Need Help? We are right here!
Need Help? We are right here!
Thanks for your Enquiry. Our team will soon reach out to you.
If you don't hear from us within 24 hours, please feel free to send a follow-up email to info@xecurify.com
Search Results:
×miniOrange seamlessly integrates with Cisco Meraki Client VPN to enhance security by adding an additional layer of protection. You can swiftly establish a secure remote access environment for your organization, promoting a hybrid work culture with multifactor authentication (MFA).
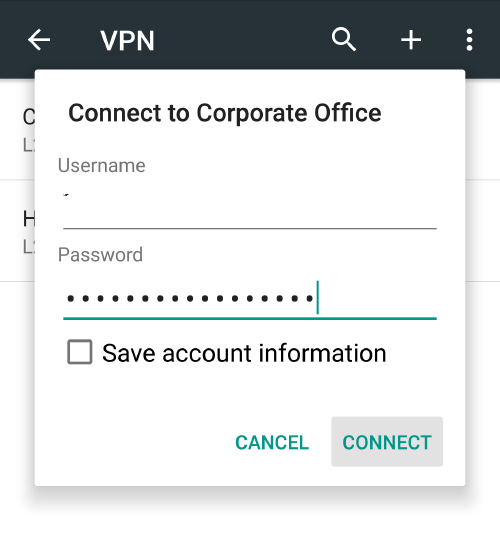
miniOrange offers users secure and smooth remote access to corporate networks and resources while on the go or working remotely, thanks to Multi-factor Authentication for Cisco Meraki VPN. You have the option to enable Multi-Factor Authentication (MFA/2FA) for both your Cisco Meraki Client VPN and your managed active directory, bolstering security. With MFA/2FA enabled, users follow their usual login process, entering their username and password as the first factor. For the second factor, they are required to input an authentication code, which is either virtually shared on their device or provided in the form of a hardware token.
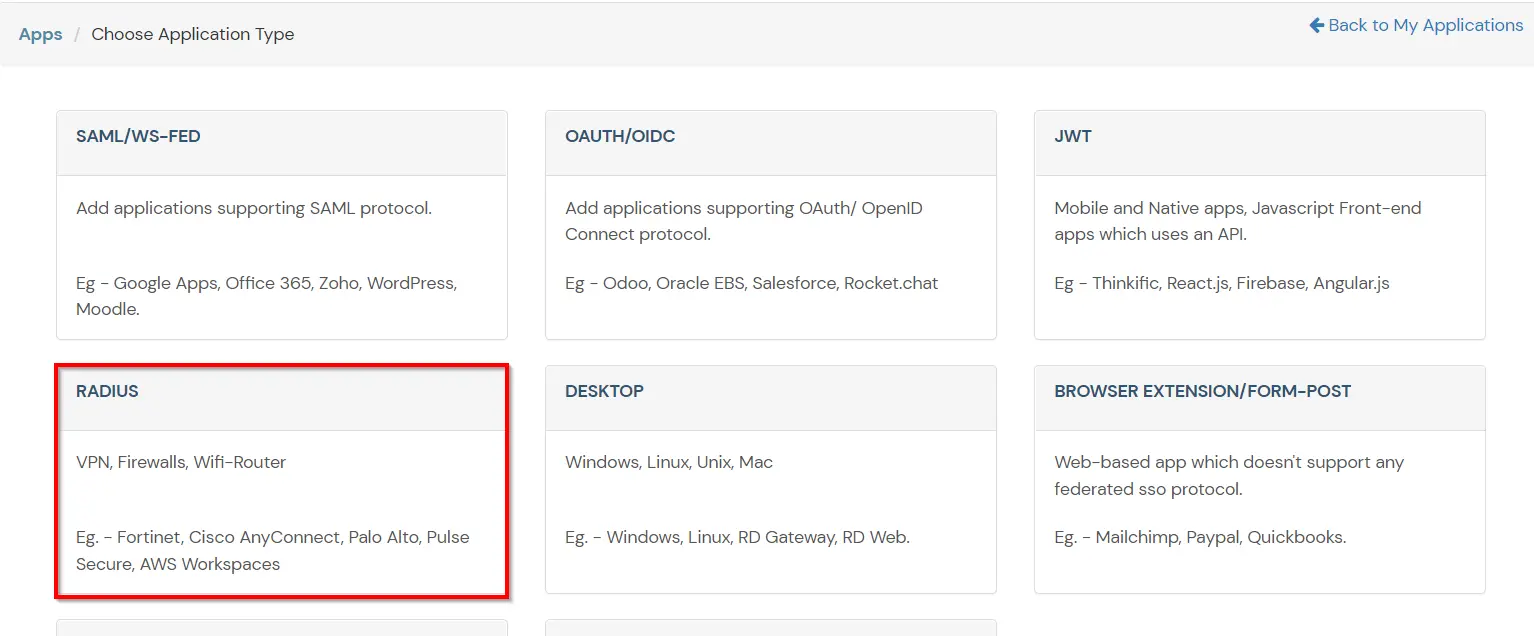
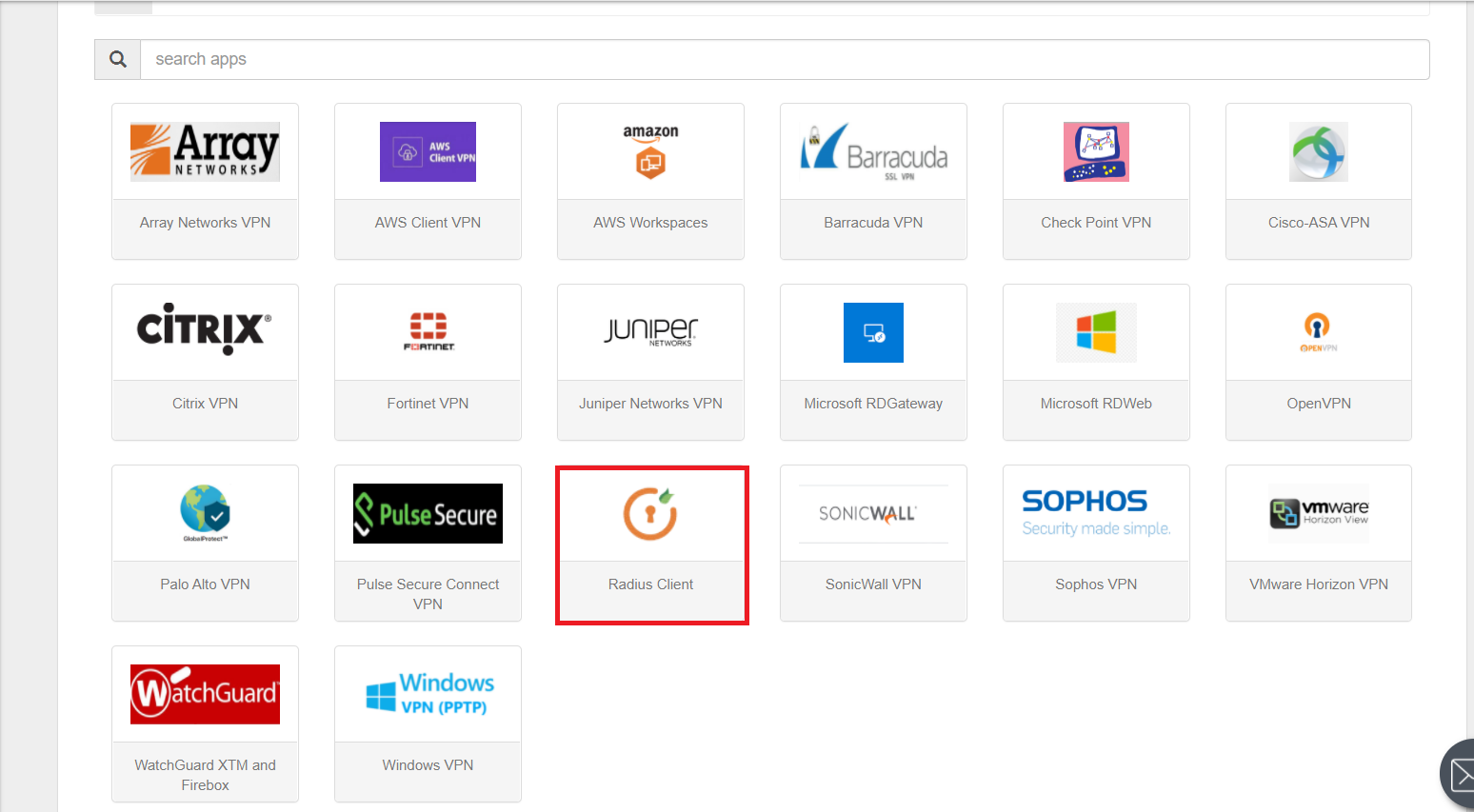
miniOrange offers a hassle-free setup solution for MFA with Cisco Meraki VPN, boasting over 15 MFA methods such as OTP over SMS, Microsoft Authenticator, Google Authenticator, and many others. Beyond Multi-Factor Authentication (MFA) for Cisco Meraki VPN, miniOrange also extends MFA support to firewalls and routers utilizing the radius Protocol. This setup guide, with its straightforward steps, will walk you through the entire process of implementing MFA with Cisco Meraki VPN.
Be Cyber Insurance compliant with miniOrange MFA solution. Read More
miniOrange offers free help through a consultation call with our System Engineers to Install or Setup Two-Factor Authentication for Cisco Meraki Client VPN solution in your environment with 30-day trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you setting it up in no time.
miniOrange accomplishes this by acting as a RADIUS server that accepts the username/password of the user entered as a RADIUS request and validates the user against the user store as Active Directory (AD). After the first level of authentication, miniOrange prompts the user with 2-factor authentication and either grants/revokes access based on the input by the user.
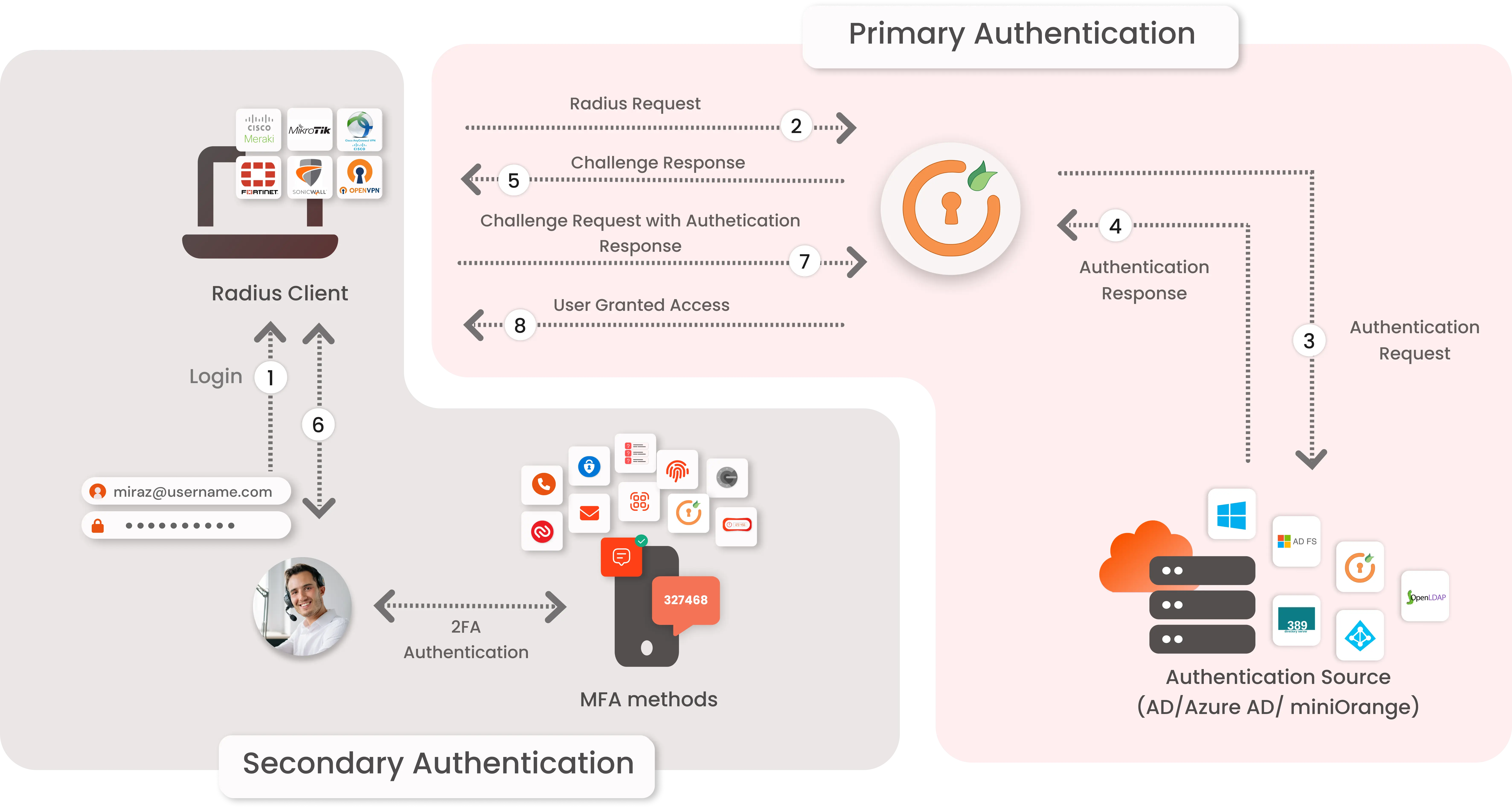
miniOrange provides user authentication from various external directories such as miniOrange Directory, Microsoft AD, Azure Active Directory/LDAP, AWS Cognito and many more.
