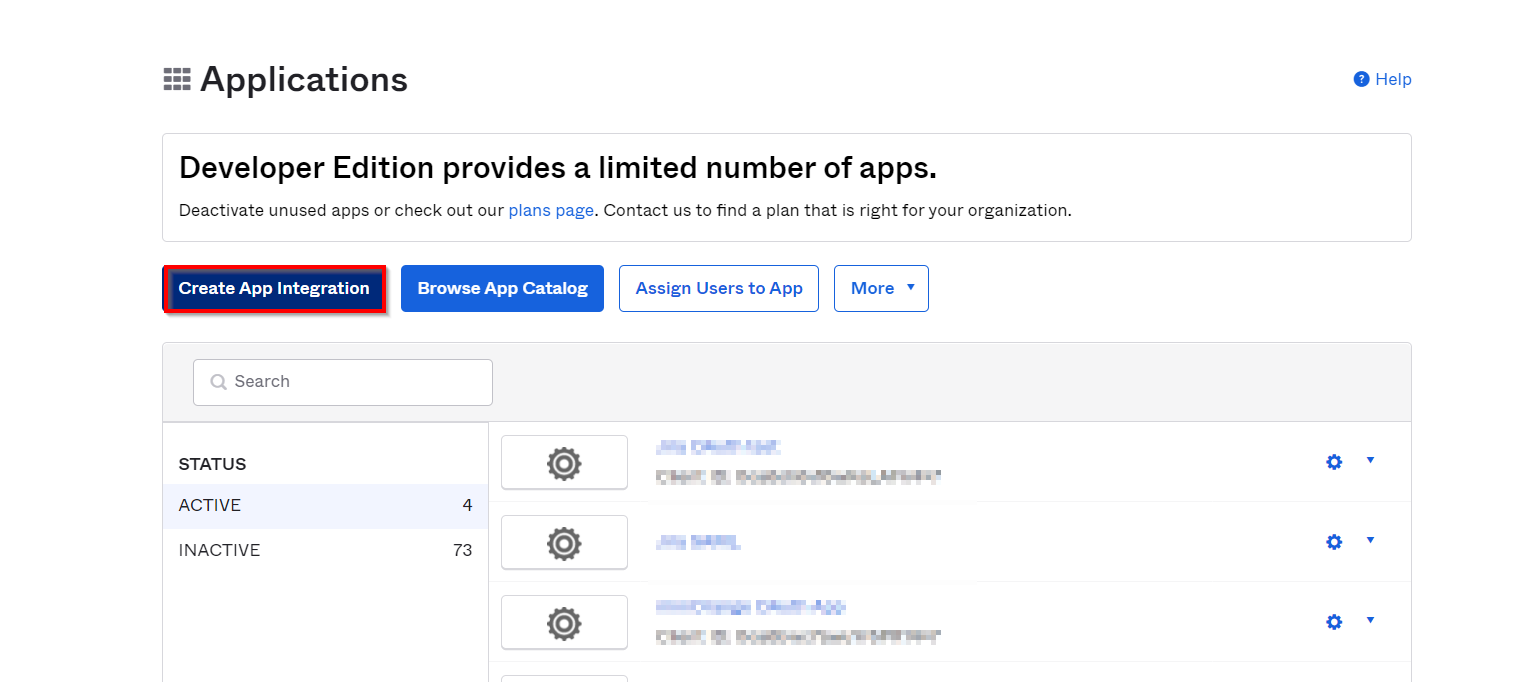
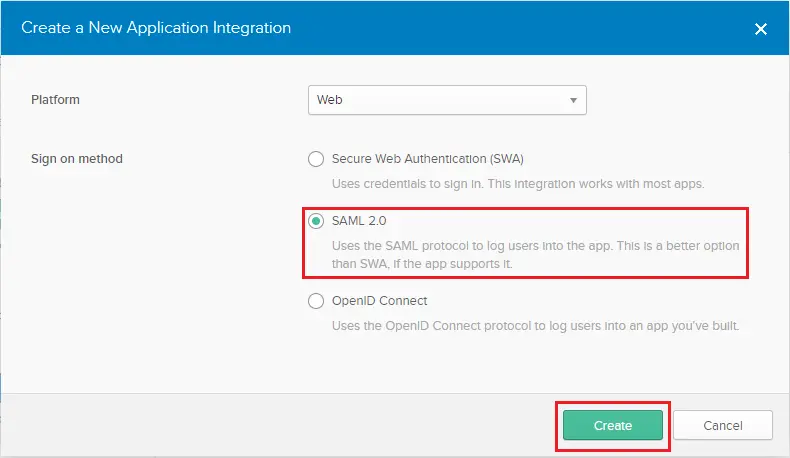
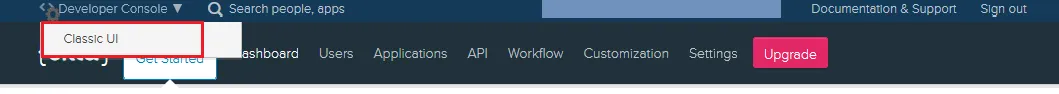
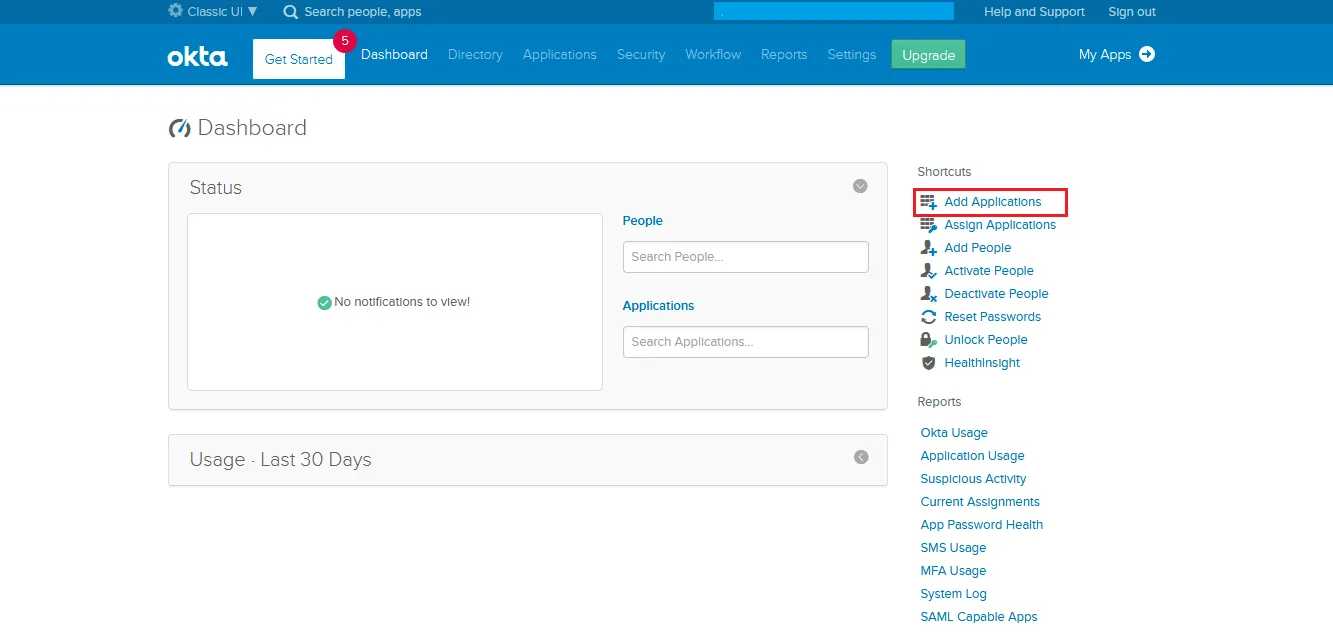
Note: Switch to Classic UI from Okta Developer Console, by selecting the Admin from the upper right corner then Developer Console > Classic UI
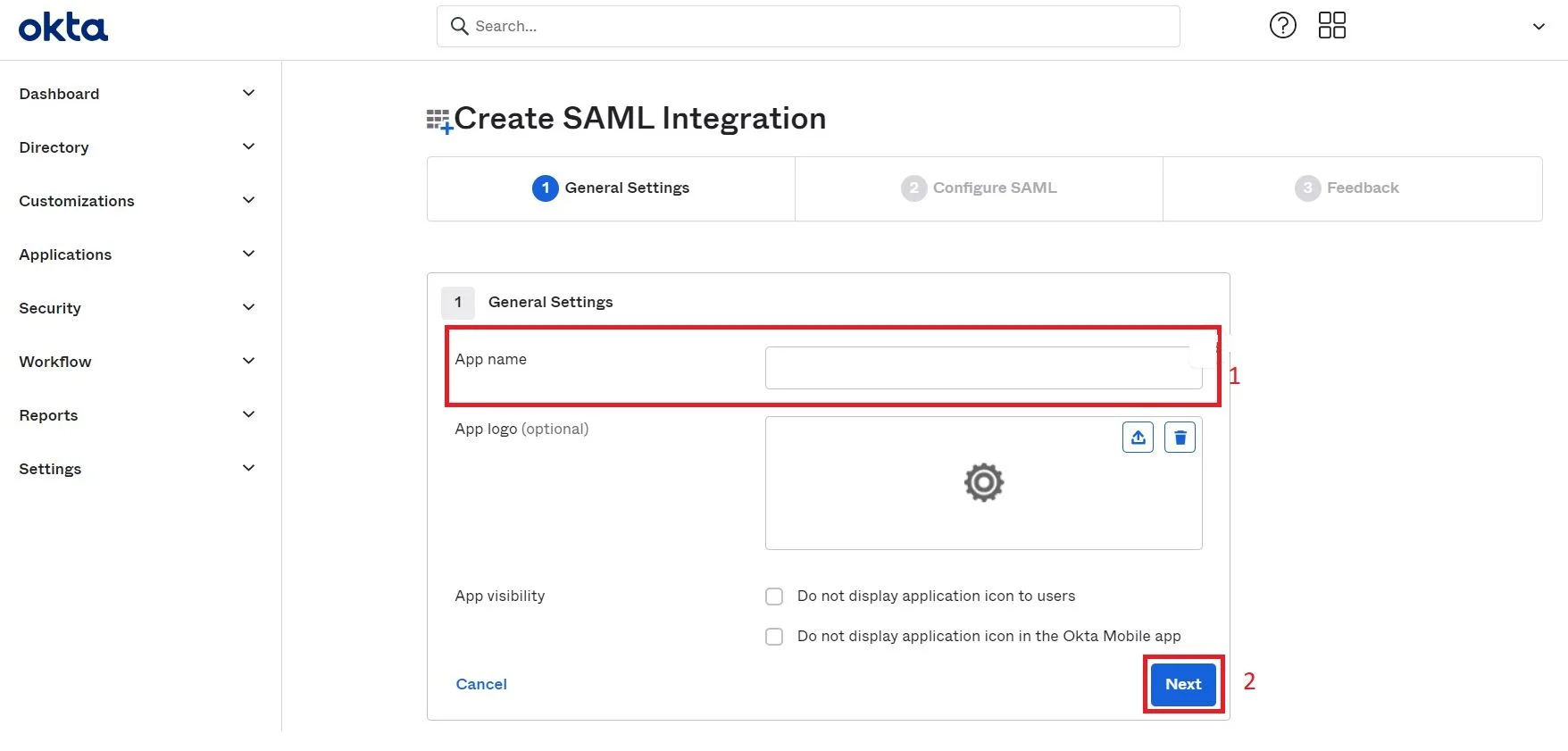
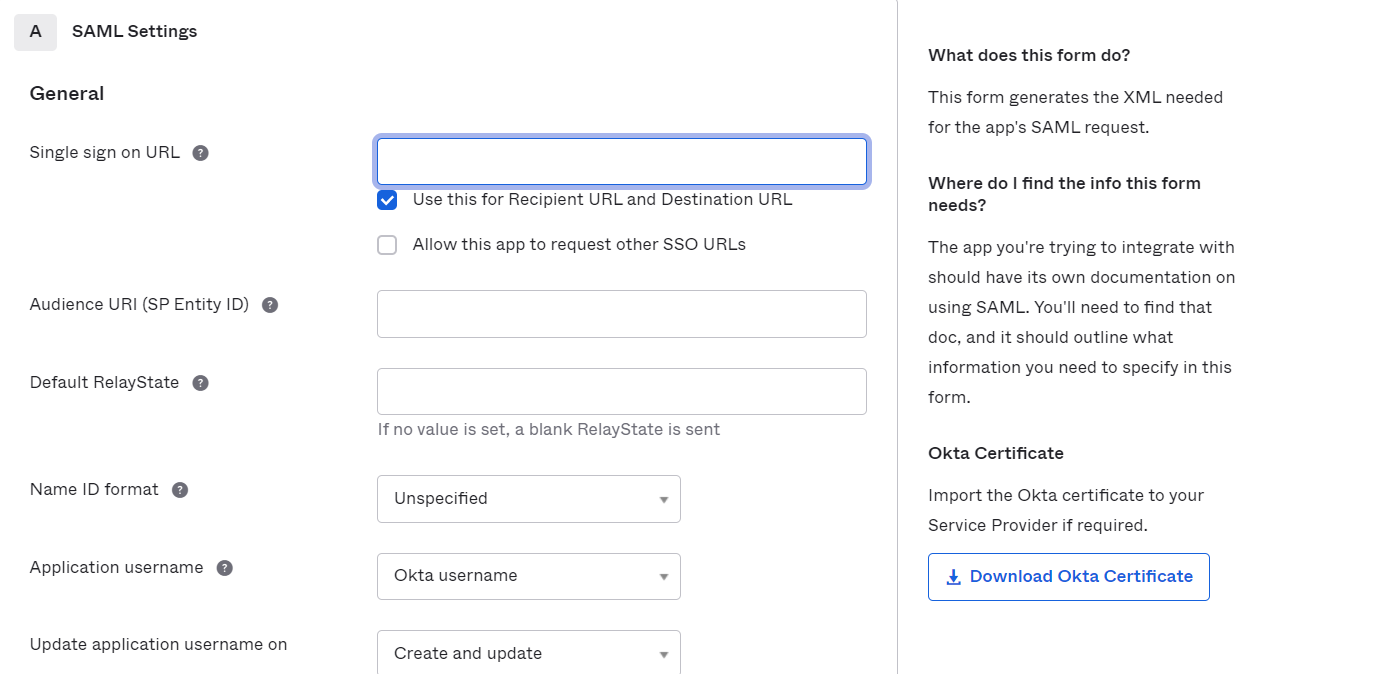
