Configure Salesforce SAML Single Sign-On (SSO)
Streamline the configuration of Salesforce SSO with this comprehensive setup guide provided by miniOrange. Our SAML Single Sign-On (SSO) solution enables seamless login to Salesforce Channels and various applications using a unified set of credentials. By enabling SSO for Salesforce, users can securely access Salesforce with just one click, eliminating the need to re-enter their username and password. Simplify your Salesforce authentication process and enhance security with miniOrange's user-friendly SSO solution.
With miniOrange Salesforce SSO, you can:
- Enable your users to automatically login to Salesforce
- Have centralized and easy access control of the users
- Connect easily with any external identity source like Azure AD, ADFS, Cognito, etc
Get Free Installation Help
miniOrange offers free help through a consultation call with our System Engineers to Install or Setup Salesforce SSO solution in your environment with 30-day free trial.
For this, you need to just send us an email at idpsupport@xecurify.com to book a slot and we'll help you in no time.
Supported SSO Features
miniOrange-Salesforce SAML integration supports the following features:
- SP Initiated SSO Login: Users can access their Salesforce account via a URL or bookmark. They will automatically be redirected to the miniOrange portal for log in. Once they've signed on, they'll be automatically redirected and logged into Salesforce.
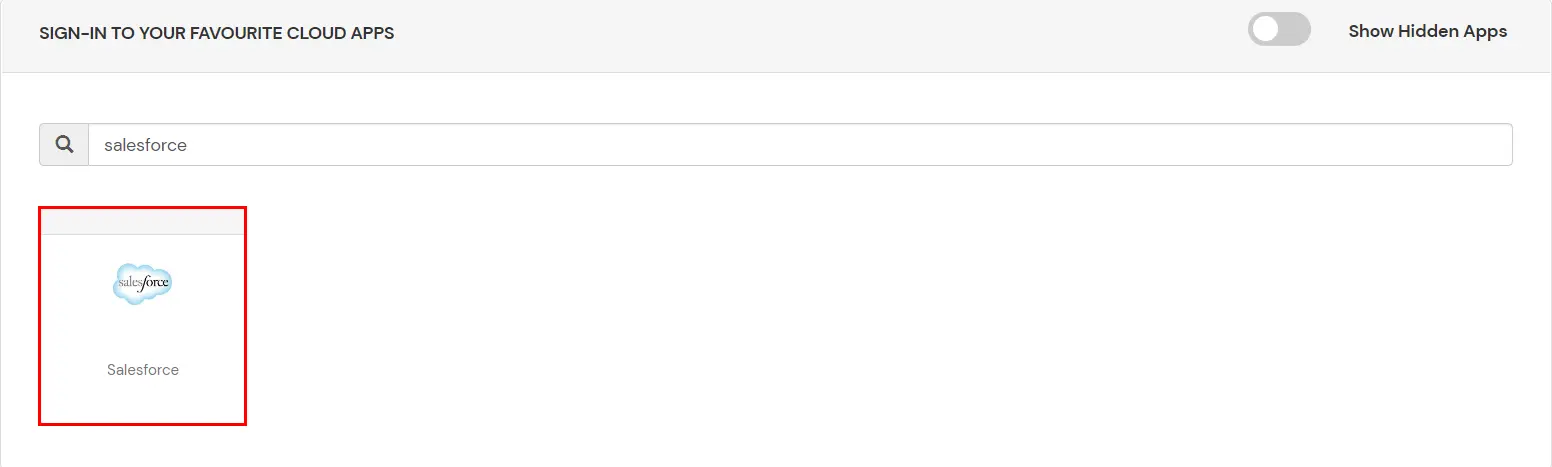
- IdP Initiated SSO Login: Users need to log in to the miniOrange first , and then click on the Salesforce icon on the applications dashboard to access Salesforce.(If you have set up any more Identity Sources, you will log in to that platform).
- JIT Provisioning: Enables the automatic creation of user accounts in Salesforce when a person logs in for the first time via Desktop SSO, IDP, or Active Directory (AD) authentication.
- Single Logout: With this feature, you will be automatically logged out of all the Salesforce applications that are connected with Identity provider (IdP) when you log out from Salesforce org or any other app.
- Mandate users to Login using SSO: Single Sign-on can make it mandatory for all Salesforce users to log in using SSO. This will prevent any person from logging win using any other source and bypassing the login system. No person will be able to have direct login making it a streamline and secure process.
Connect with External Source of Users
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Azure AD, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Shibboleth, Ping, Okta, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more.
Prerequisites
- The following Subscription plans are required for the mentioned authentication methods:
- Federated Authentication: All Editions
- Delegated Authentication Professional, Enterprise, Performance, Unlimited, Developer, and How you integrate Editions.
- Authentication Providers: Professional, Enterprise, Performance, Unlimited, and Developer Editions.
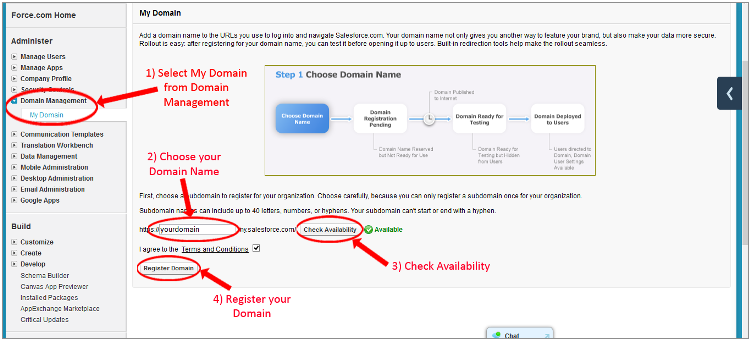
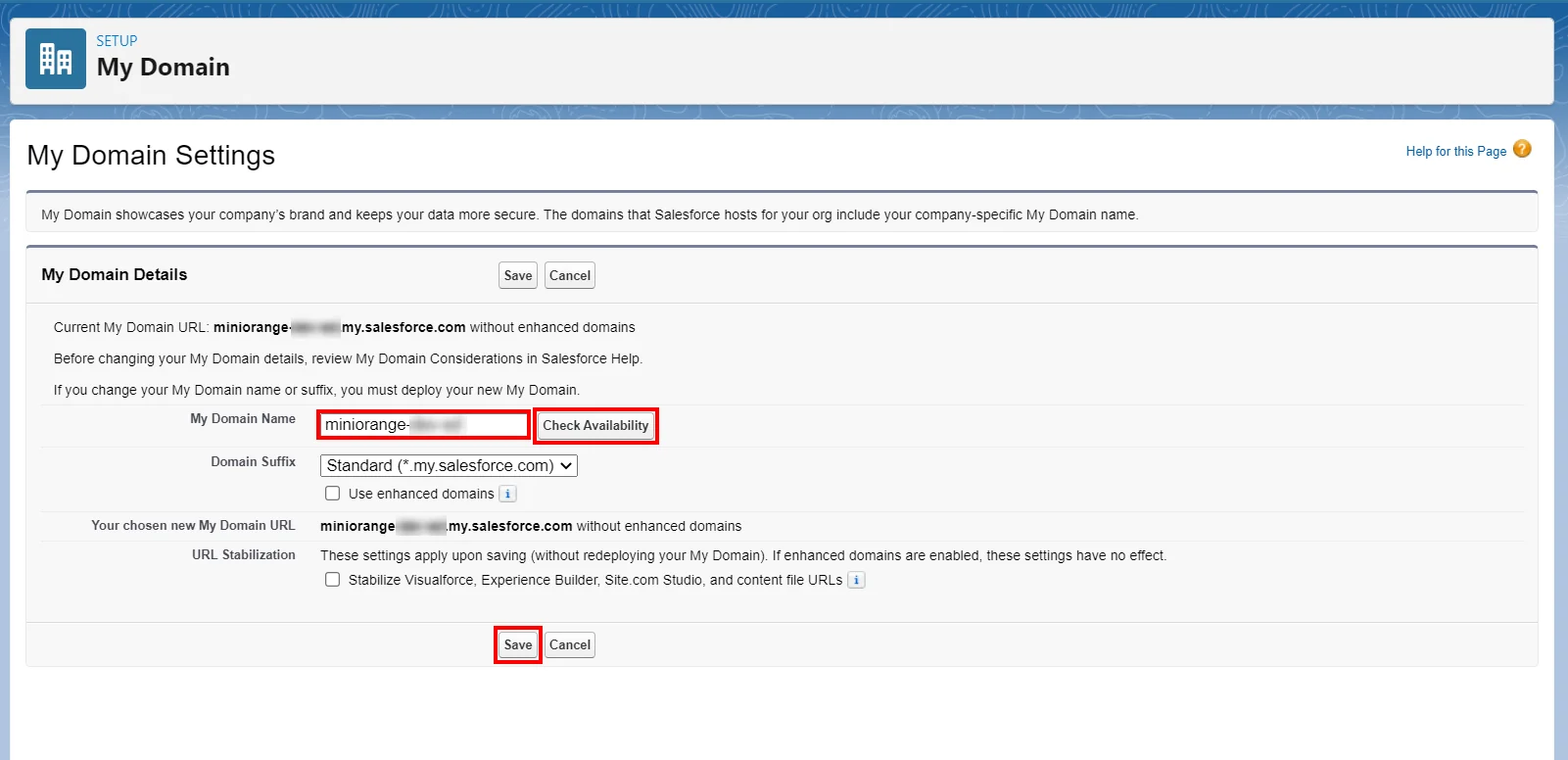
- Note - In order to do SP initiated SSO into Salesforce, you need to create a custom Domain. Check this link - Salesforce domain changes and follow the below steps:
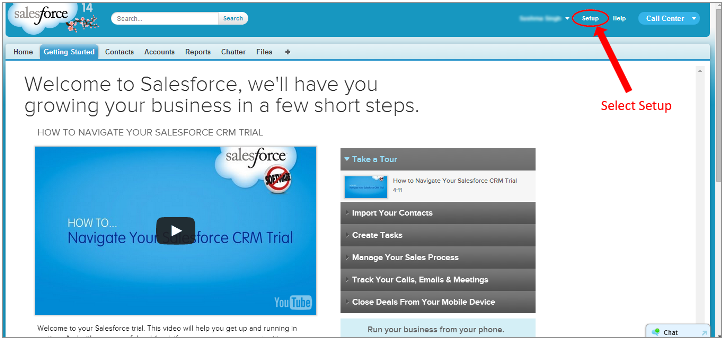
- Login to your Salesforce account.
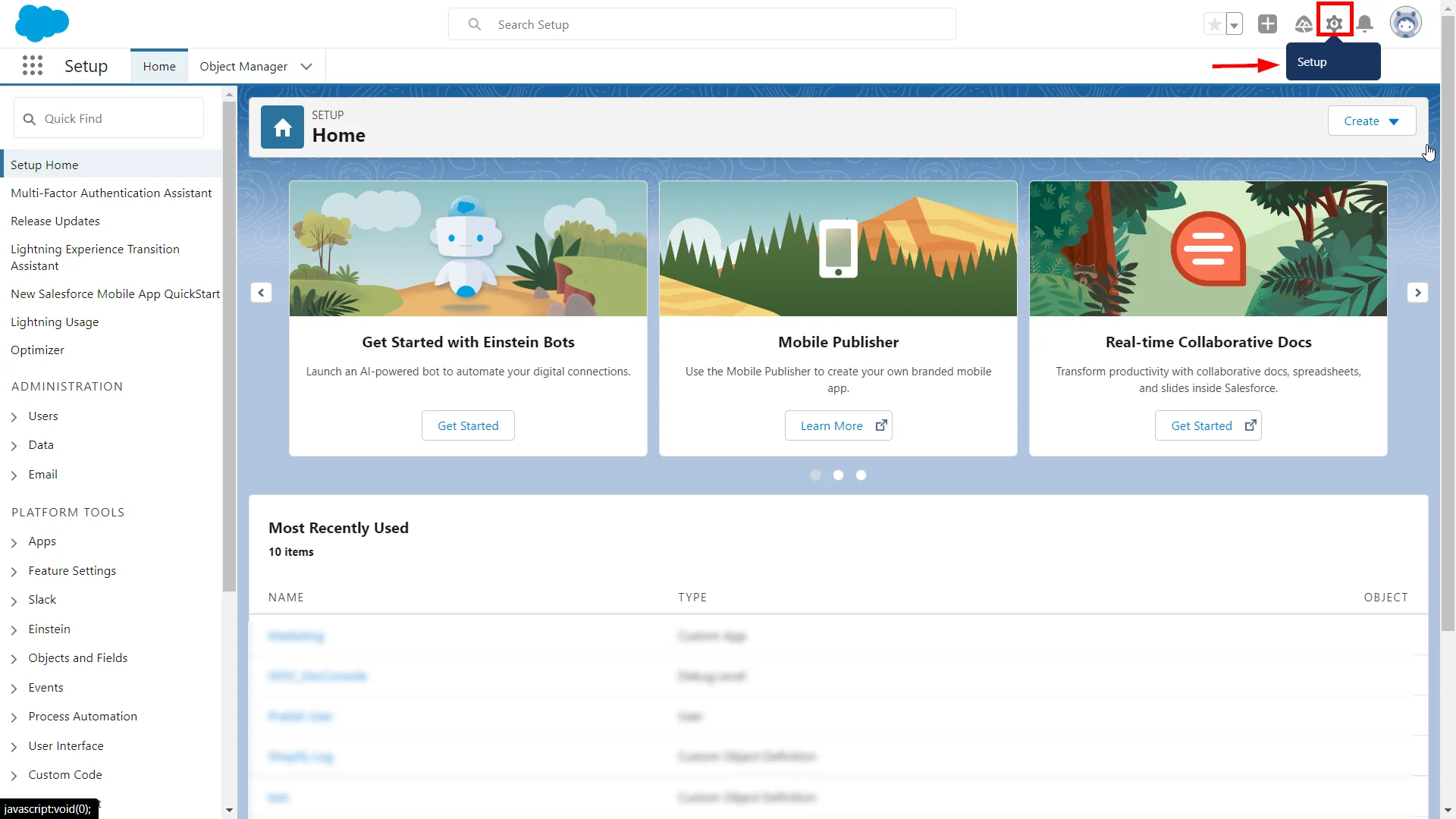
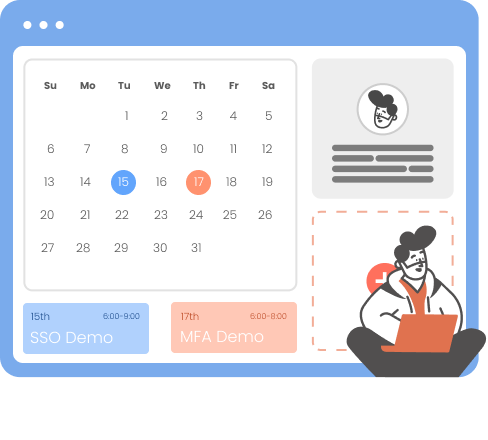
- Click on the Setup icon in the top-right section of the Salesforce lightening dashboard page.
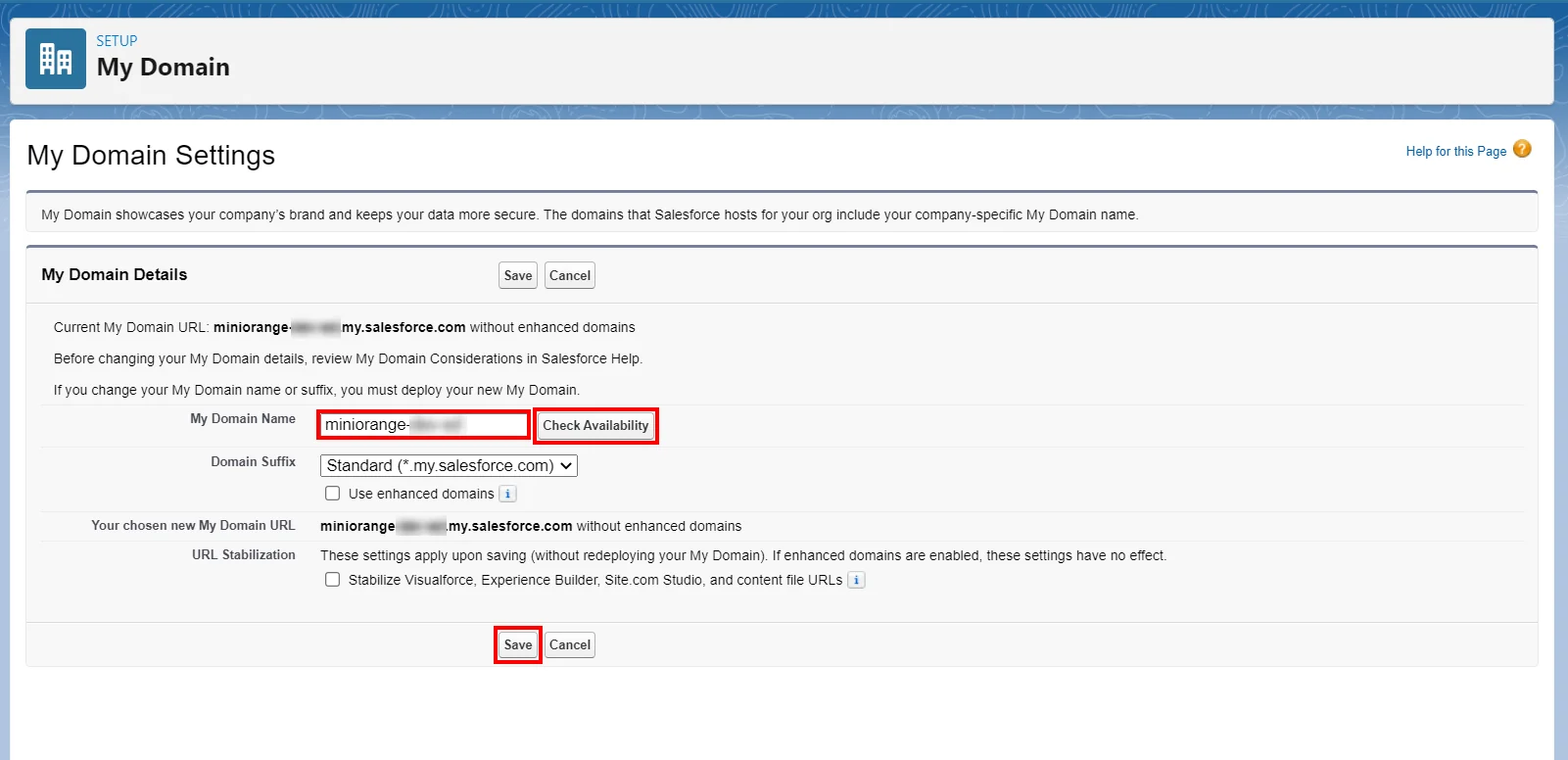
- Now in the search field, search for the My Domain Settings.
- Choose your domain name, check for availability and if available, proceed by saving the settings.