Can't find your Directory? Contact us on idpsupport@xecurify.com
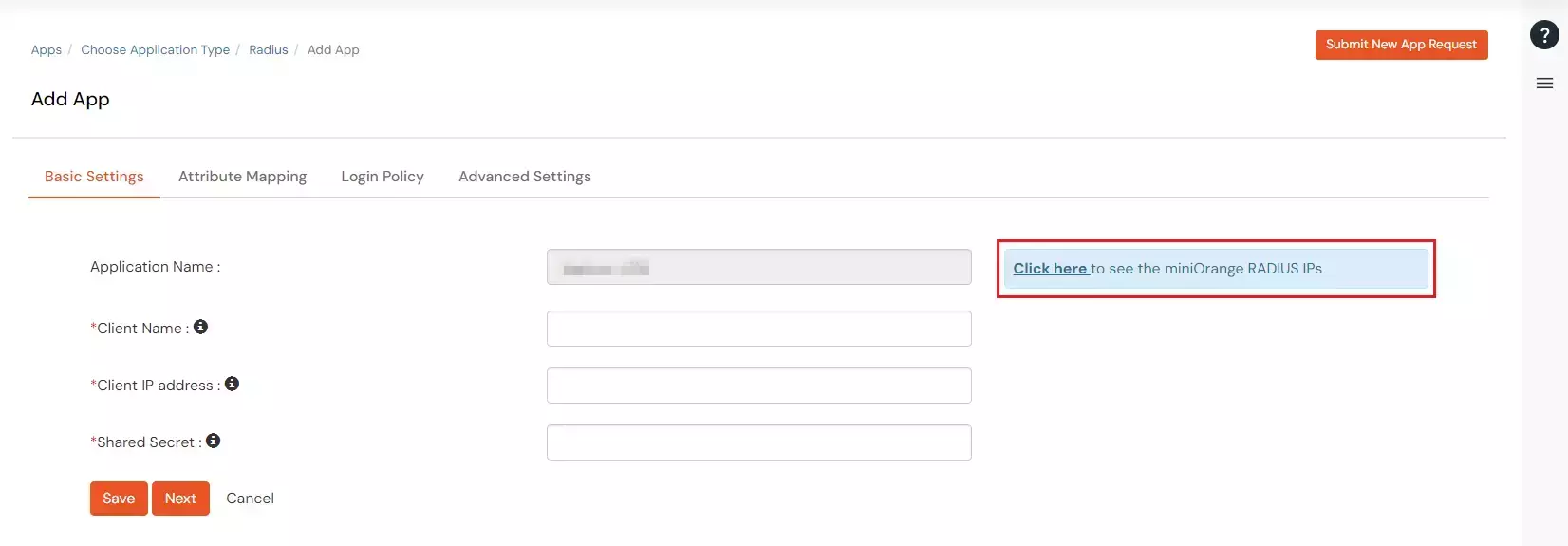
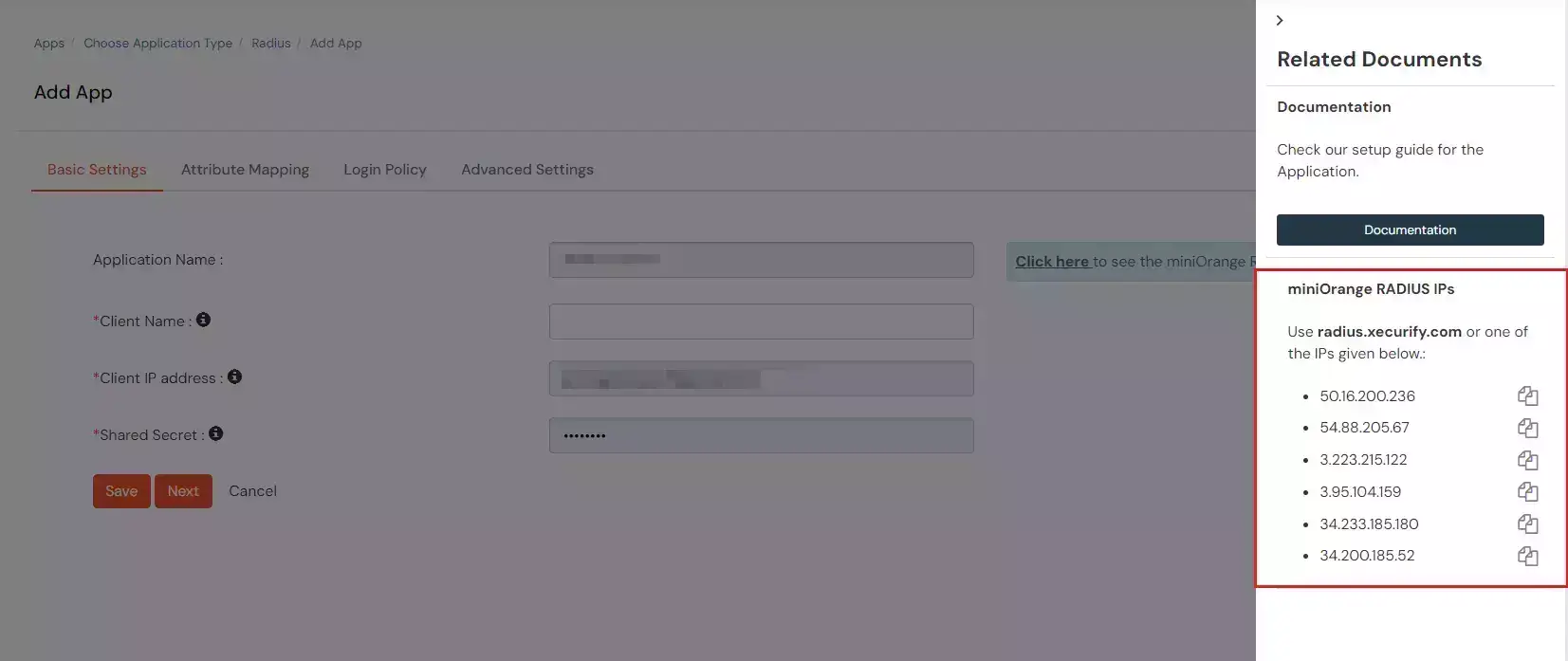
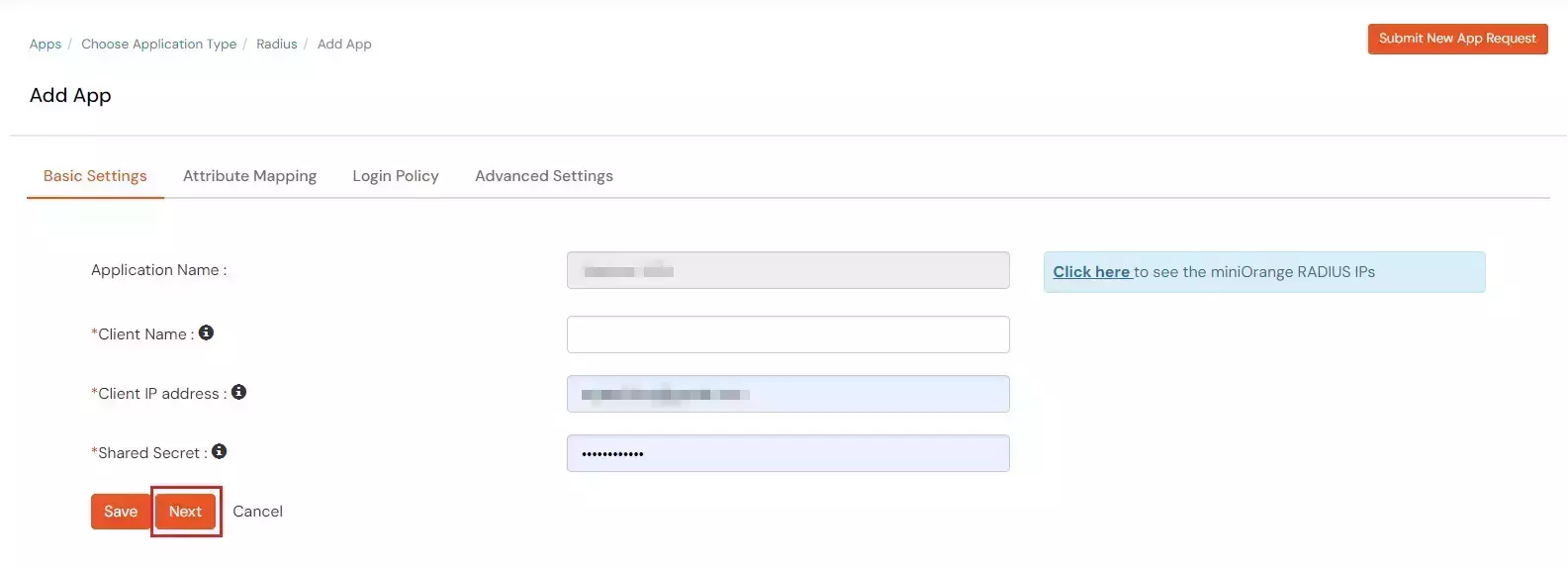
| Client Name: | Any name for your reference. |
| Client IP: | IP address of VPN server which will send Radius authentication request. |
| Shared Secret: | Security key. For Eg. "sharedsecret" (Keep this with you, you will need to configure same on VPN Server). |
| Vendor Name | Group Attribute | Vendor ID | Vendor Attribute ID |
|---|---|---|---|
| Cisco ASA VPN | 26 Vendor-Specific | 3076 | 25 |
| Fortinet VPN | 26 Vendor-Specific | 12356 | 1 |
| Palo Alto VPN | 26 Vendor-Specific | 25461 | 5 |
| SonicWall VPN | 26 Vendor-Specific | 8741 | 3 |
| Citrix VPN | 26 Vendor-Specific | 66 | 16 |
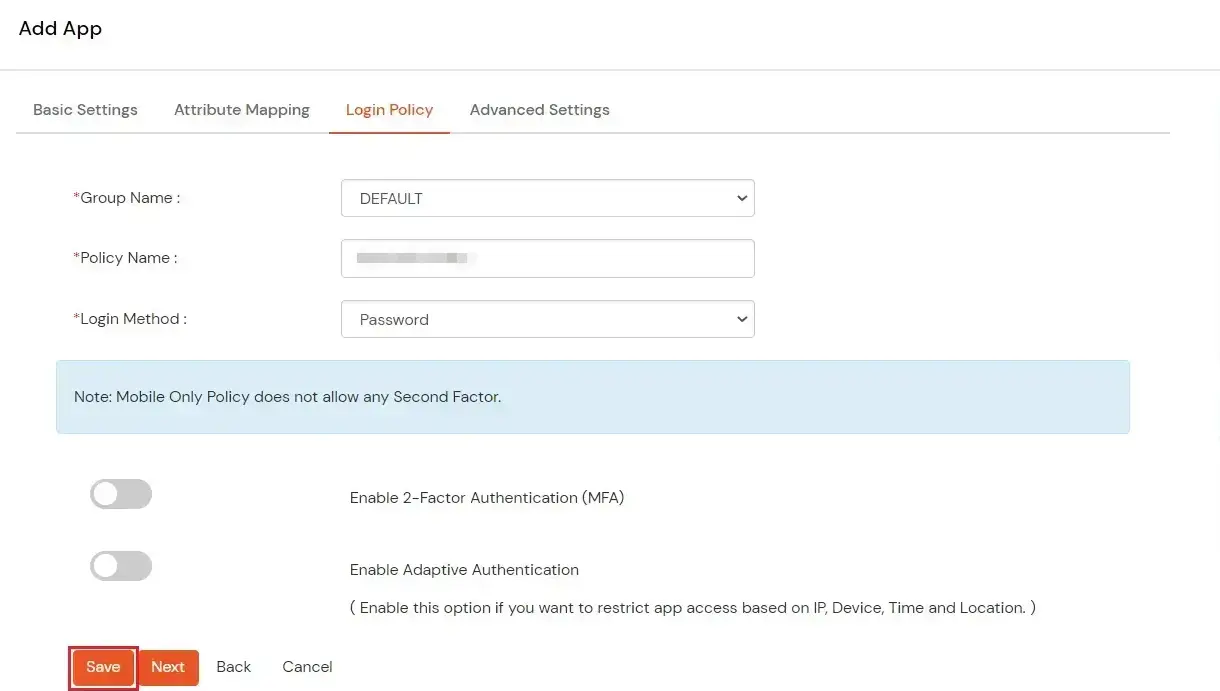
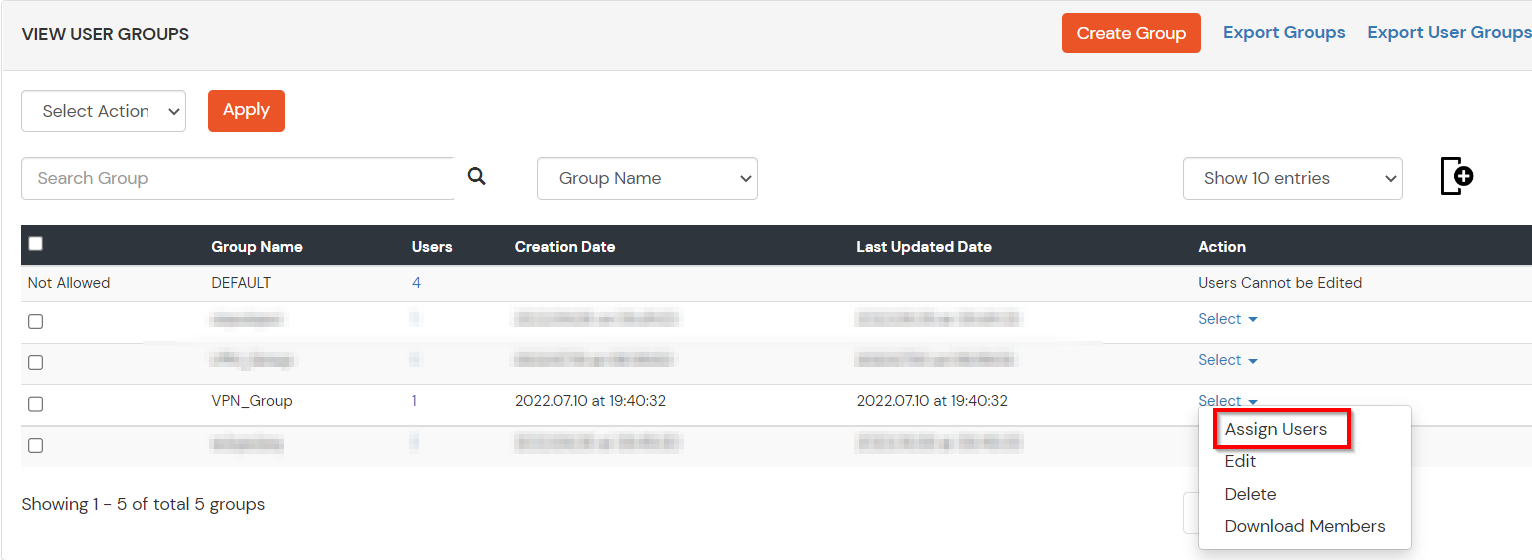
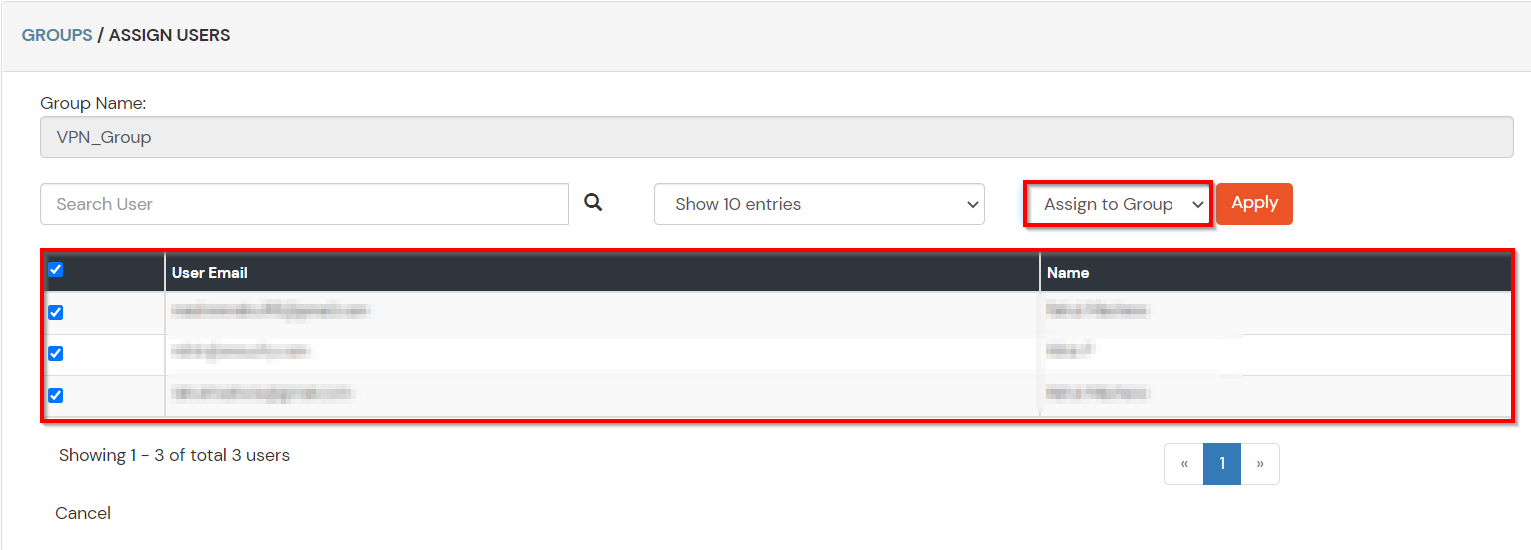
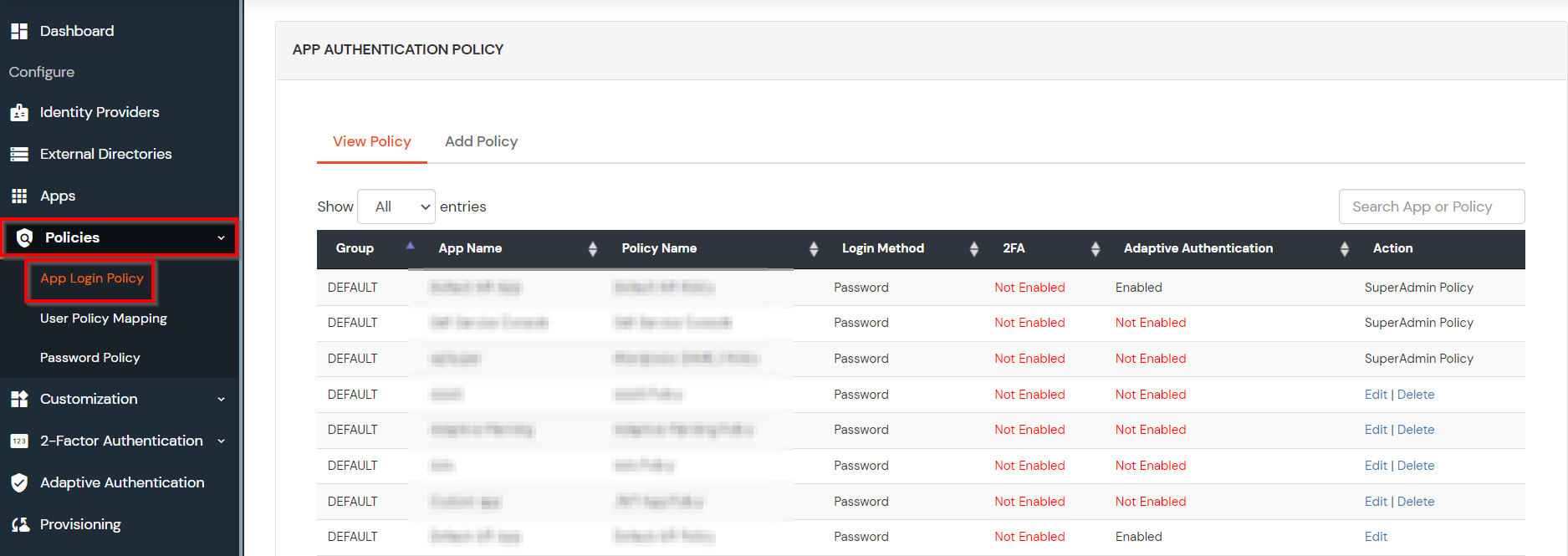
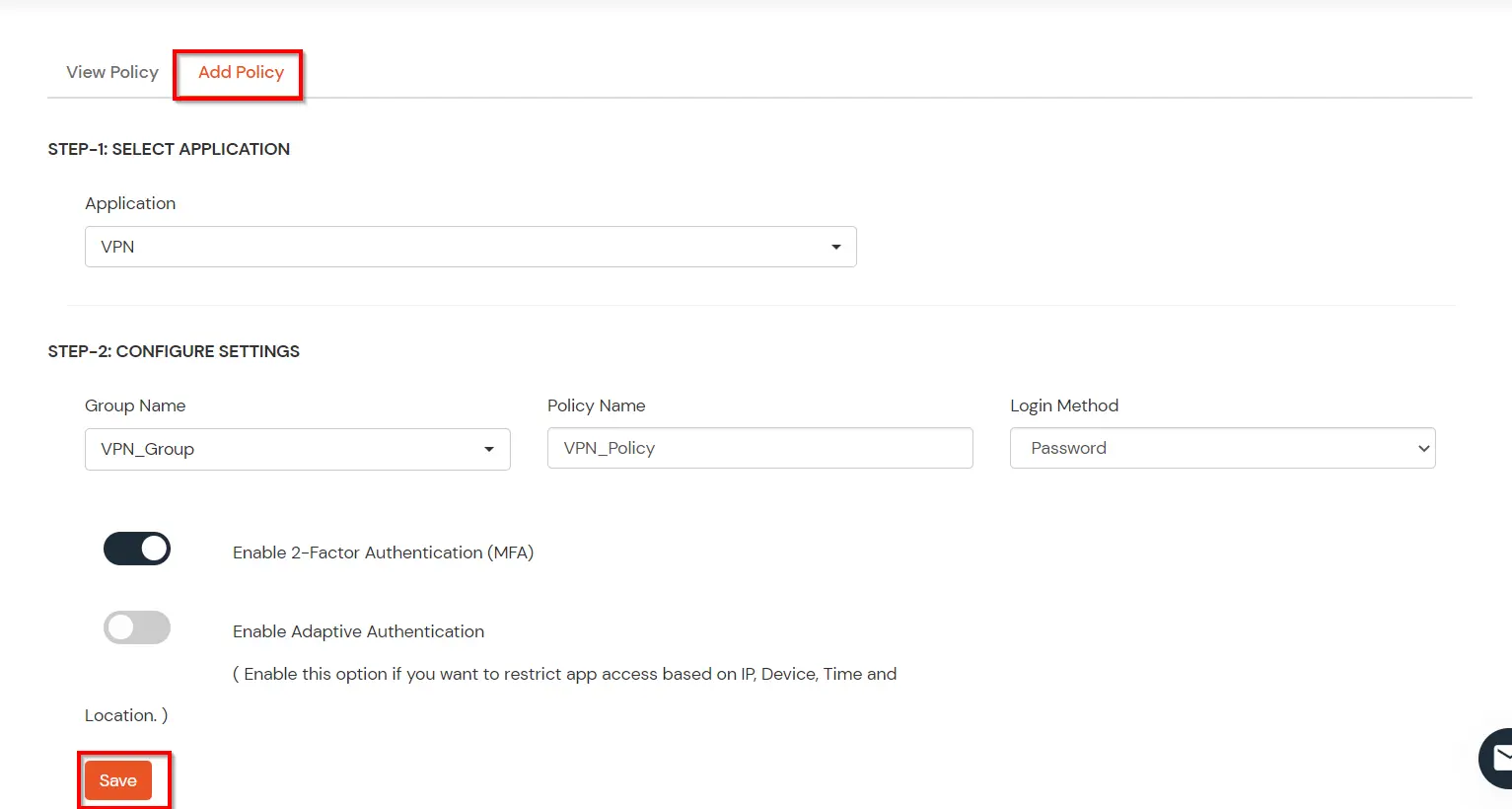
| Group Name: | Group for which the policy will apply. |
| Policy Name: | Any Identifier that specifies policy name. |
| Login Method | Login Method for the users associated with this policy. |
| Enable 2-Factor Authentication | Enables Second Factor during Login for users associated with this policy. |
| Enable Adaptive Authentication | Enables Adaptive Authentication for Login of users associated with this policy. |
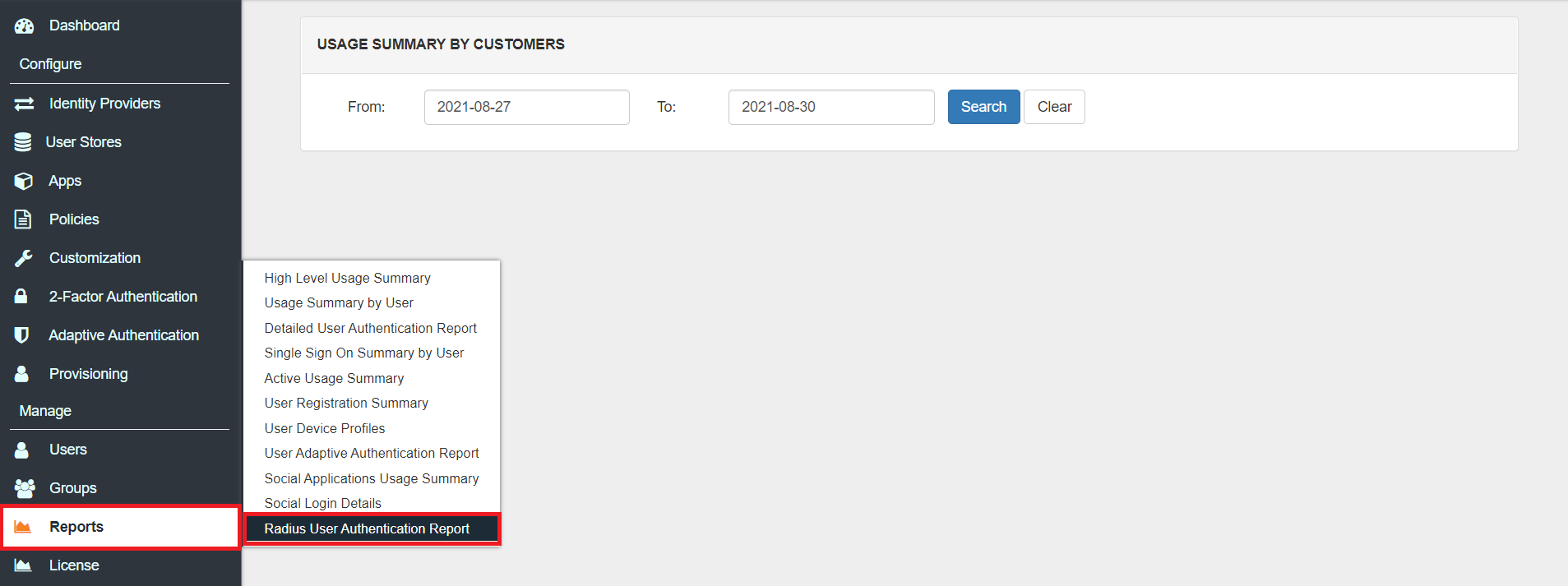
Only For On-Premise Version
Open Firewall Ports.