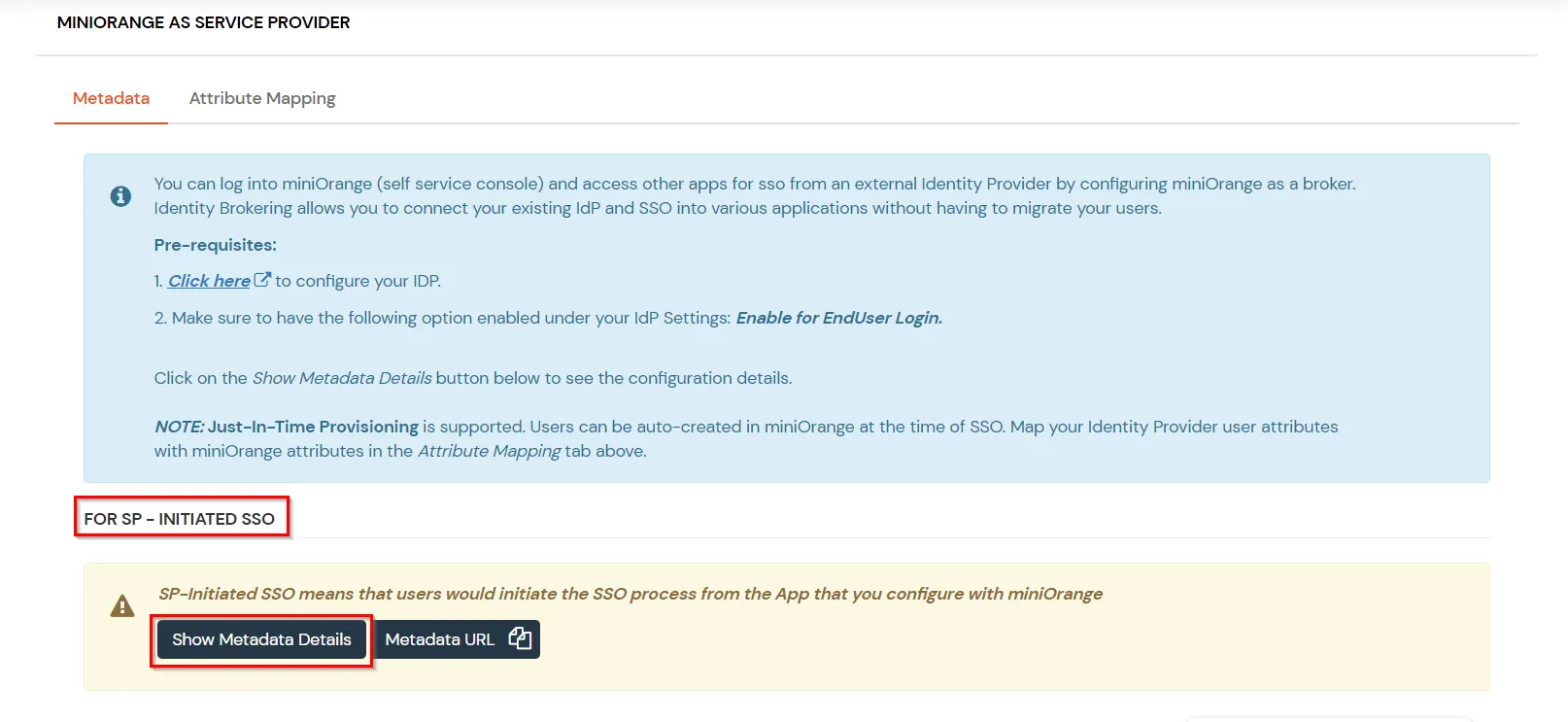
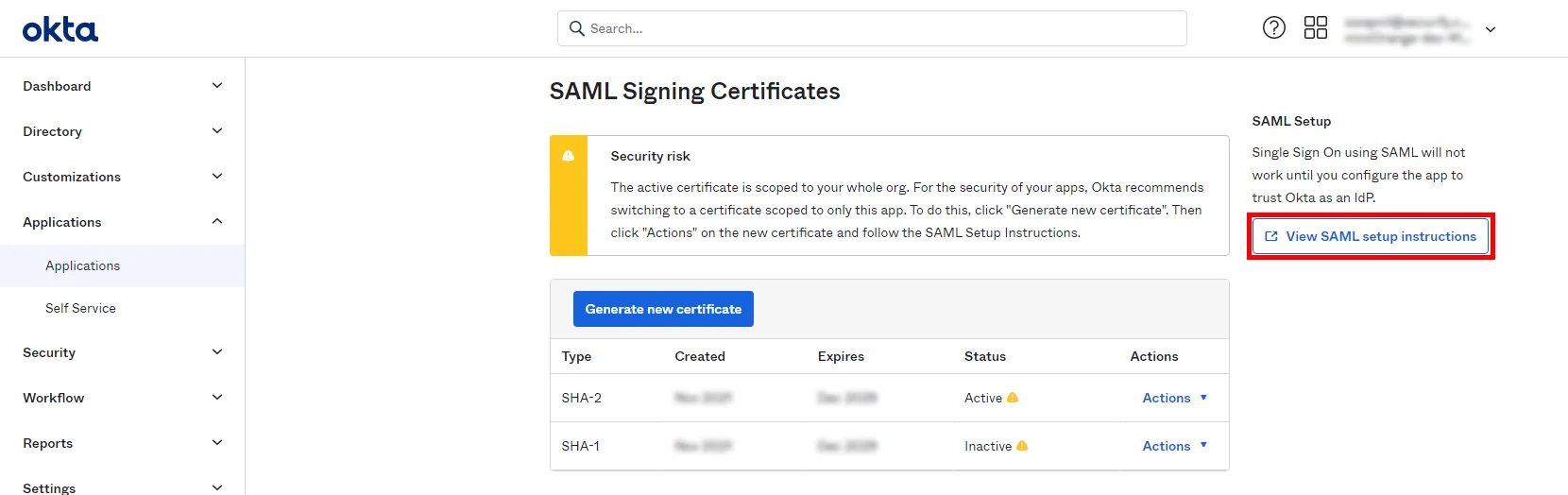
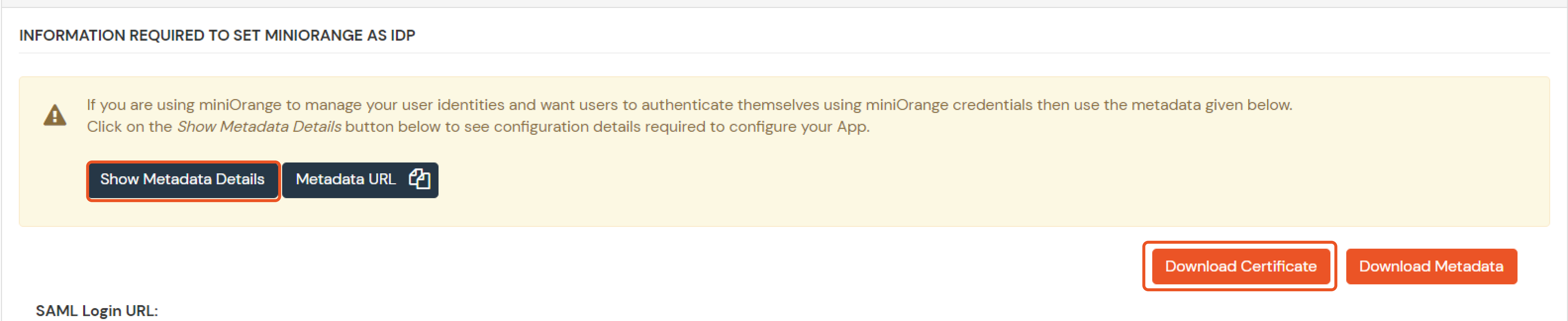
| Single sign on URL | ACS URL |
| Audience URI (SP Entity ID) | Entity ID or Issuer |
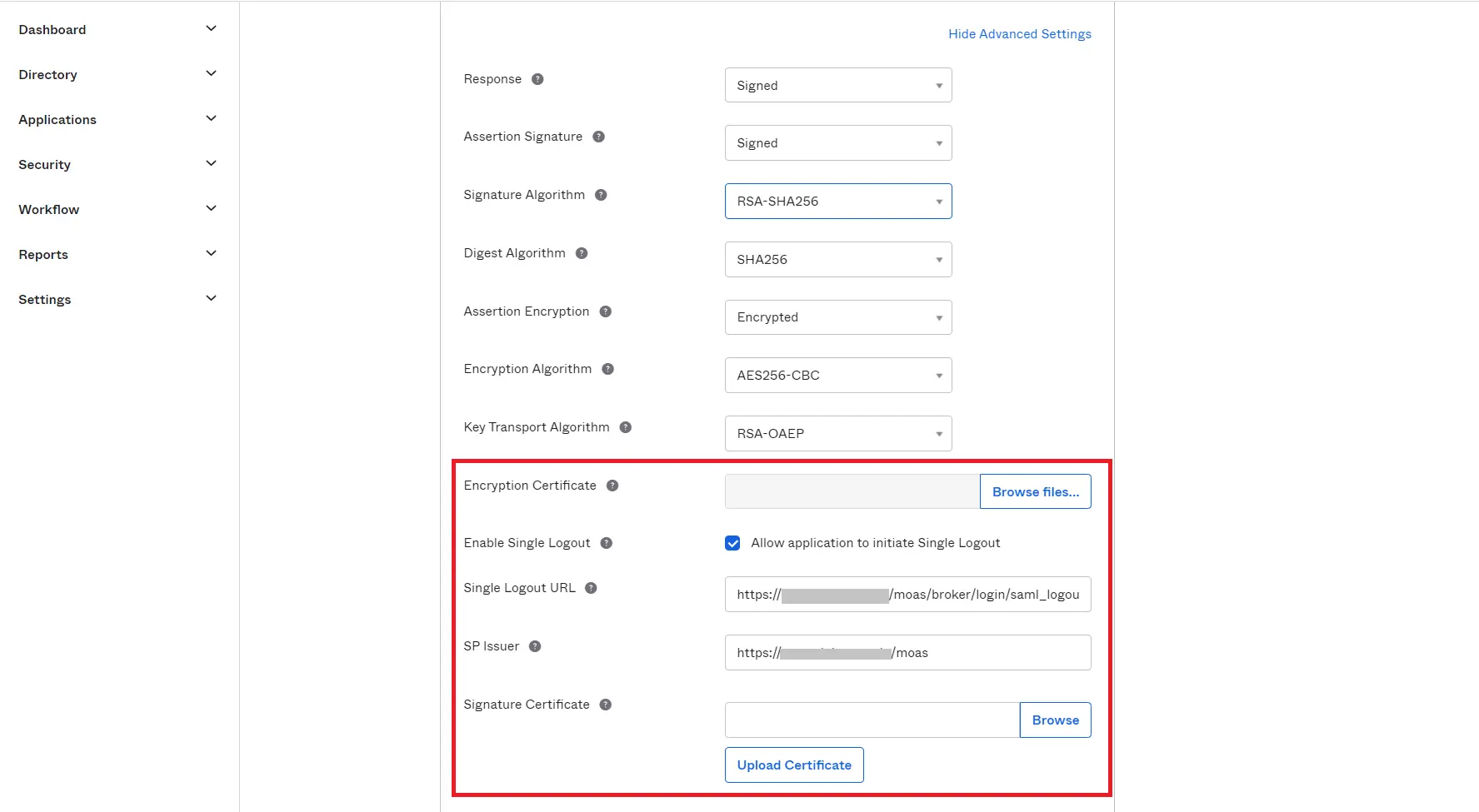
| Encryption Certificate | This is optional |
| Enable Single Logout | Enable the check box to Allow application to initiate Single Logout |
