Need Help? We are right here!
Search Results:
×
Adaptive authentication is a security mechanism that triggers additional authentication factors or Multi-Factor Authentication (MFA) during high-risk scenarios based on contextual factors like IP address, user behavior, device info, location, time, and more. By analyzing these factors, the system assigns a risk score.
If the risk is low, the user gets streamlined access without going through the additional MFA factor, whereas if the risk is high, the user is required to fulfill the MFA challenge in order to authenticate themselves and gain access to the requested resources. If the risk score is too high, then user access will be denied to prevent any kind of unauthorized access. This approach finds a balance between user convenience and security by adapting to the situation.
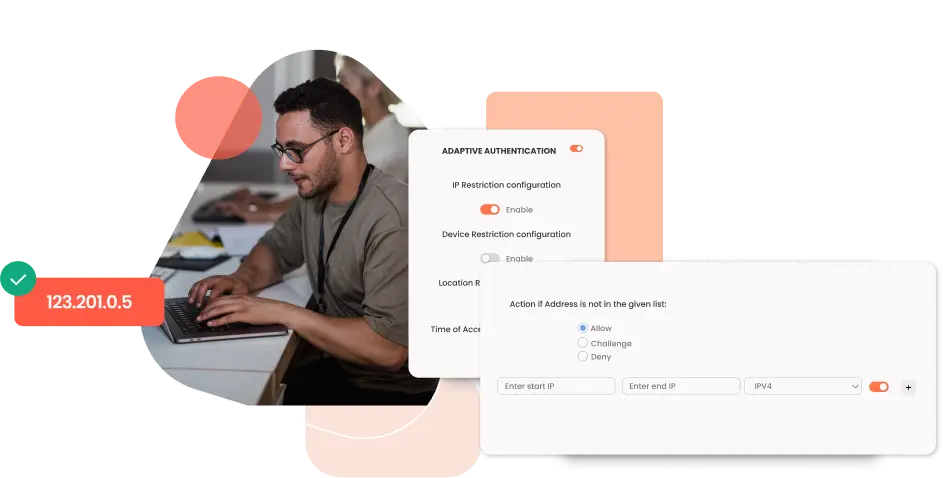
In Adaptive Authentication IP-based restriction method, the admin configures and enlists all IP addresses to allow or deny access. When a user attempts to log into one of the adaptive authentication-enabled apps, his IP address is compared to the preset IP list, and the appropriate action is taken depending on the results (i.e. Allow, Deny or Challenge).
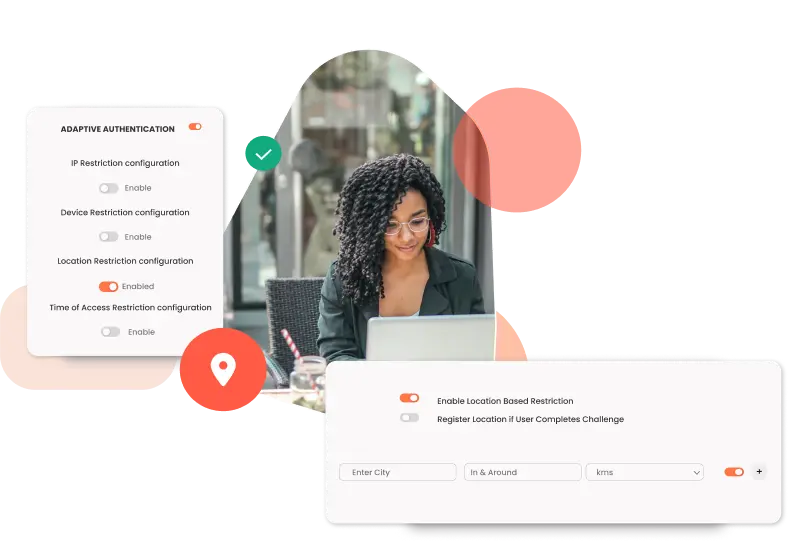
In Location-based Adaptive Authentication restriction, the admin shortlist and configure a list of Geo-locations where they want to allow end-users to either login or deny based on the location set by the admin. When a user tries to login with adaptive authentication enabled, his location attributes such as (Latitude, Longitude, and Country Code) are verified against the Location list configured by the admin, and based on this user will be either allowed, challenged, or denied.