| Setting | Value |
|---|---|
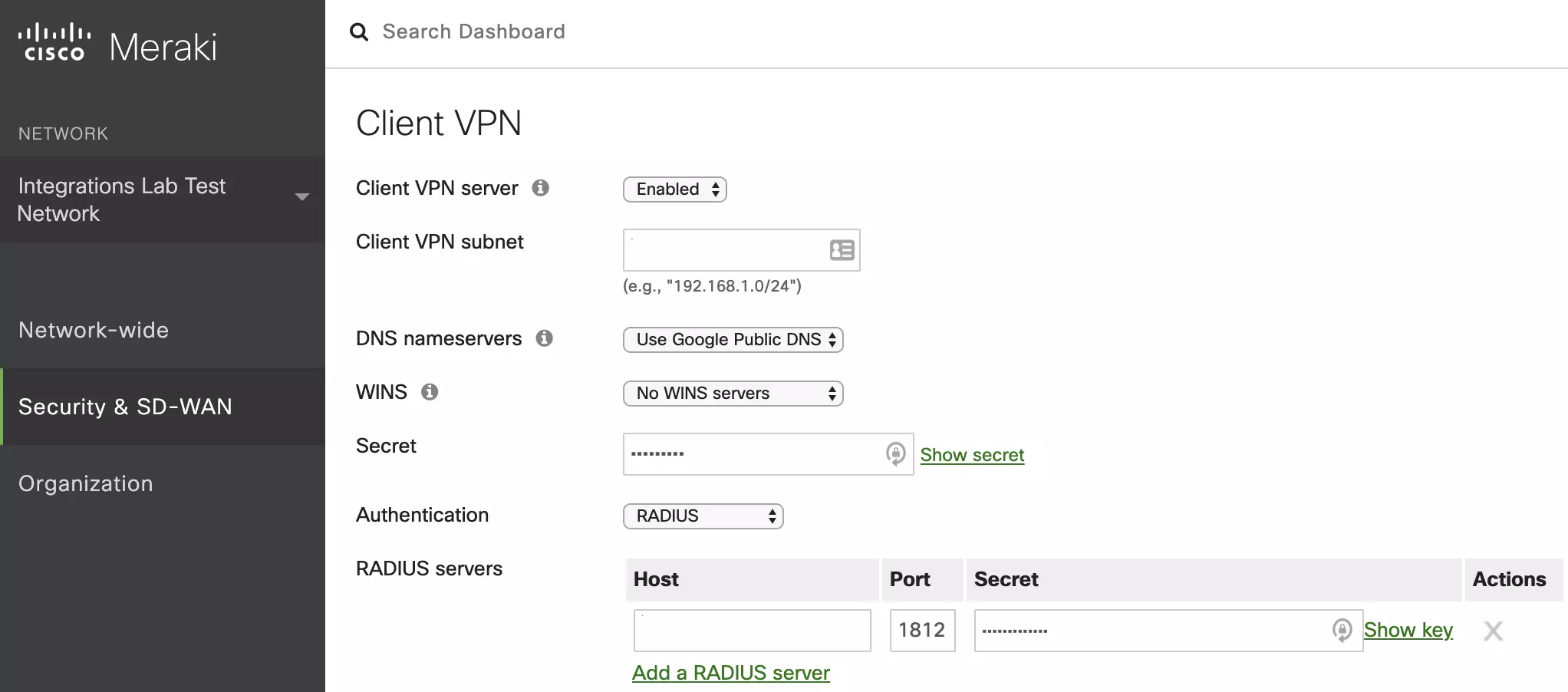
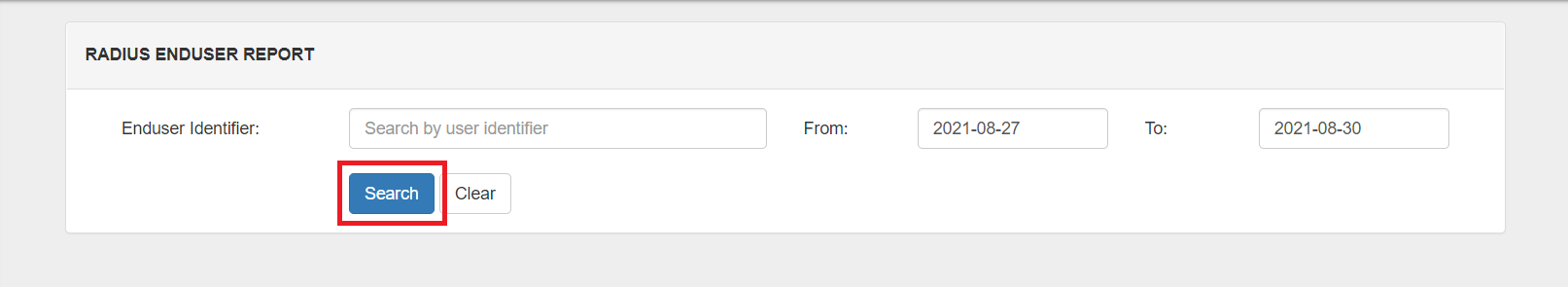
| Host | Enter the hostname or IP address of Radius server of miniOrange that you got from Step 1. |
| Port | 1812 |
| Server Secret Key | Shared Secret used while app creation in miniOrange. |
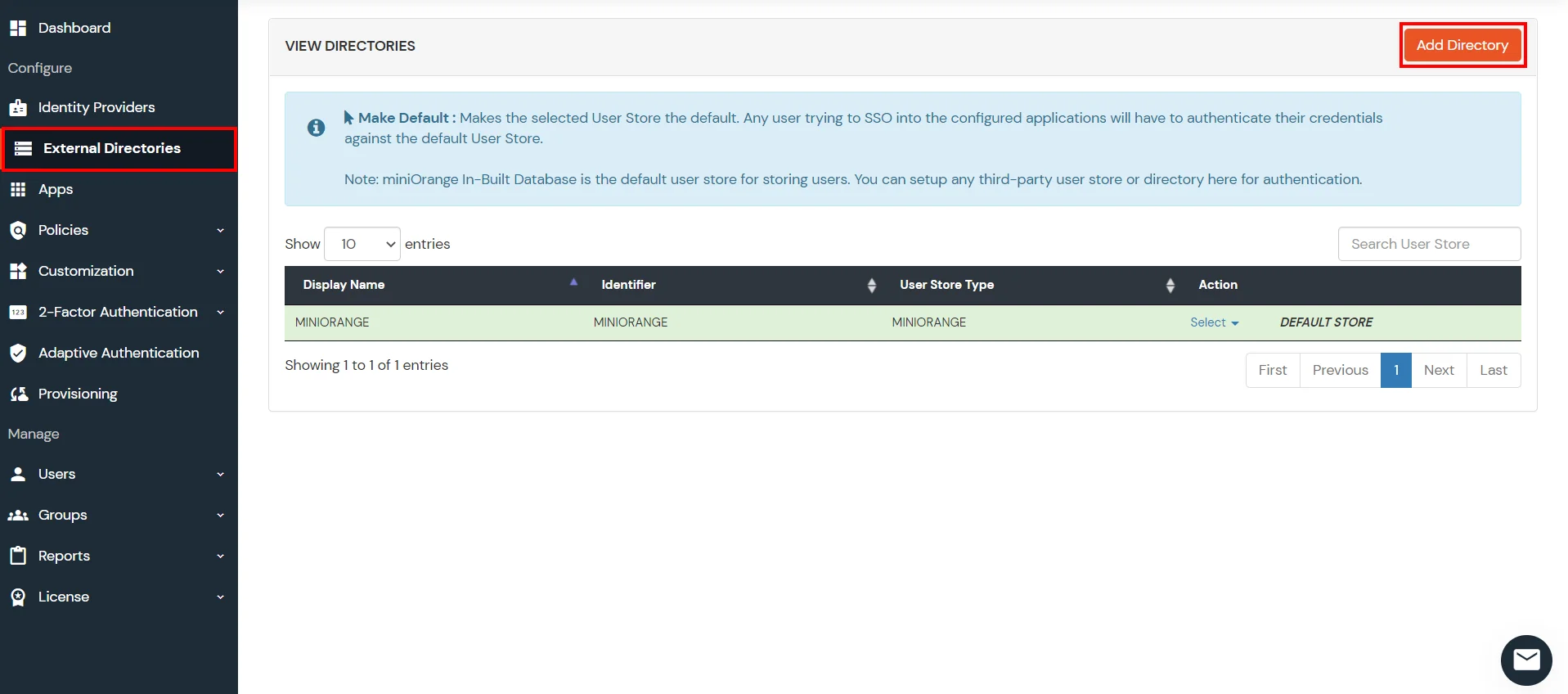
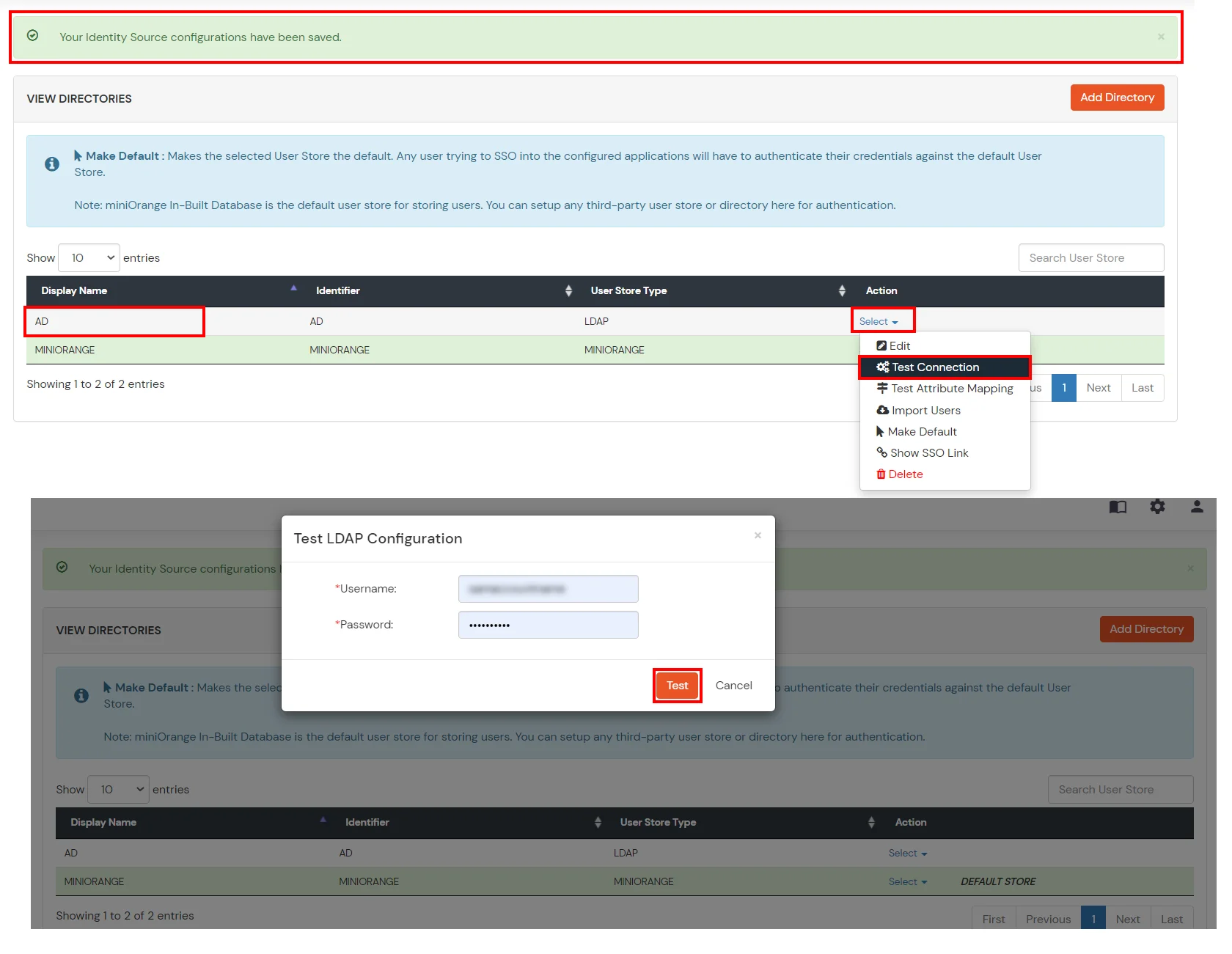
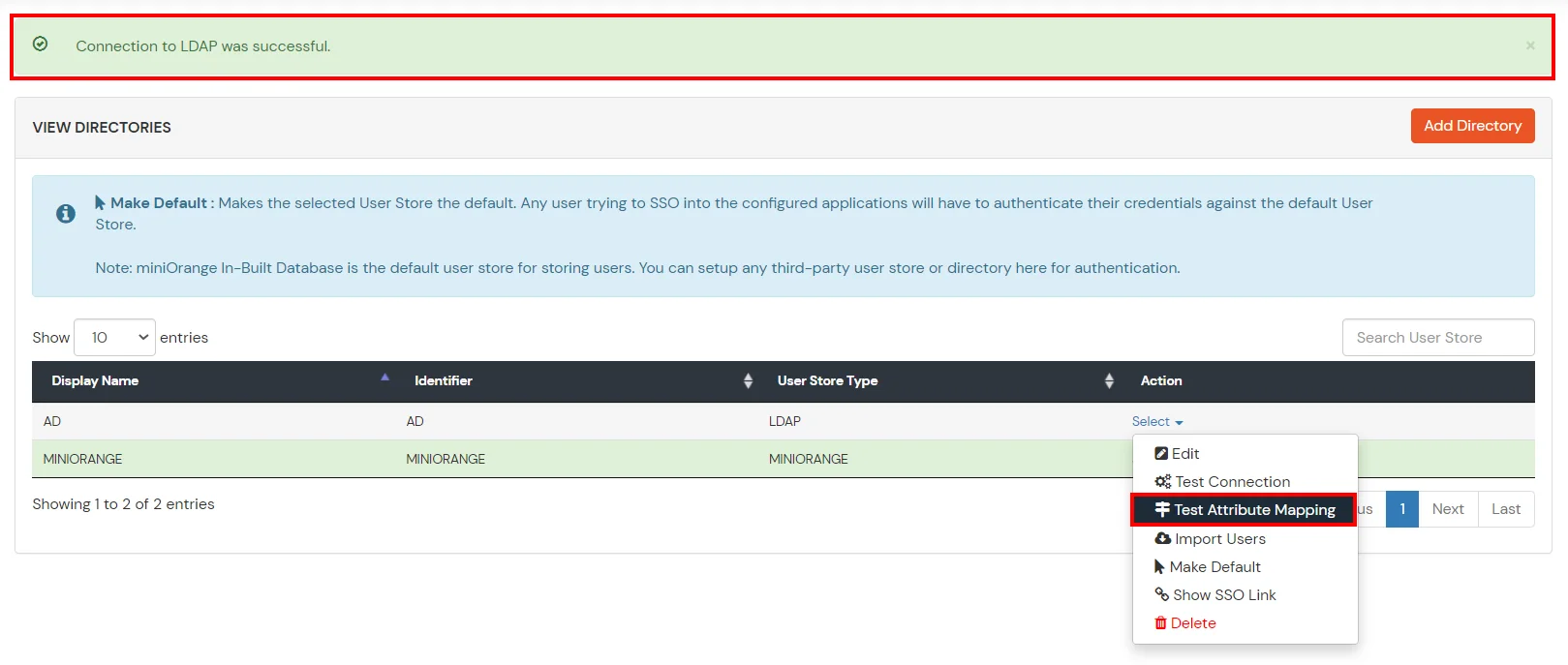
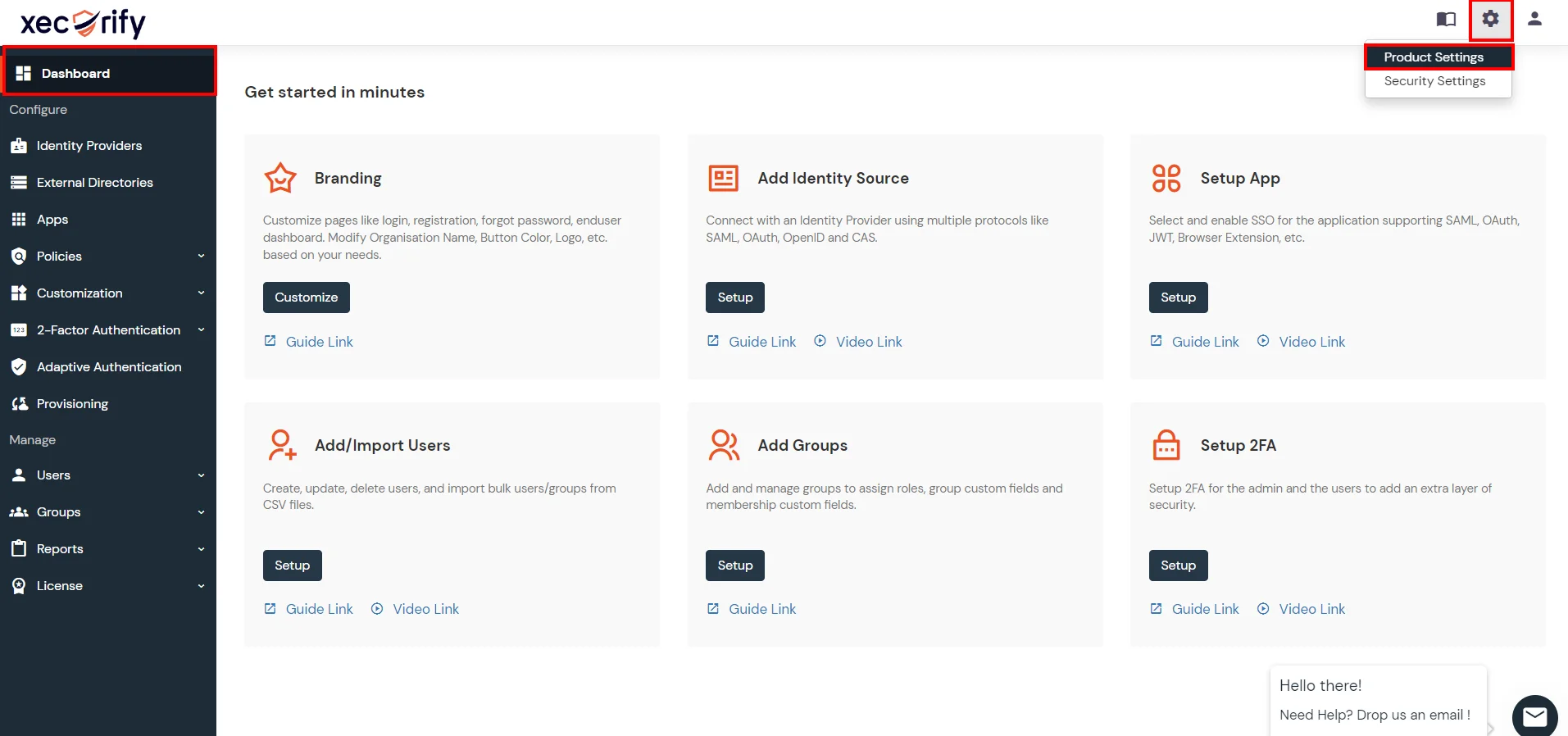
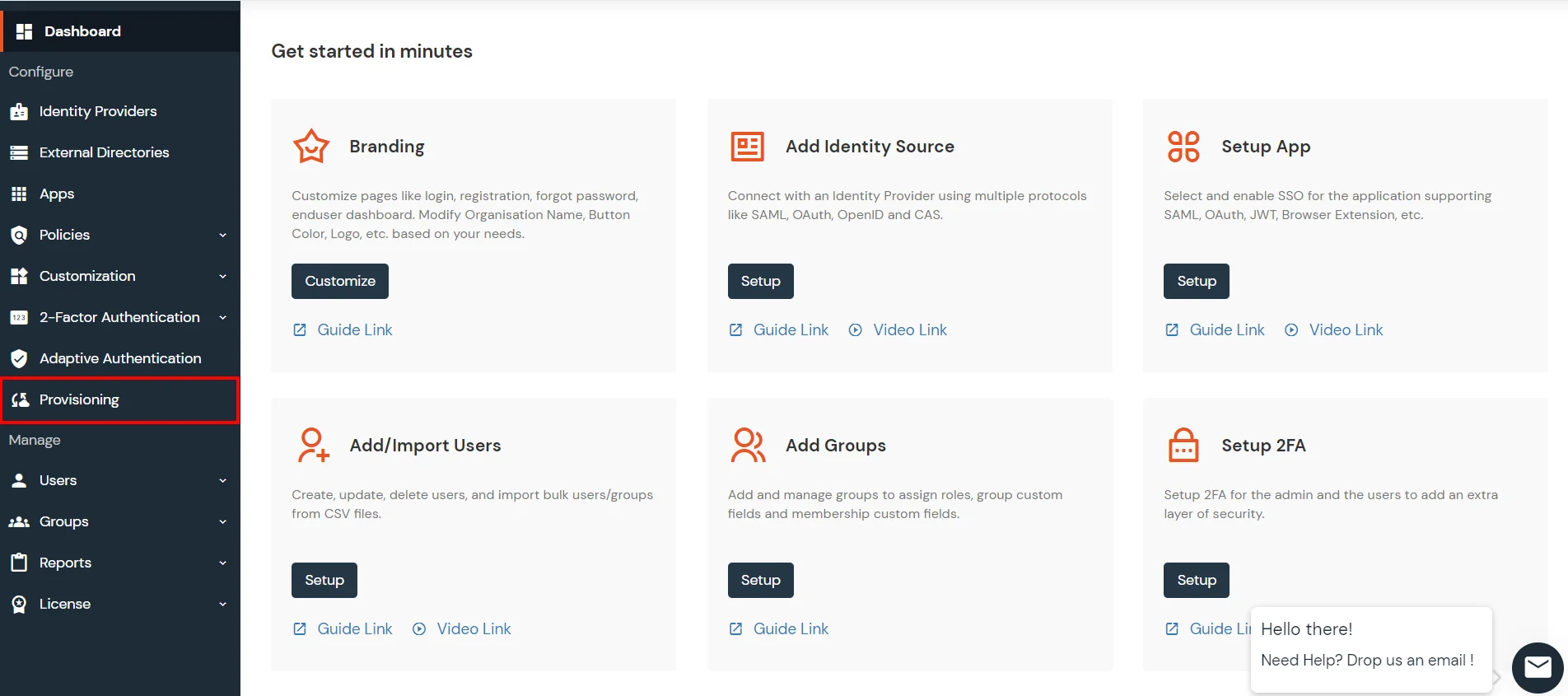
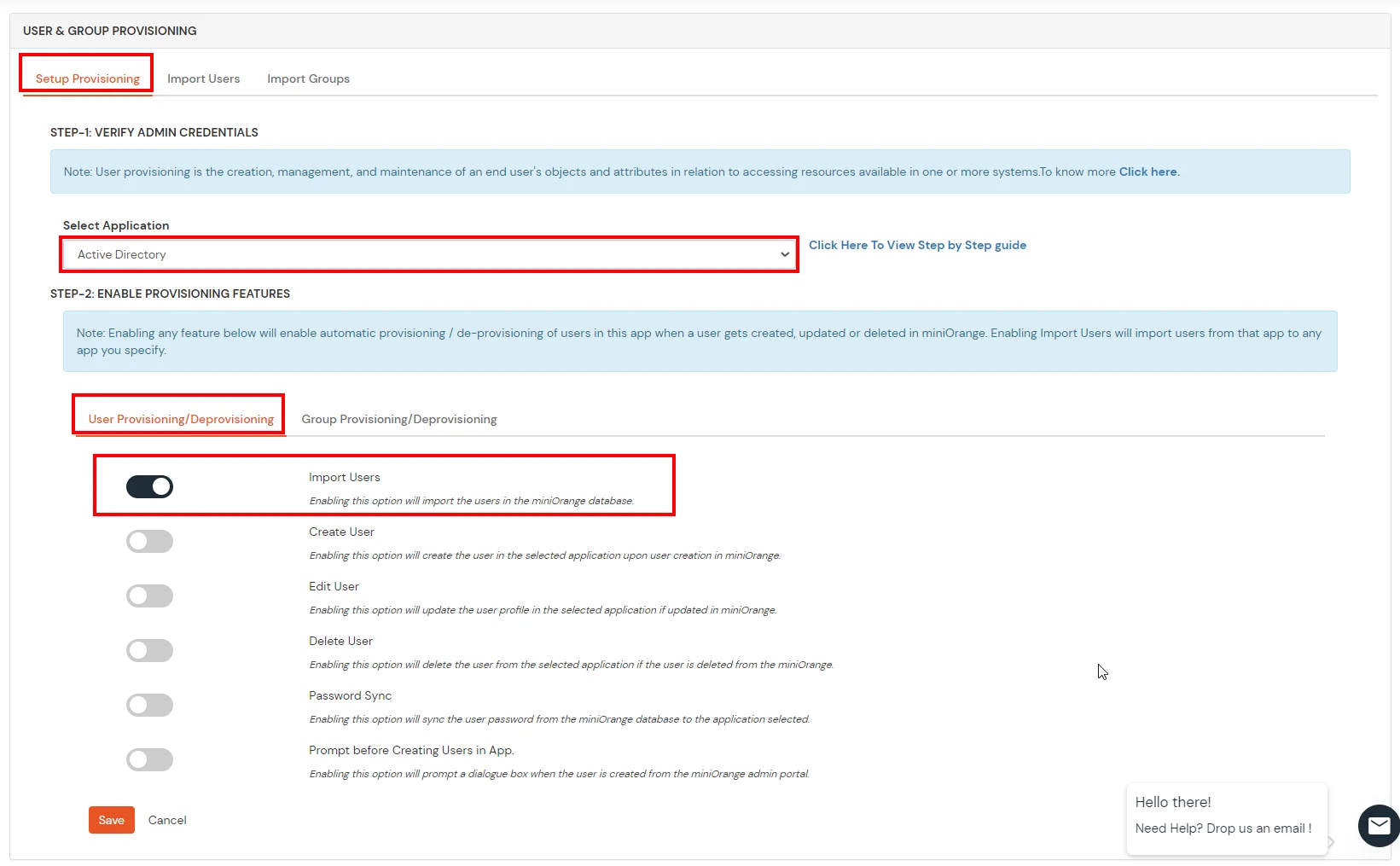
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Azure AD, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