| Single Logout URL | Single Logout URL as mentioned in the Metadata Section |
| SP Issuer | Entity ID or Issuer as mentioned in the Metadata Section |
| Signature Certificate | X.509 Certificate can be downloaded from the Metadata Section |
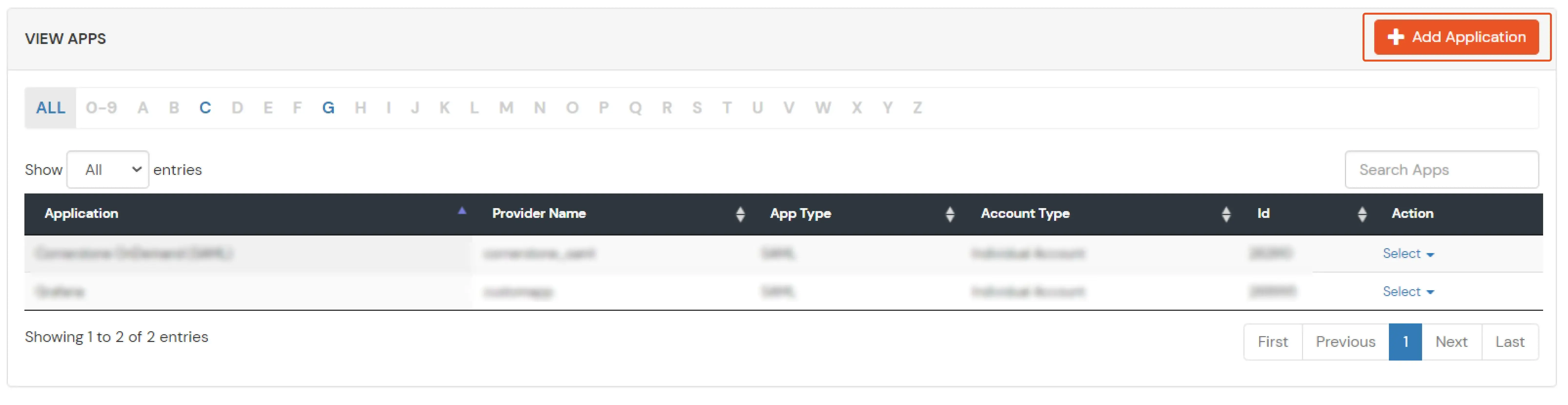
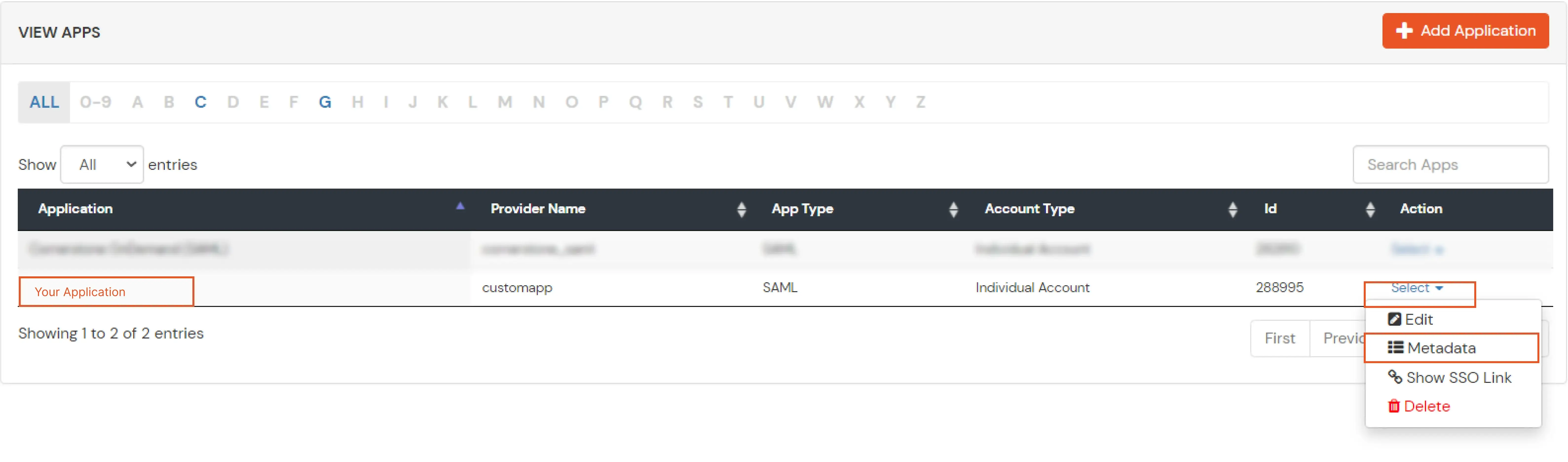
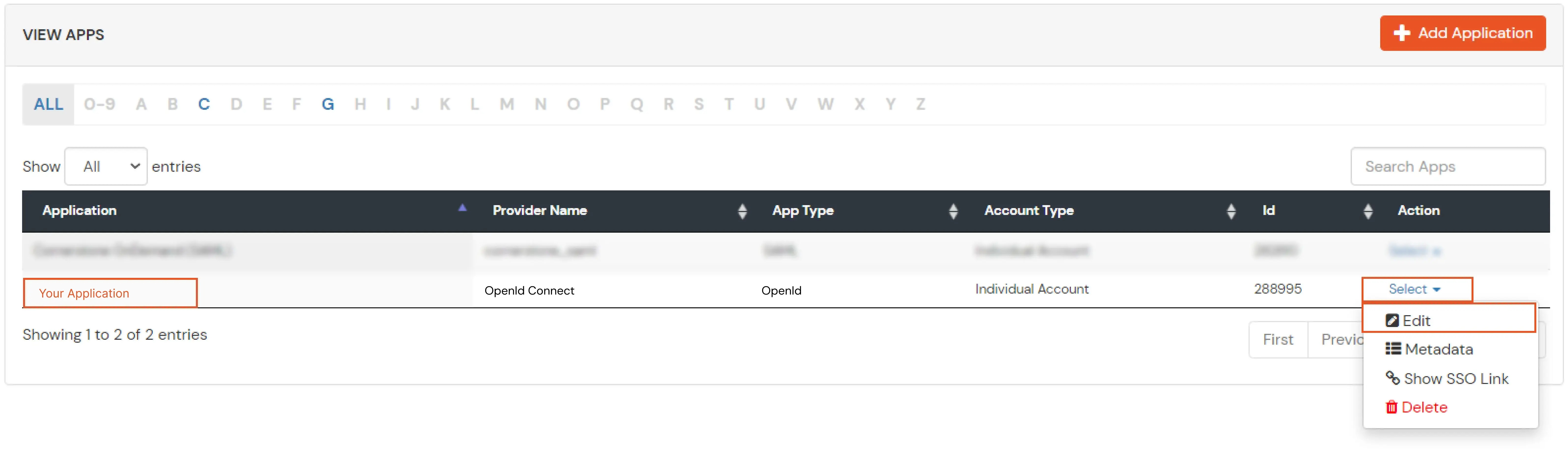
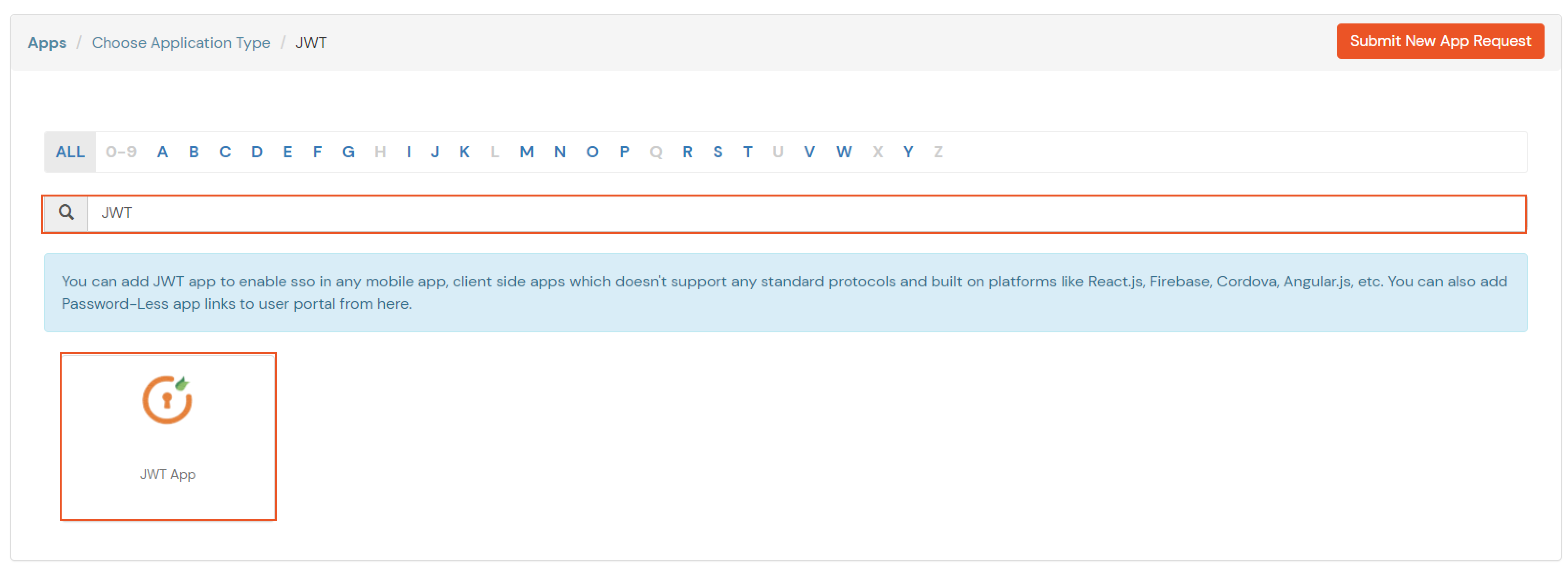
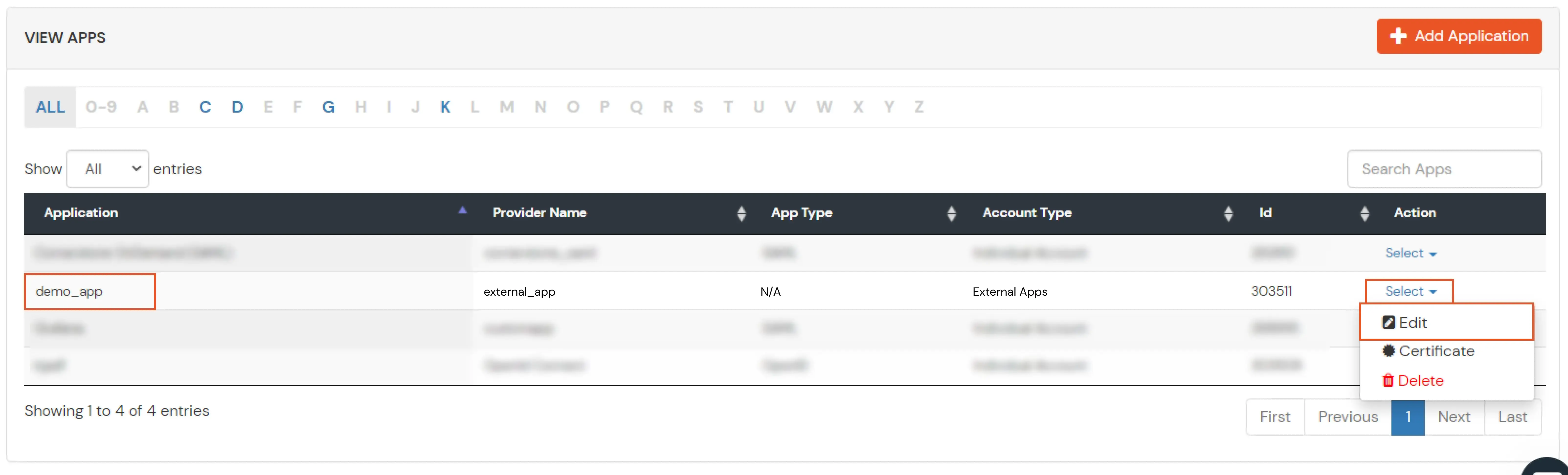