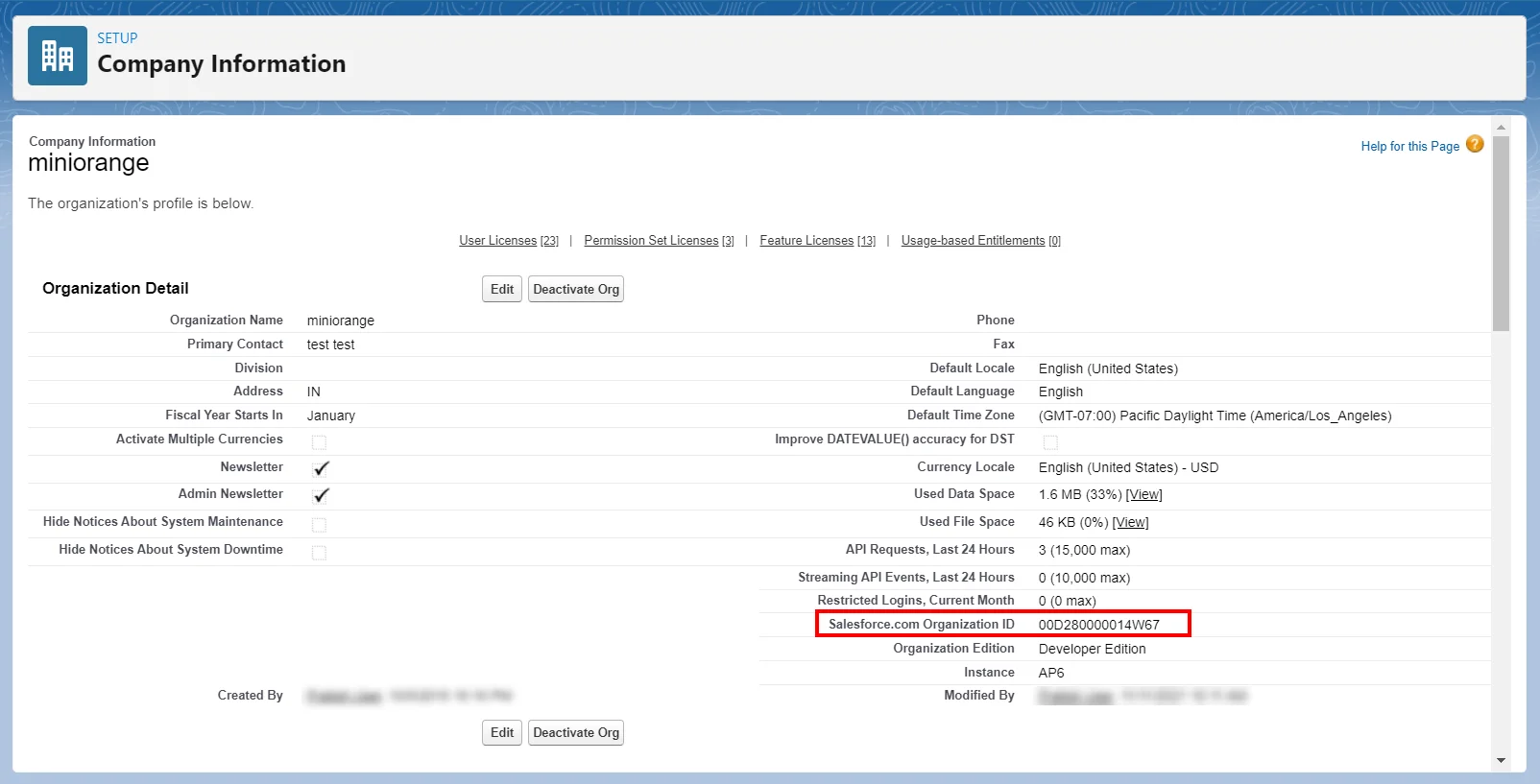
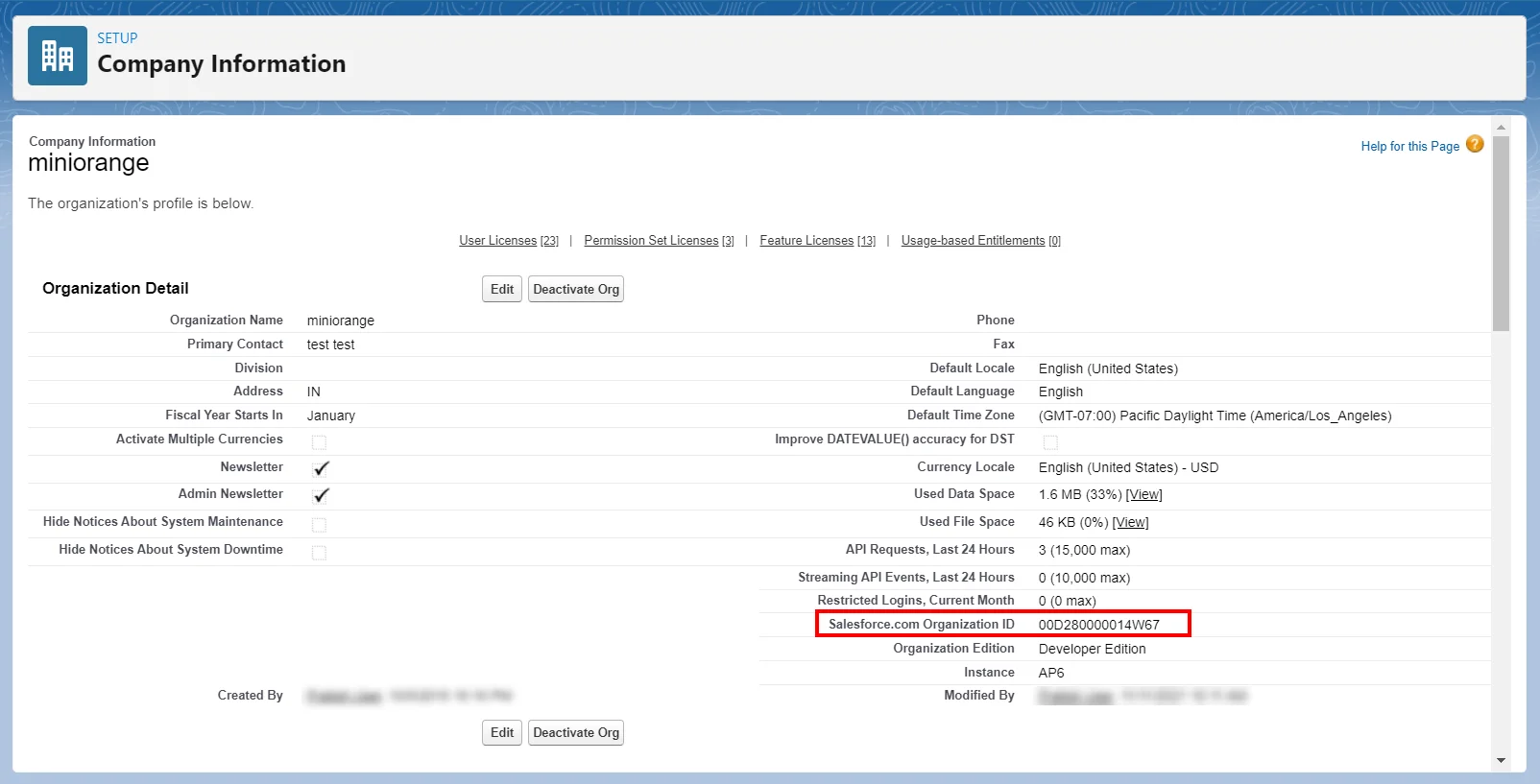
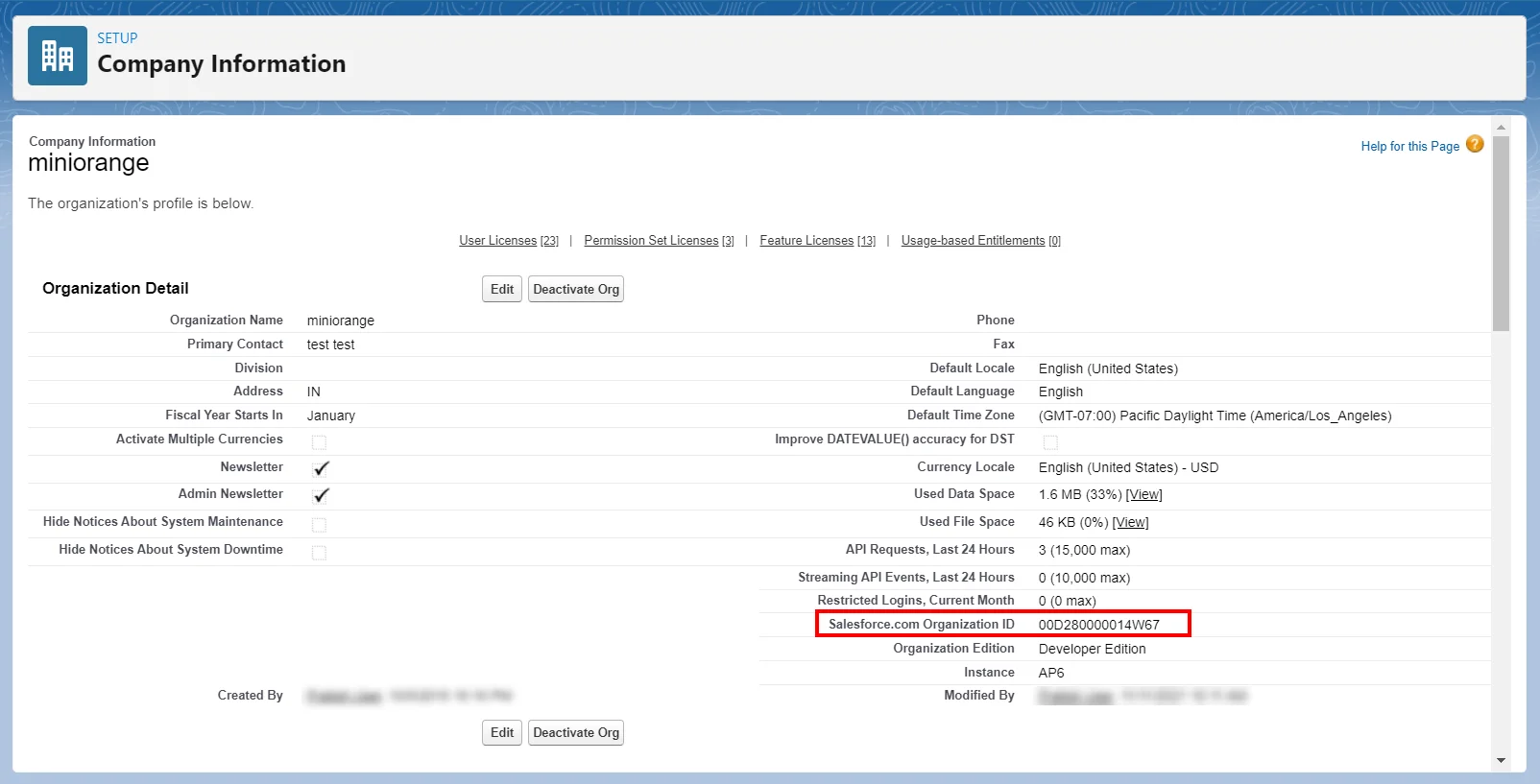
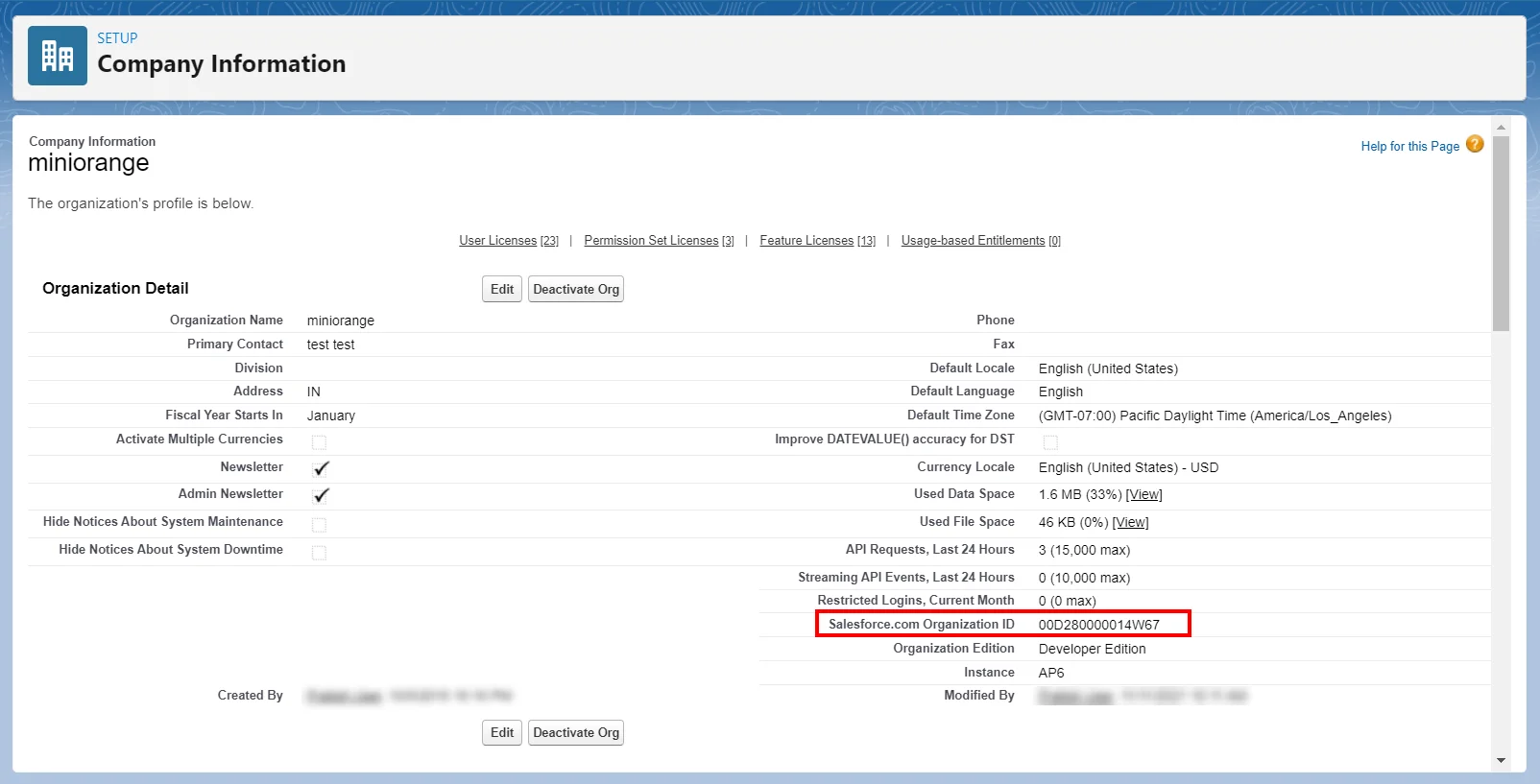
- Search for Company Information in the search bar.
- Copy the Organization Id. (This will be required later)
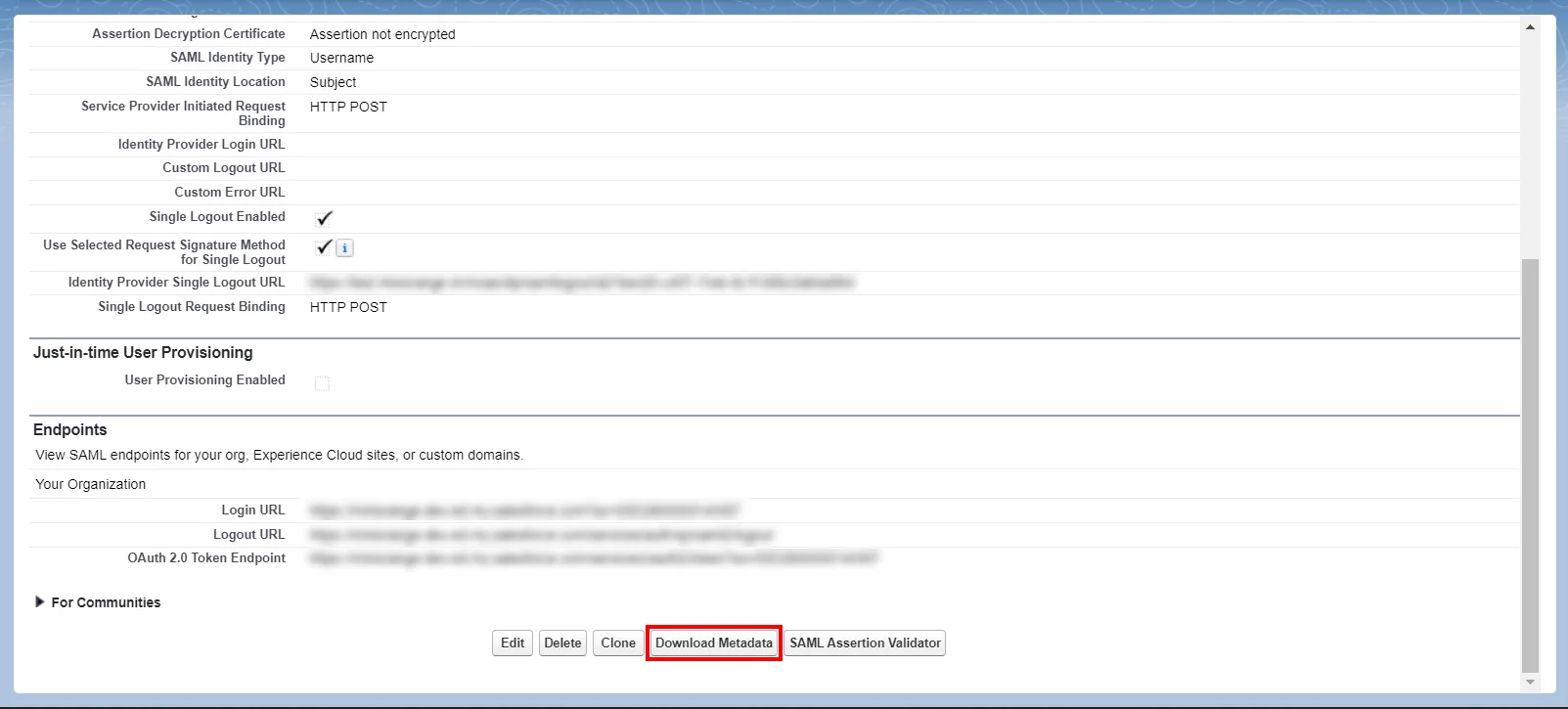
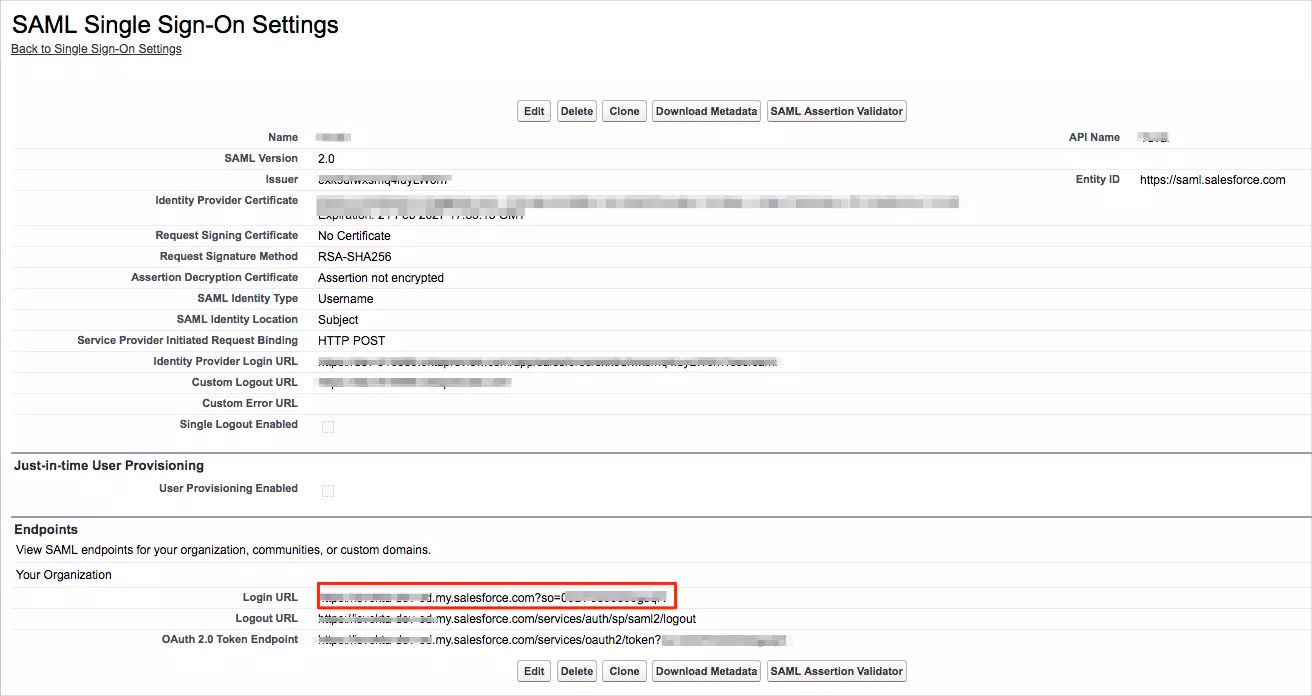
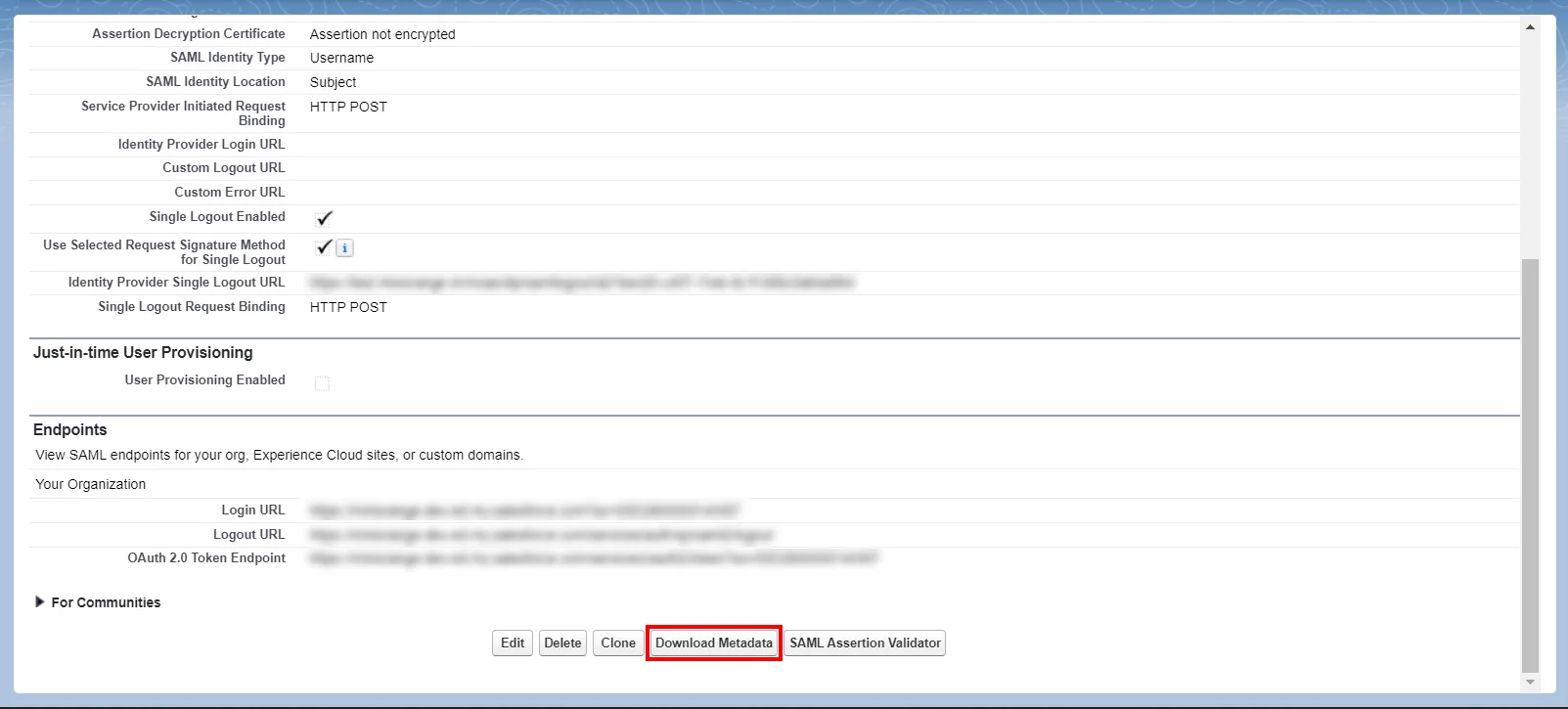
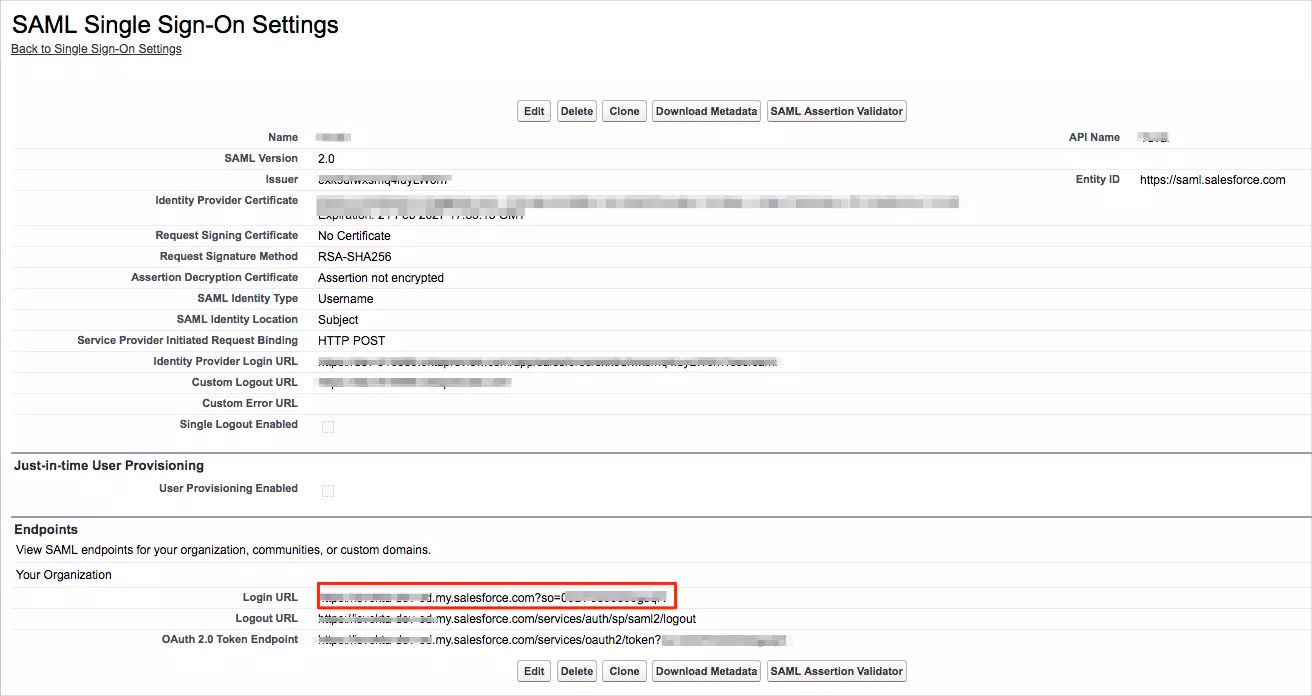
- Salesforce Metadata: After you have set up the SSO settings in Salesforce Admin Dashboard, you will get the Salesforce Metadata File. Click Download Metadata to download an XML file of your SAML configuration settings to send to your identity provider. The identity provider can then upload these configuration settings to connect to your Experience Cloud site.
- Login to your Salesforce account.
- Go to Setup in the top-right section of the Salesforce classic dashboard page.
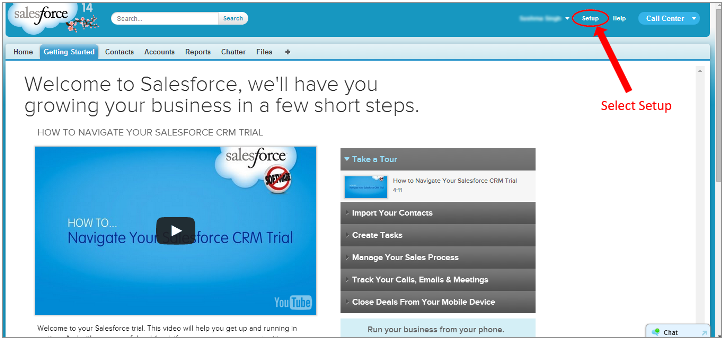
- Now in the left pane, select Domain Management.