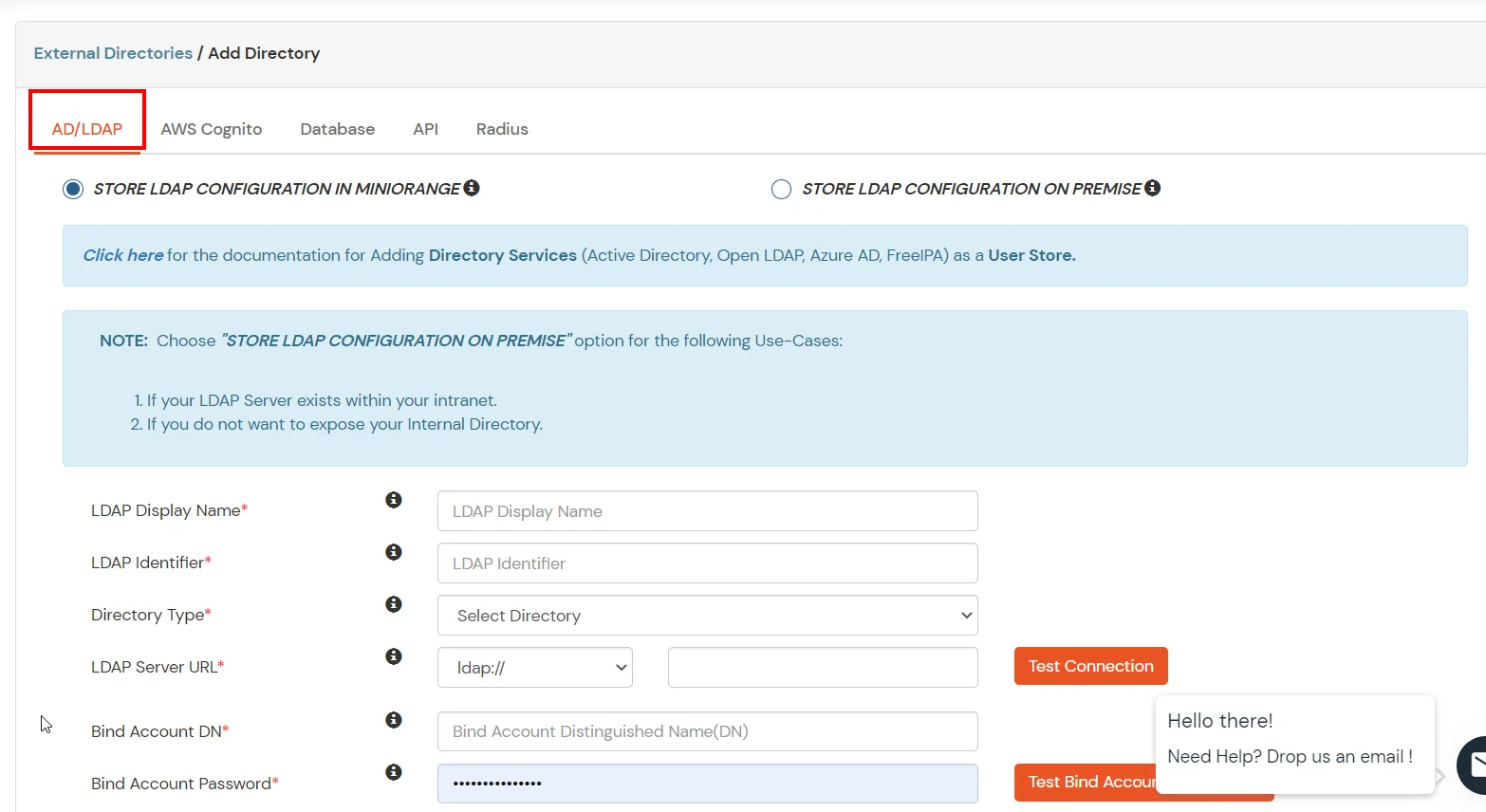
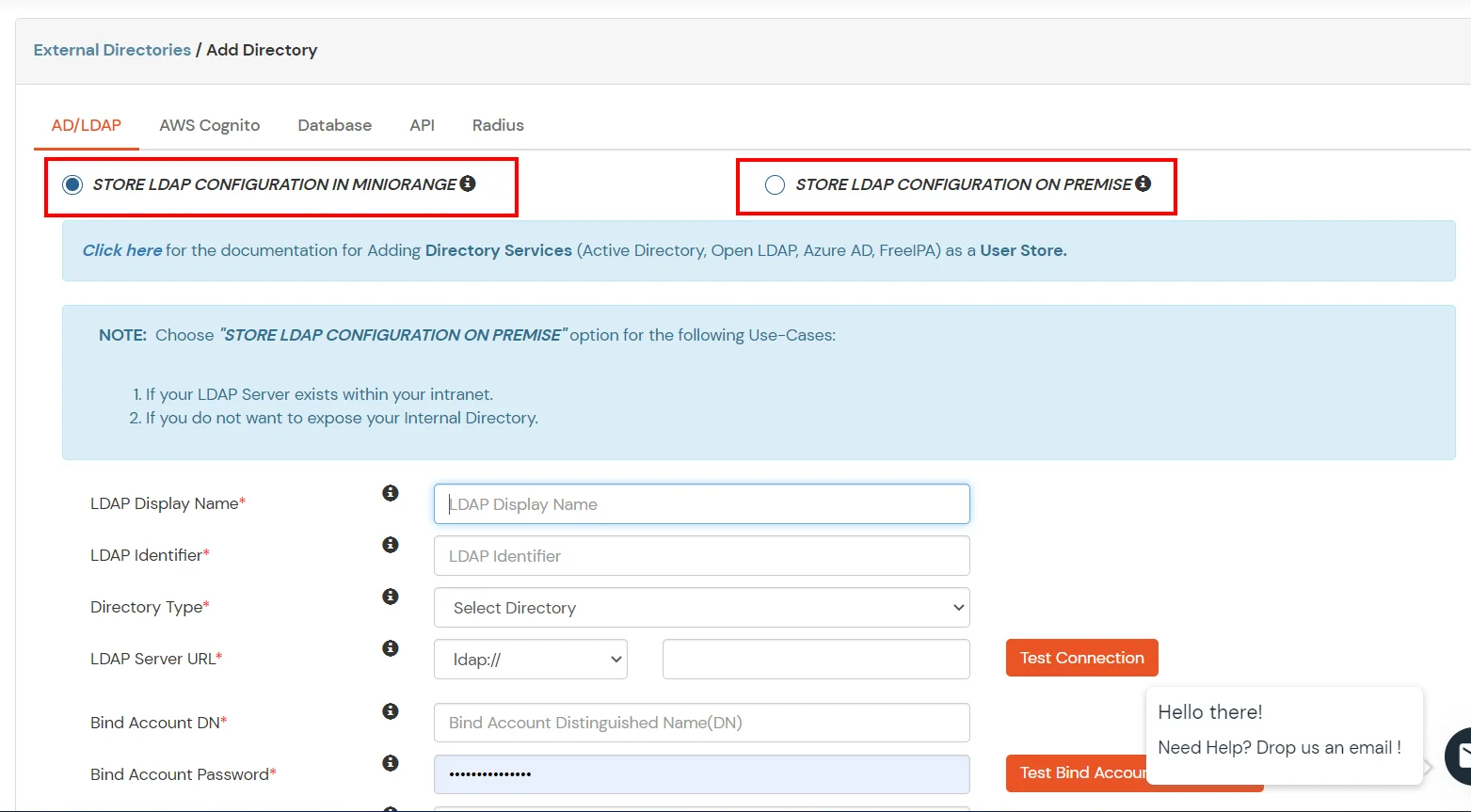
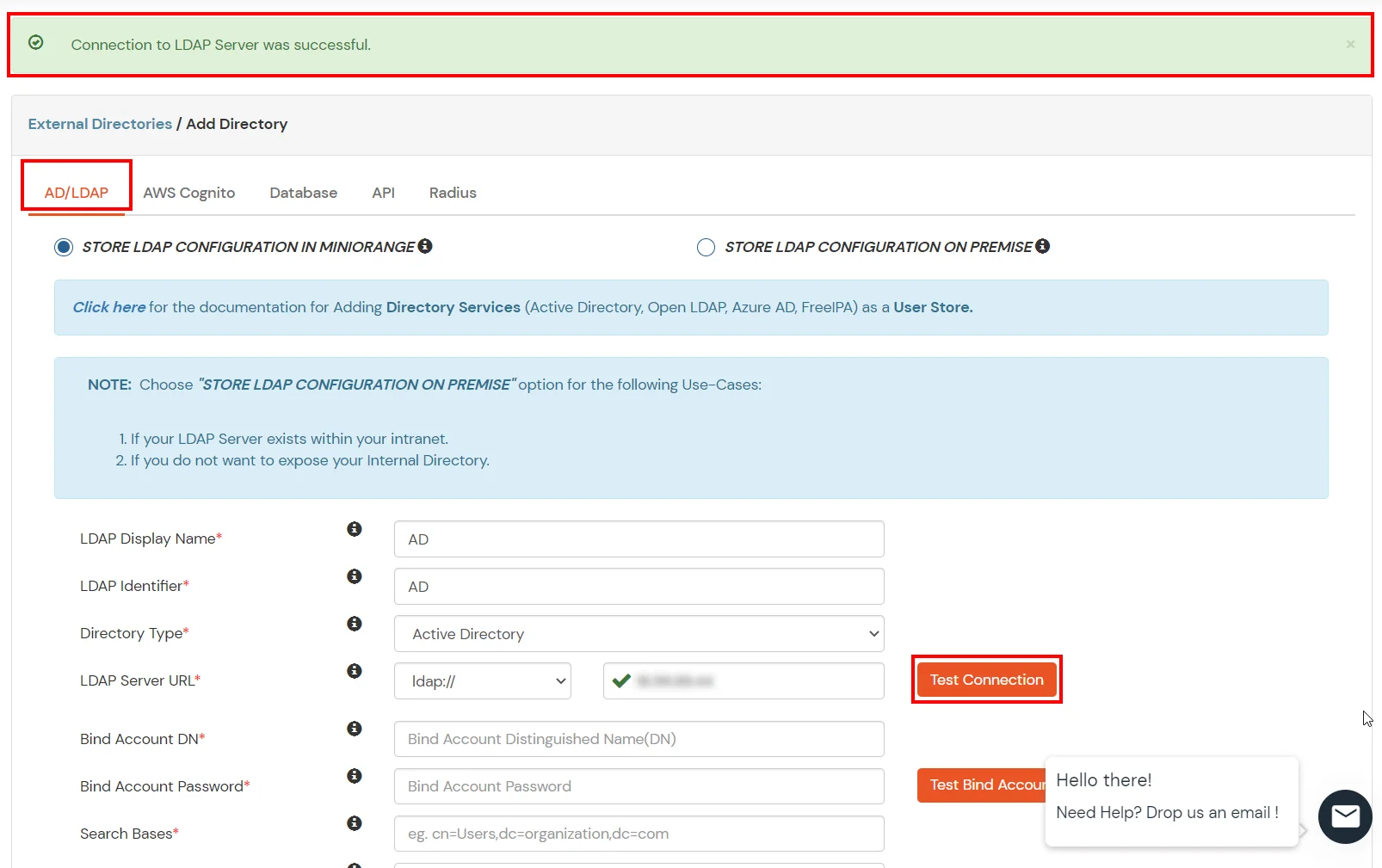
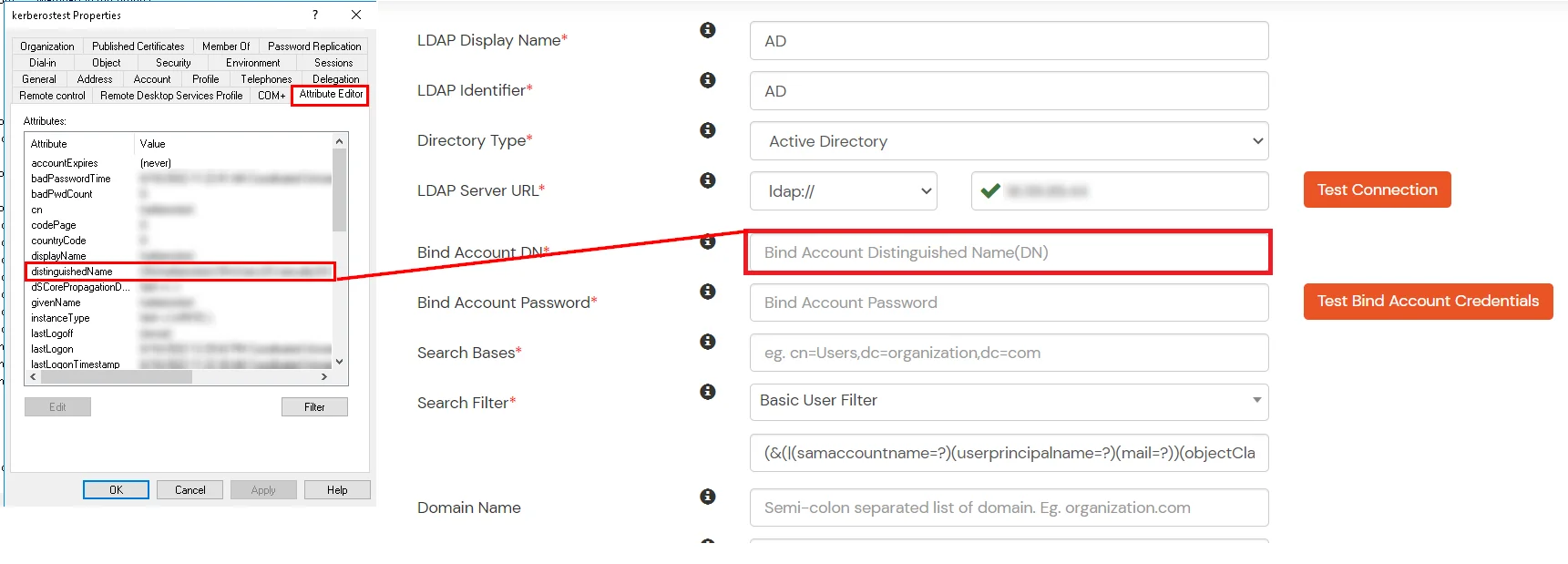
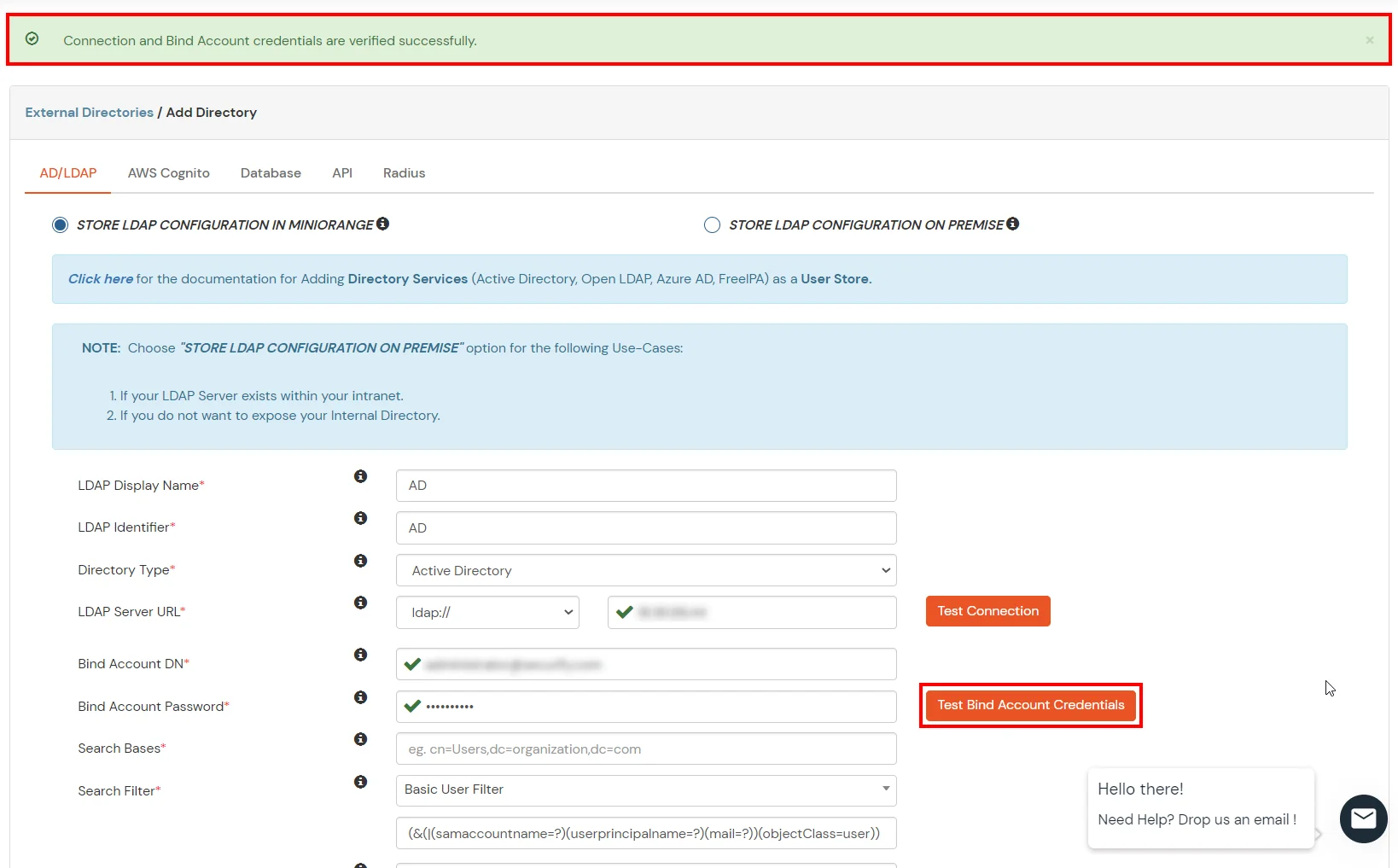
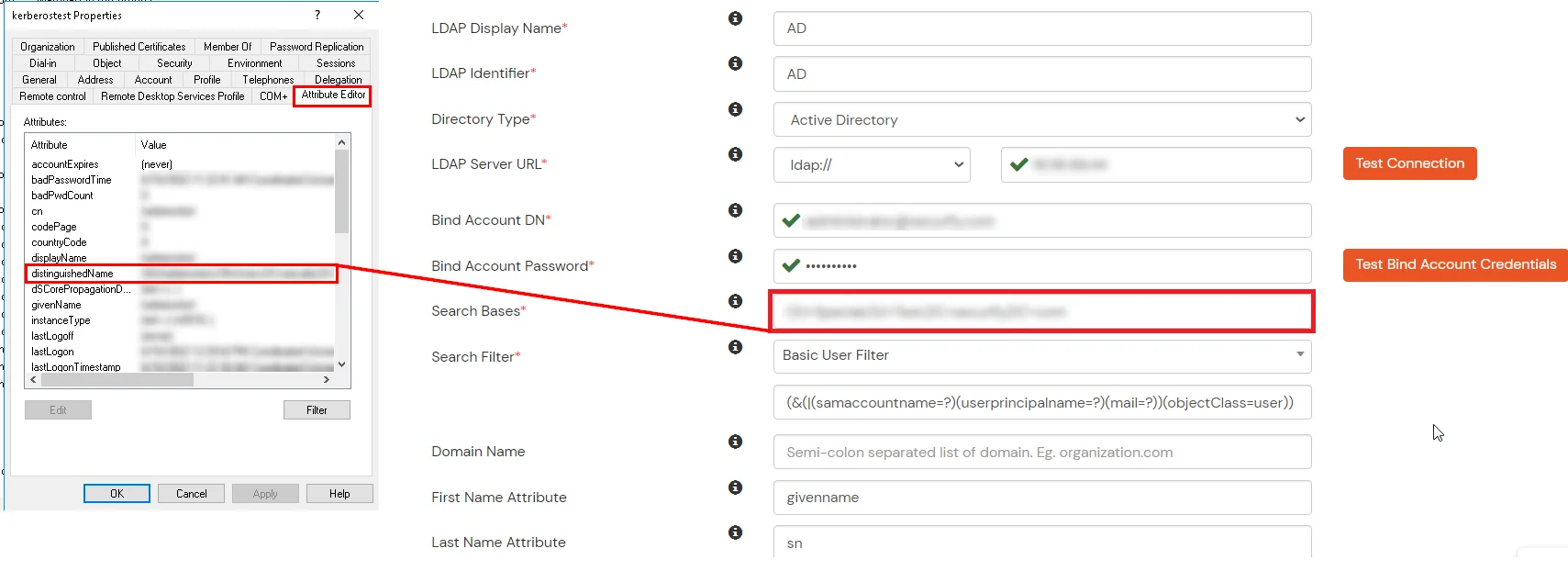
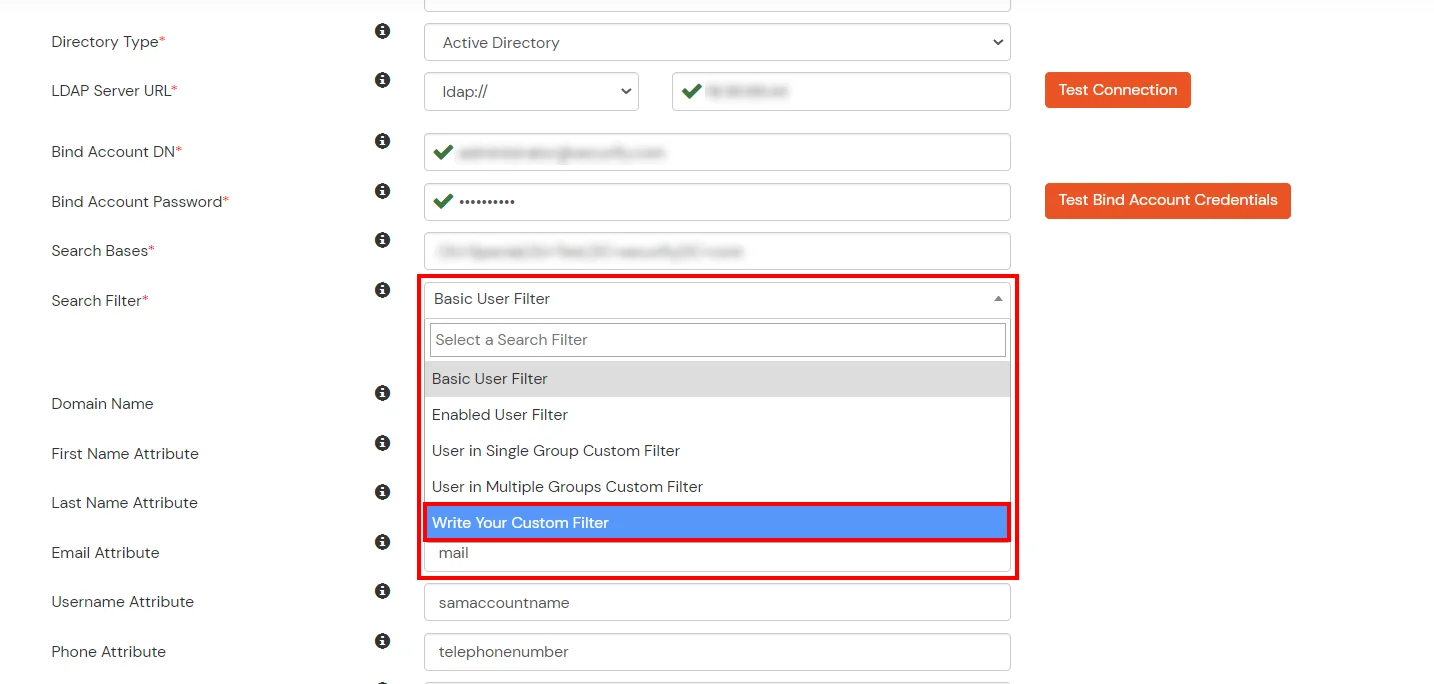
Configure your existing directories such as Microsoft Active Directory, Azure, OpenLDAP, etc.
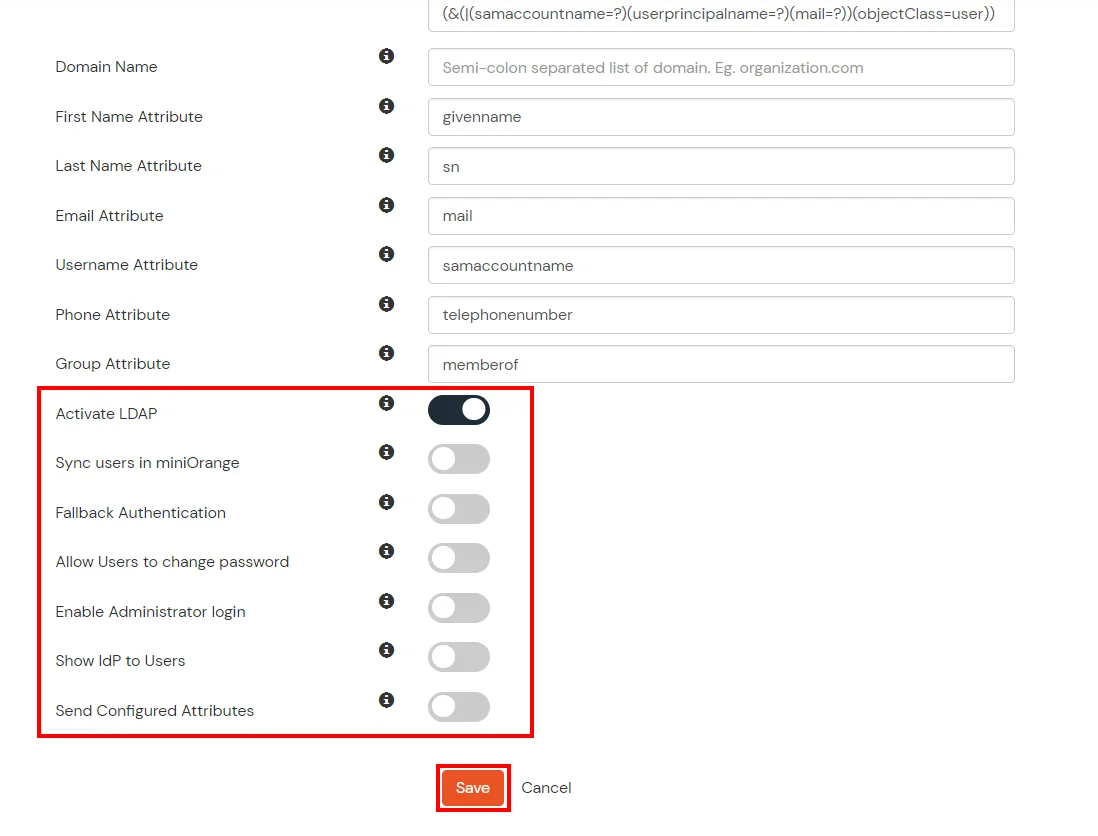
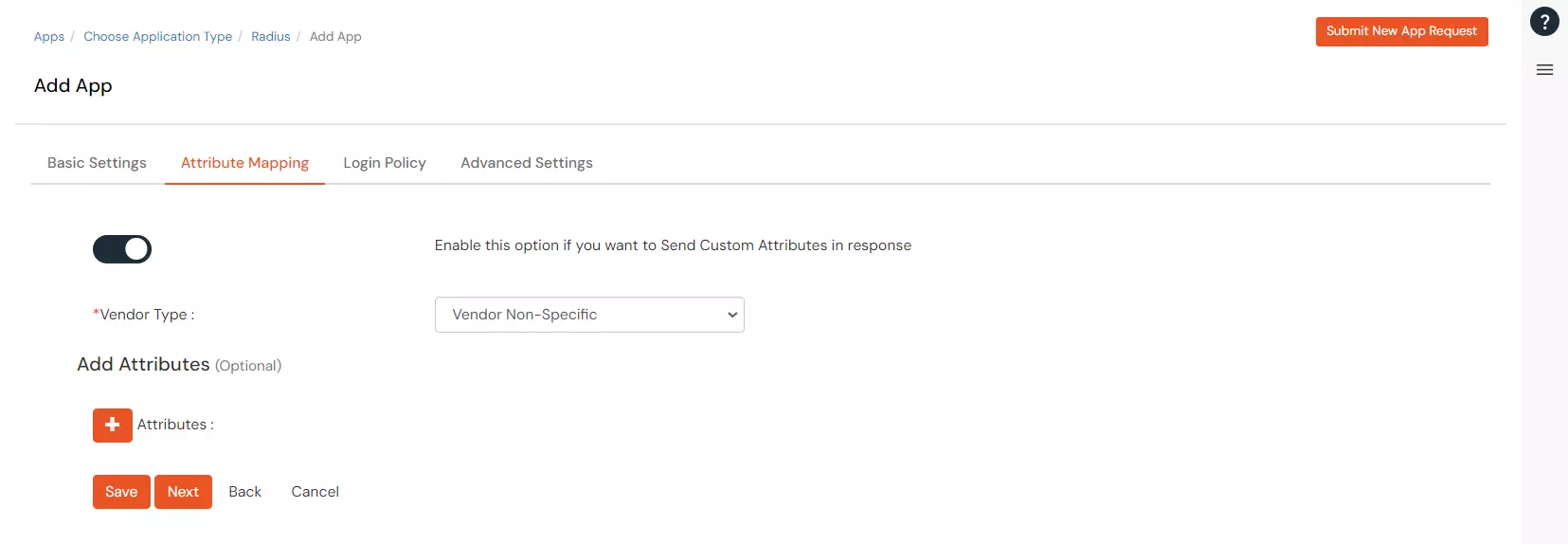
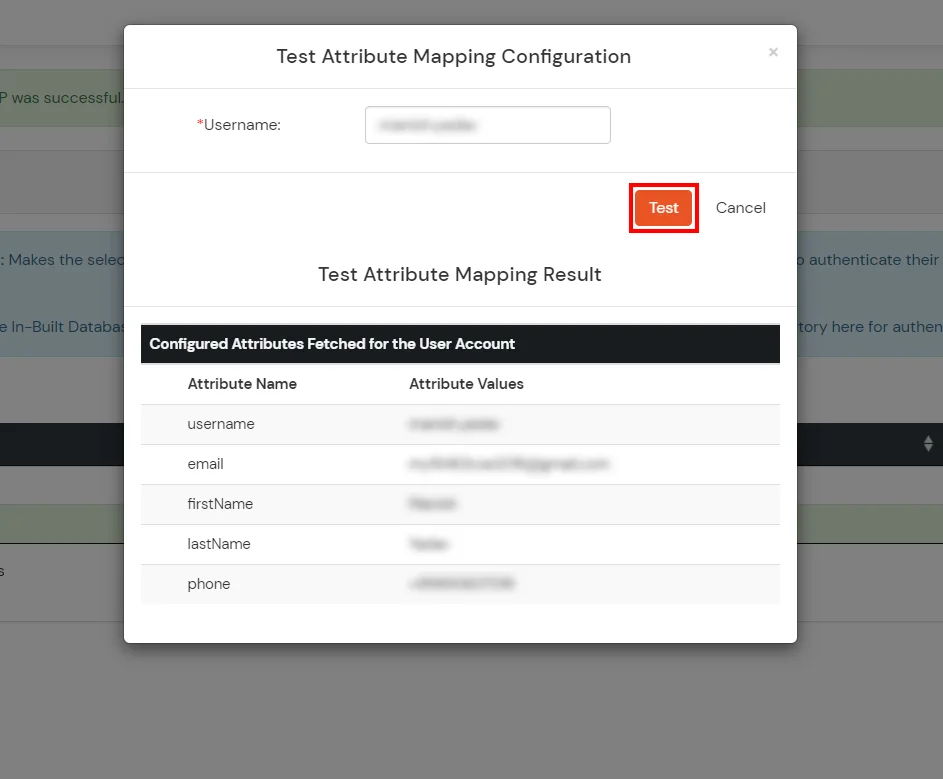
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute | Description |
|---|---|
| Activate LDAP | All user authentications will be done with LDAP credentials if you Activate it |
| Sync users in miniOrange | Users will be created in miniOrange after authentication with LDAP |
| Fallback Authentication | If LDAP credentials fail then user will be authenticated through miniOrange |
| Allow users to change password | This allows your users to change their password. It updates the new credentials in your LDAP server |
| Enable administrator login | On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users | If you enable this option, this IdP will be visible to users |
| Send Configured Attributes | If you enable this option, then only the attributes configured below will be sent in attributes at the time of login |
Refer our guide to setup LDAPS on windows server.