If you have already configured your application in miniOrange you can skip the following steps.
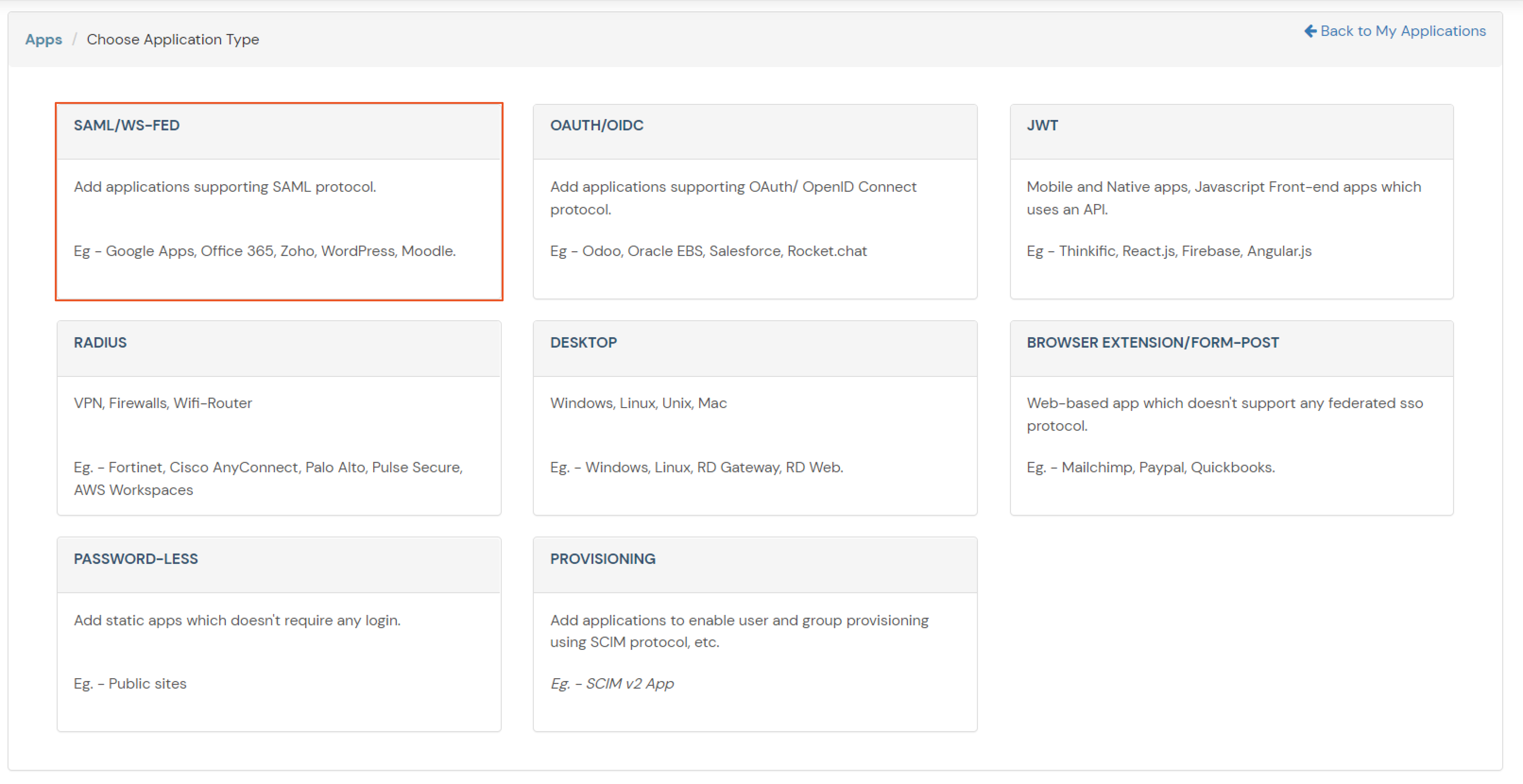
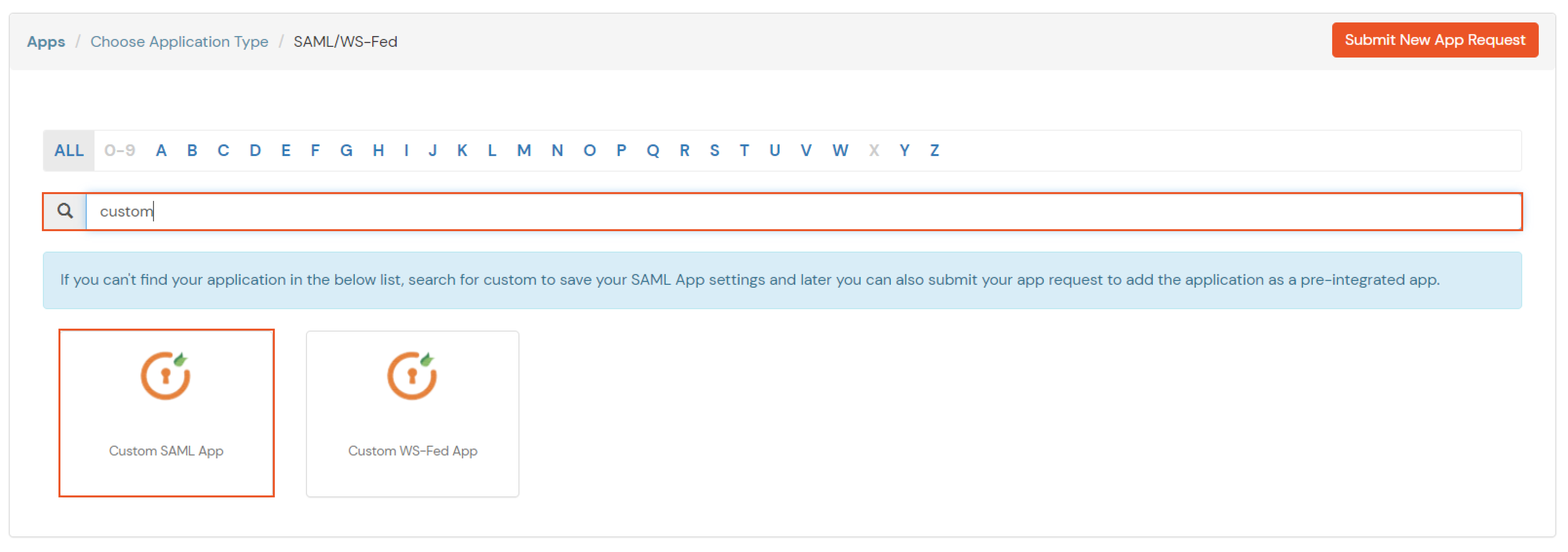
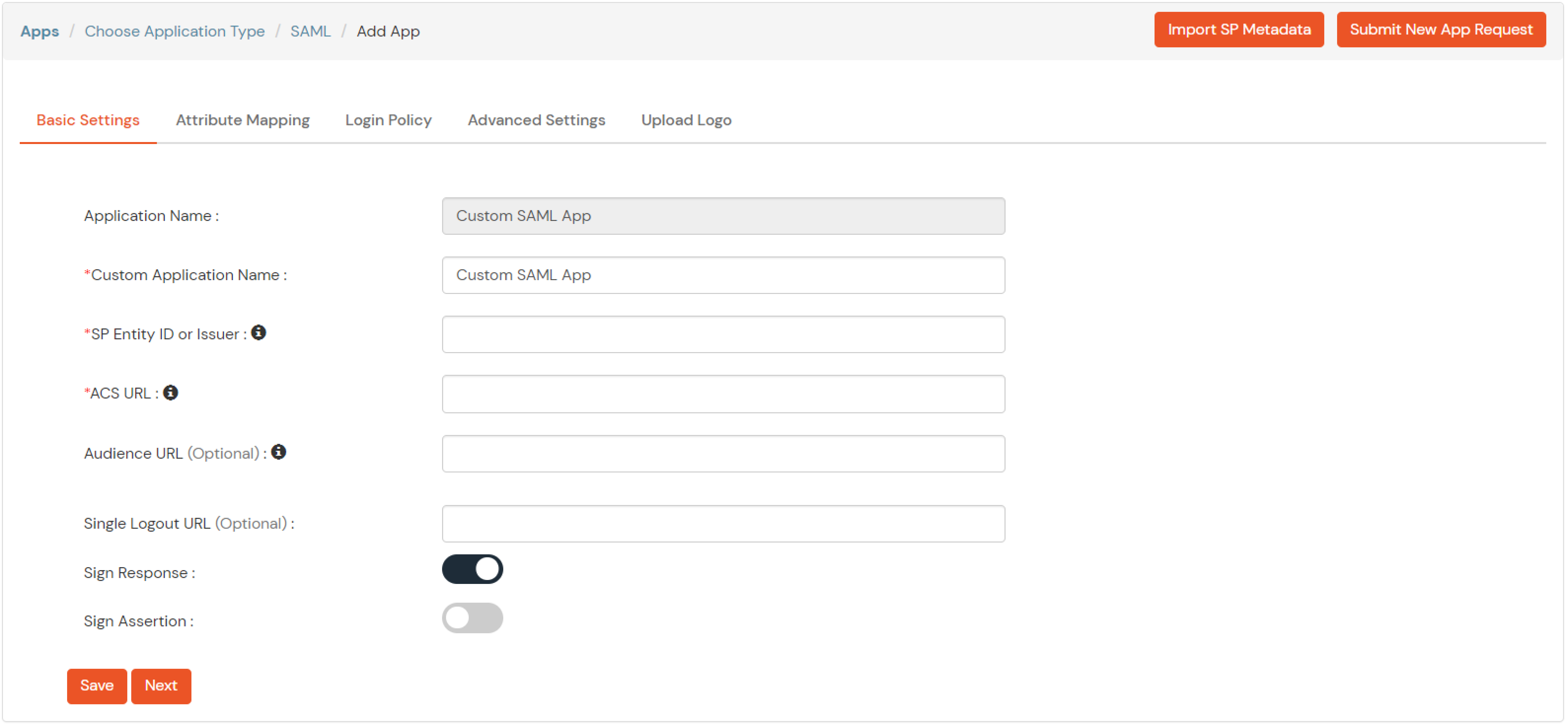
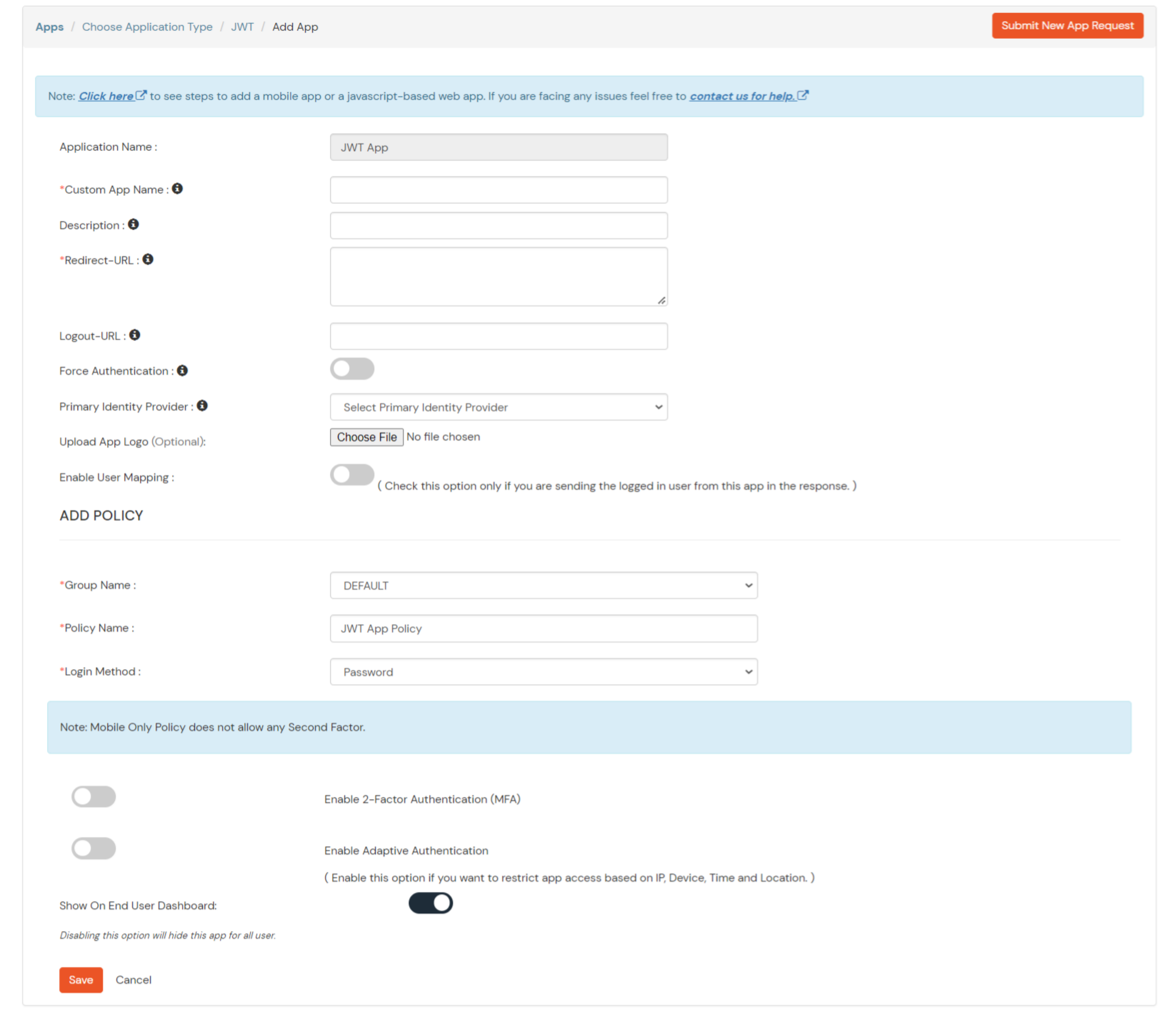
| Service Provider Name | Choose appropriate name according to your choice |
| SP Entity ID or Issuer | Your Application Entity ID |