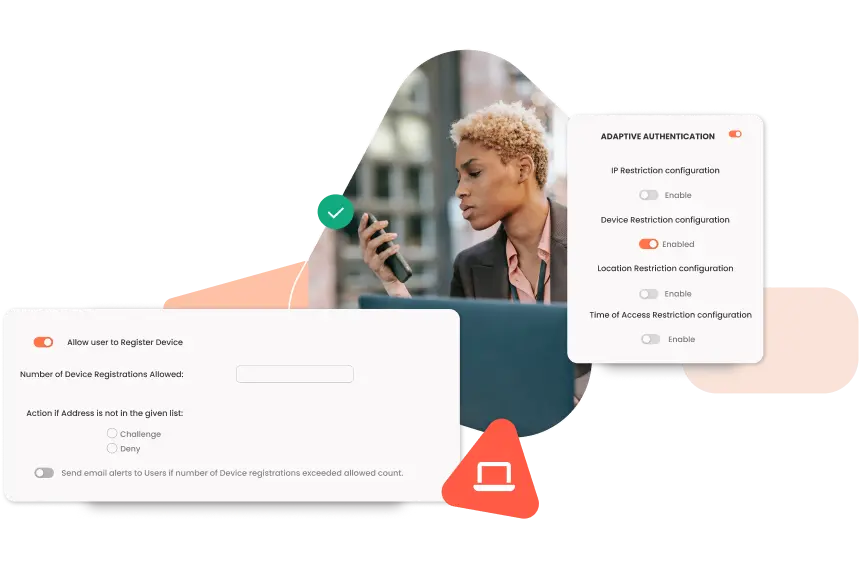
In the Device based Adaptive Authentication method, the admin allows end-users to add a fixed number of trusted devices to their account (A device here refers to a Browser Session). There are two types of Device Restriction that you can enable with our solution:
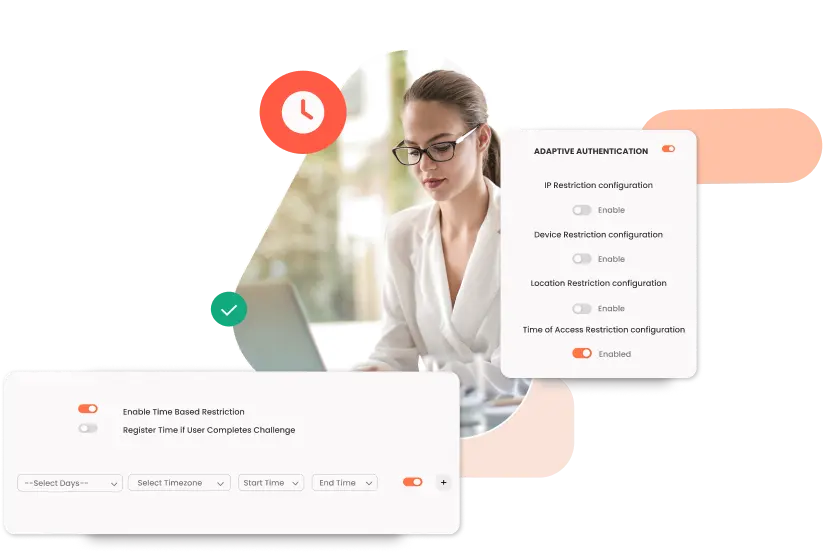
Users are either permitted, refused, or challenged based on the timezone and policies defined in the Time Restriction. When a user logs in with time-based adaptive authentication enabled, the system checks their time zone and current system time against an admin-defined list. Based on the configuration, the user will either be allowed to log in, denied access, or prompted for additional authentication.
Identity solutions from miniOrange can be easily deployed in your organization's existing environment.
per user per month
*Please contact us to get volume discounts for higher user tiers.







"Nahdi wanted to adopt SSO, and they were using Siebel CRM, but it didn't support any SSO protocols. Changing the entire CRM system and transferring data from one CRM to another is a time-consuming job....."