- Select My Domain.
- Choose your domain name, check for availability and if available, proceed by clicking the Register Domain button.
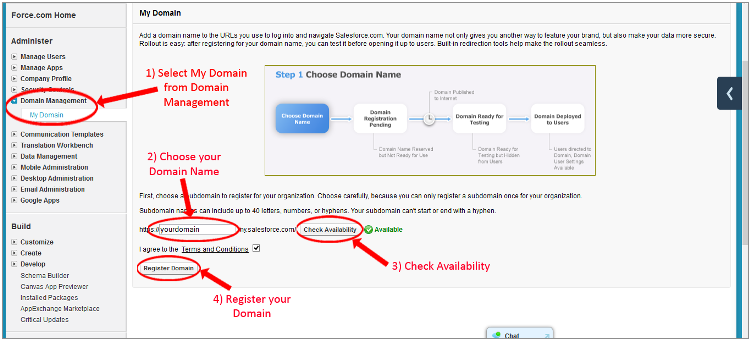
- Test your domain once it is ready, by clicking the link and then click Deploy to Users.
- Search for Company Information in the search bar.
- Copy Organization Id. (This will be required later)
Follow the step-by-step guide given below for Salesforce Single Sign-On (SSO)
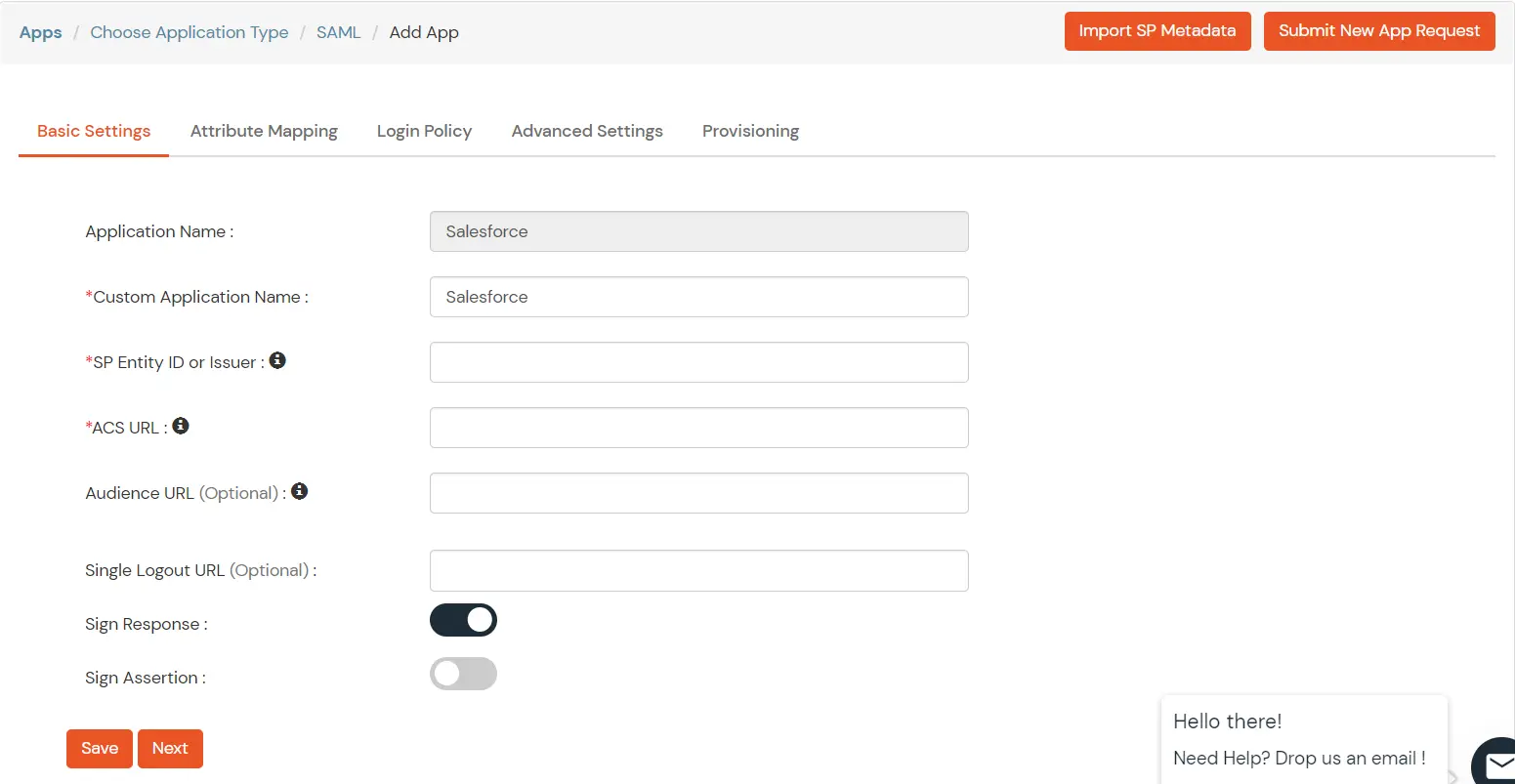
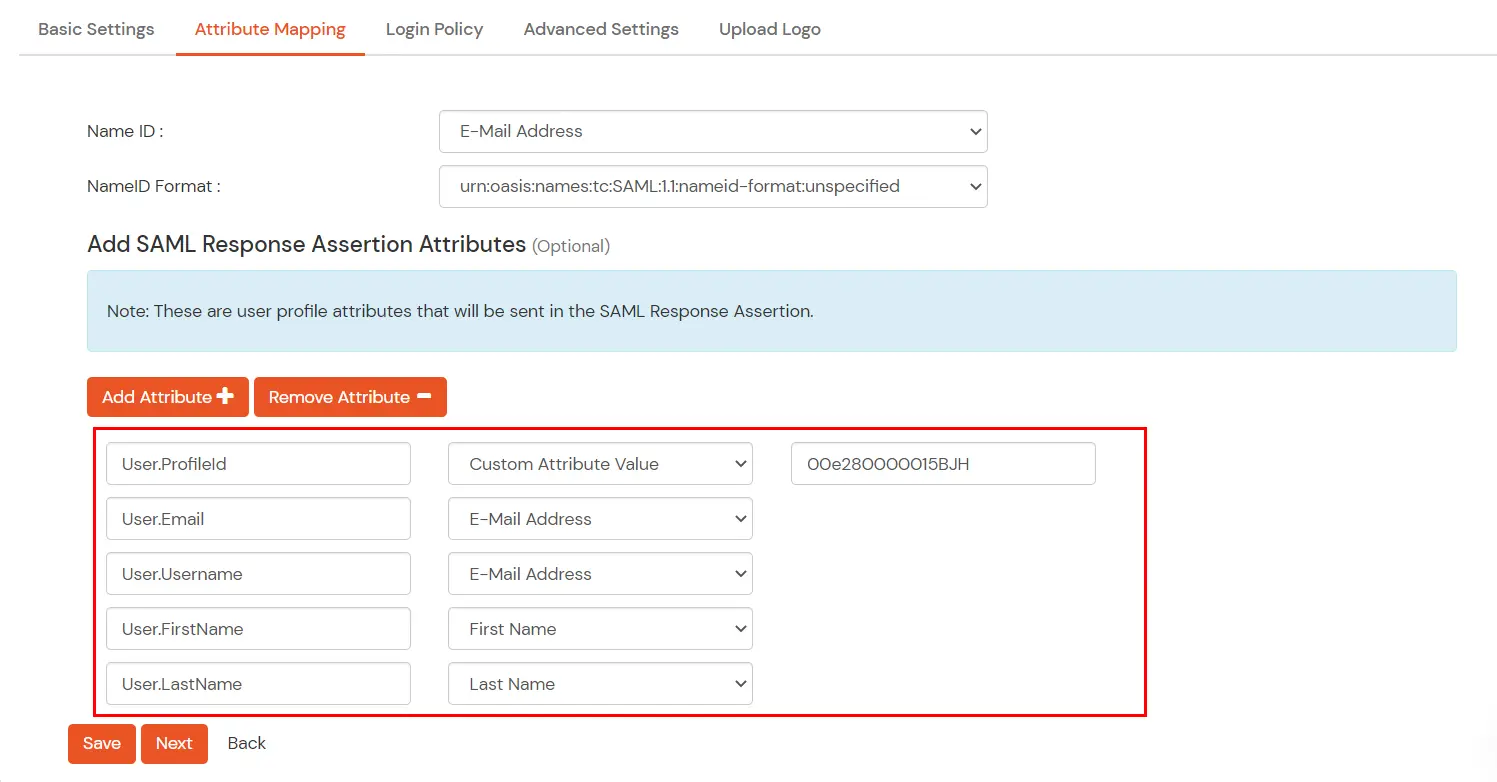
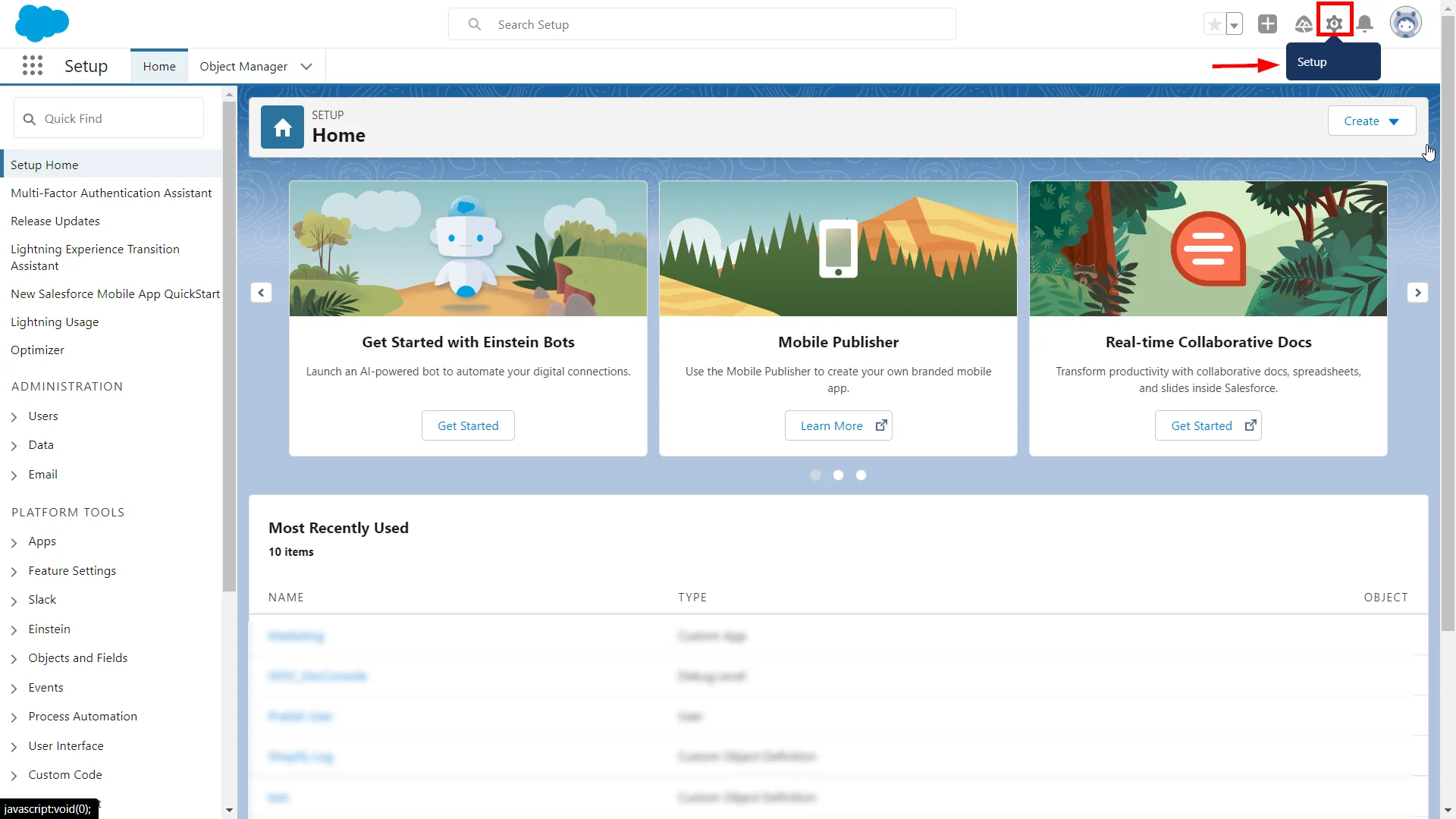
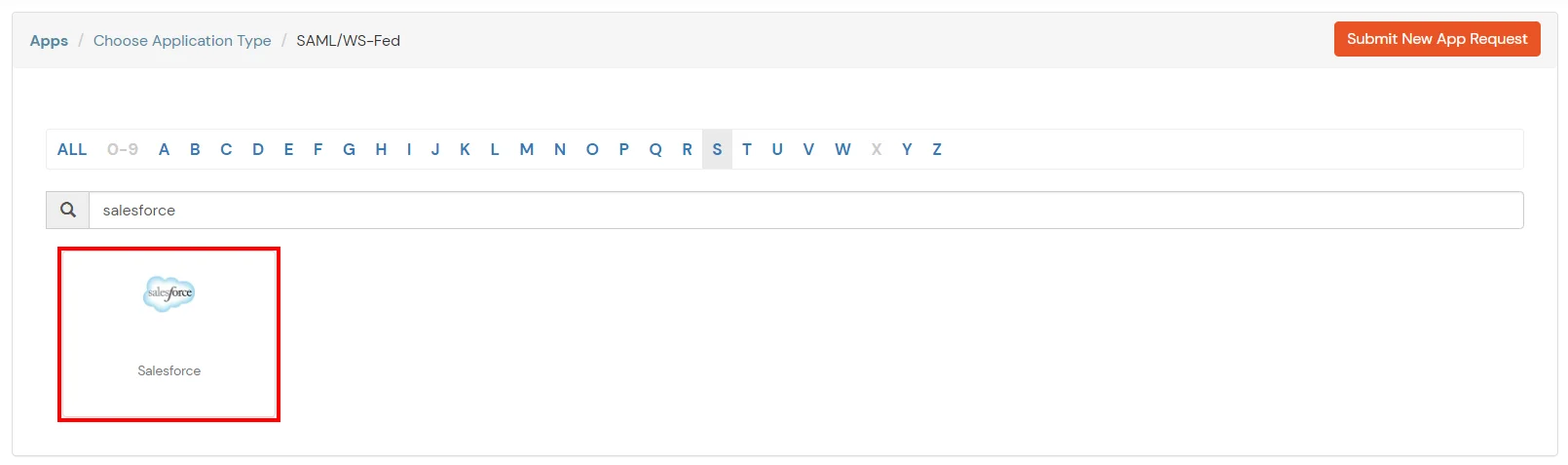
1. Configure Salesforce in miniOrange
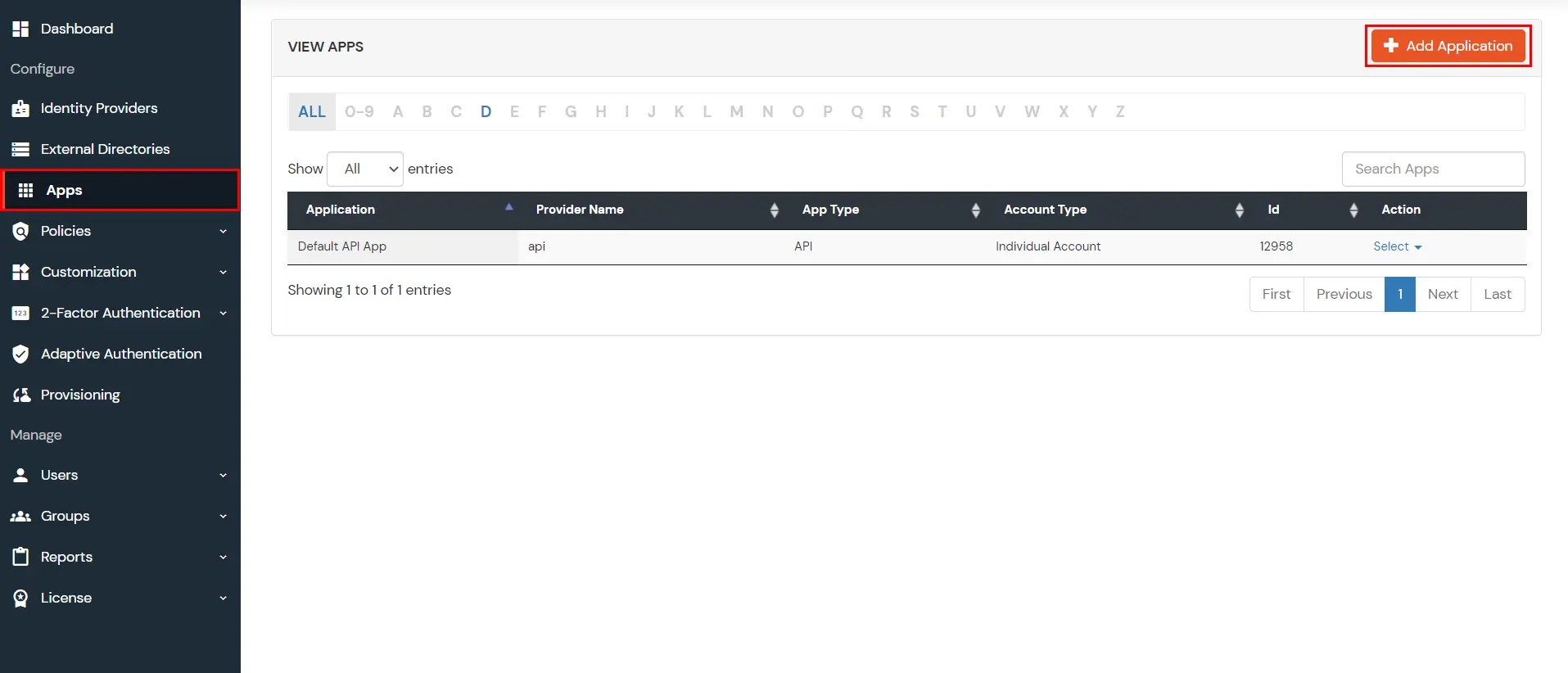
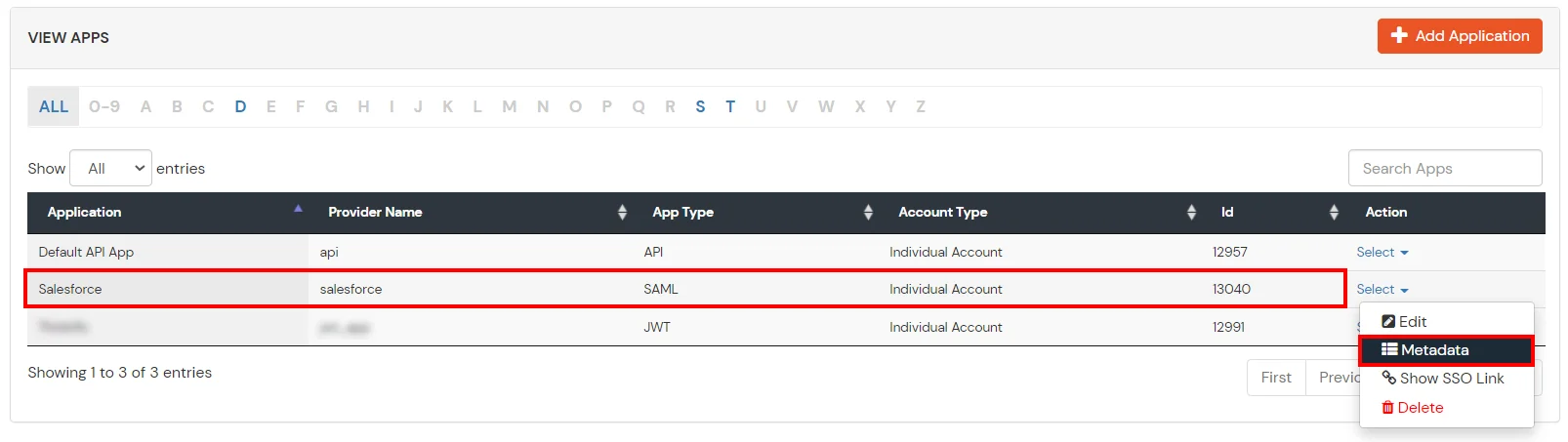
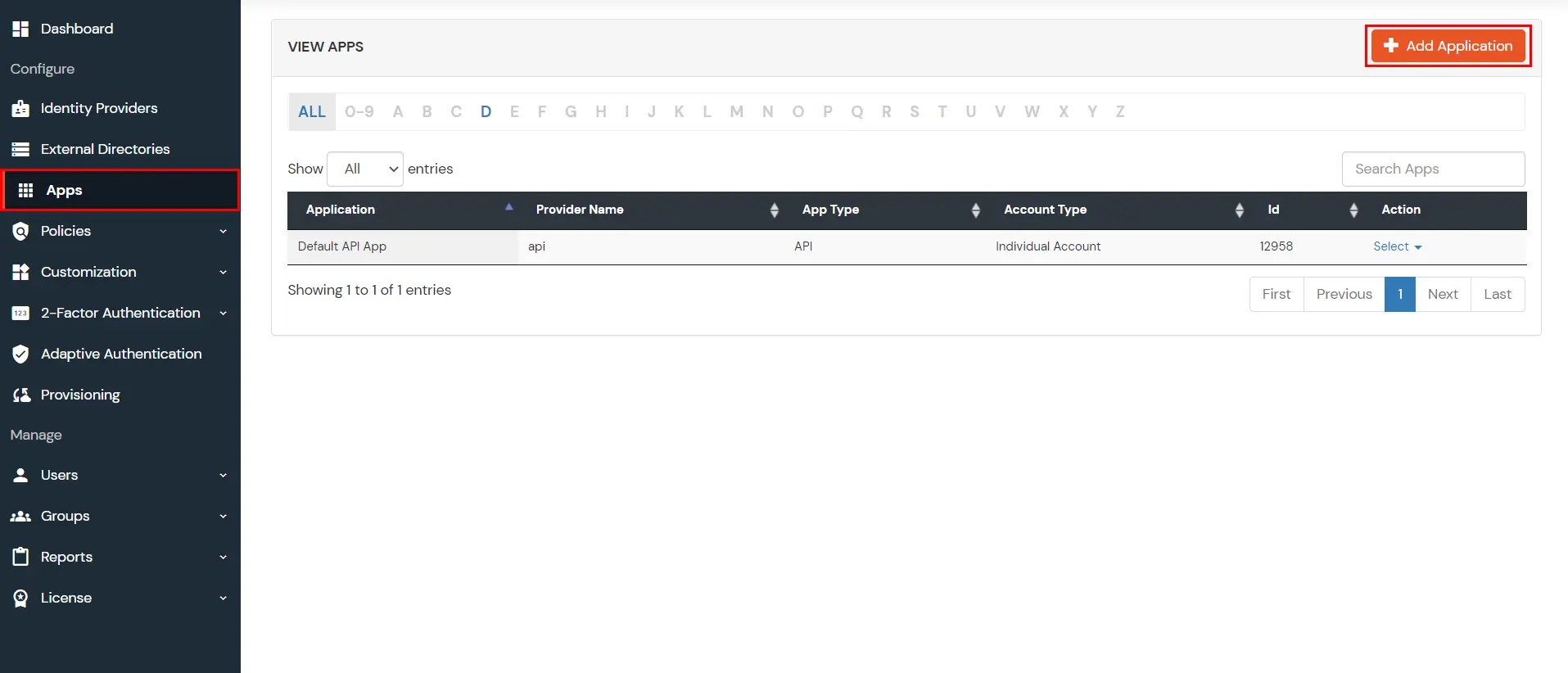
- Login into miniOrange Admin Console.