| ACS URL X.509 Certificate (optional) | Your Application Assertion Consumer Service URL |
| NameID format | Select urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress |
| Response Signed | Unchecked |
| Assertion Signed | Checked |
| Encrypted Assertion | Unchecked |
| Group policy | Default |
| Login Method | Password |
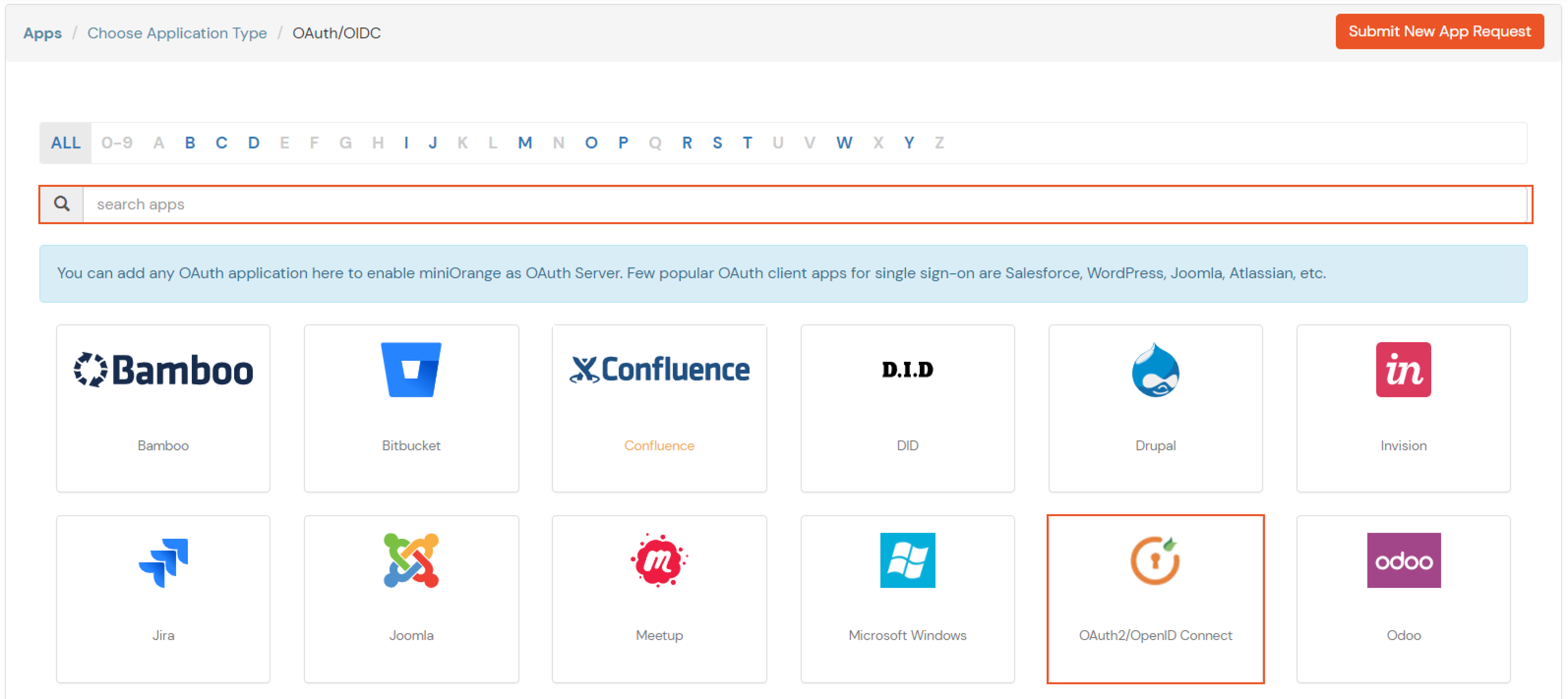
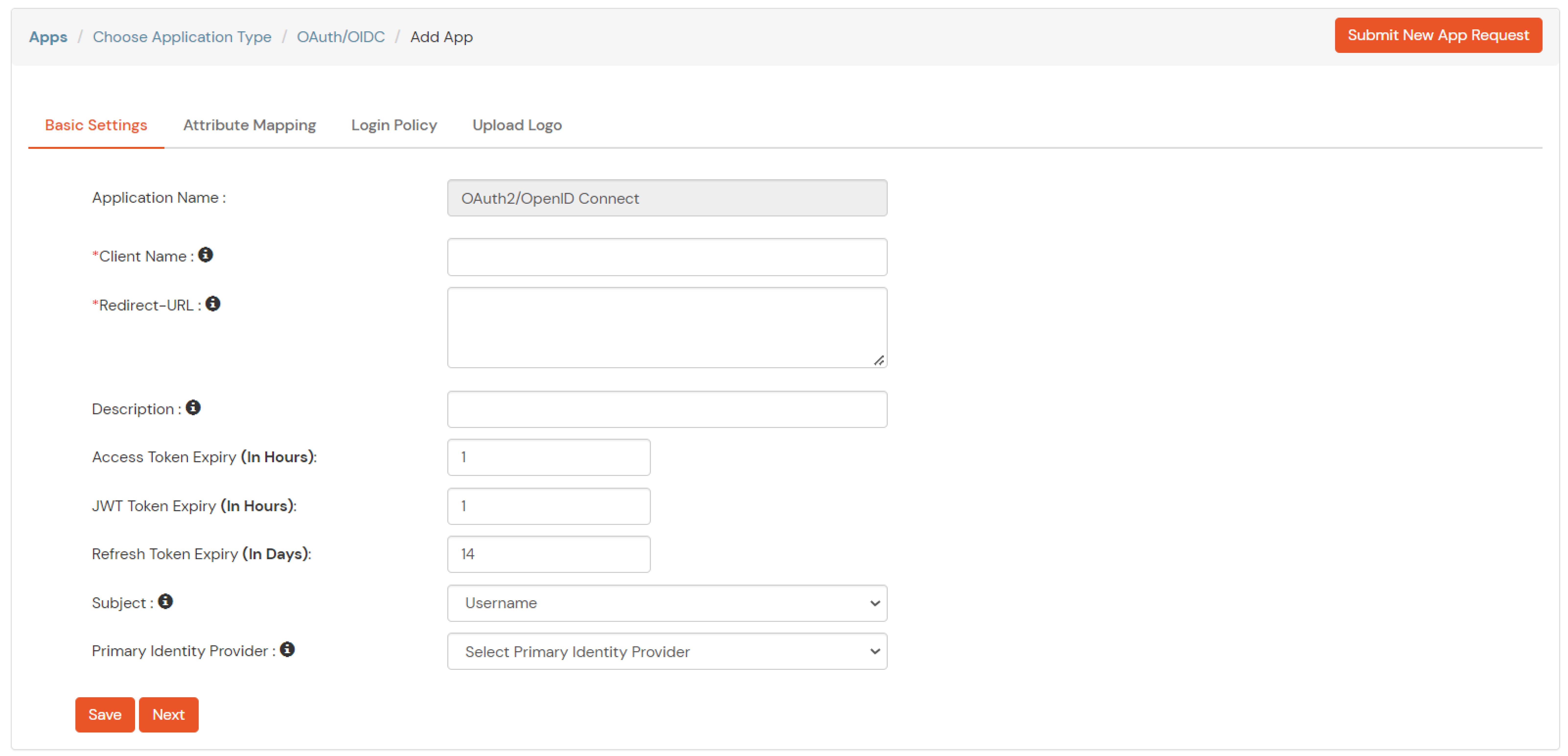