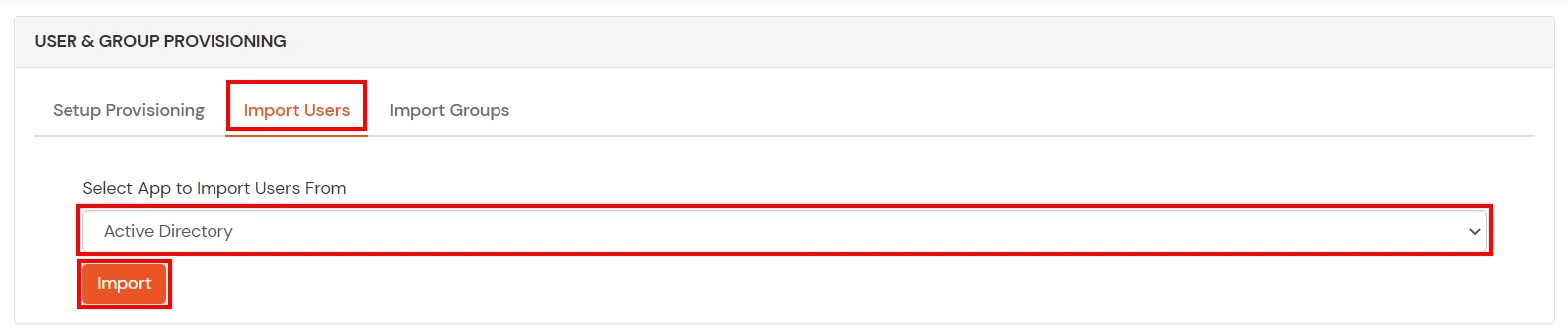
Note: Below steps are used to enable one time or manual sync. To enable sync on scheduled basis, you should use LDAP gateway module. Read more and download the LDAP gateway module.