- Go to Apps and click on Add Application button.
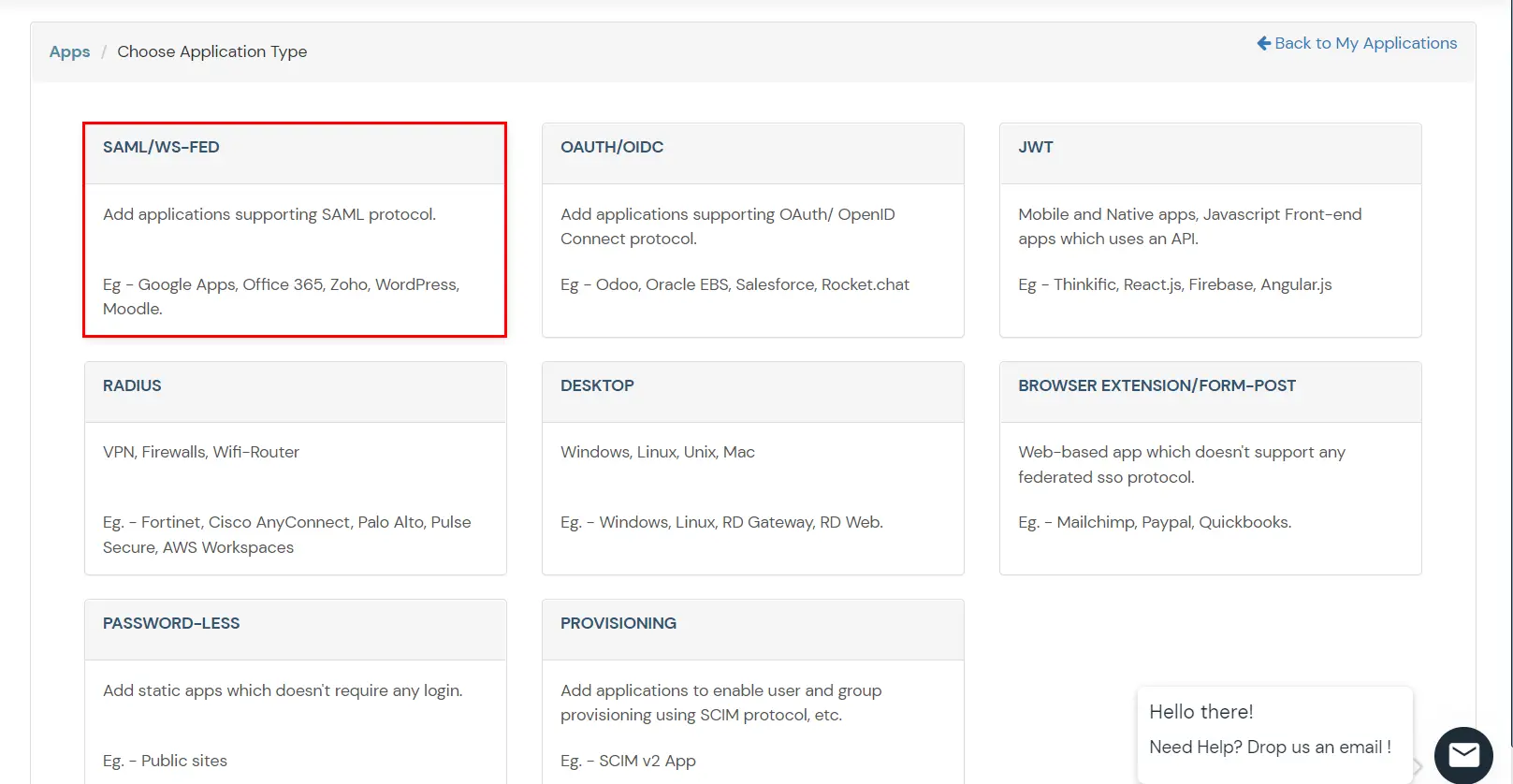
- In Choose Application Type click on SAML/WS-FED application type.
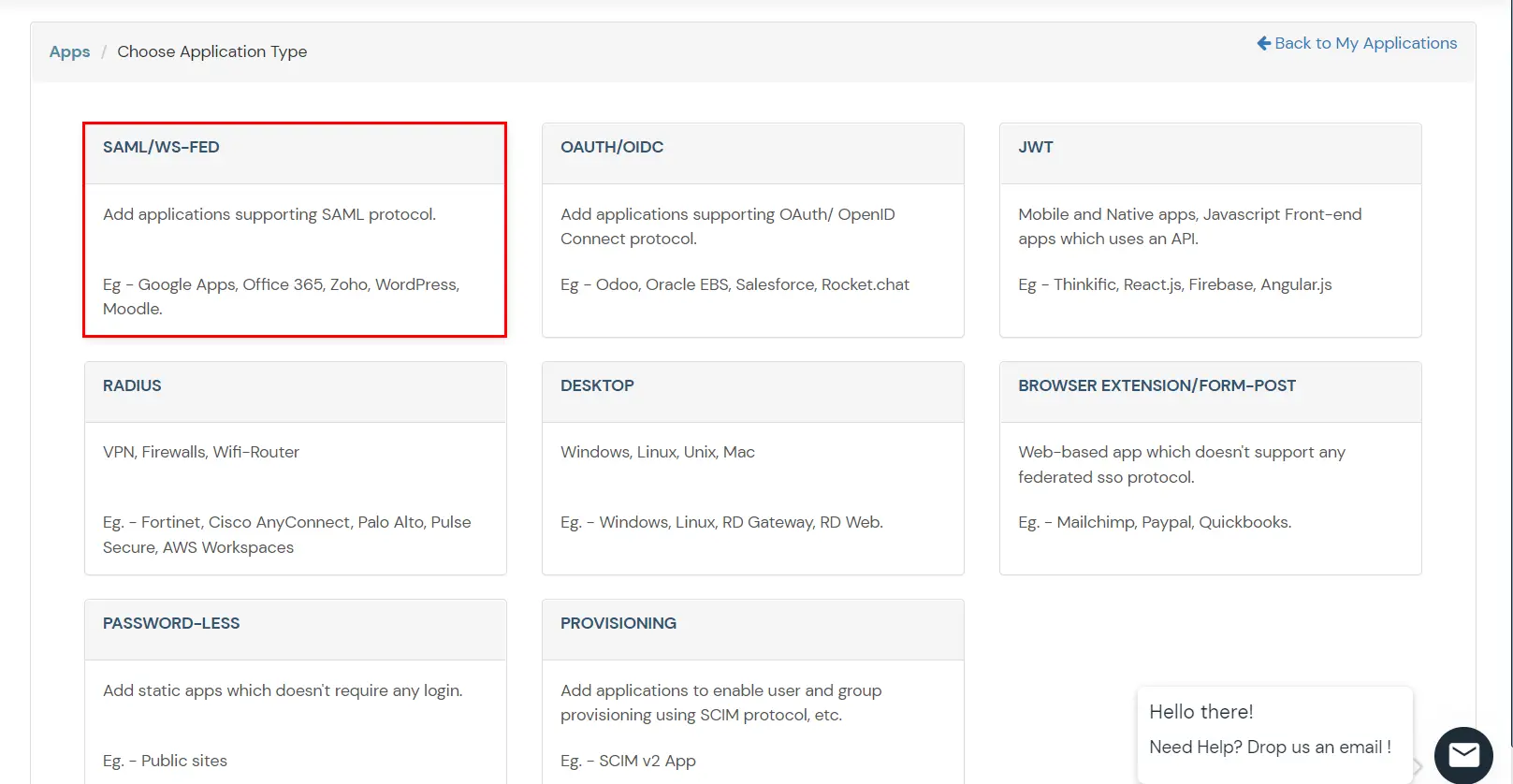
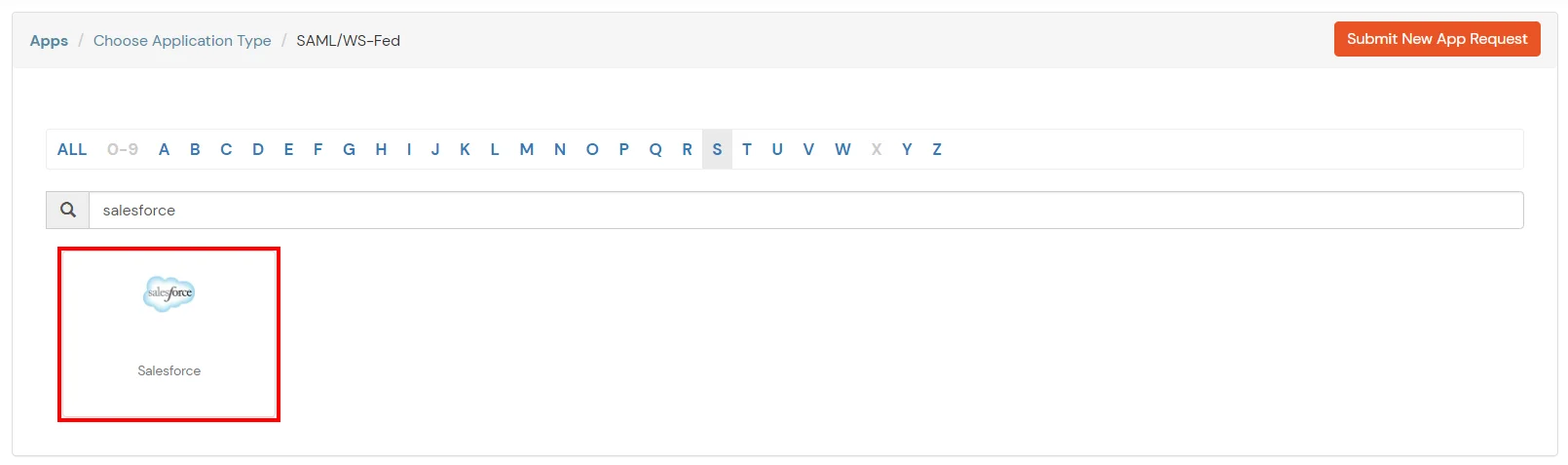
- Search for Salesforce in the list, if you don't find Salesforce in the list then, search for custom and you can set up your application via Custom SAML App.
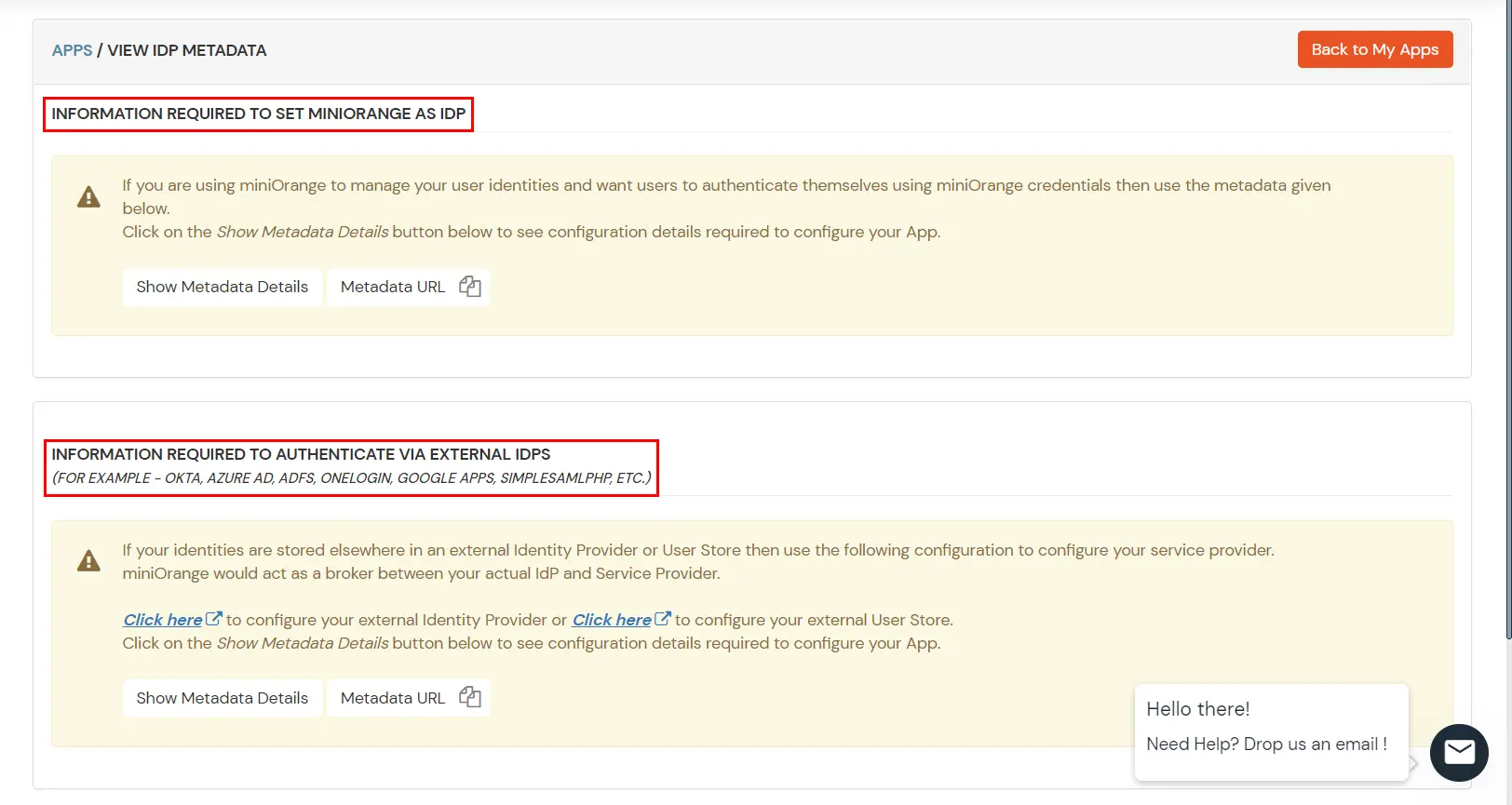
2. Configure SSO in Salesforce Admin Account
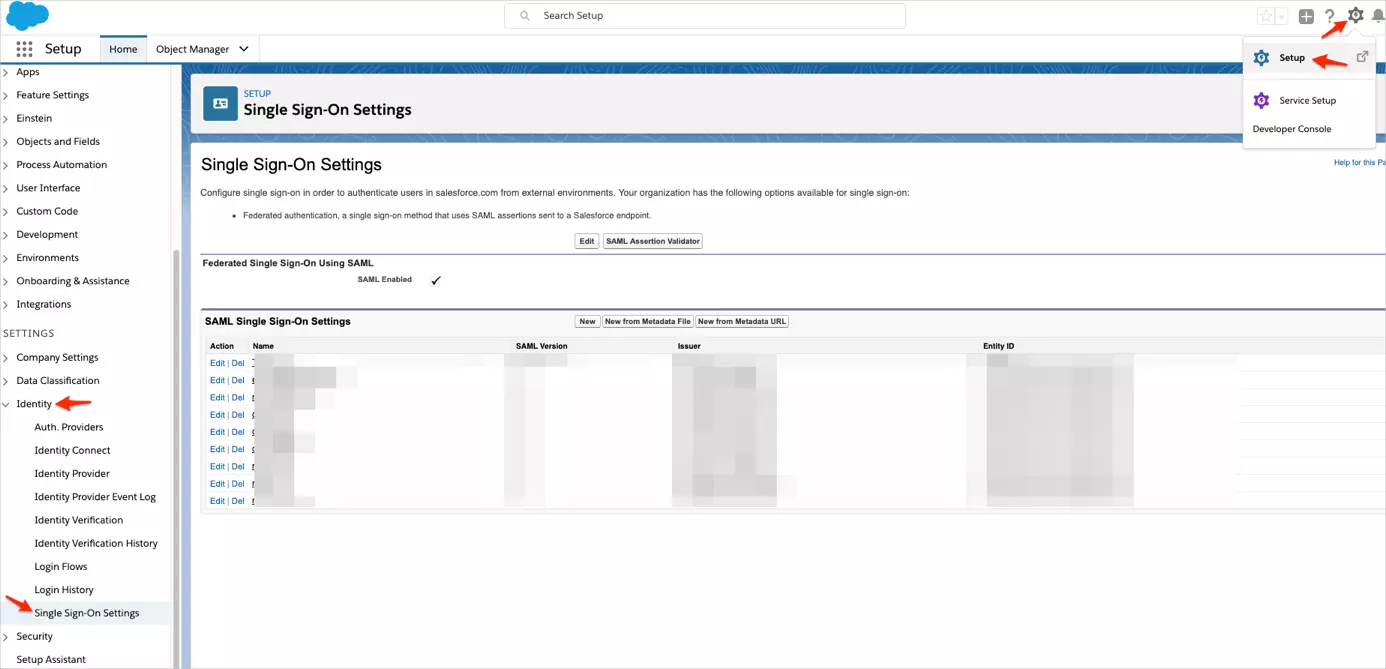
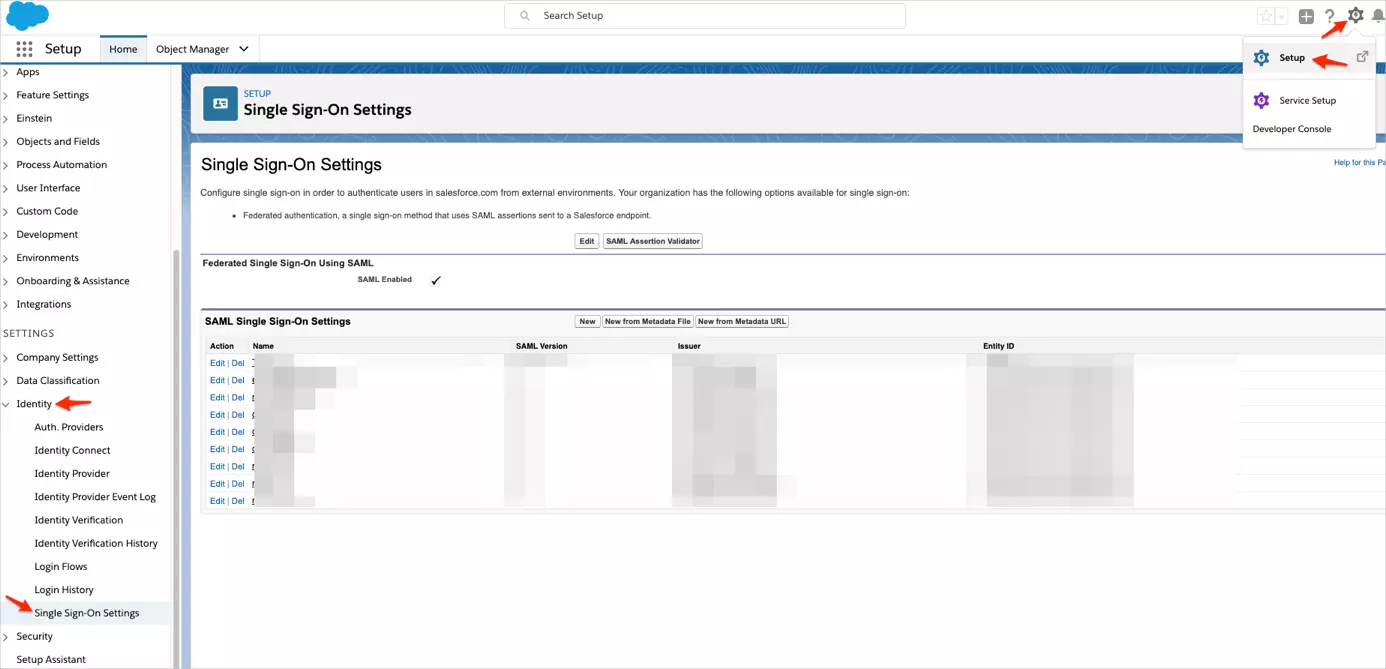
- Log in to your Salesforce account as Account Admin.
- Click the gear icon, then navigate to Setup > Identity > Single Sign-On Settings.
- Log in to your Salesforce account as Account Admin.
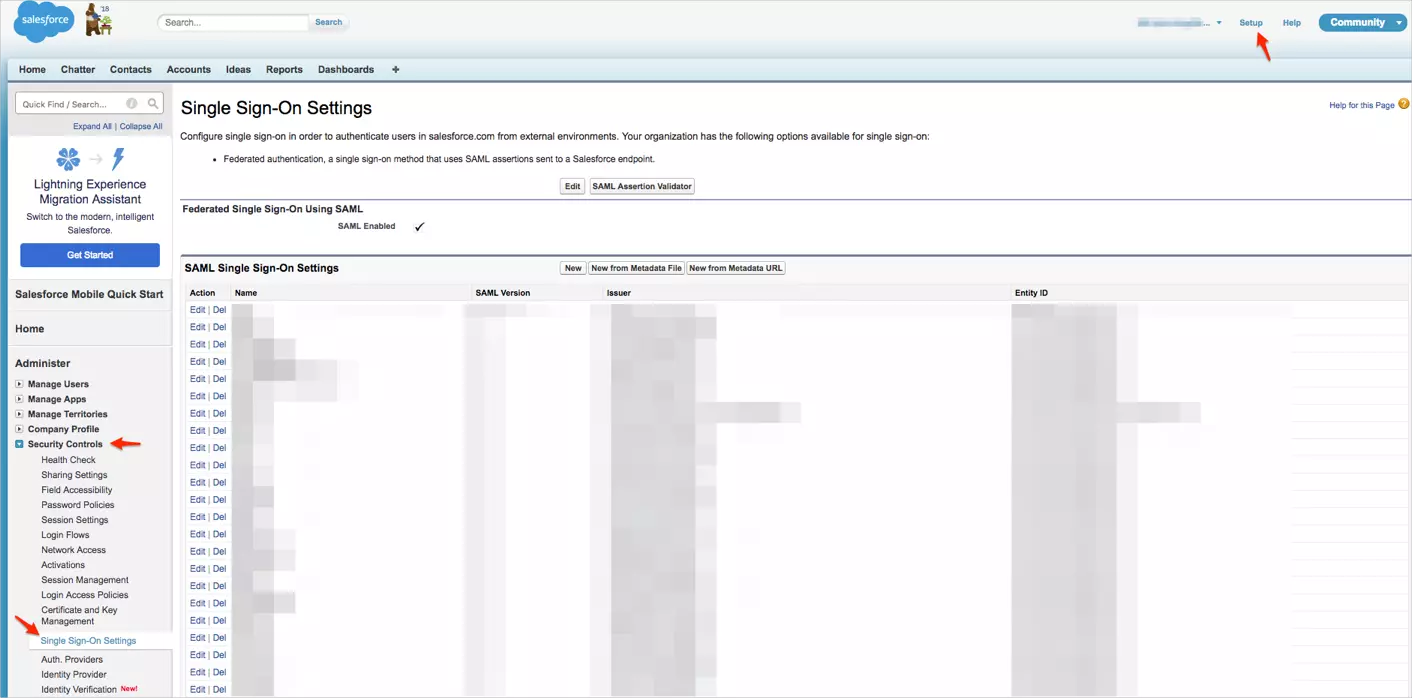
- Navigate to Setup > Security Controls > Single Sign-On Settings.