Secure the sensitive data of your organization with Adaptive Authentication, which protects against unauthorized access to corporate networks and confidential data through enhanced runtime risk analysis.
miniOrange's Adaptive Authentication supports various use cases, seamlessly integrating with your systems. Admins can set custom policies using dynamic setup options.
Adaptive MFA lets you limit user access based on factors like IP, device, location, and time. It assesses session attributes in real-time to calculate risk and make access decisions.
Use miniOrange's Adaptive Authentication APIs to add extra security with Adaptive MFA to all your SaaS apps on any web browser-supported device with quick and effortless deployment.
Our Adaptive MFA product is platform independent and can be easily deployed to any device supporting a web browser, irrespective of the type of device.
Ensure a smooth user experience by concealing advanced security measures from end users. This maintains productivity as users can work without disruptions from security concerns.
According to Ponemon Institute statistics, 77% of companies are woefully ill-prepared and planned when it comes to thwarting an attack or a data breach. Data breaches can cause companies losses worth billions of dollars, which can cripple the growth of any organization.
Hence, It is extremely crucial to implement stringent security mechanisms like Adaptive MFA in order to keep these cyber attacks at bay while engaging your workforce in more productivity and peace of mind. Here are some of the reasons why today’s modern organizations need Adaptive Authentication
Organizations are exposed to dynamic threats and to cater to these evolving security challenges, an adaptable solution like Adaptive MFA is crucial. It detects unusual patterns or high-risk indicators and triggers MFA challenges, bolstering security against evolving cyber threats.
Monitoring user activities and contextual details in real-time can prevent 90% of all cyber attacks in organizations. Adaptive MFA enables real-time monitoring for swift responses to emerging threats and potential security breaches. By proactively identifying suspicious activities, organizations can effectively safeguard their sensitive information and operations.
Many industries are subject to regulations of local governments and international regulatory bodies, which mandates robust security measures. Adaptive MFA helps organizations meet compliance standards without causing disruptions to daily operations.
Adaptive MFA builds threat resilience in organizations by thwarting modern cyber attacks like phishing, ransomware, etc. It detects insider threats by flagging unusual behavior. Furthermore, it prevents unauthorized access through dynamic responses to risk factors.
Safeguard sensitive data in Google Workspace apps (Gmail, Drive, etc.) using miniOrange Adaptive MFA. Prevent unauthorized access, ensure productivity, and enable smooth access for authorized users.
VPNs are vulnerable to brute force attacks and to better secure them, add adaptive MFA for VPNs. It analyzes risks and prompts MFA when needed, alerts admins of unusual activity, and prevents unauthorized access and data breaches.
Securing different SaaS apps is challenging, and a simple credential leak leads to sensitive data exposure. With miniOrange Adaptive MFA, you can secure all your different SaaS apps at once with easy integration.
Multi-Factor Authentication (MFA) is an authentication method that requires the user to provide two or more verification factors, such as a username, password, and additional security measure, to gain access to a resource.
On the other hand, Adaptive MFA provides an extra edge to MFA security based on risk and access provided by the security admin to control user access. It detects fraudulent attempts based on predetermined risk criteria and prompts customers to complete an additional authentication step to confirm their identities.
An Authentication service provides an identity verification mechanism that verifies the identity of a user against some fixed attributes (like login credentials, passwords, etc.) before granting them access to the requested digital resources (like app account, digital services, and many more). Without a proper authentication system in place, there lies the risk of unauthorized access to sensitive resources.
Knowledge Factor (something you know): Includes multiple passwords, PIN codes, and answers to security questions. Anything you can remember, type, say, do, execute, or otherwise recall when needed is considered a knowledge element.
Possession Factor (something you have): Includes a particular object which you possess since it is improbable that a hacker would acquire your password and take anything physical. This category includes smart cards, mobile phones, physical tokens, key fobs, and keychains.
Inherence Factor (something you are): Verified by a fingerprint test on a phone, but it also includes anything that may be a wholly unique identification of your physical body, such as a retinal test, voice or facial recognition, or any other sort of biometrics.
Identity, Access, and Beyond