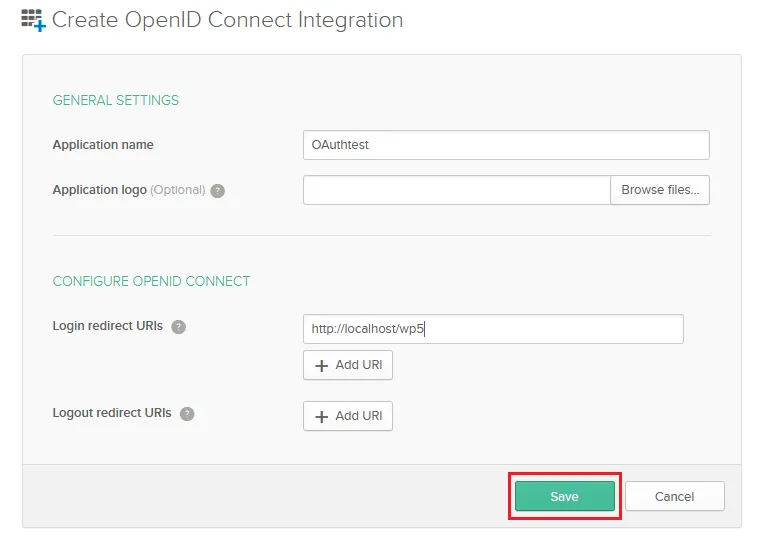
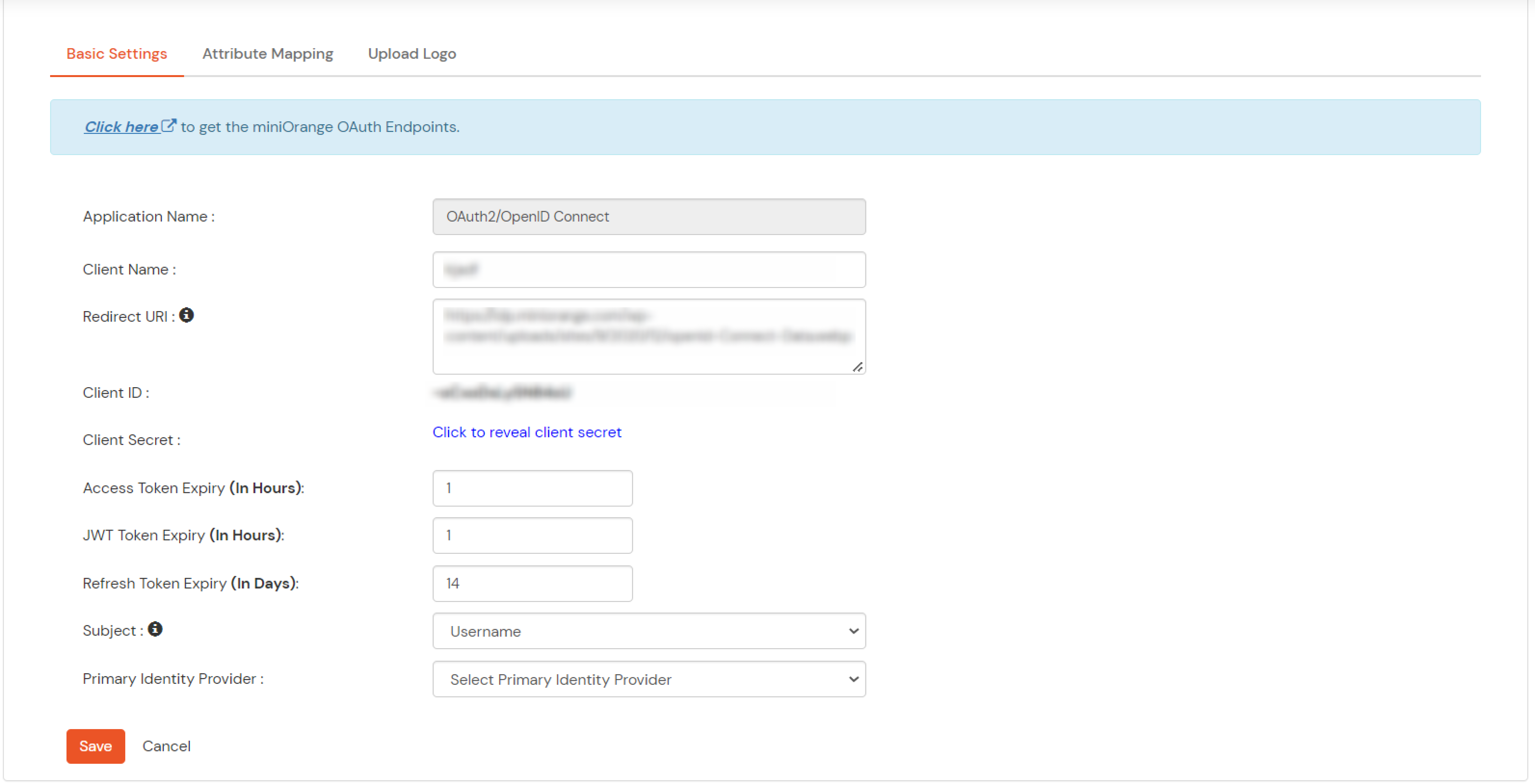
| Client Name | Add appropriate Name |
| Redirect URL | Get the Redirect-URL from your OAuth Client |
| Description | Add if required |
| Group Name | Default |
| Policy Name | As per your Choice |
| Login Method | Password |
Note: Choose the Authorization Endpoint according to the identity source you configure.