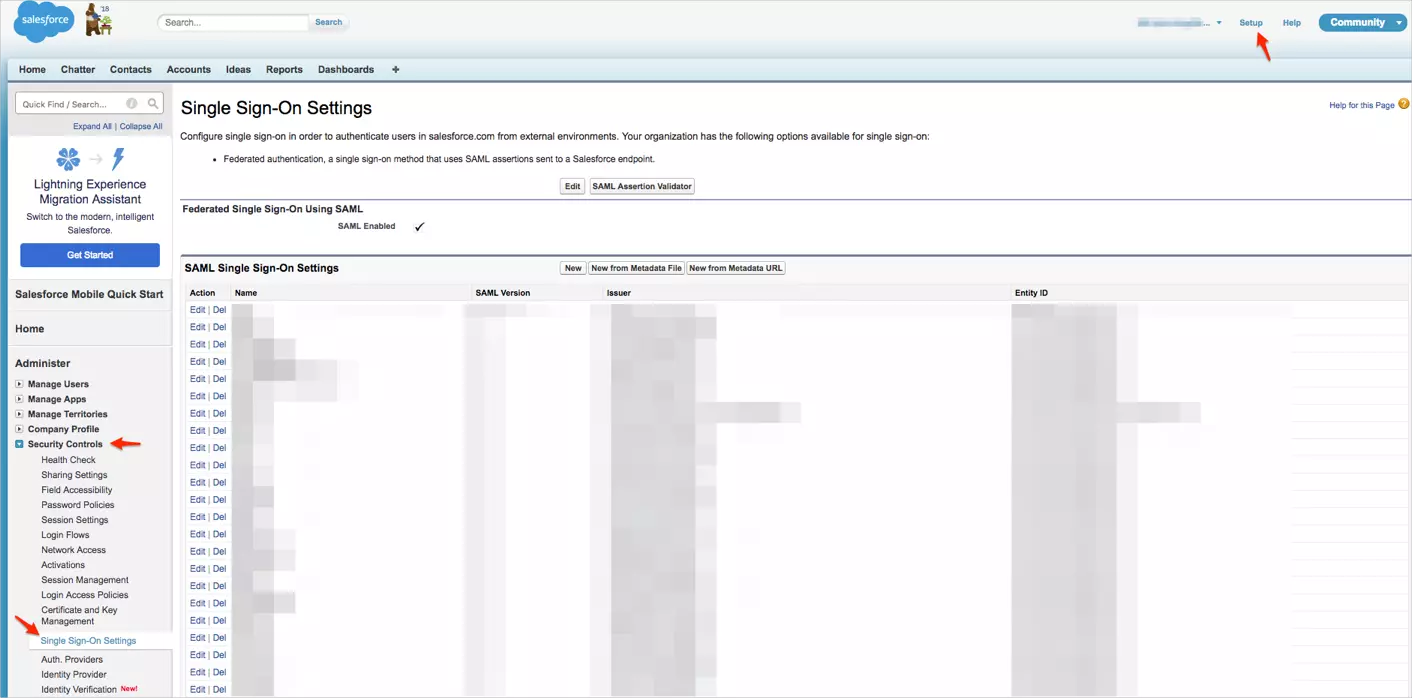
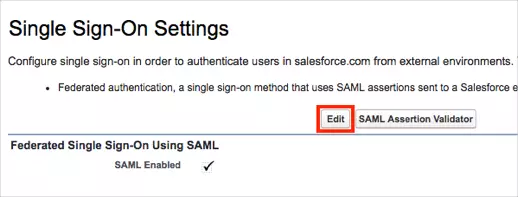
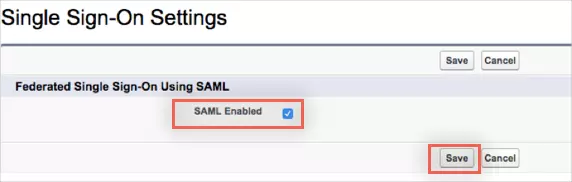
- On the Single Sign-On Settings page, click on Edit.
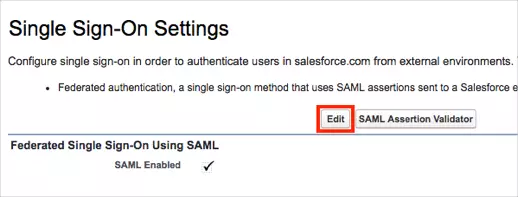
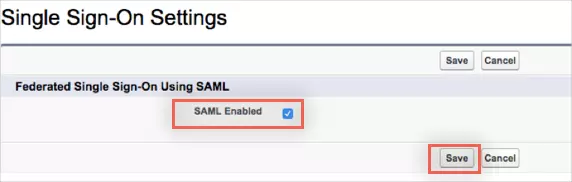
- Check the SAML Enabled box to enable the use of SAML Single-Sign On, then click on Save.
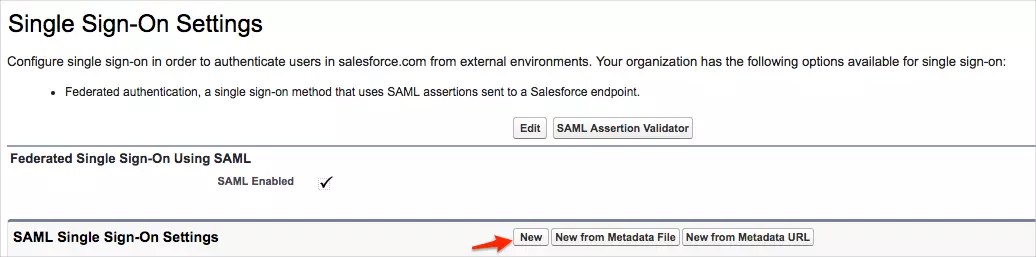
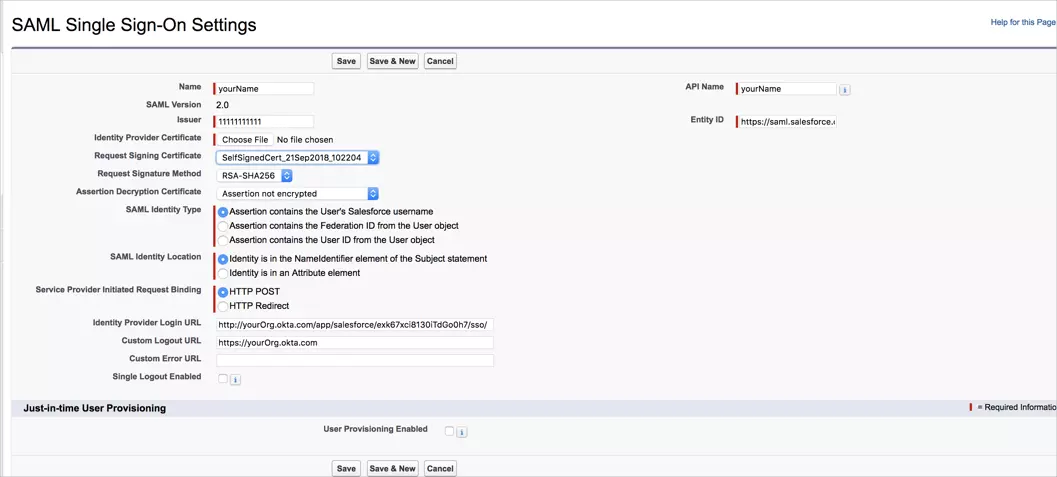
- Click New to open SAML Single Sign-On Settings.
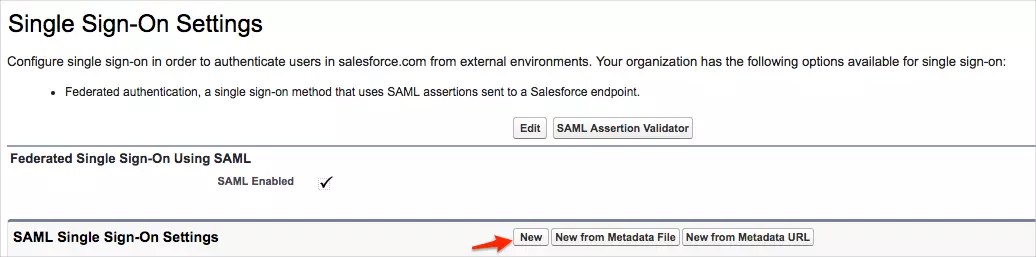
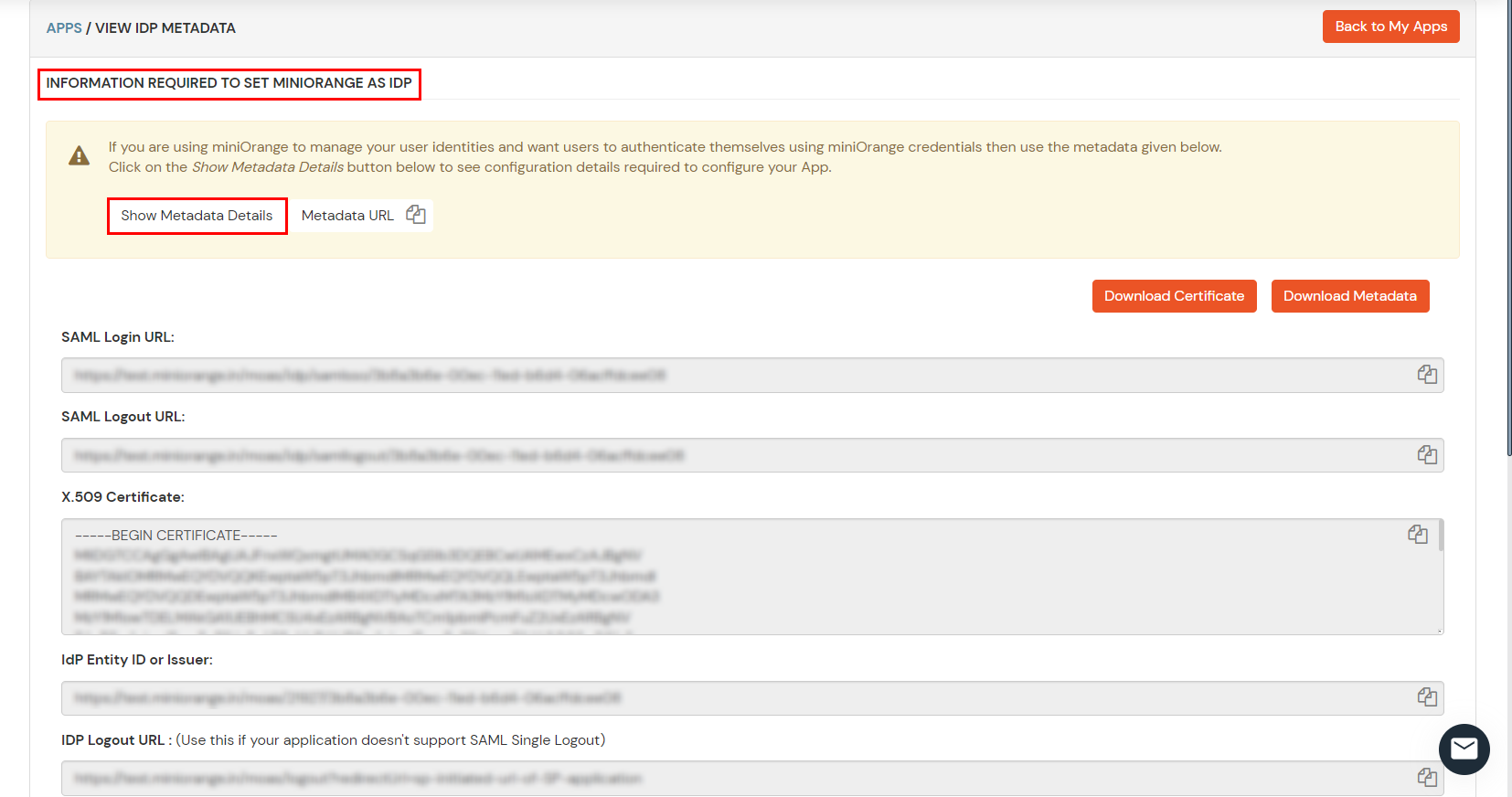
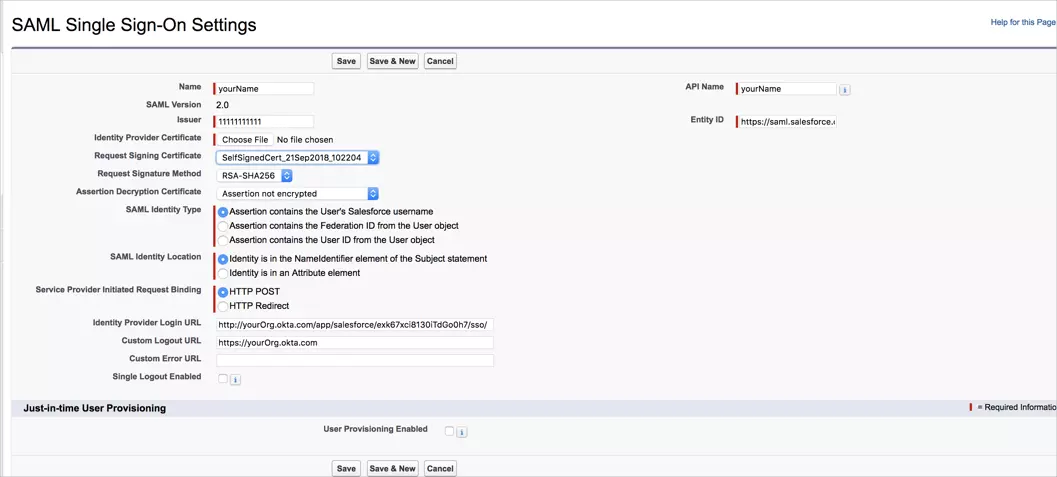
- Enter the following values in the respective fields.
- Issuer :
IDP Entity ID/Issuer in miniorange metadata
- Entity ID :
https://[yourdomain].my.salesforce.com
- Identity Provider Certificate :
Upload Certificate from miniOrange metadata
- Request Signature method :
RSA-SHA256
- Assertion Decryption Certificate :
Not encrypted
- SAML Identity Type :
Assertion contains the User's Salesforce username
- SAML Identity Location :
Identity is in the NameIdentifier element of the Subject statement
- Service Provider Initiated Request Binding :
HTTP Redirect
- Identity Provider Login URL :
SAML Login URL in miniOrange metadata
- Custom Logout URL :
https://[yourdomain].my.salesforce.com
- Click on Save.
- Copy your Login URL value.
3. Test SSO Configuration
Test SSO login to your Salesforce account with miniOrange IdP:
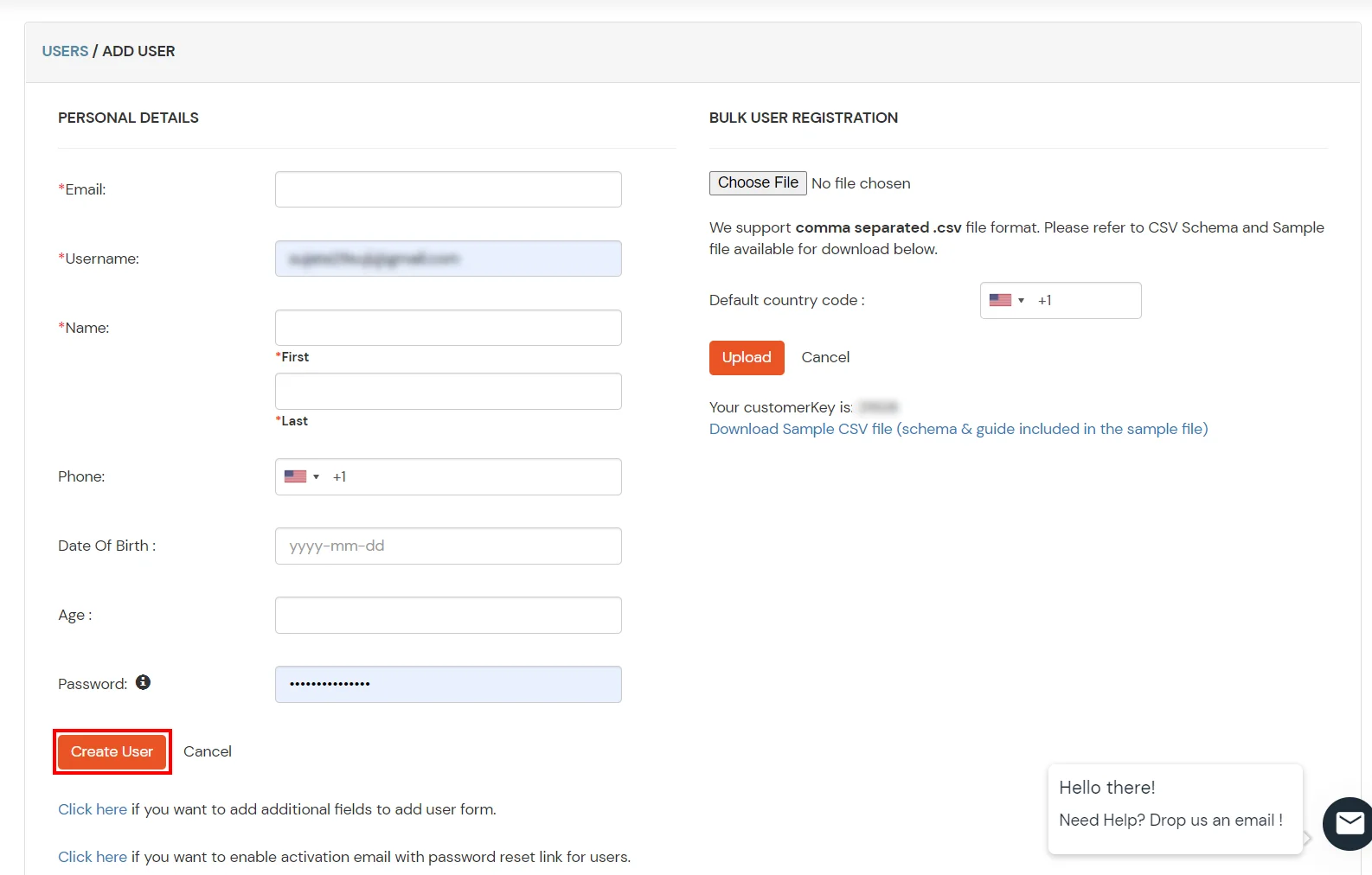
4. Configure Your User Directory (Optional)
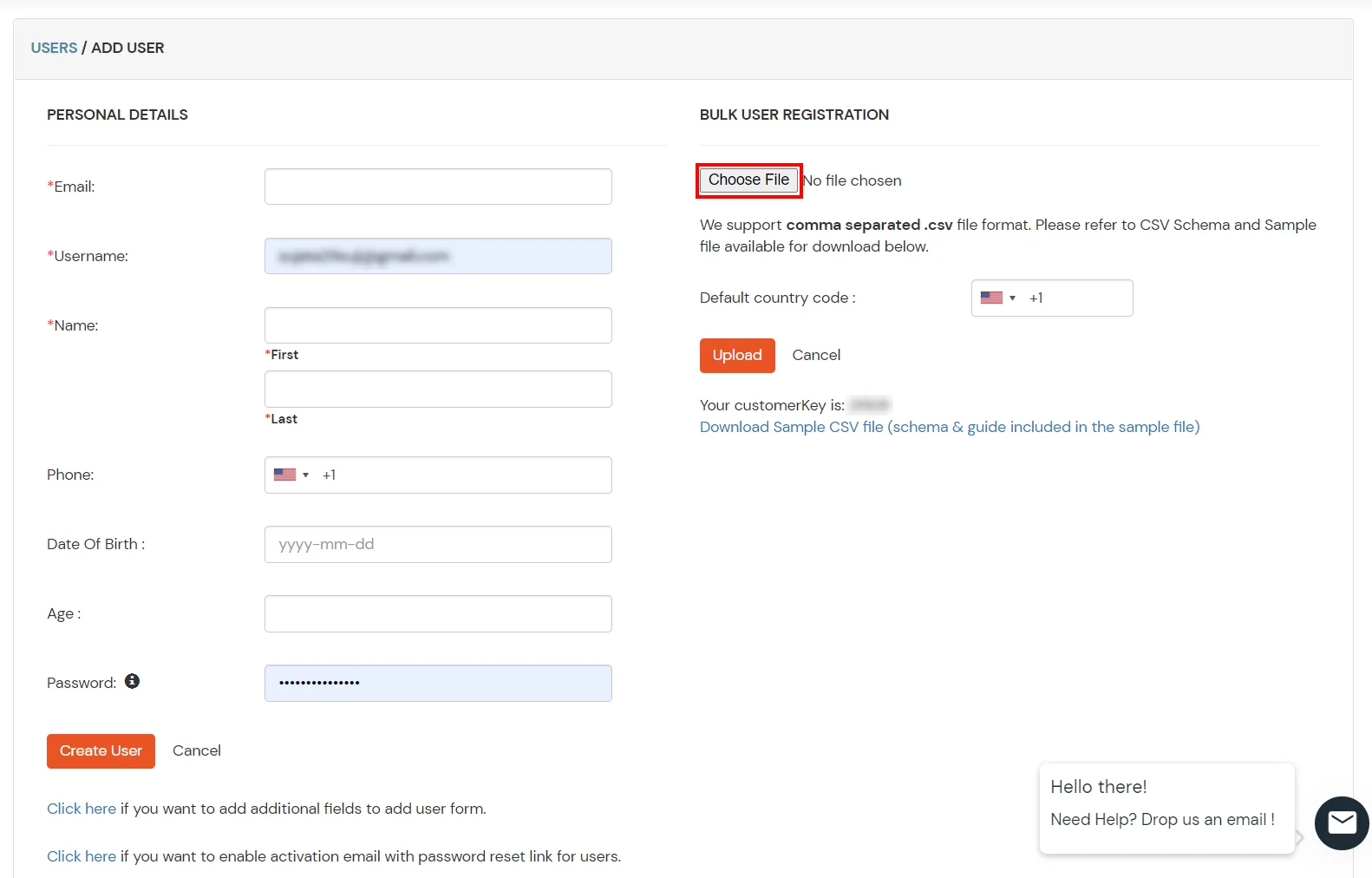
miniOrange provides user authentication from various external sources, which can be Directories (like ADFS, Microsoft Active Directory, Azure AD, OpenLDAP, Google, AWS Cognito etc), Identity Providers (like Okta, Shibboleth, Ping, OneLogin, KeyCloak), Databases (like MySQL, Maria DB, PostgreSQL) and many more. You can configure your existing directory/user store or add users in miniOrange.