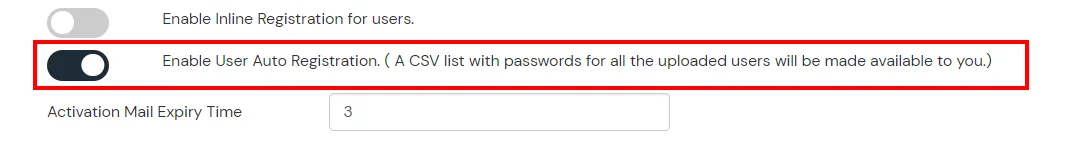
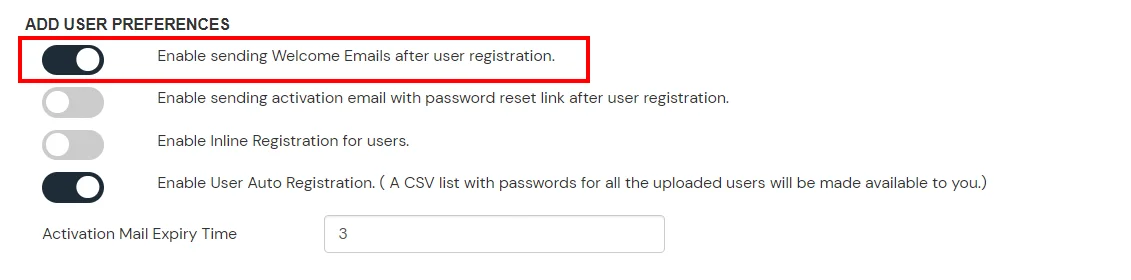
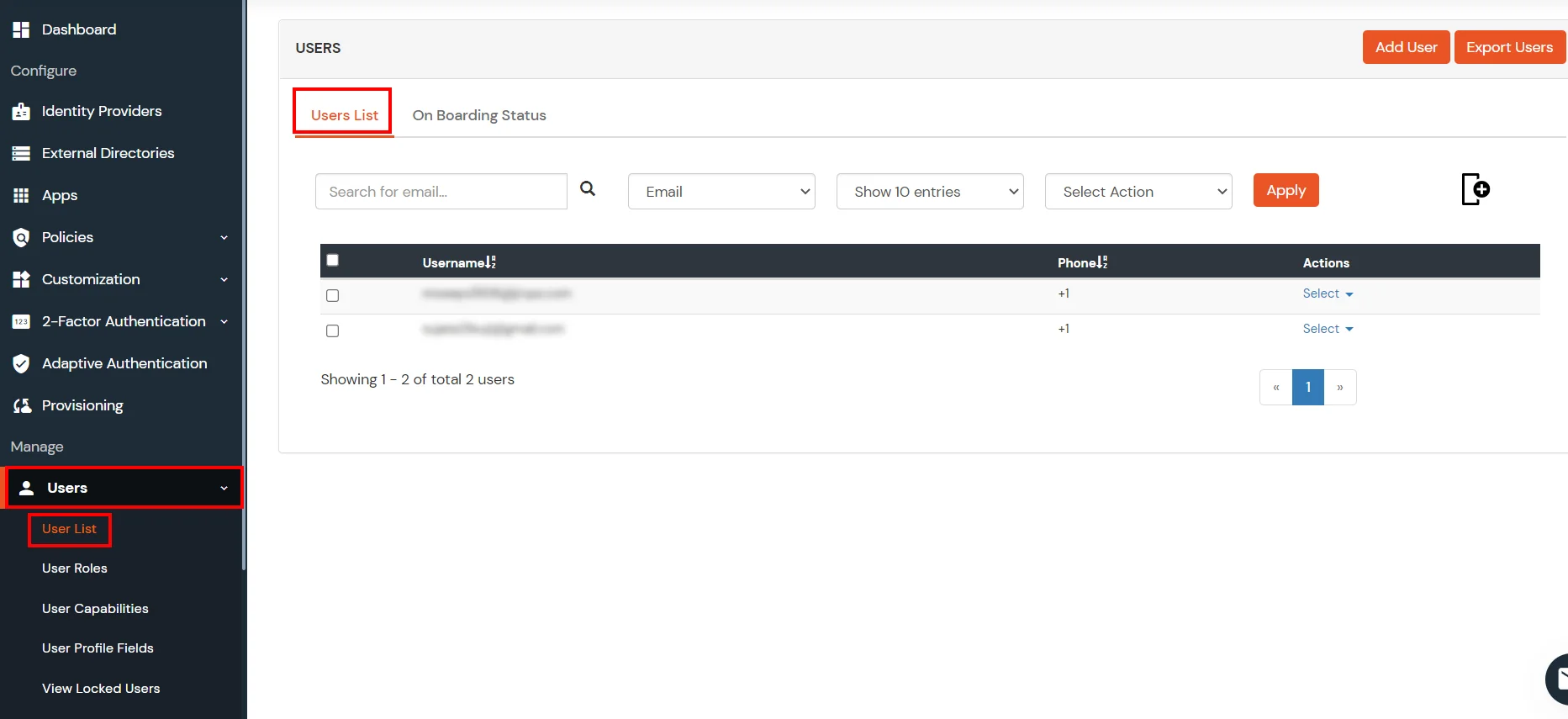
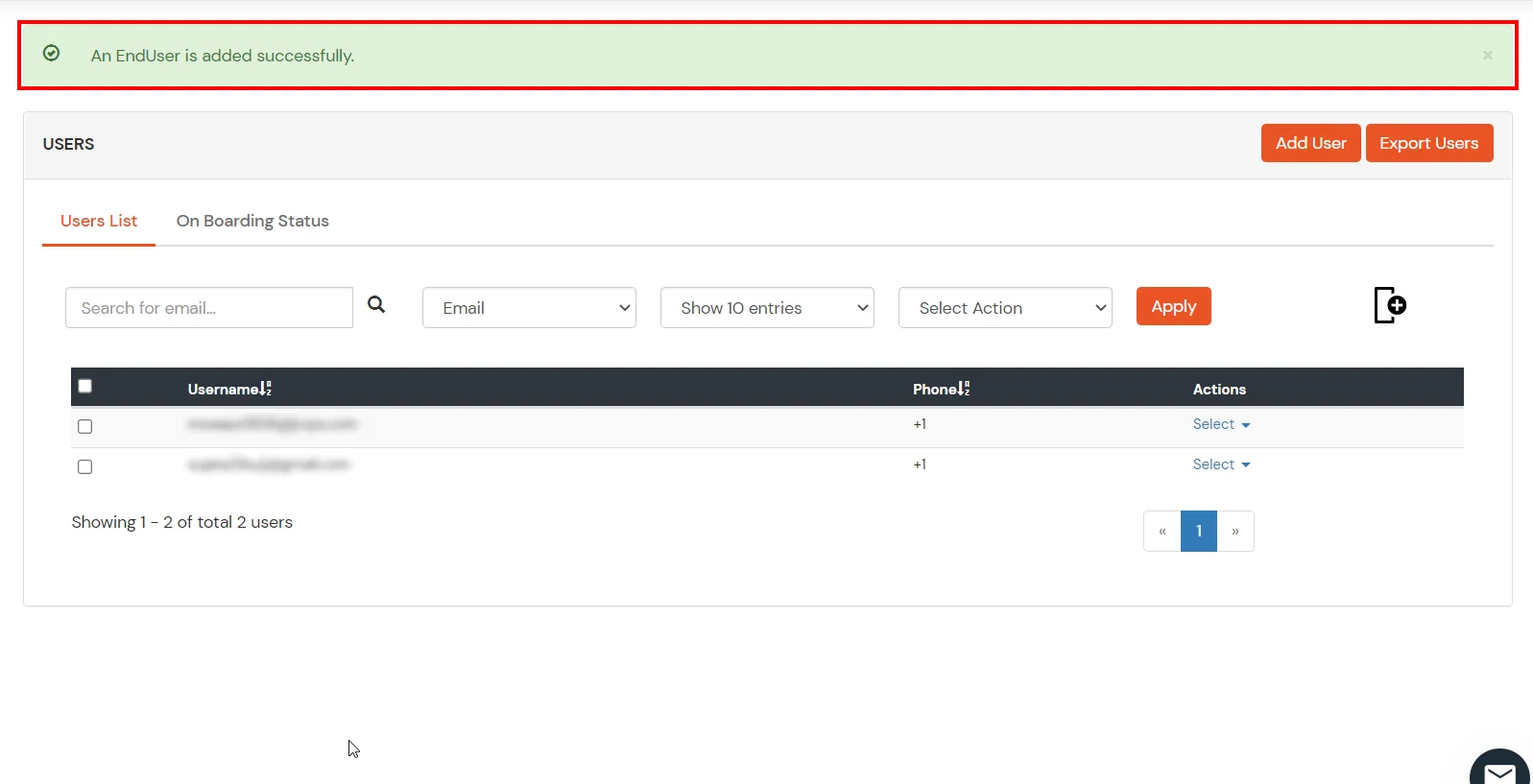
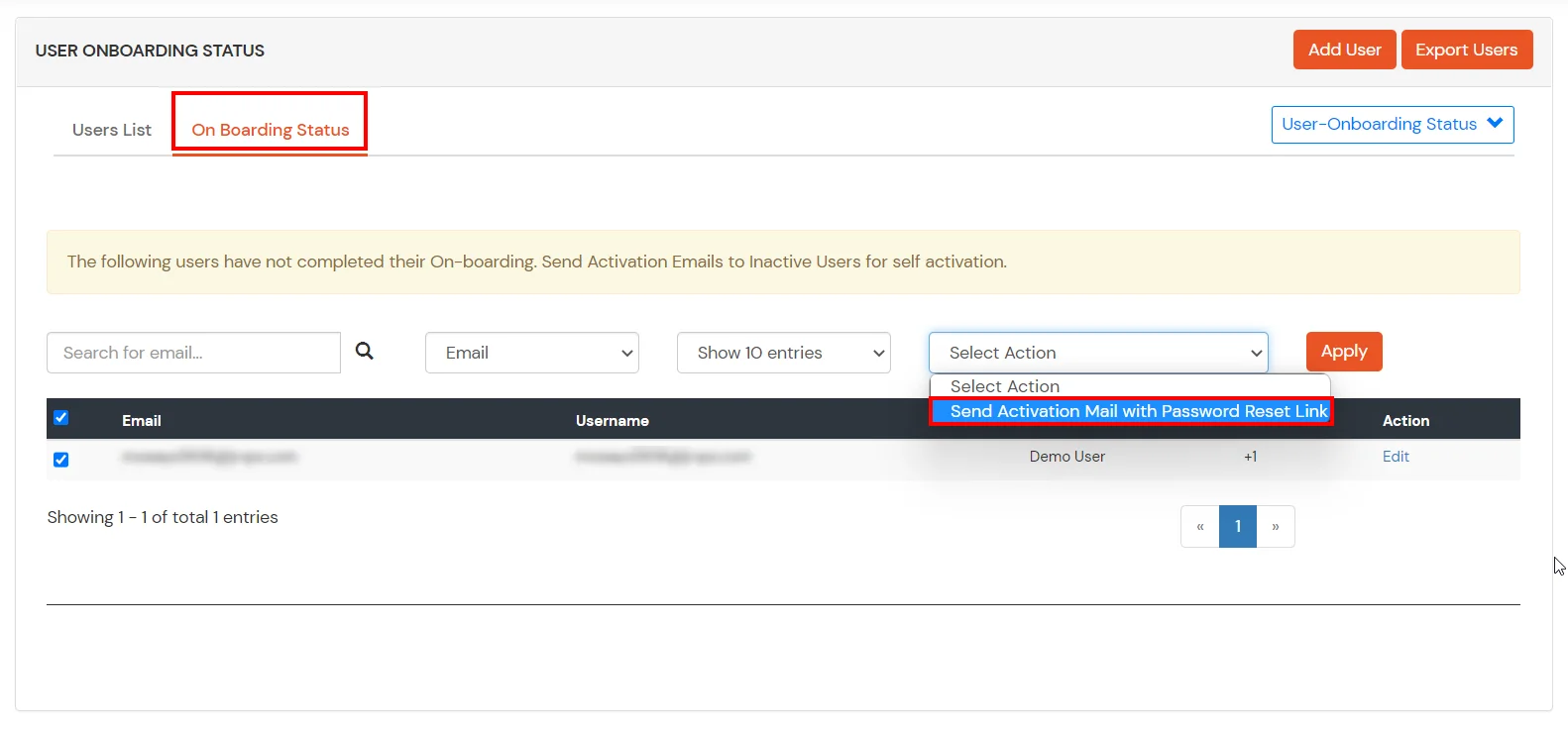
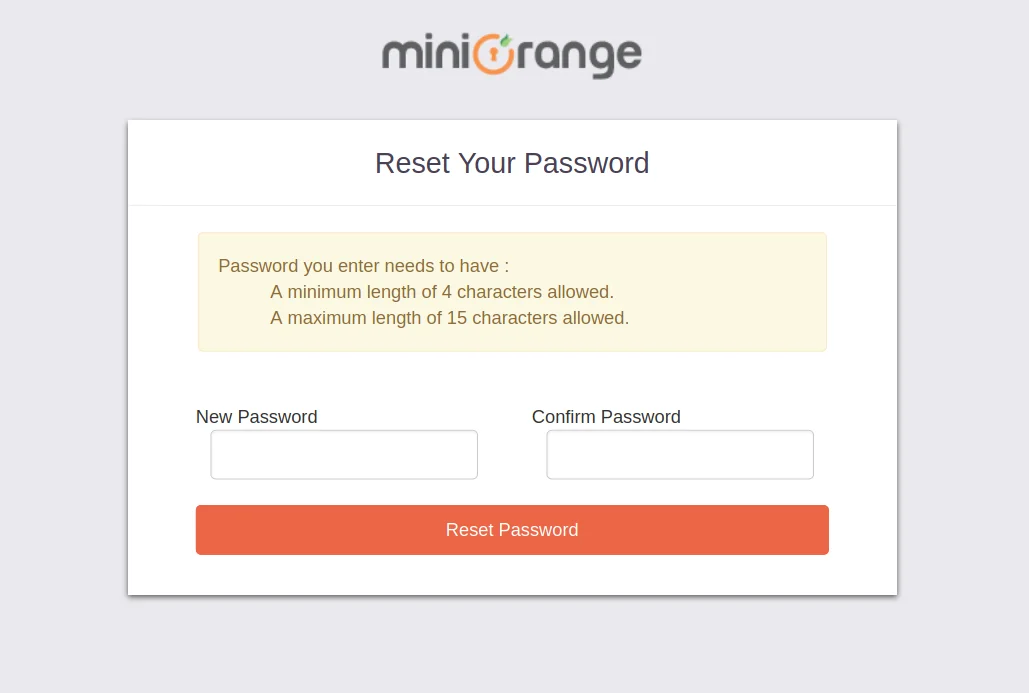
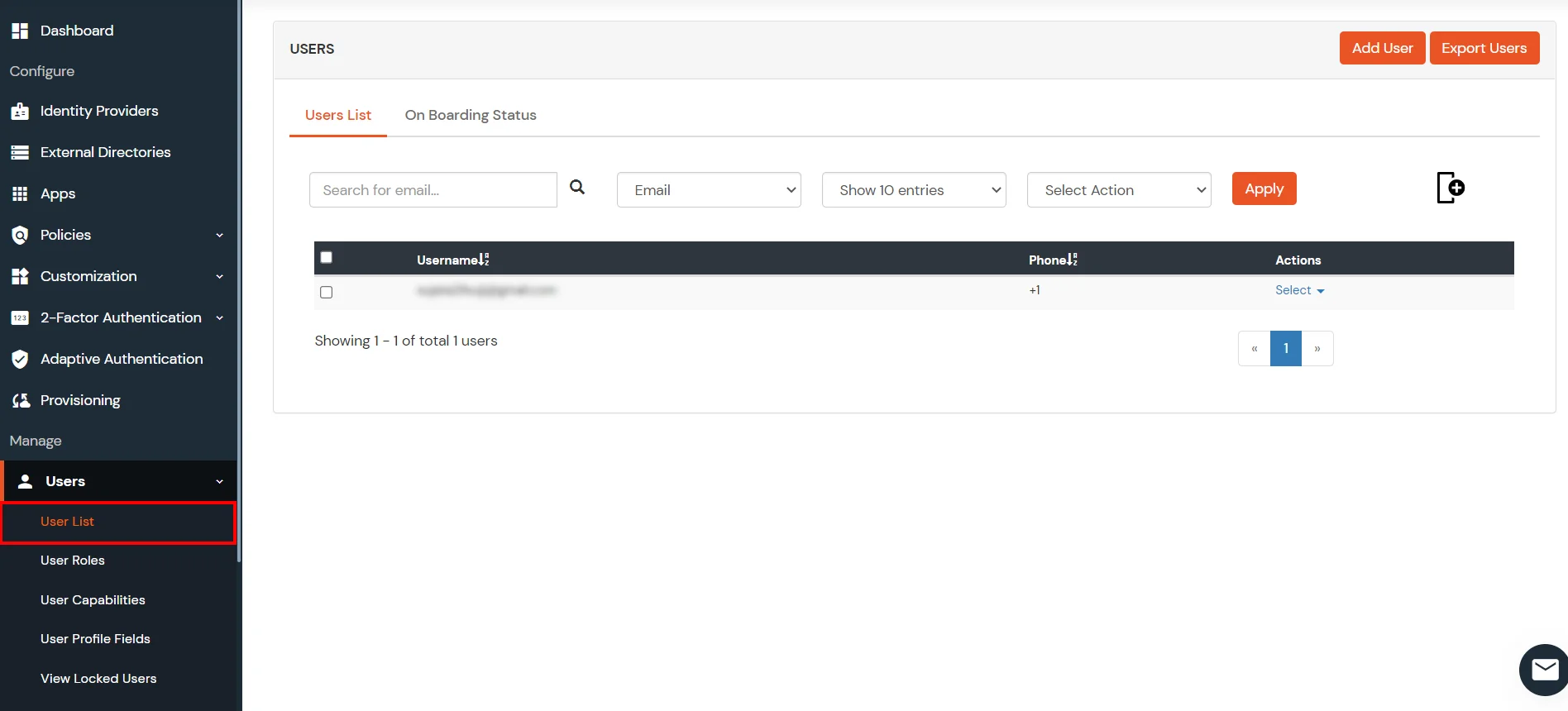
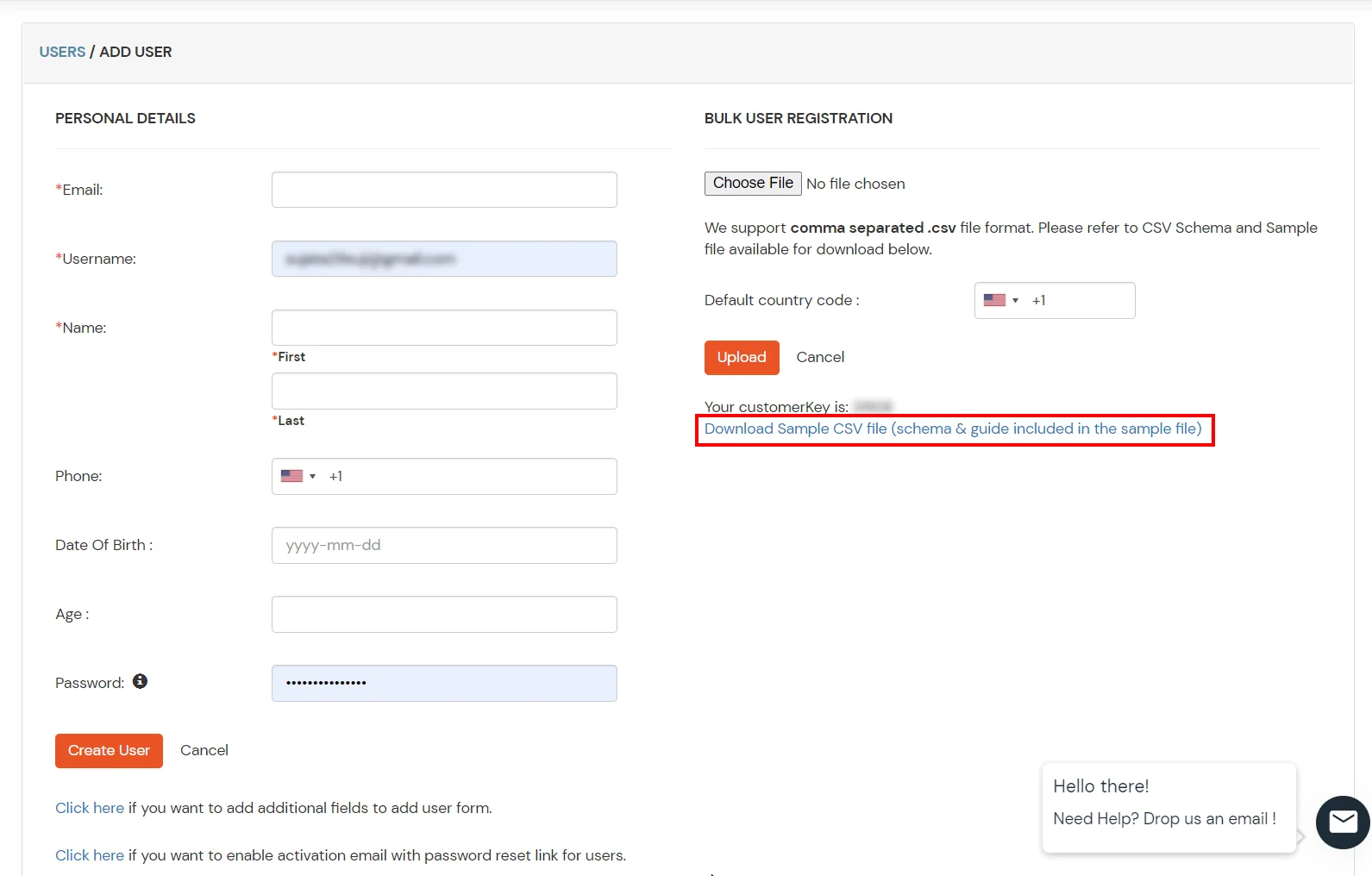
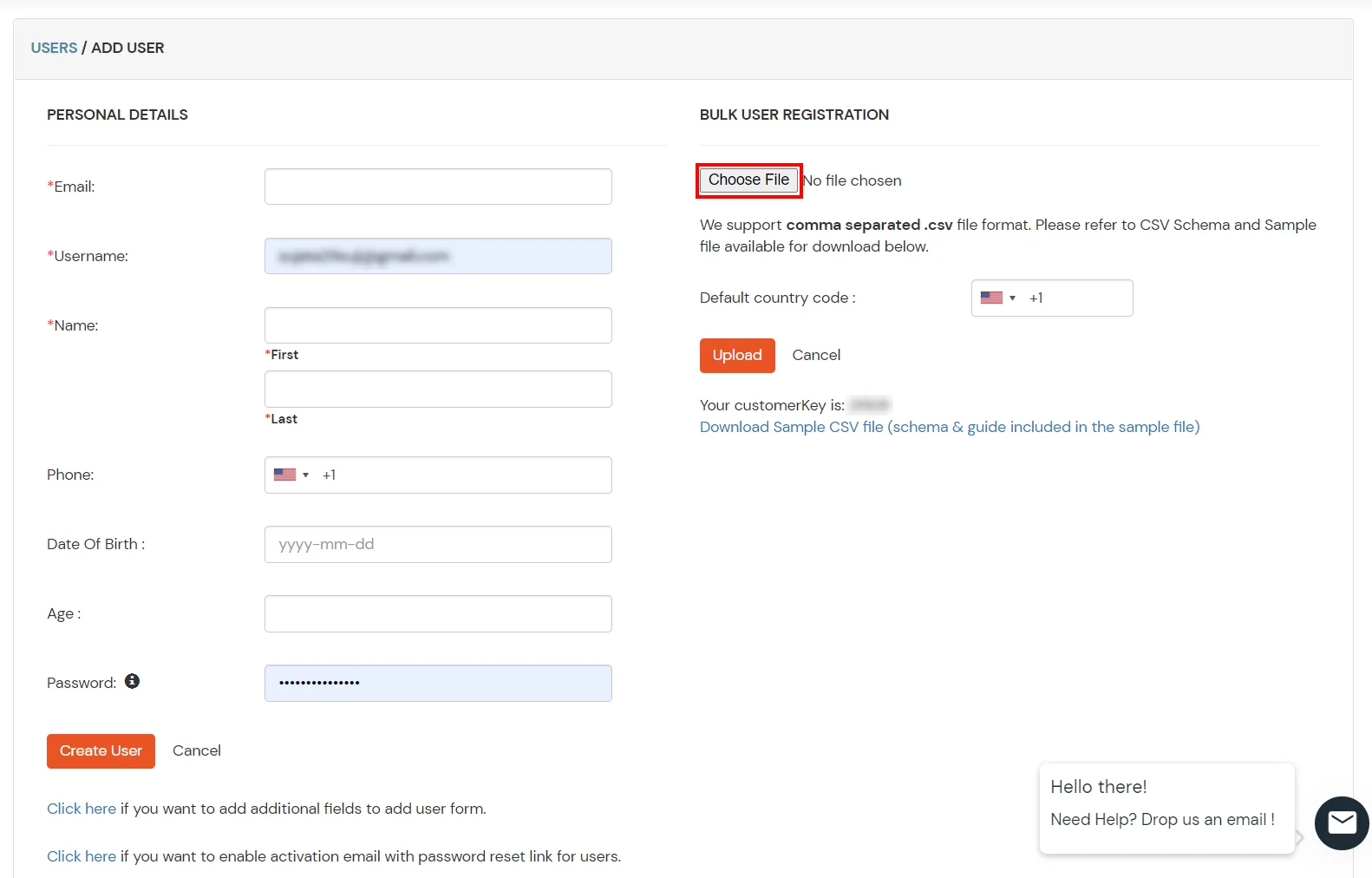
1. Create User in miniOrange
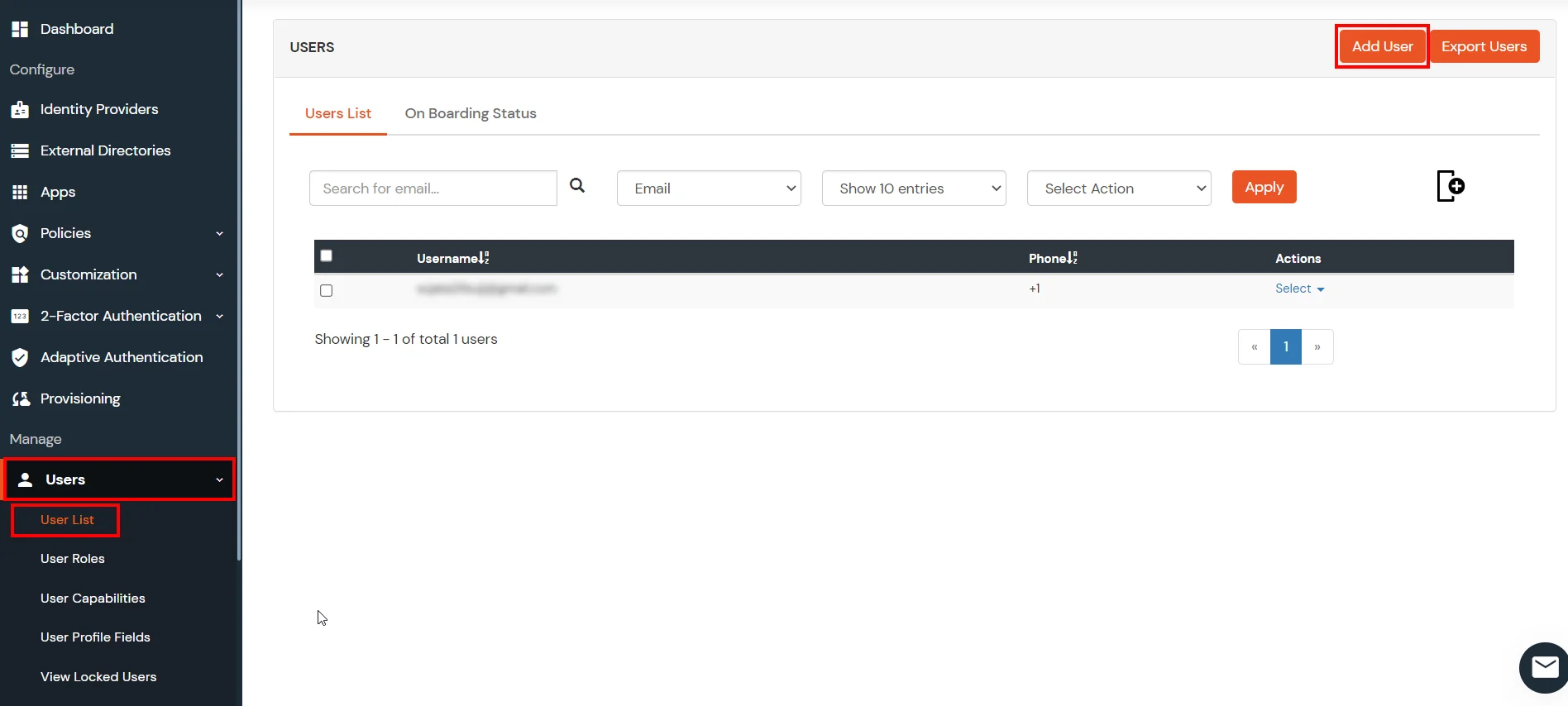
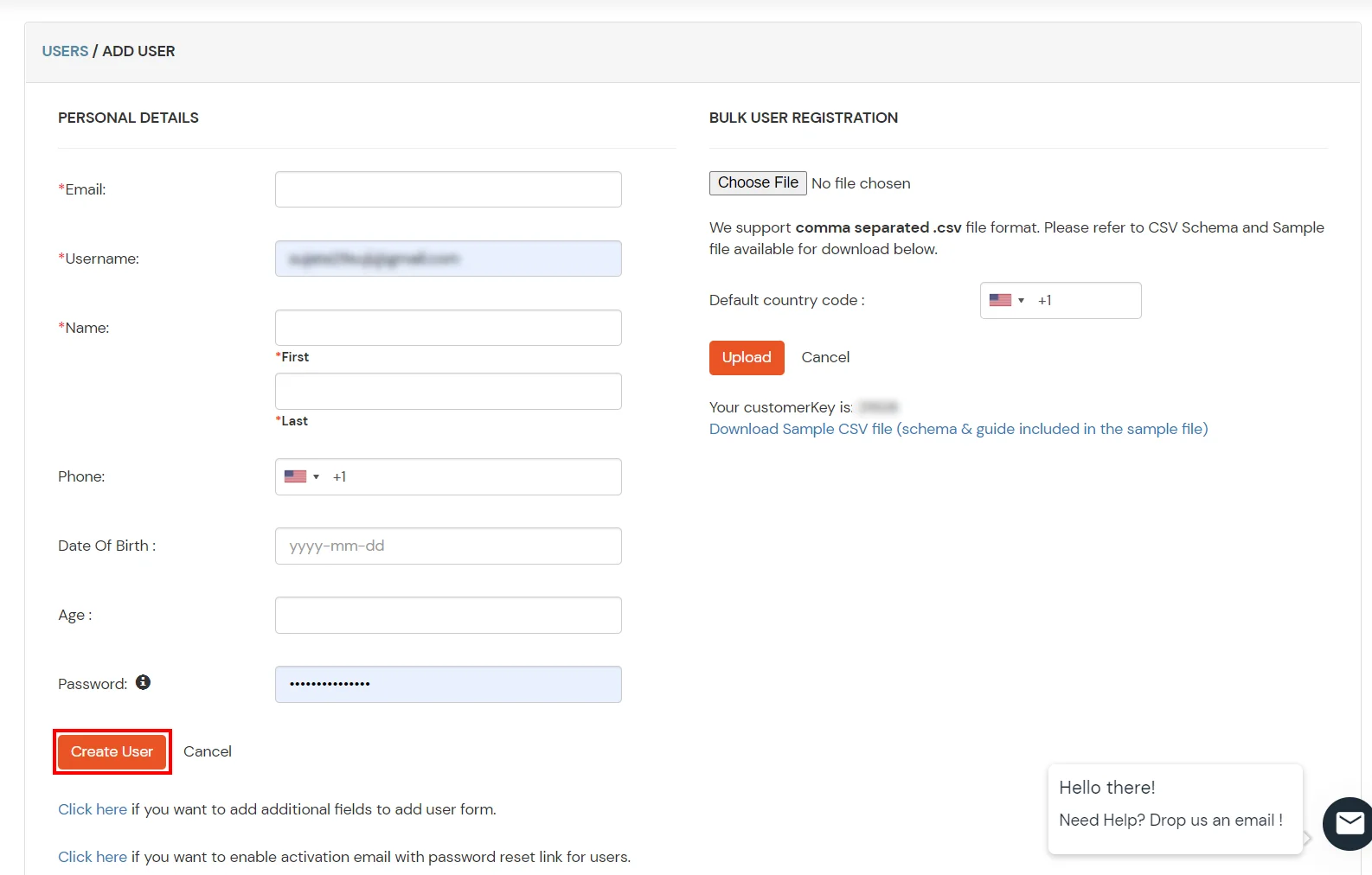
2. Bulk Upload Users in miniOrange via Uploading CSV File.
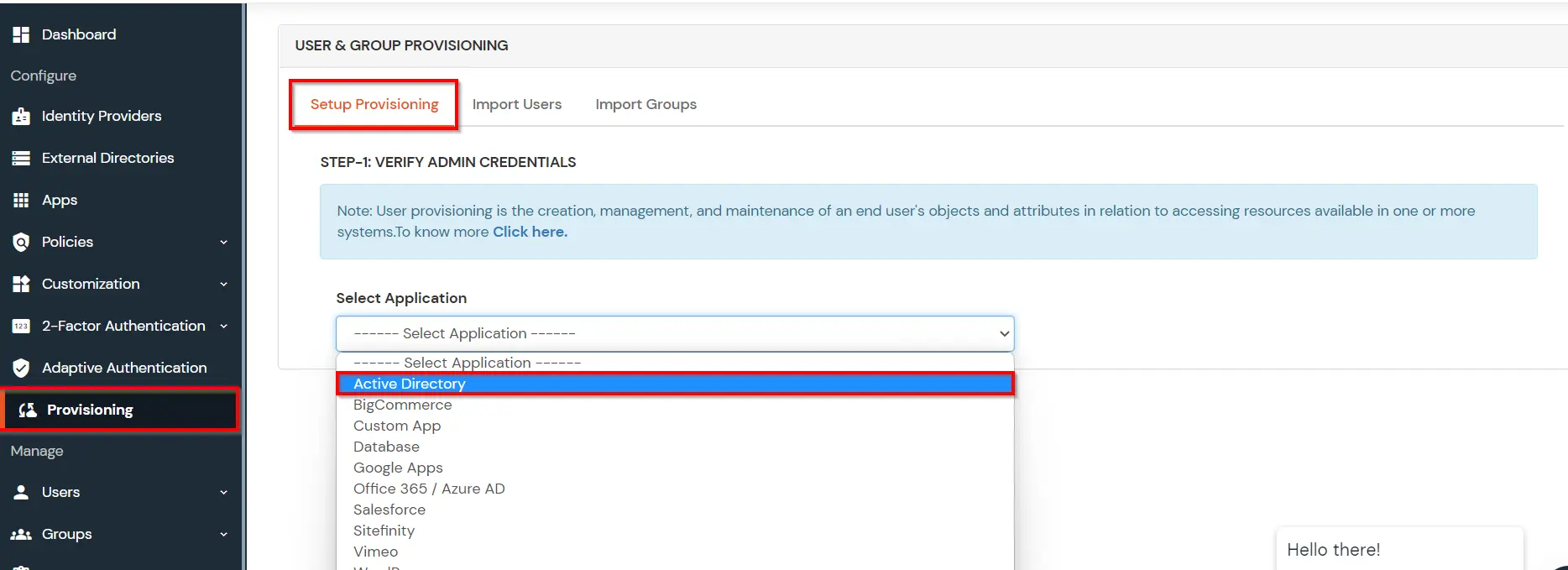
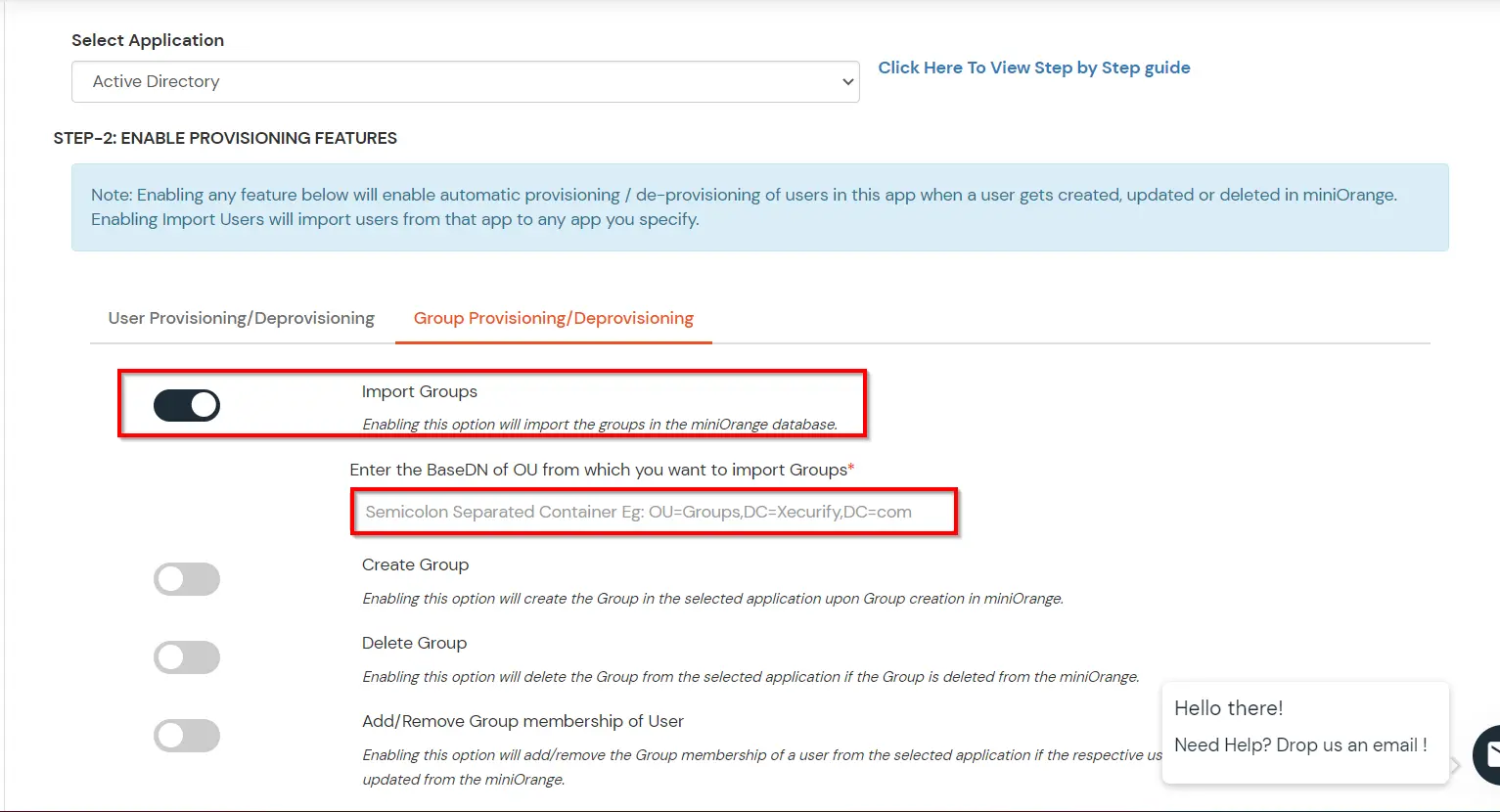
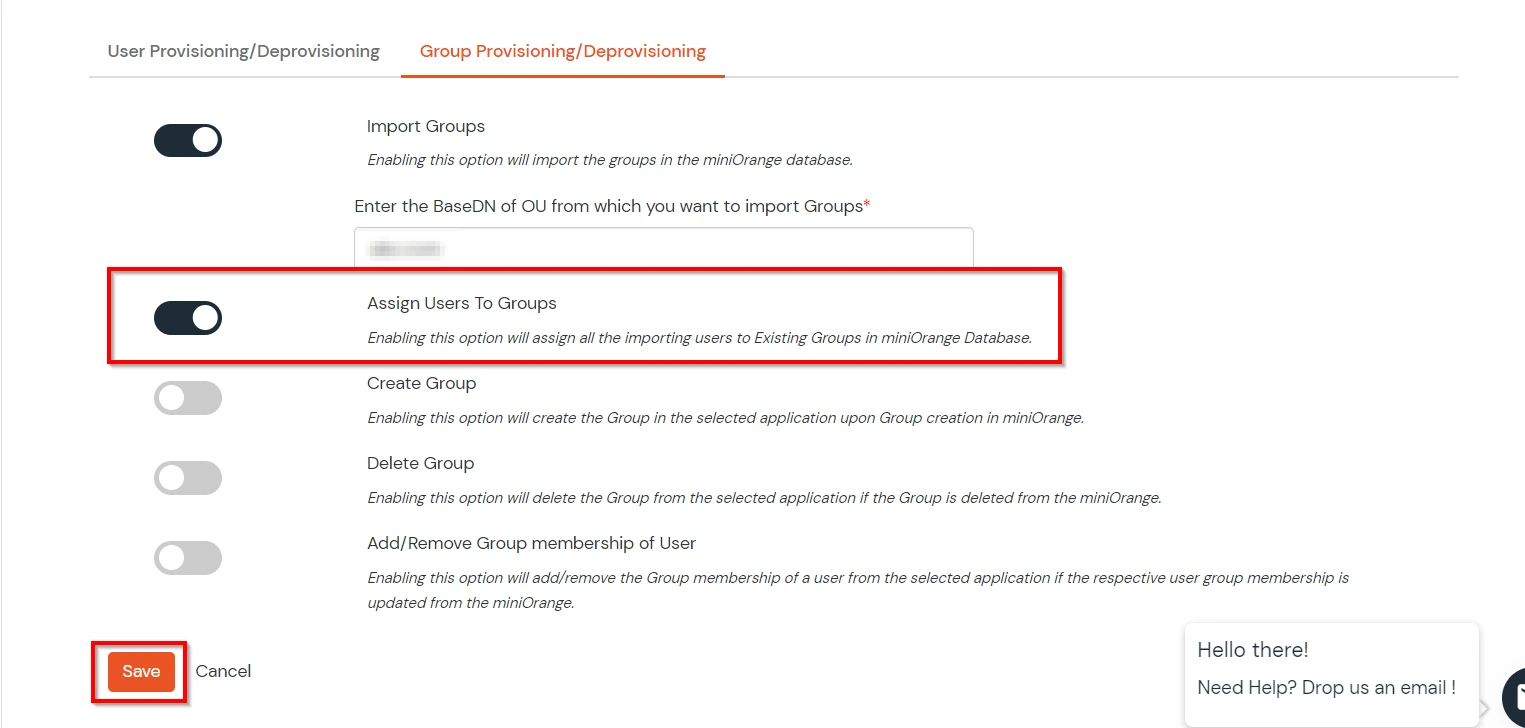
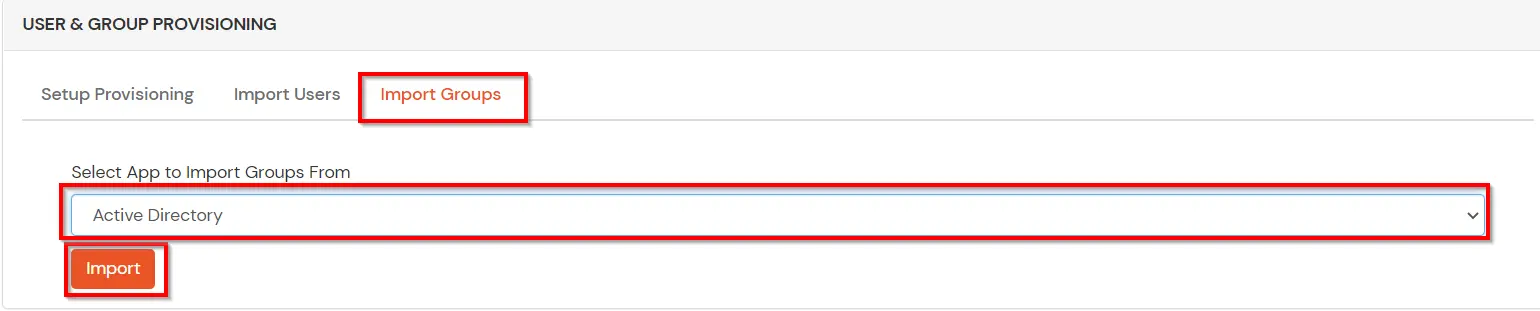
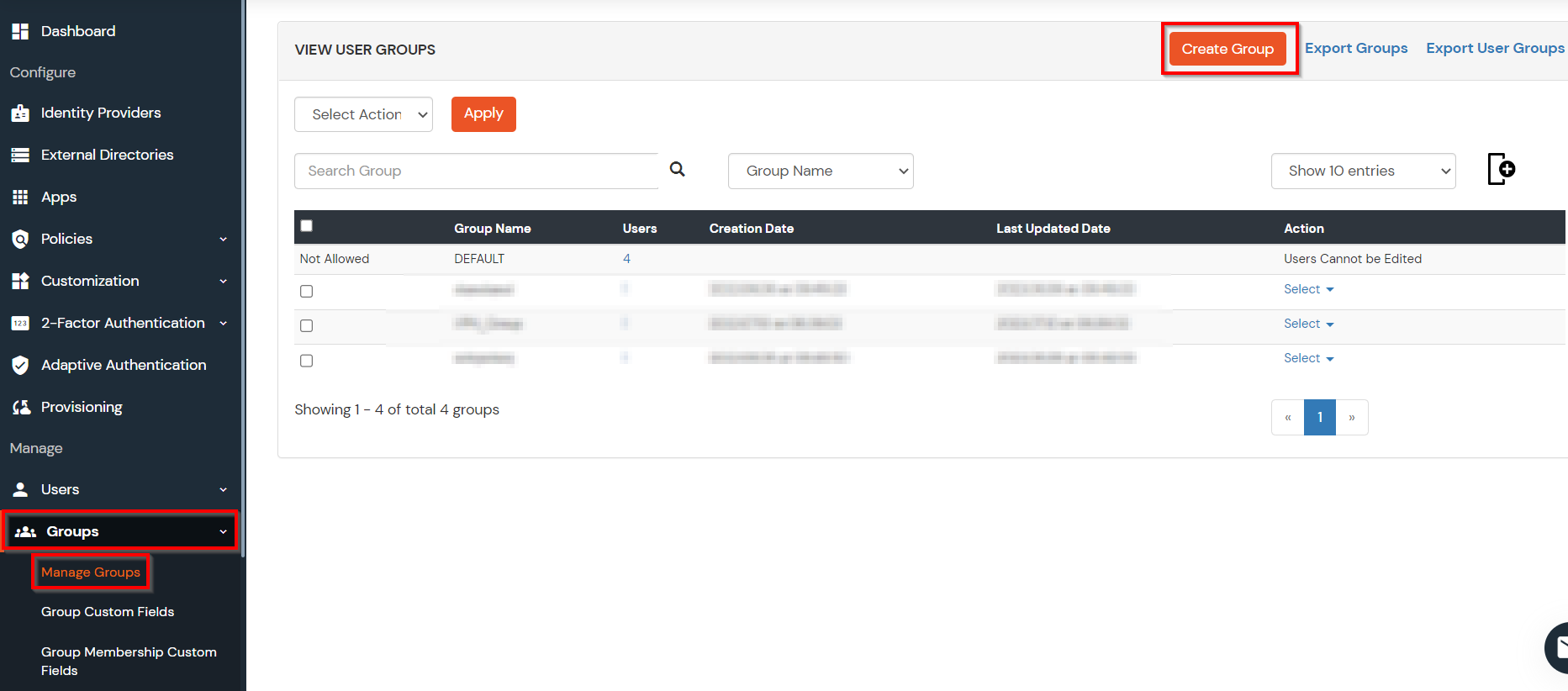
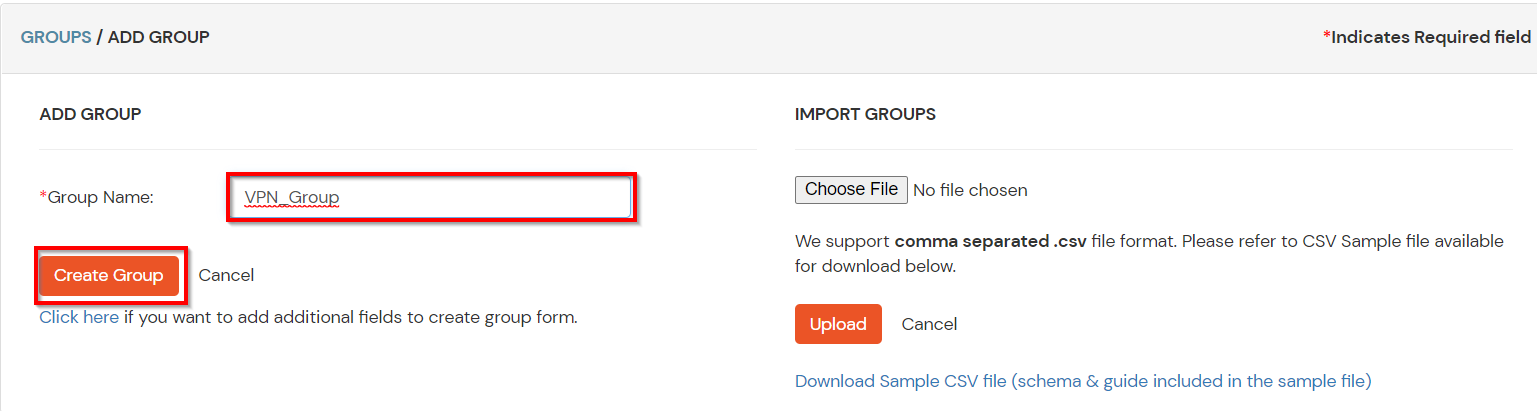
(The Active Directory Group Provisioning (Sync) setup is done. Now, whenever a user is created or modified in LDAP server and if the Assign Users to groups is enabled, then user group attribute from the LDAP server will be automatically synced and the user group will be assigned or changed accordingly in miniOrange.)
Note: You can follow this guide, if you want to customize and enroll MFA for end users.
Multi-Factor Authentication (MFA) is an authentication method that requires the user to authenticate themselves for two or more factors, in order to gain access to company resources, applications, or a VPN (Cisco Meraki Client VPN in this case). Enabling Multi-Factor Authentication (MFA) means that users need to provide additional verification factors apart from their username and passwords thus increasing the security of the organization's resources. Checkout more about Multi-Factor Authentication (MFA) here.
Depending on the VPN client, 2-factor authentication can take two forms..
miniOrange supports multiple 2FA/MFA authentication methods for Cisco Meraki Client VPN secure access such as, Push Notification, Soft Token, Microsoft / Google Authenticator etc.
| Authentication Type | Method | Supported |
|---|---|---|
| miniOrange Authenticator | Soft Token | |
| miniOrange Push Notification | ||
| Mobile Token | Google Authenticator | |
| Microsoft Authenticator | ||
| Authy Authenticator | ||
| SMS | OTP Over SMS | |
| SMS with Link | ||
| OTP Over Email | ||
| Email with Link | ||
| Call Verification | OTP Over Call | |
| Hardware Token | YubiKey Hardware Token | |
| Display Hardware Token |
x
Thank you for your response. We will get back to you soon.
Please enter you work email-id
Our Other Identity & Access Management Products