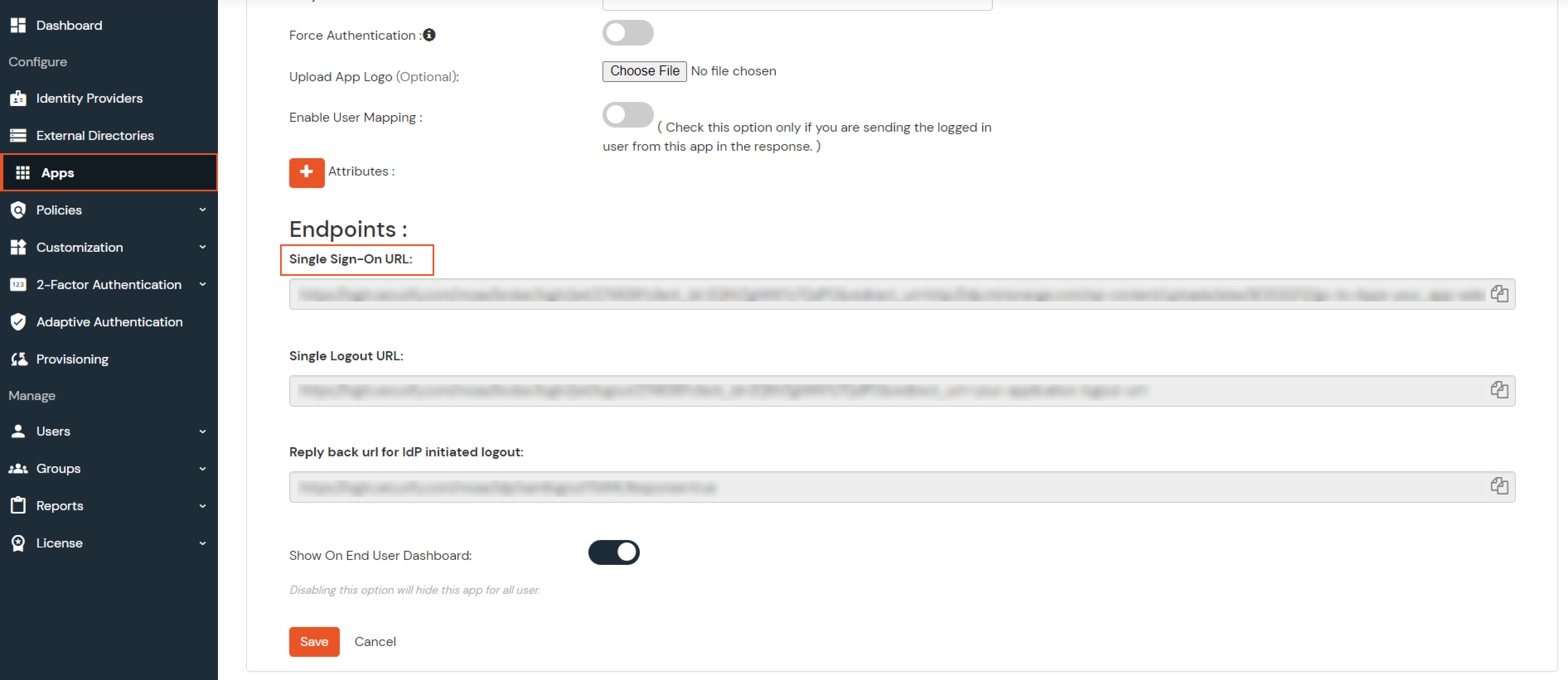
https://{mycompany.domainname.com}/moas/idp/openidssohttps://{mycompany.domainname.com}/broker/login/oauth{customerid}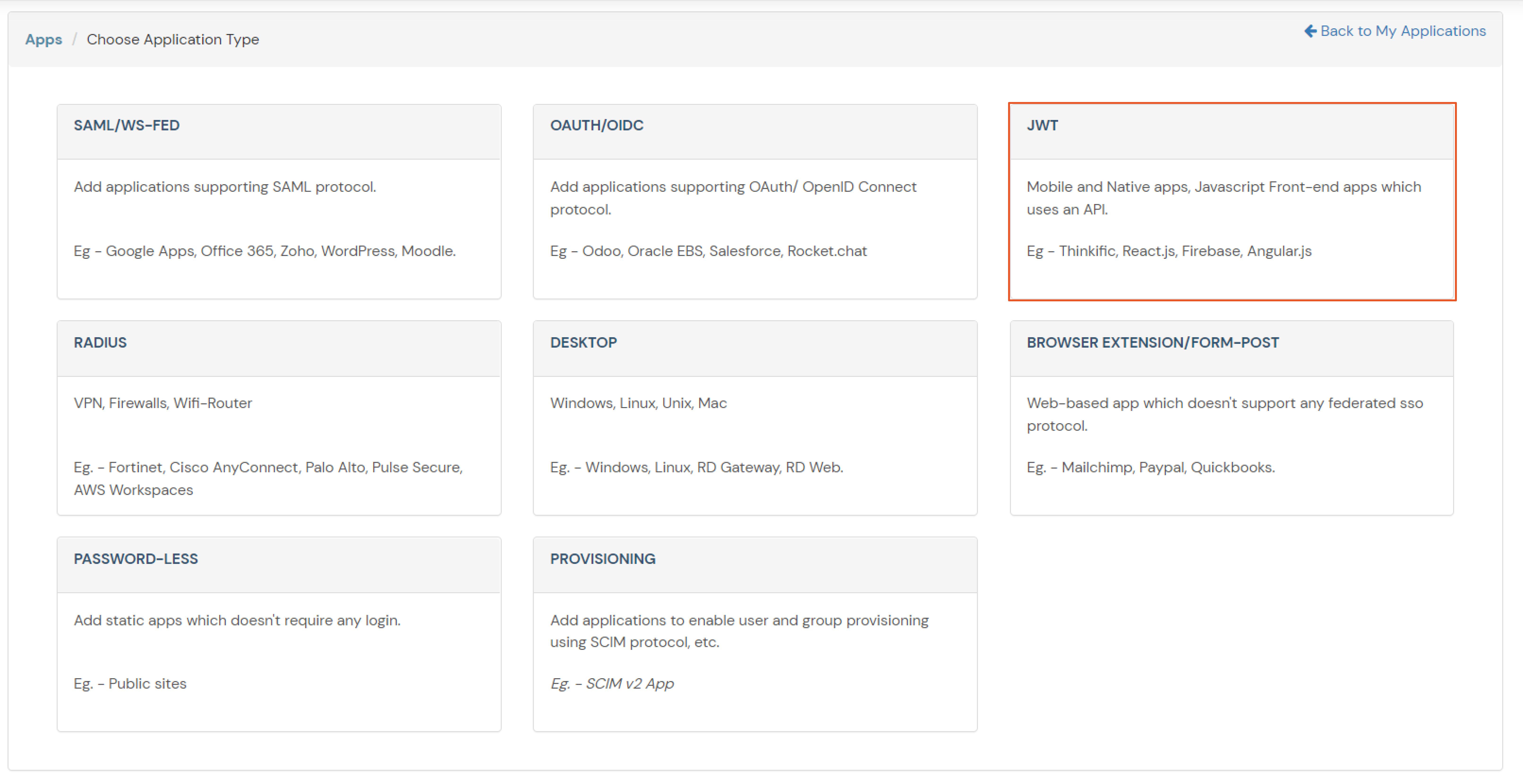
In case you are setting up SSO with Mobile Applications where you can't create an endpoint for Redirect or Callback URL, use below URL.