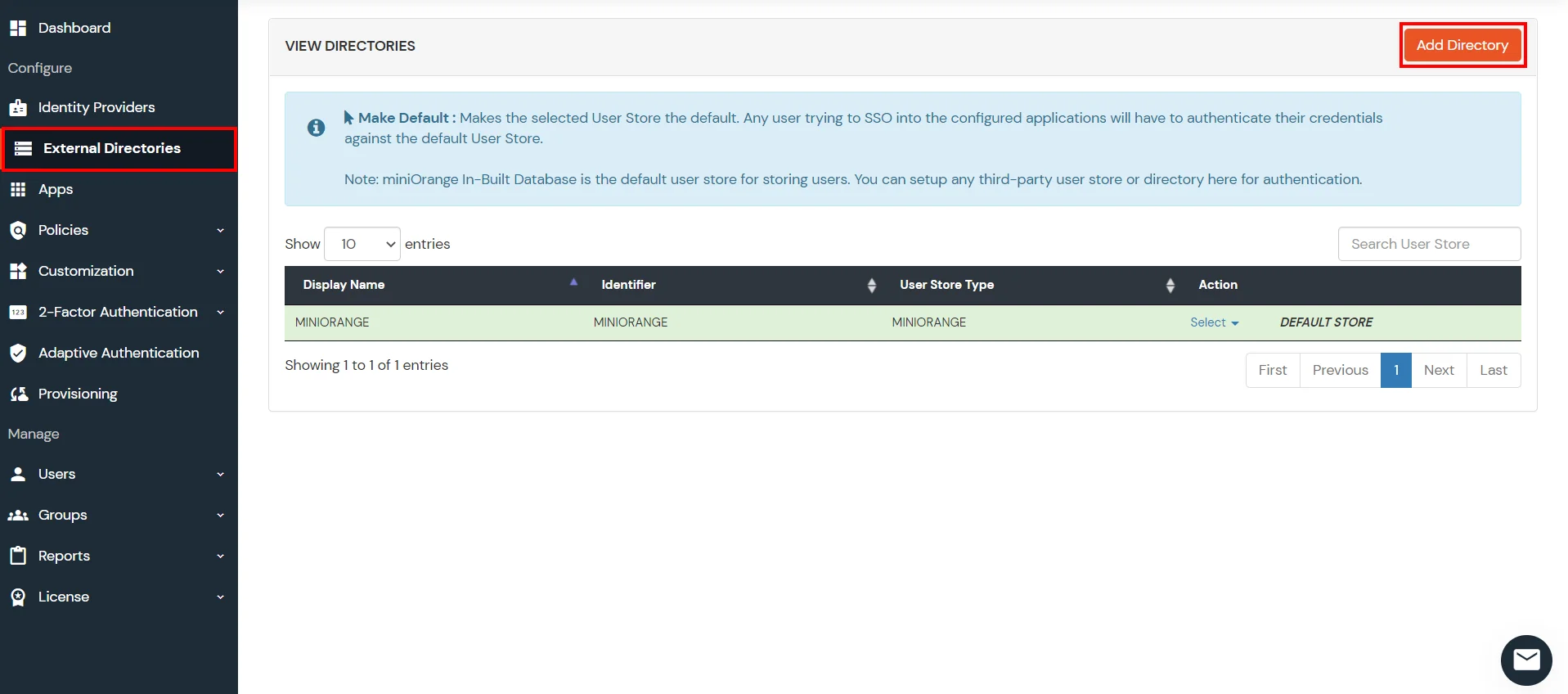
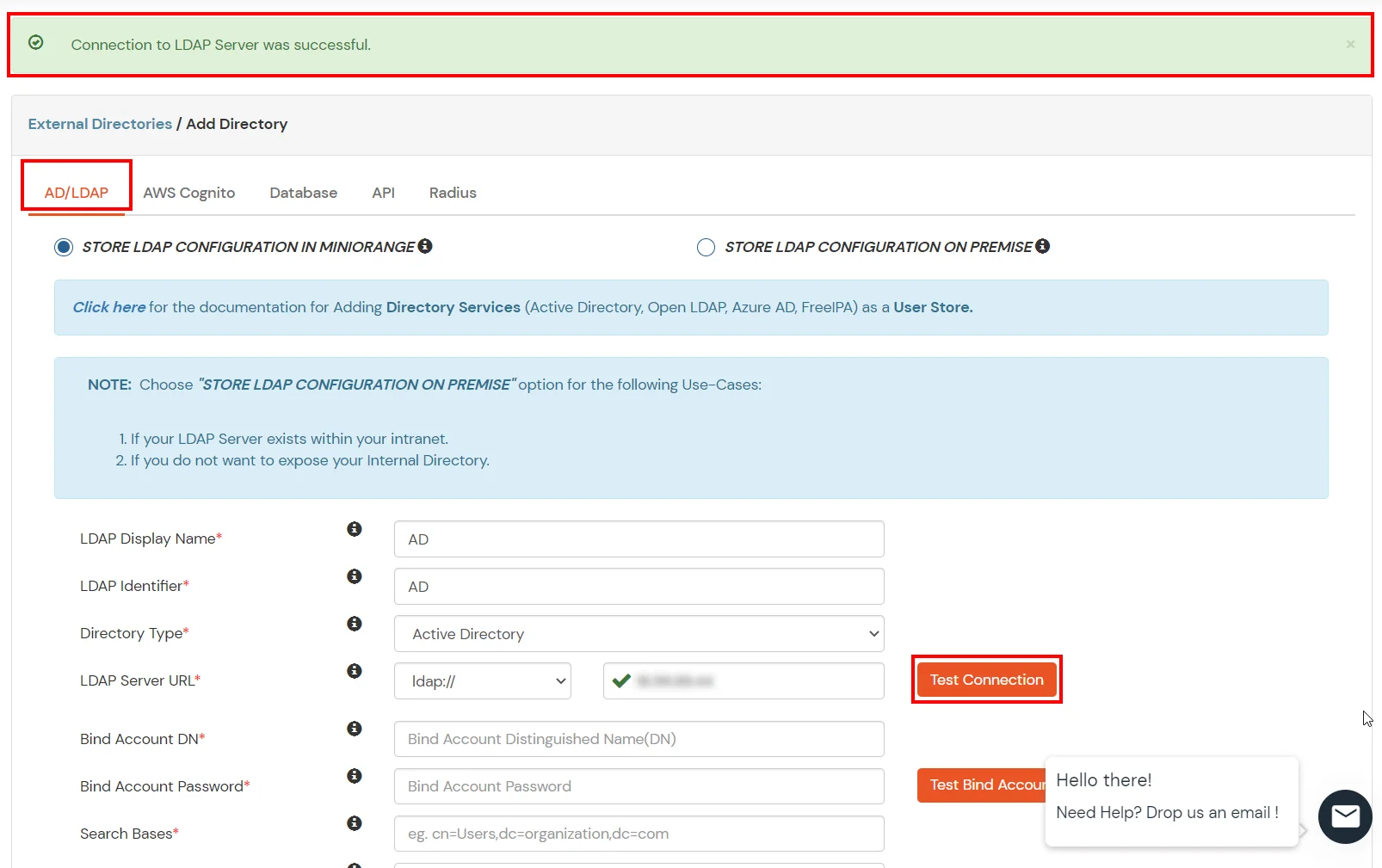
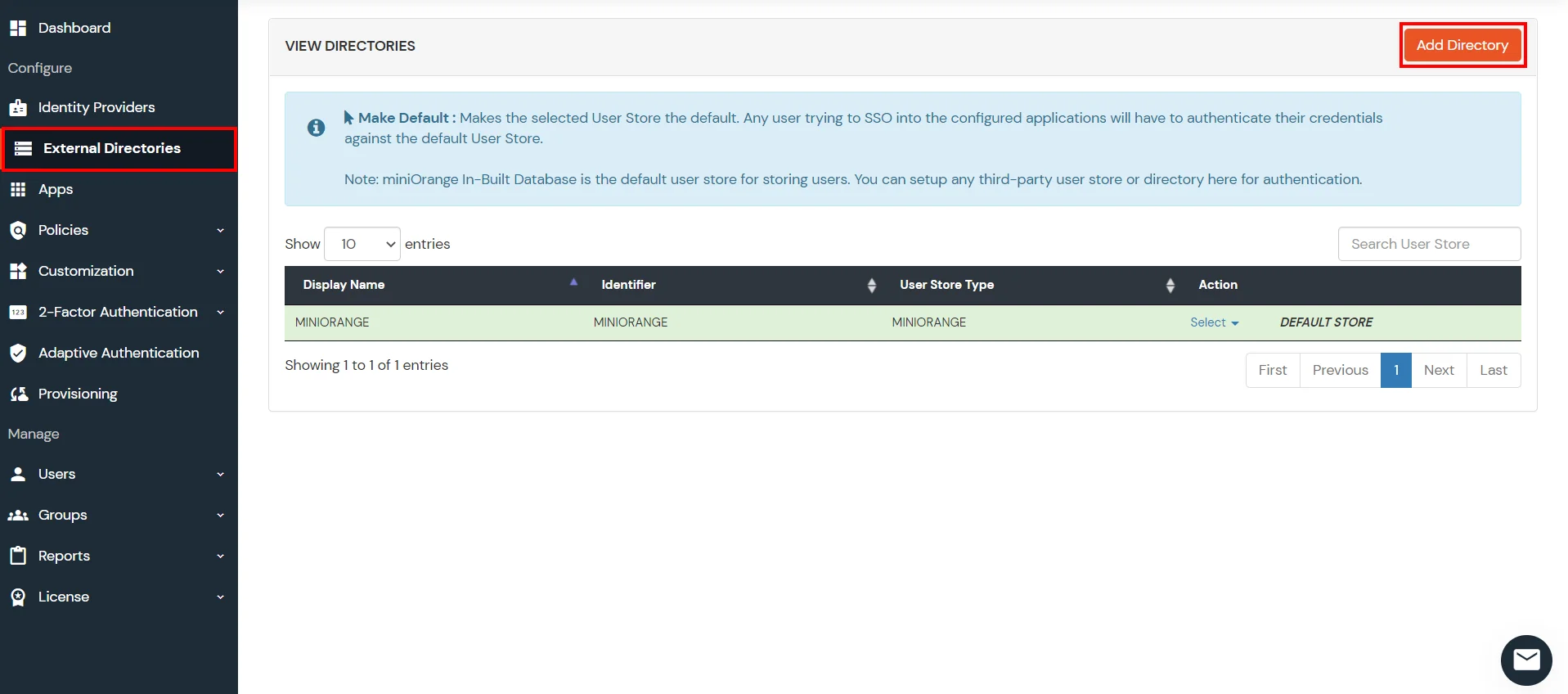
- Click on External Directories >> Add Directory in the left menu of the dashboard.
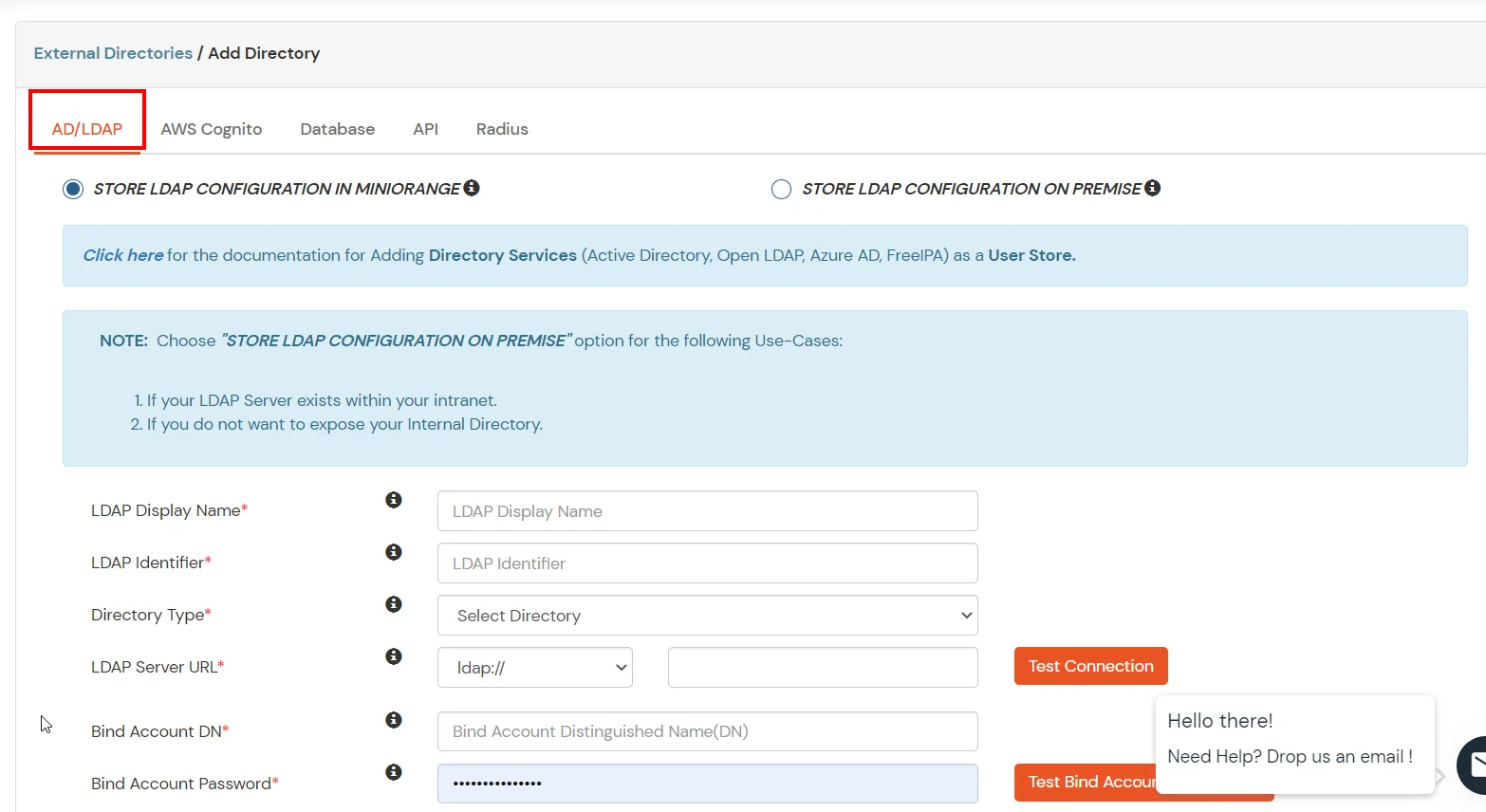
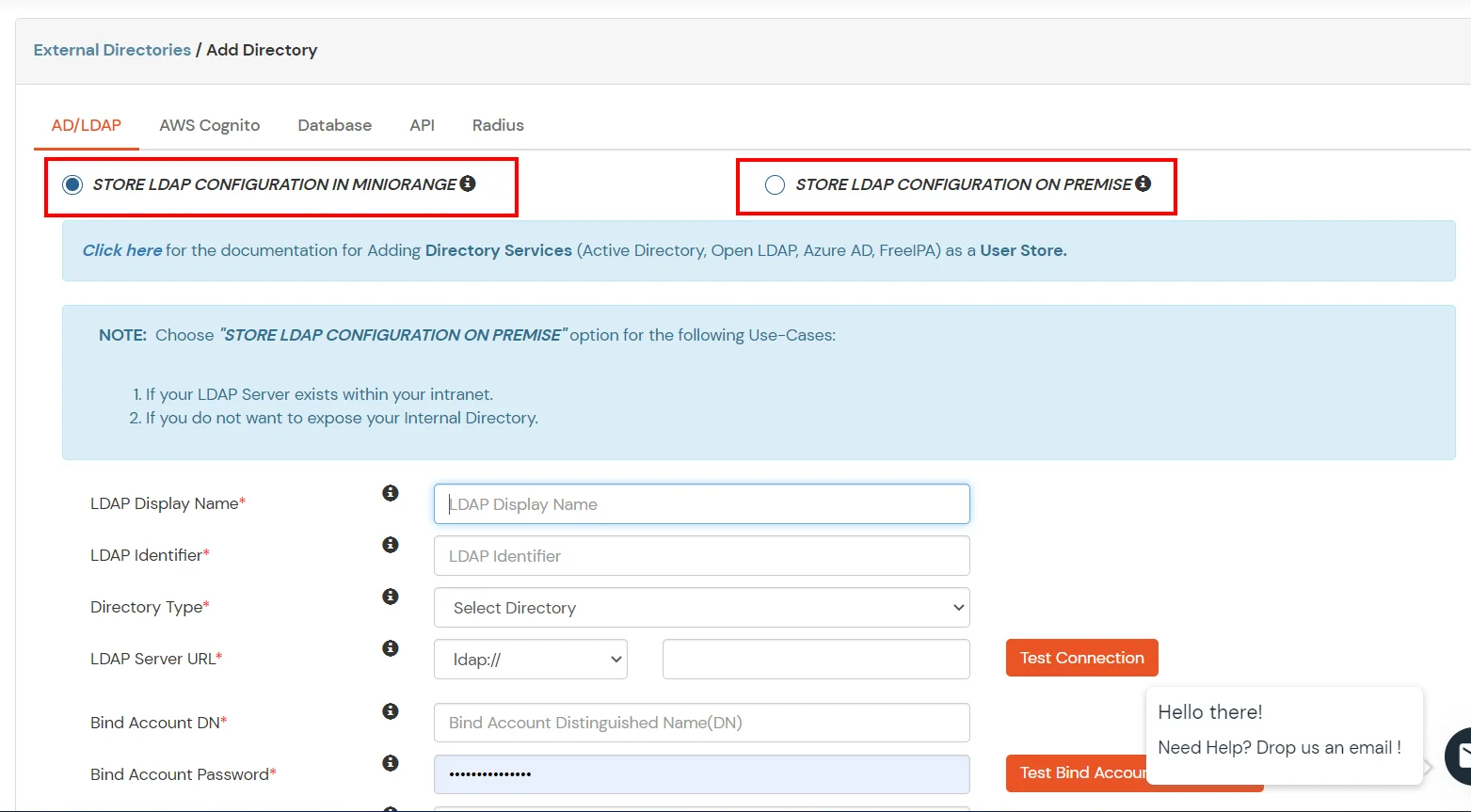
- Select Directory type as AD/LDAP.
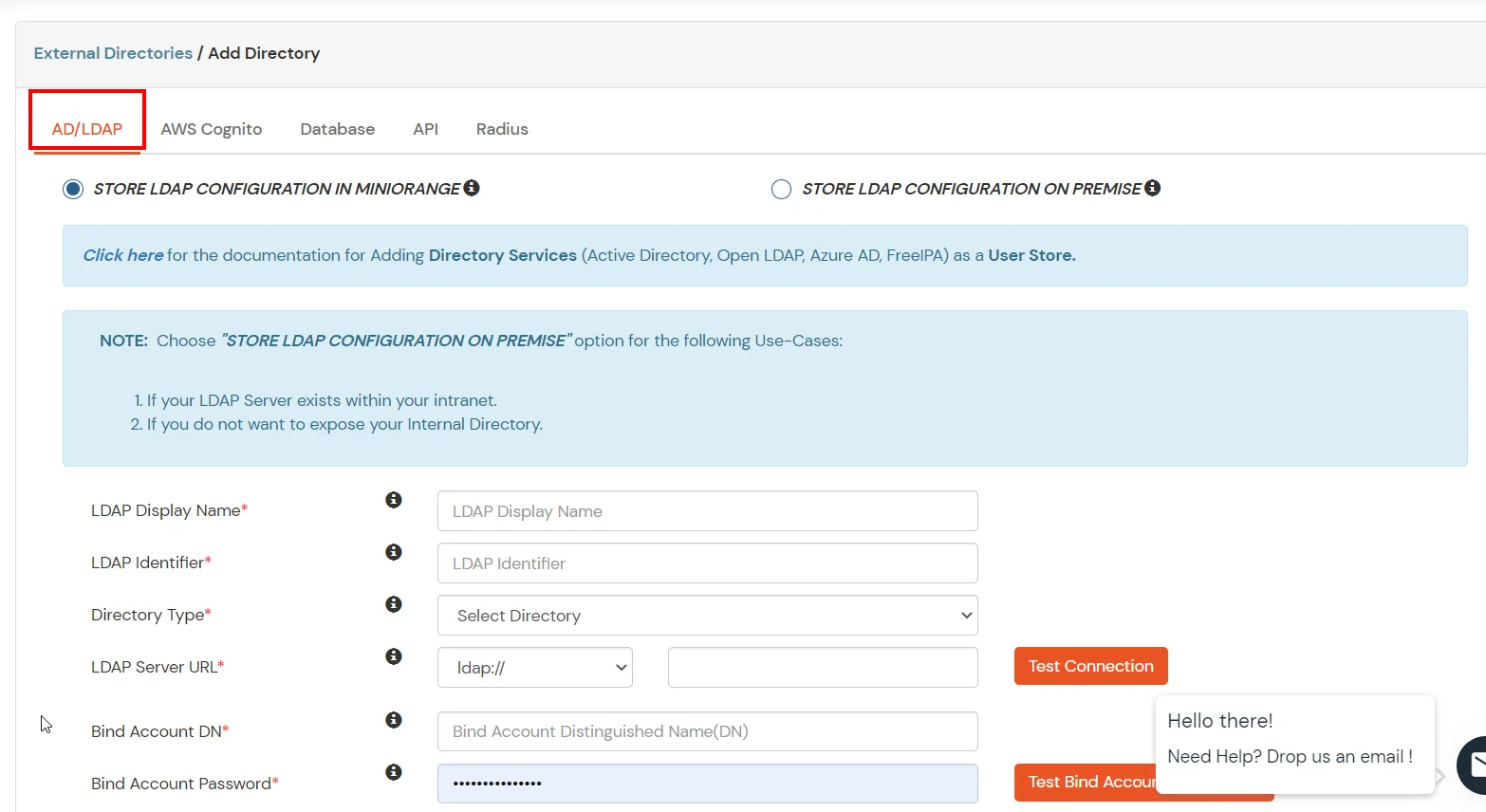
- STORE LDAP CONFIGURATION IN MINIORANGE: Choose this option if you want to keep your configuration in miniOrange. If active directory is behind a firewall, you will need to open the firewall to allow incoming requests to your AD.
- STORE LDAP CONFIGURATION ON PREMISE: Choose this option if you want to keep your configuration in your premise and only allow access to AD inside premises. You will have to download and install miniOrange gateway in your premise.
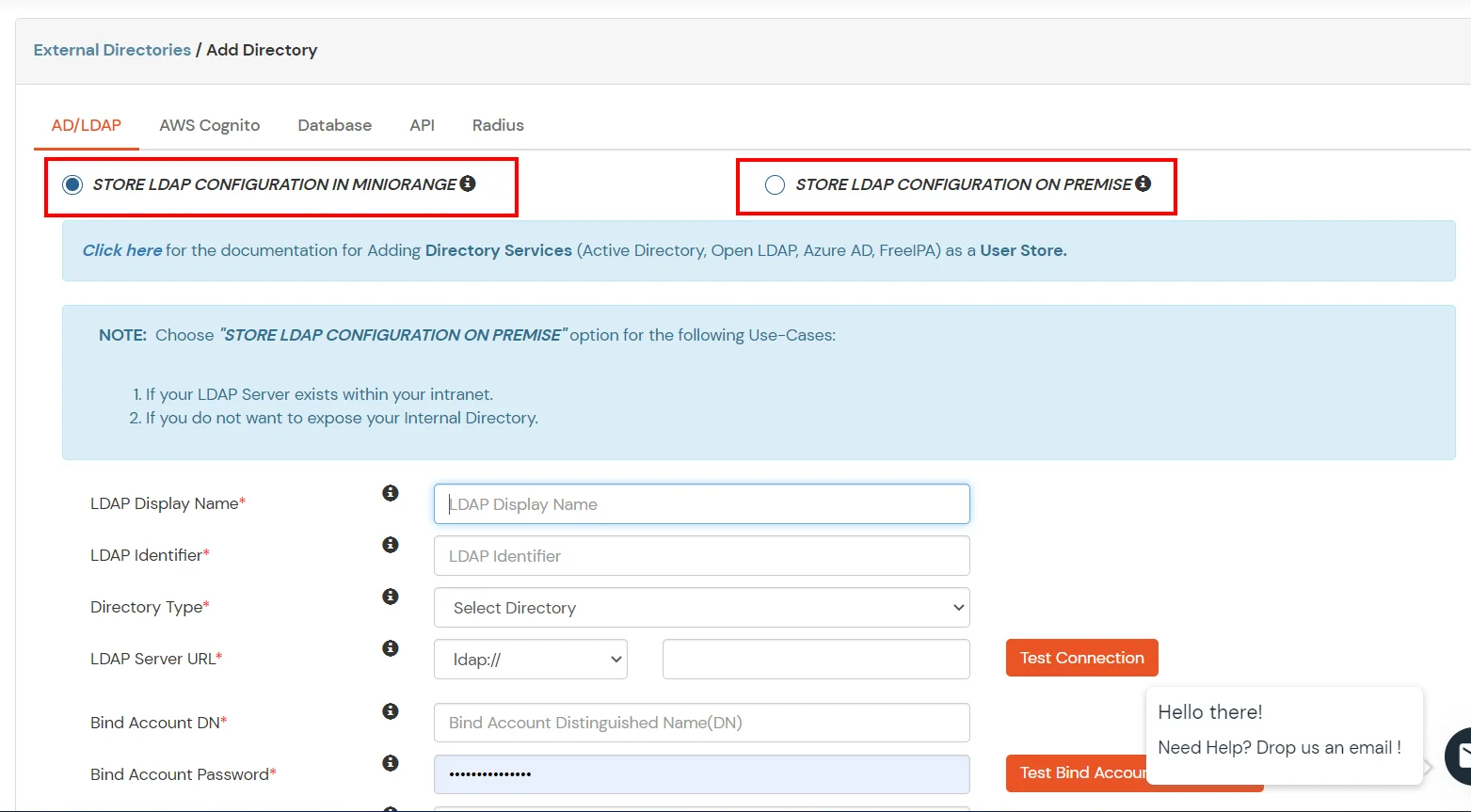
- Enter LDAP Display Name and LDAP Identifier name.
- Select Directory Type as Active Directory.
- Enter the LDAP Server URL or IP Address against LDAP Server URL field.
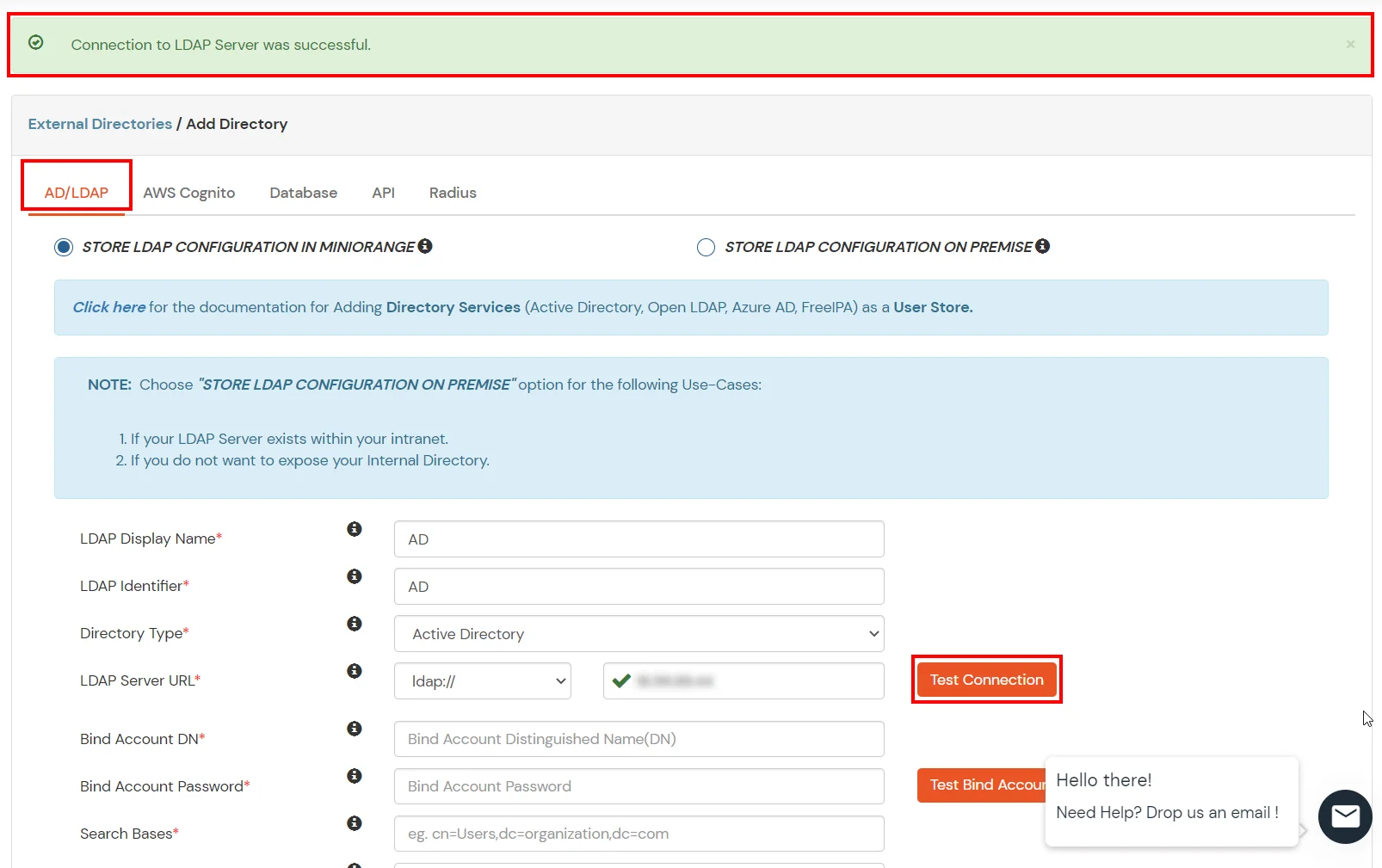
- Click on Test Connection button to verify if you have made a successful connection with your LDAP server.
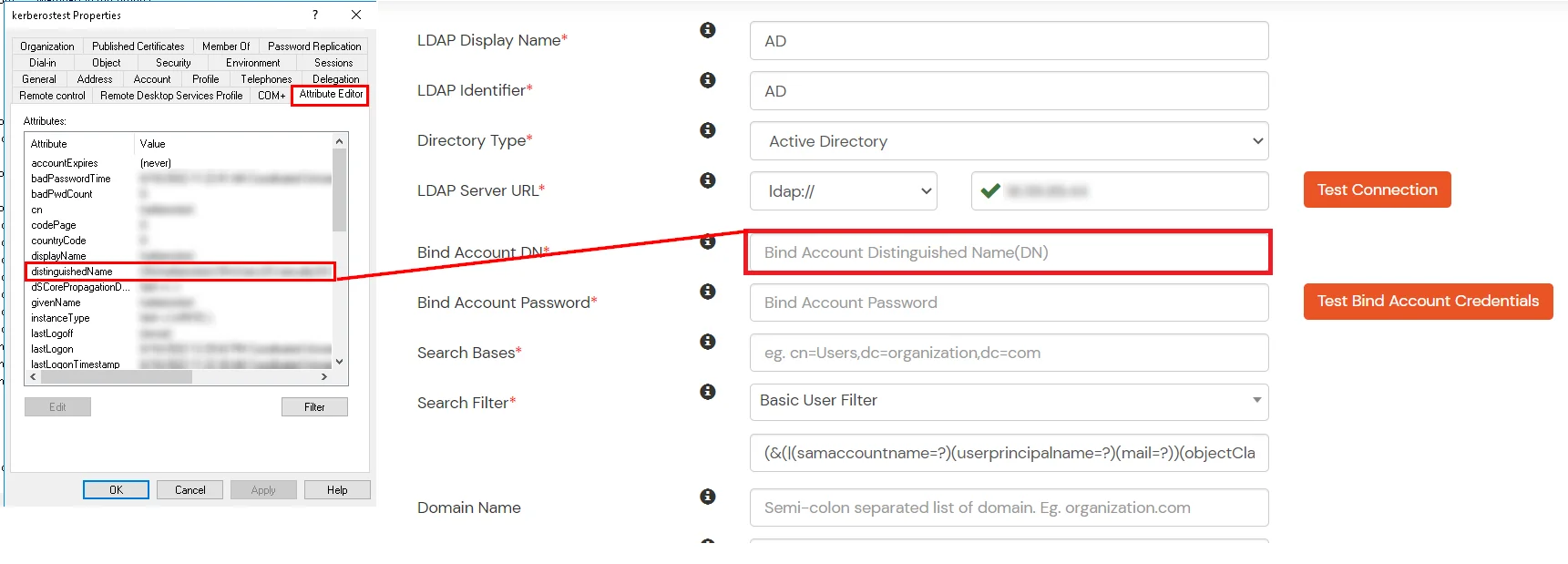
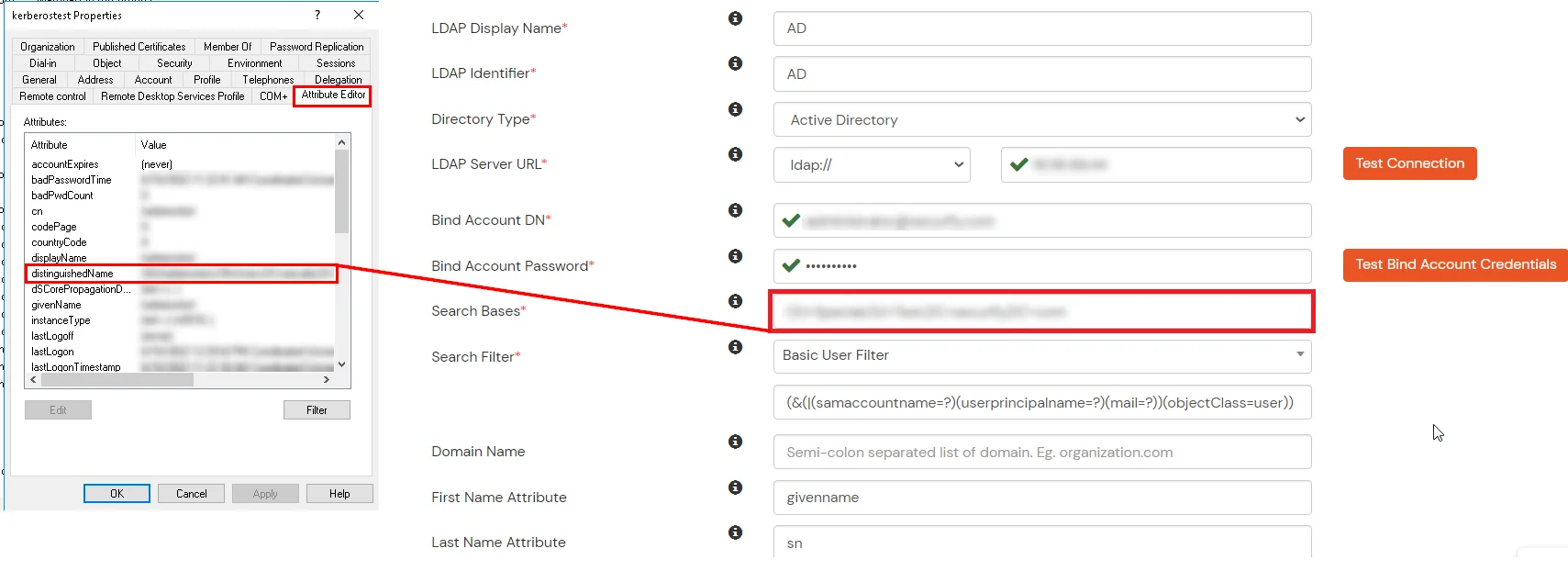
- In Active Directory, go to the properties of user containers/OU's and search for Distinguished Name attribute.
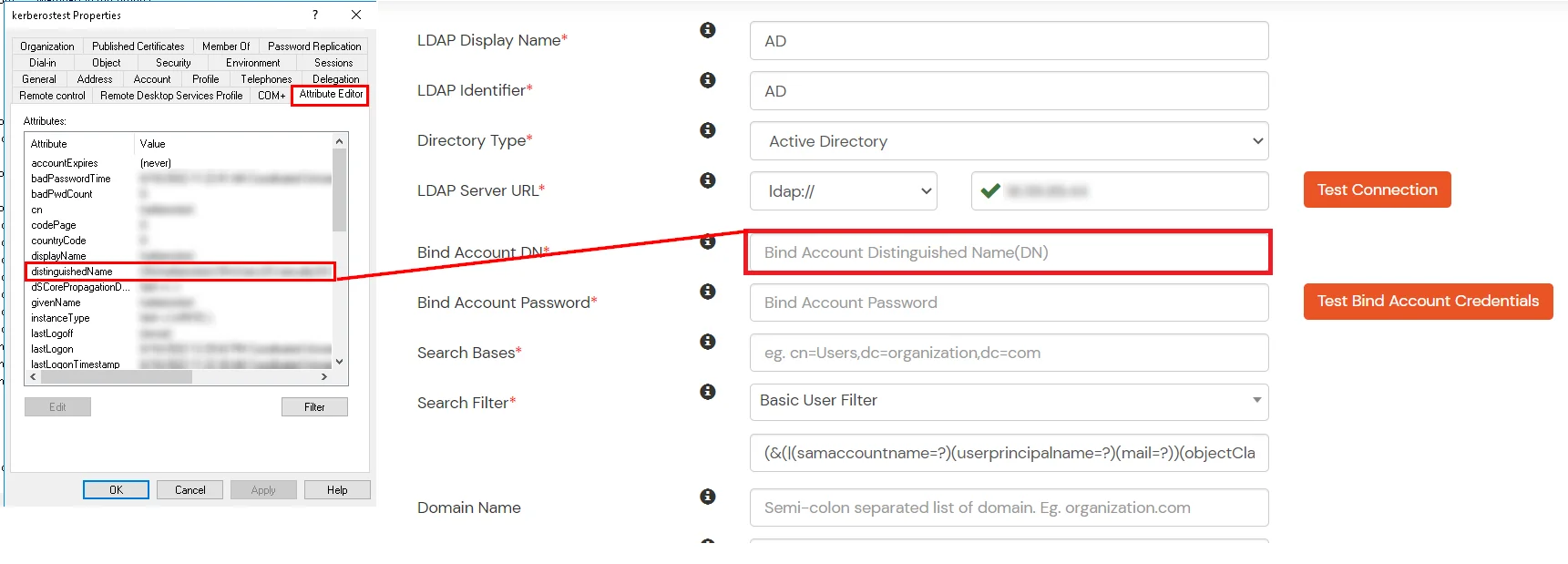
- Enter the valid Bind account Password.
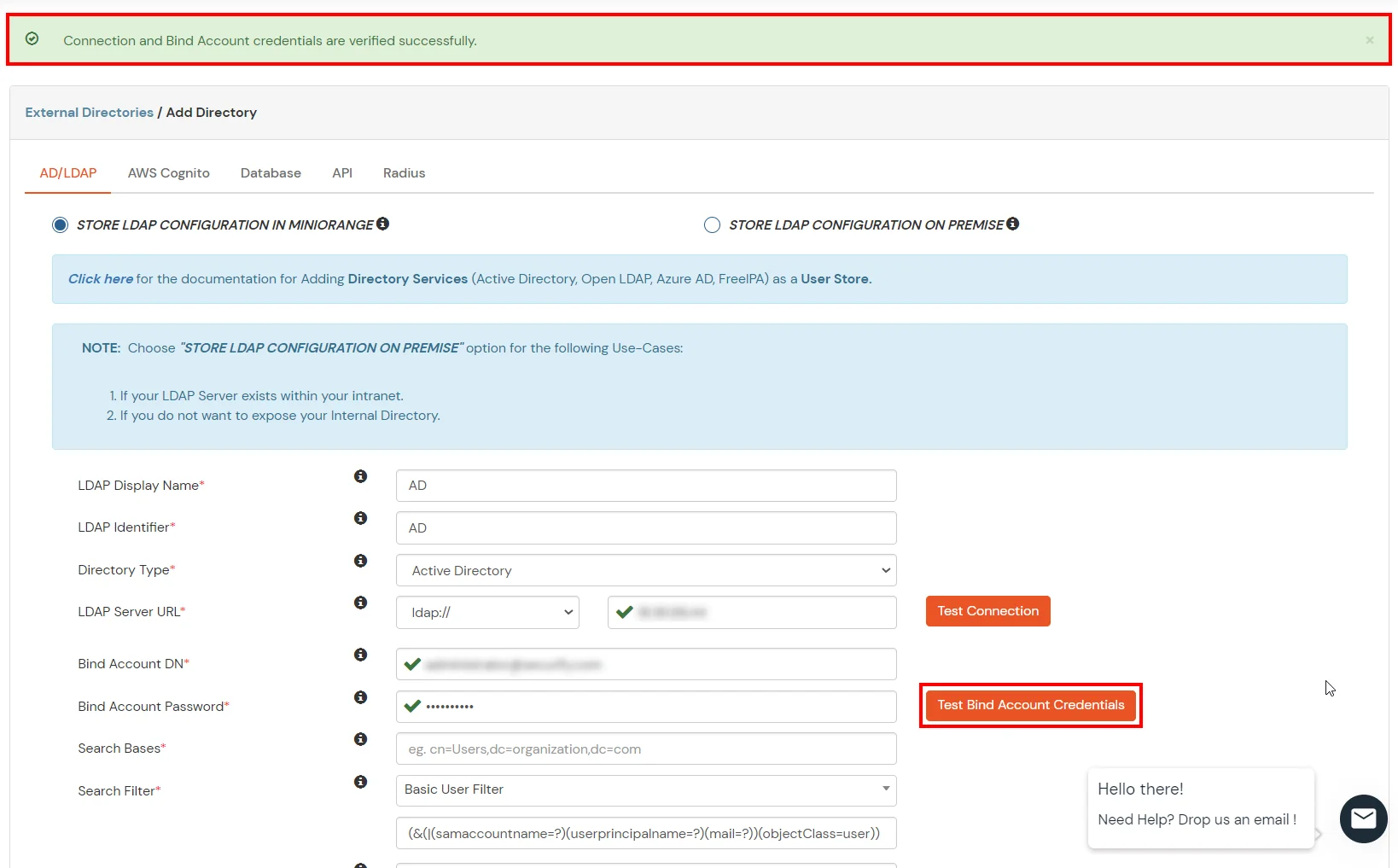
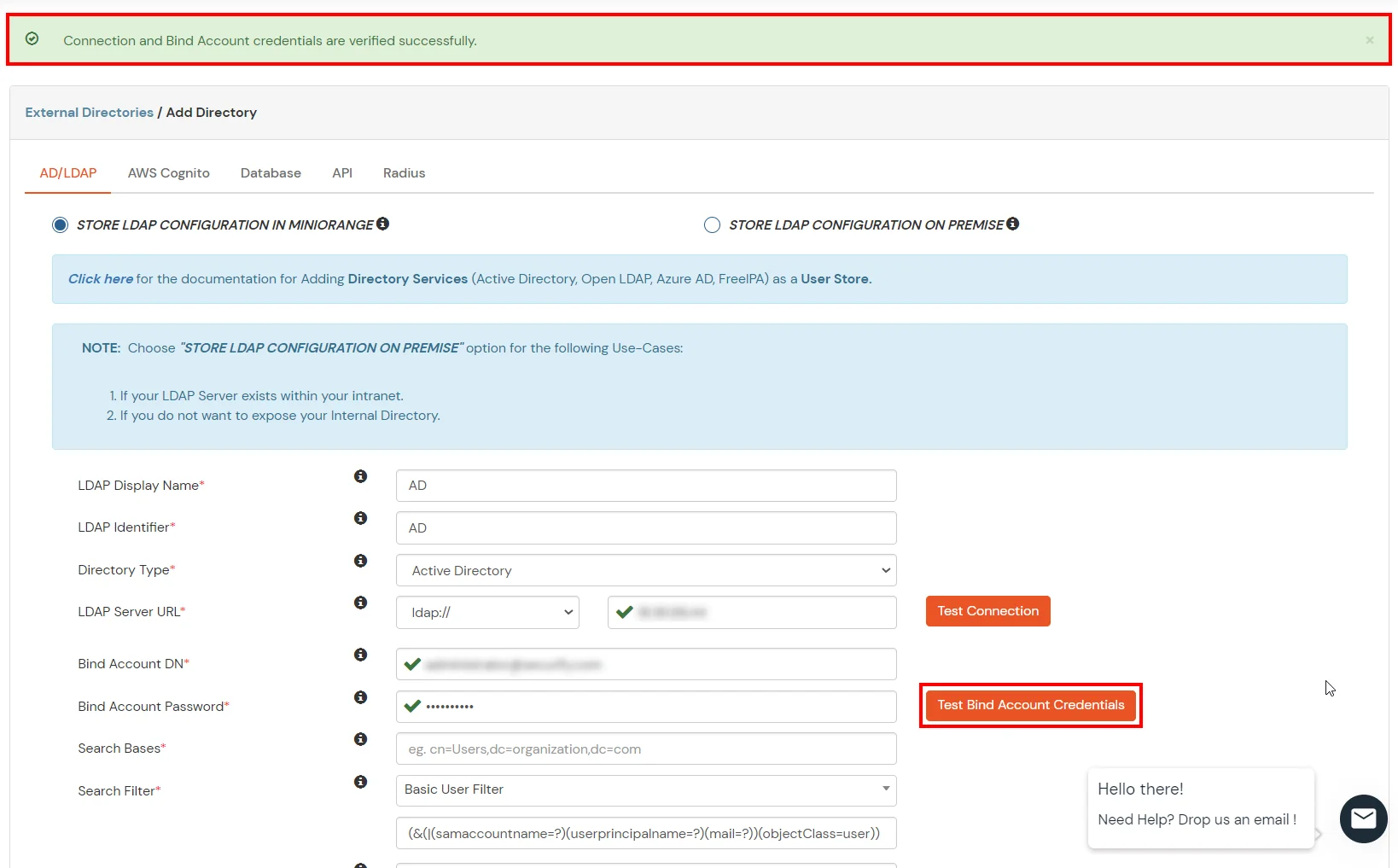
- Click on Test Bind Account Credentials button to verify your LDAP Bind credentials for LDAP connection.
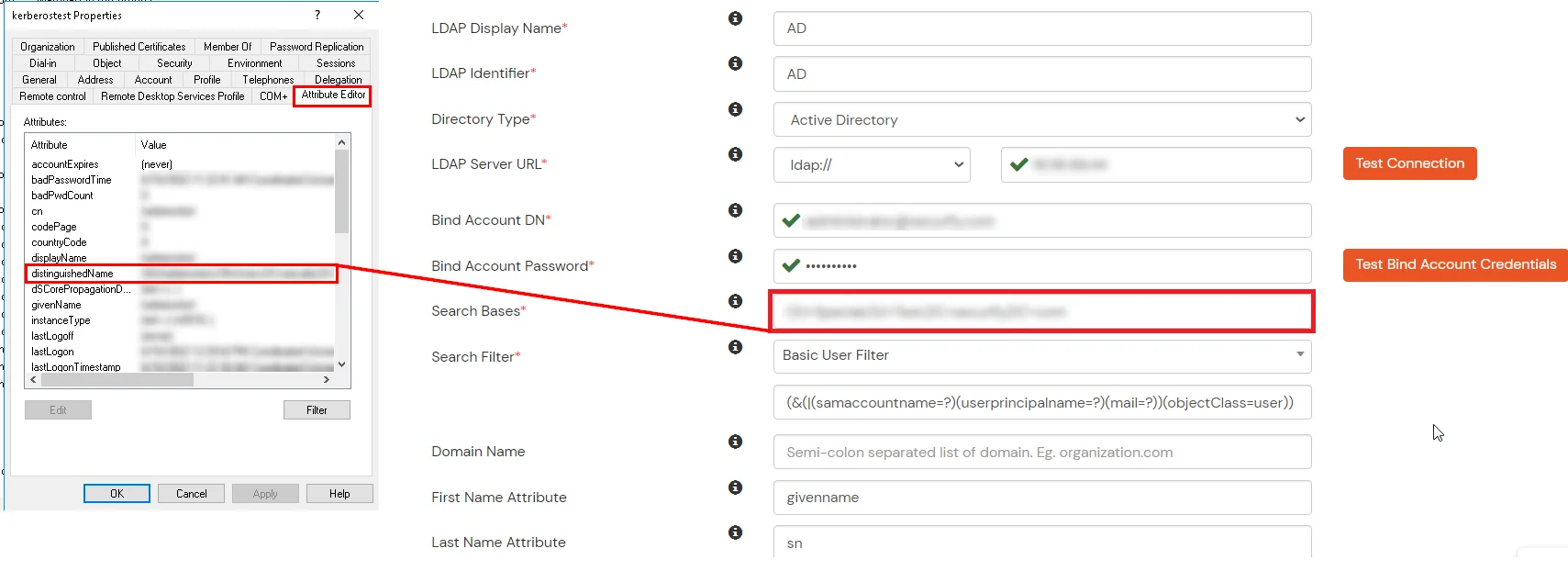
- Search Base is the location in the directory where the search for a user begins. You will get this from the same place you got your Distinguished name.