https://login.xecurify.com/moas/jwt/mobile
Few usecases where customers configure multiple IDPs -
| For Cloud IDP - | https://login.xecurify.com/moas/discovery?customerId=<customer_id> |
| For On-Premise IDP - | https://yourdomain.com/discovery?customerId=<customer_id> |
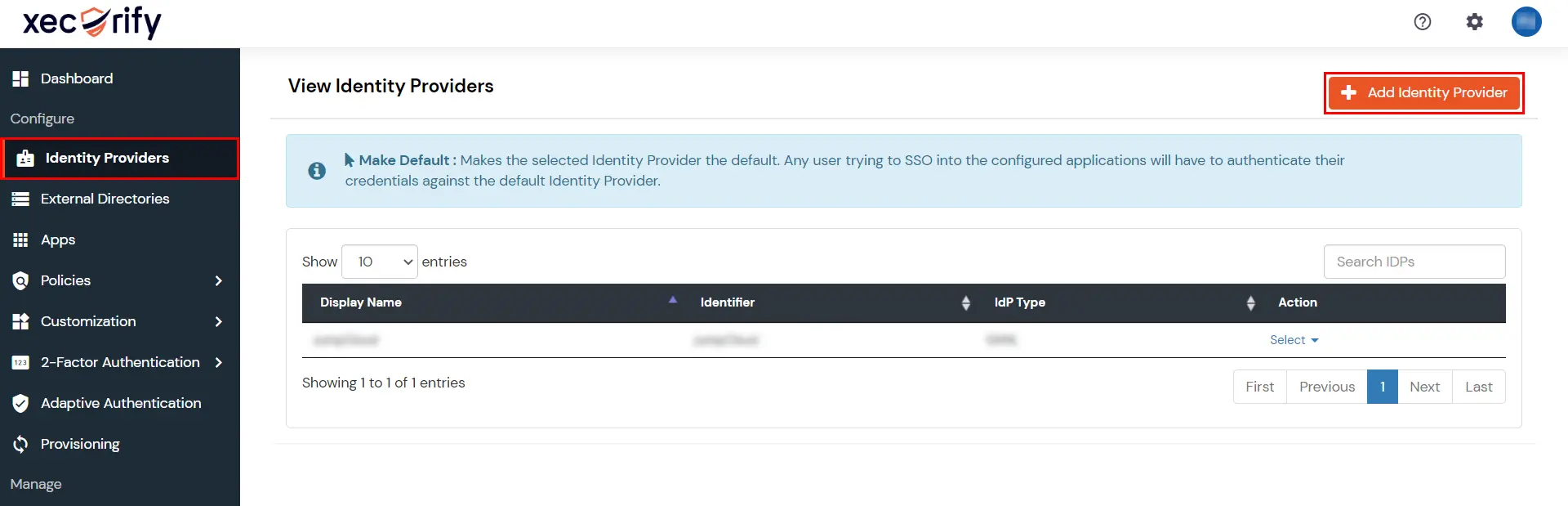
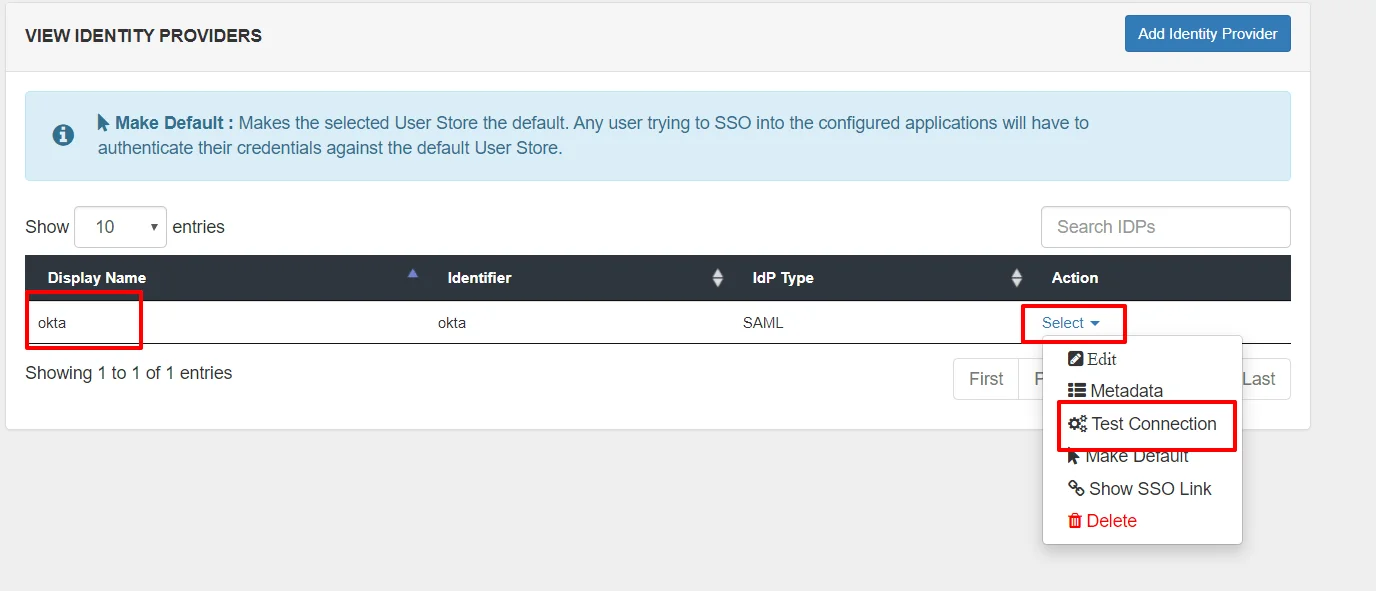
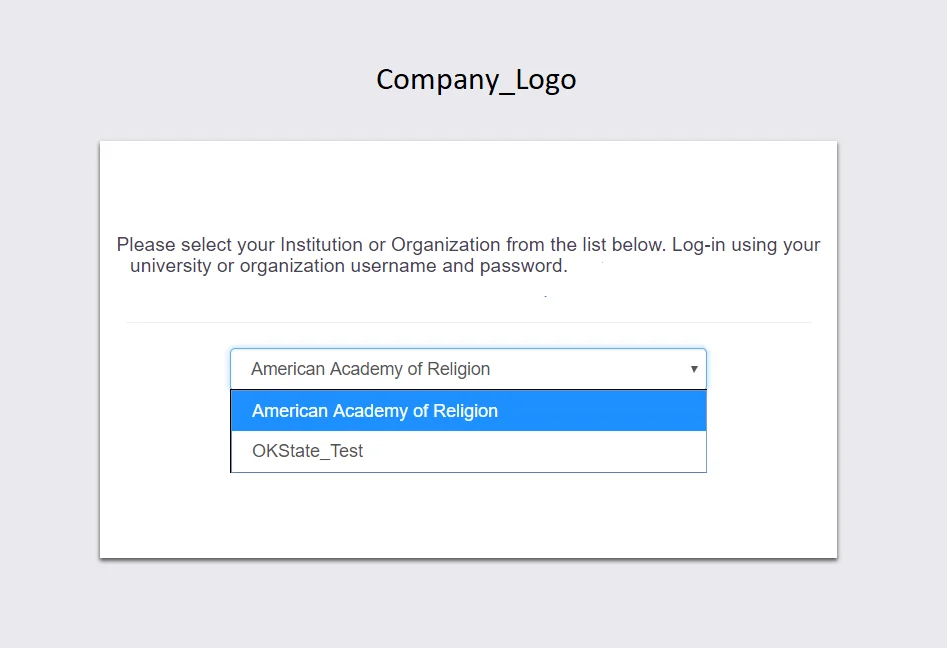
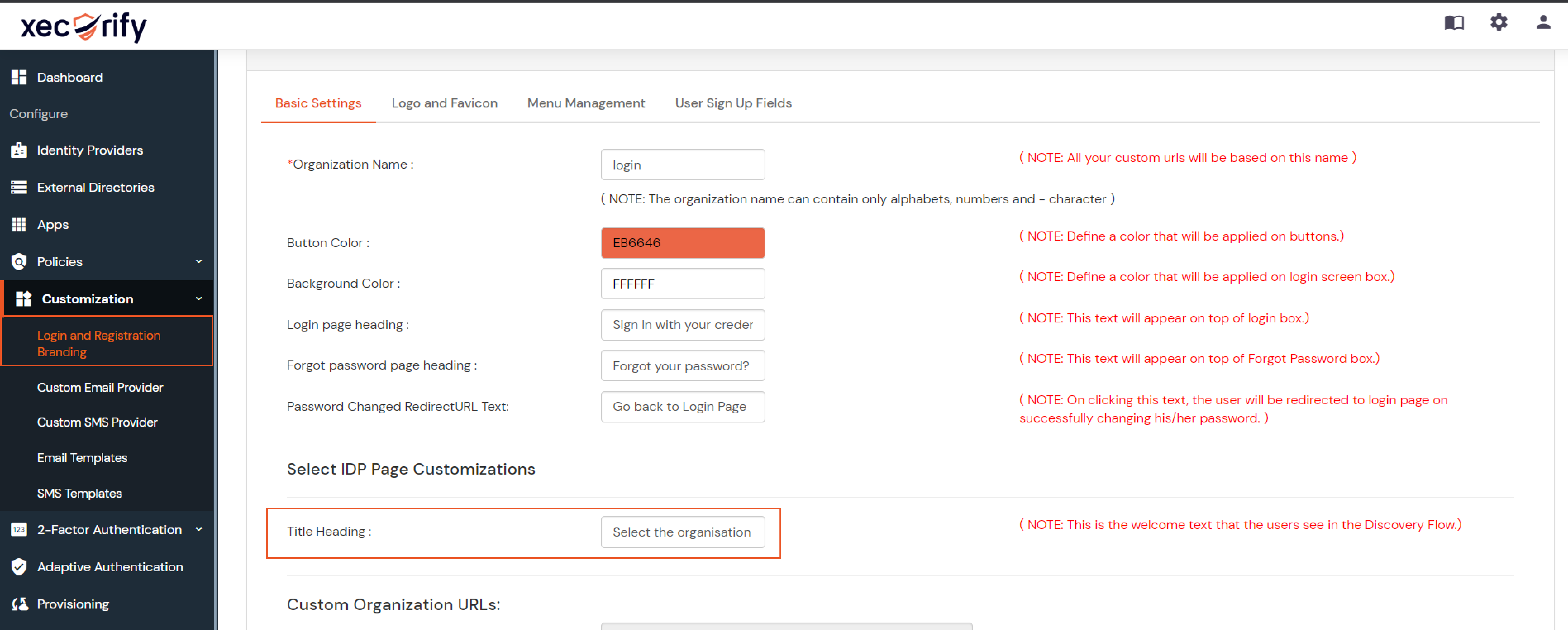
You can see the screenshot below of the IDP Selection Page with a list of IDPs.
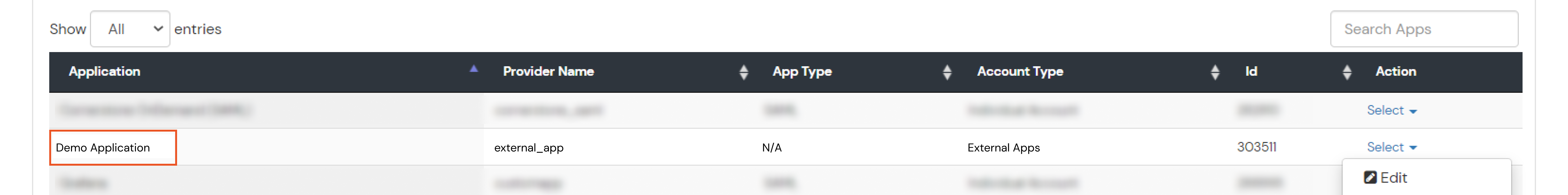
Note: To view the IDP in drop-down list, go to Identity Providers tab > against your configured IDP > Select >Edit , here Enable the Show IdP to Users option.
Our Other Identity & Access Management Products