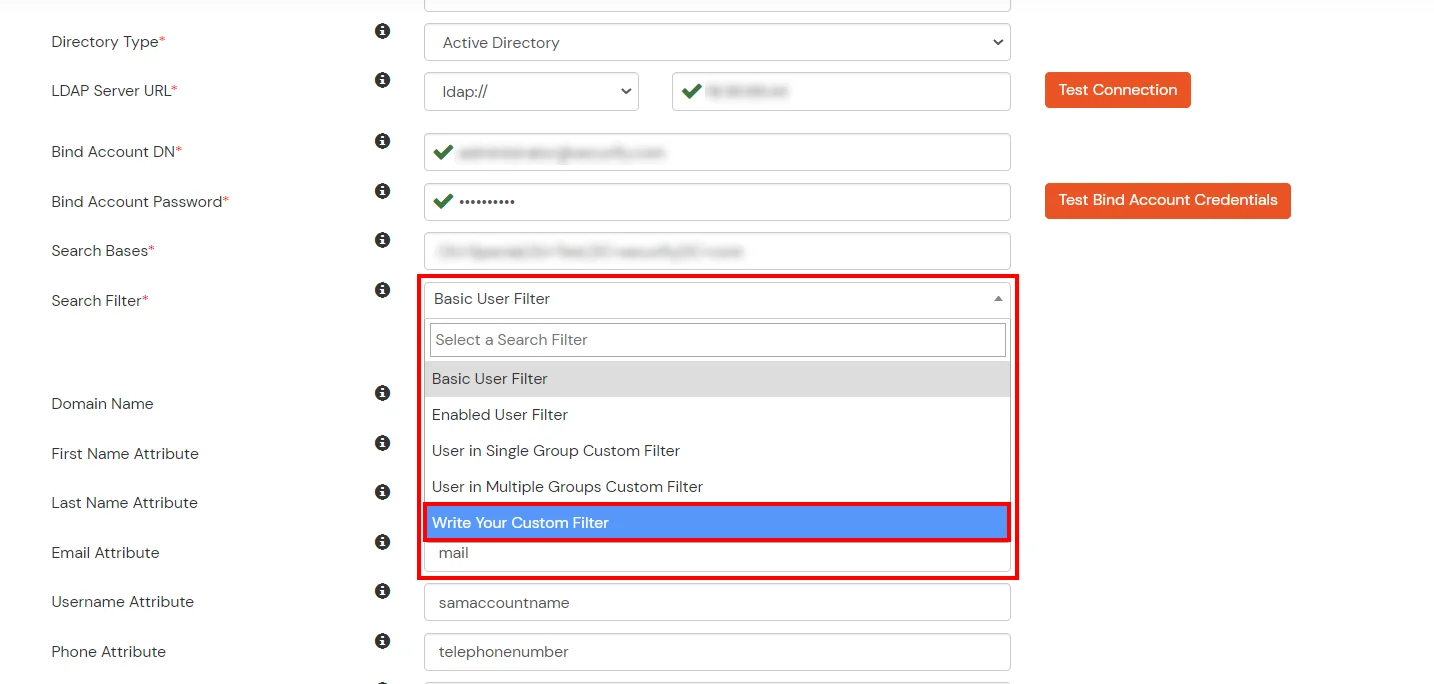
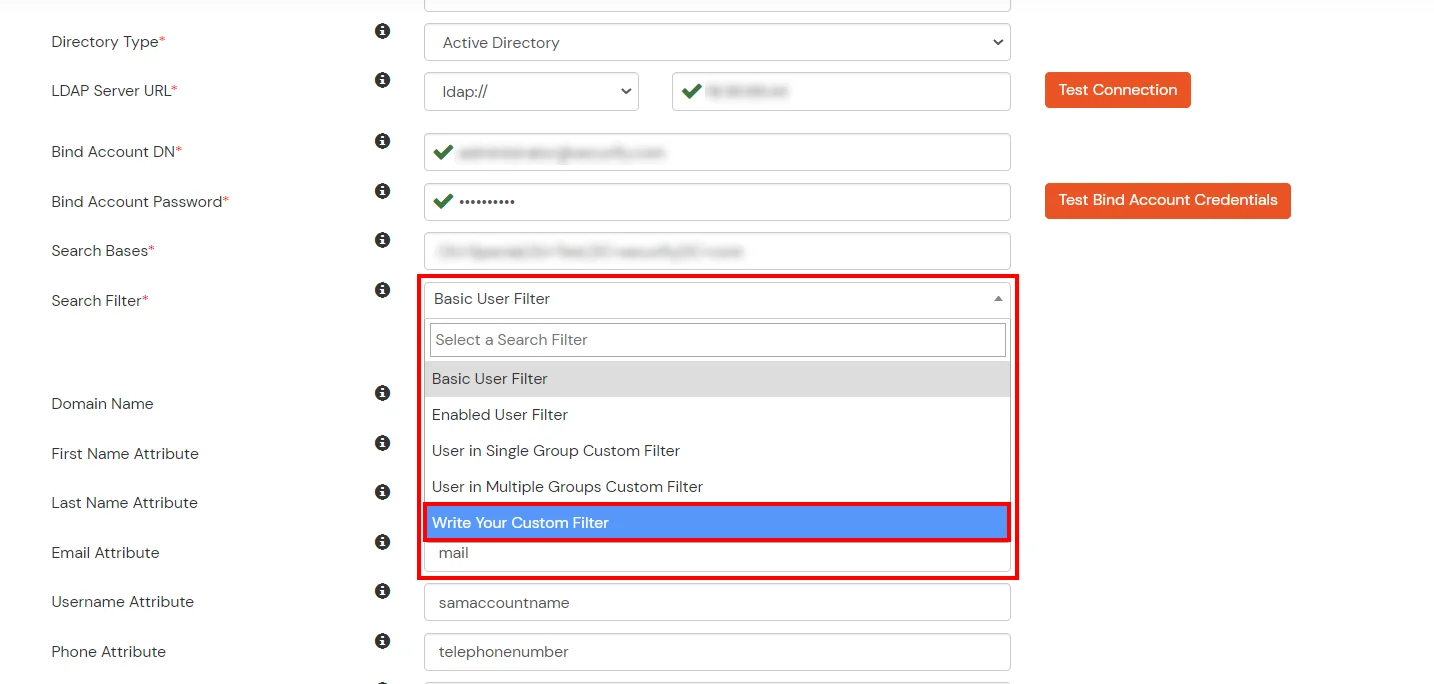
- Select a suitable Search filter from the drop-down menu. To use custom Search Filter select "Write your Custom Filter" option and customize it accordingly.
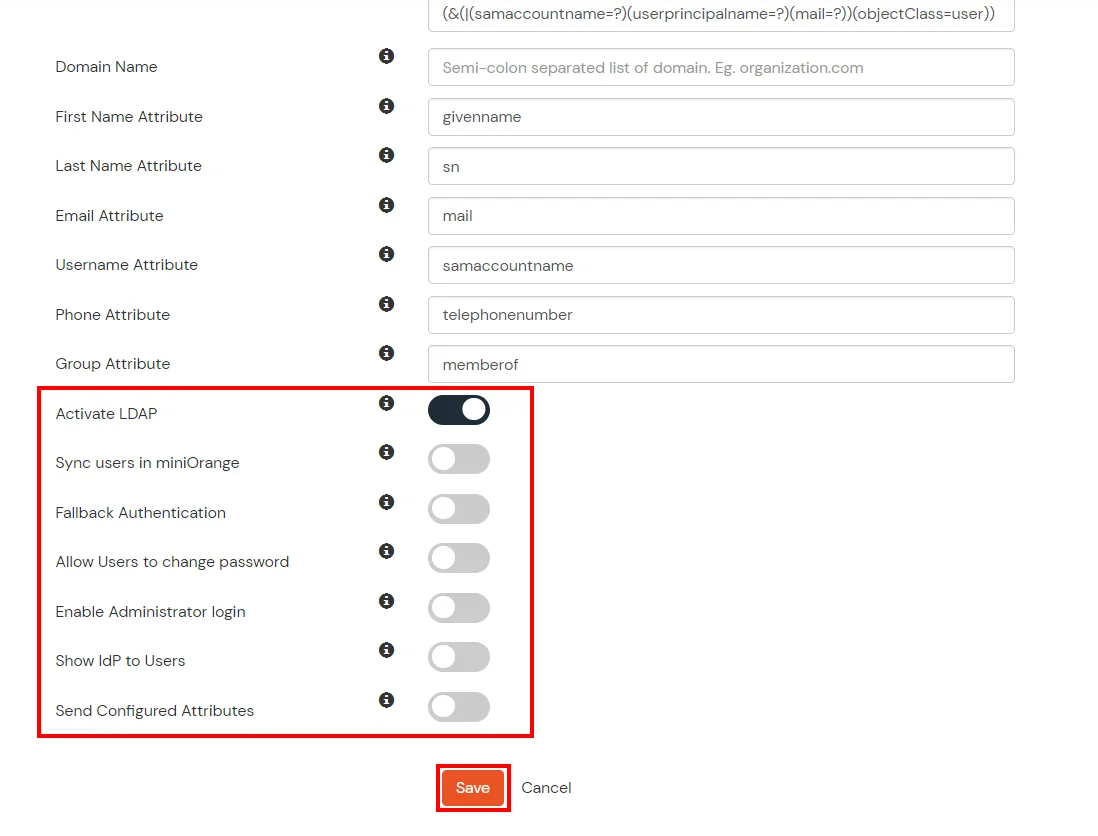
- You can also configure following options while setting up AD. Enable Activate LDAP in order to authenticate users from AD/LDAP. Click on the Save button to add user store.
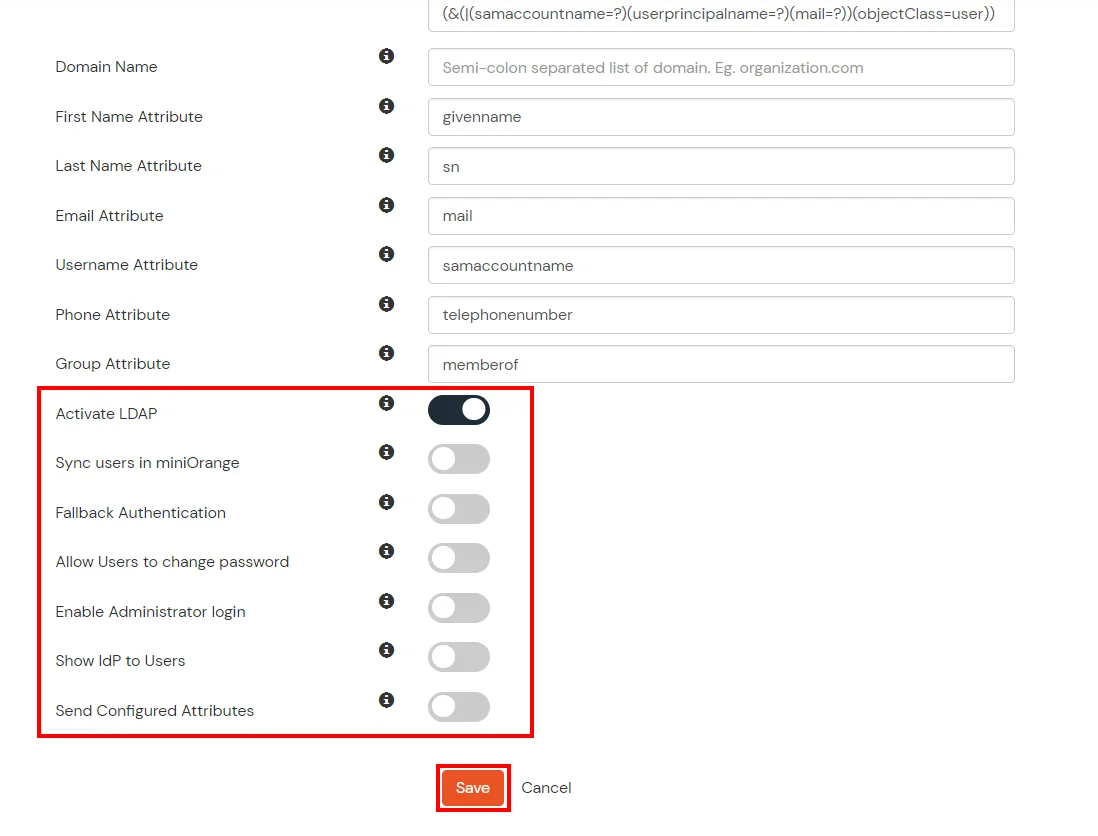
Here's the list of the attributes and what it does when we enable it. You can enable/disable accordingly.
| Attribute |
Description |
| Activate LDAP |
All user authentications will be done with LDAP credentials if you Activate it |
| Sync users in miniOrange |
Users will be created in miniOrange after authentication with LDAP |
| Fallback Authentication |
If LDAP credentials fail then user will be authenticated through miniOrange |
| Allow users to change password |
This allows your users to change their password. It updates the new credentials in your LDAP server |
| Enable administrator login |
On enabling this, your miniOrange Administrator login authenticates using your LDAP server |
| Show IdP to users |
If you enable this option, this IdP will be visible to users |
| Send Configured Attributes |
If you enable this option, then only the attributes configured below will be sent in attributes at the time of login |
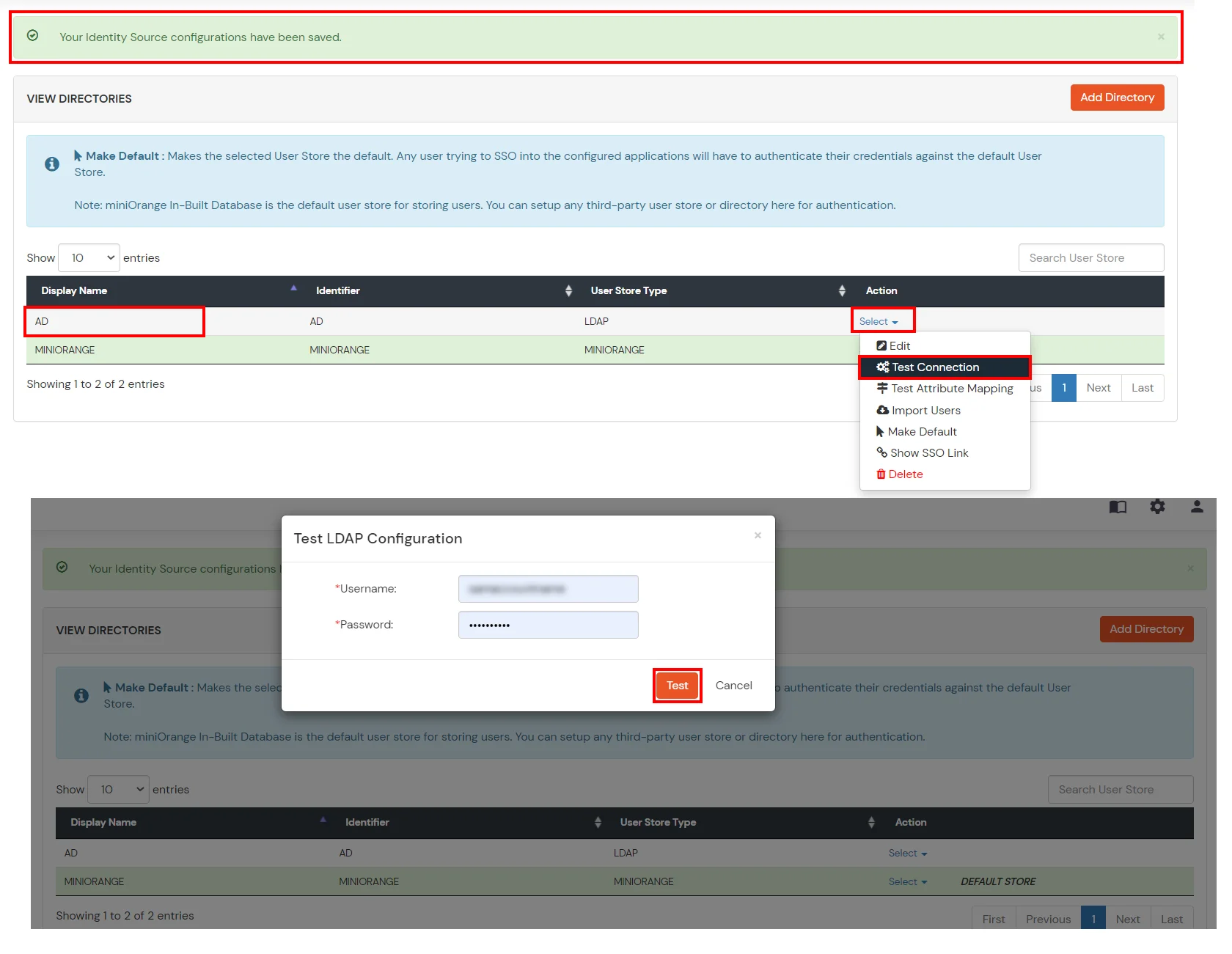
- Click on Save. After this, it will show you the list of User stores. Click on Test Connection to check whether you have enter valid details. For that, it will ask for username and password.
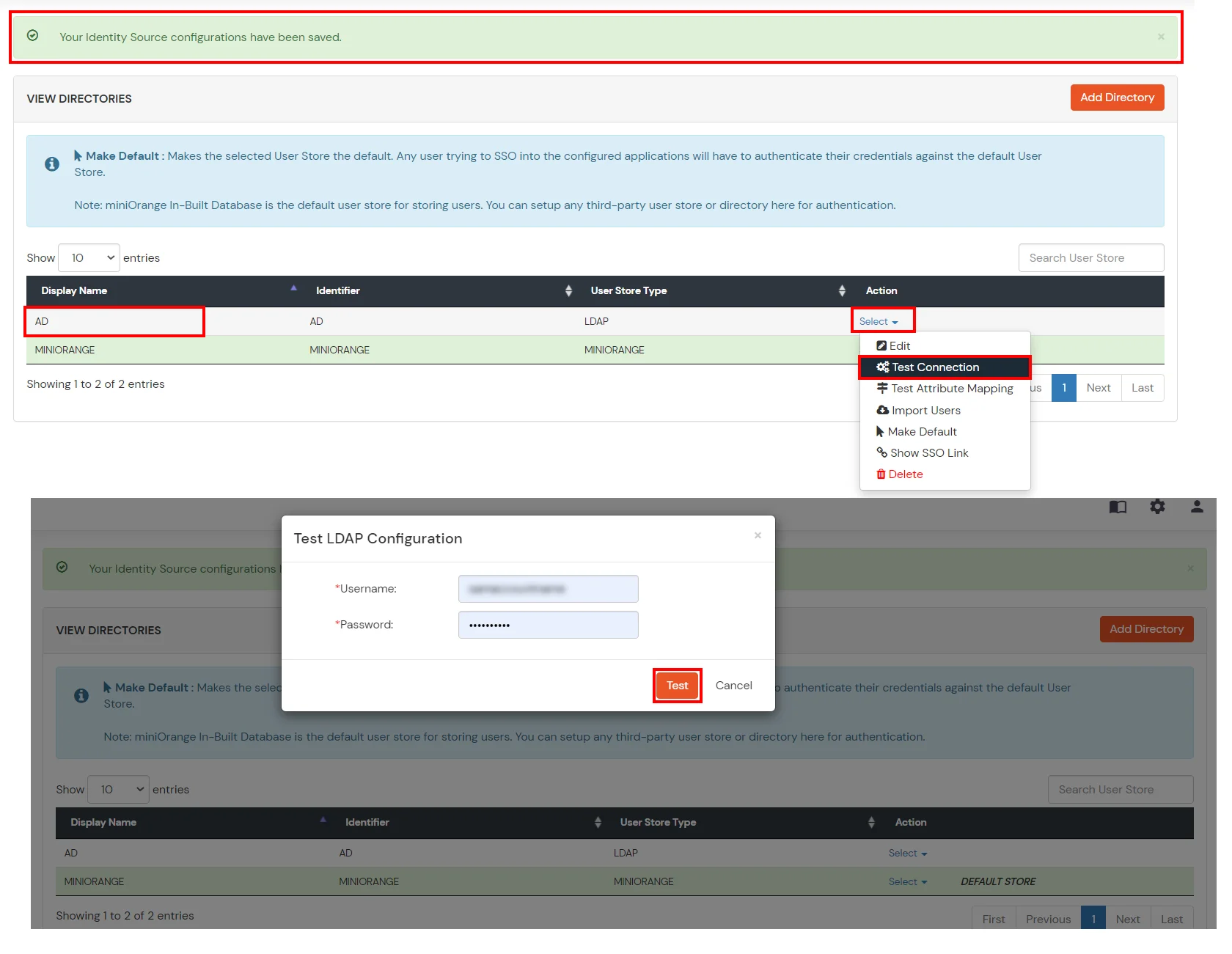
- On Successful connection with LDAP Server, a success message is shown.
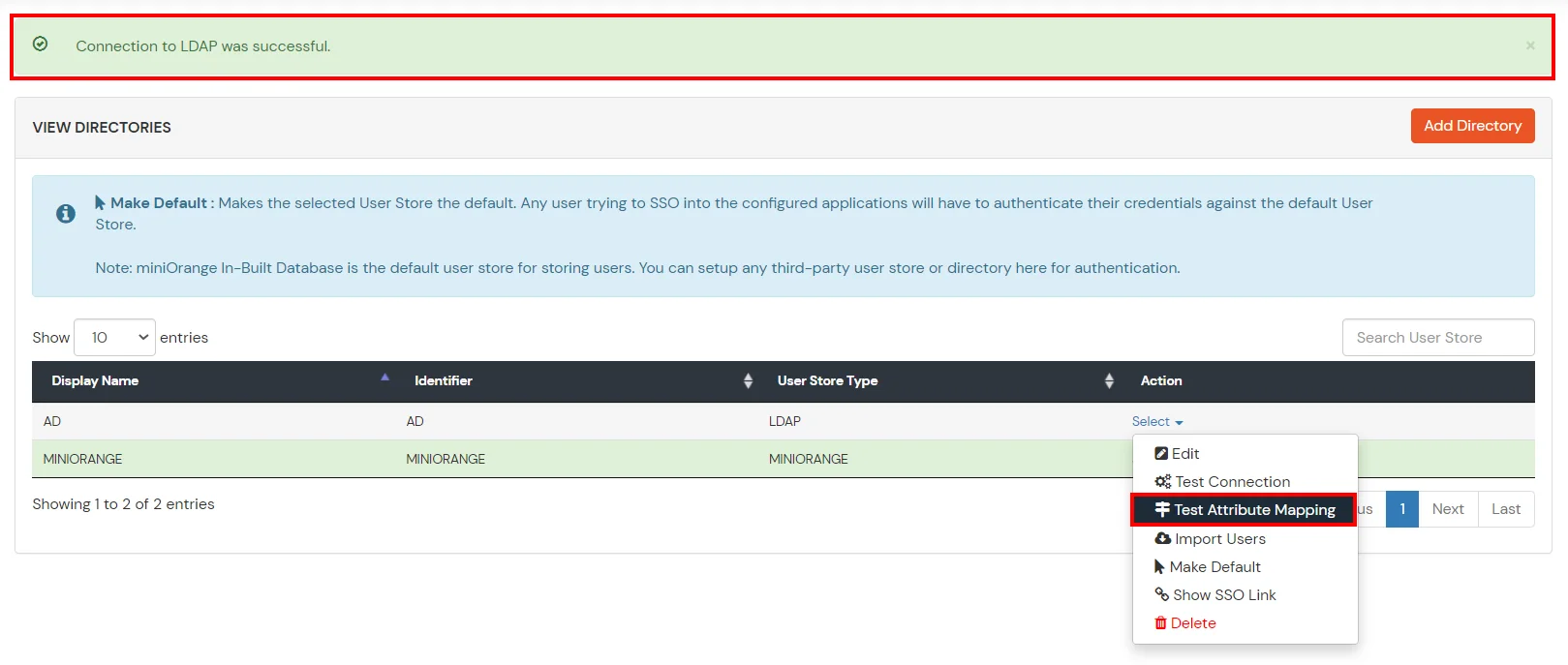
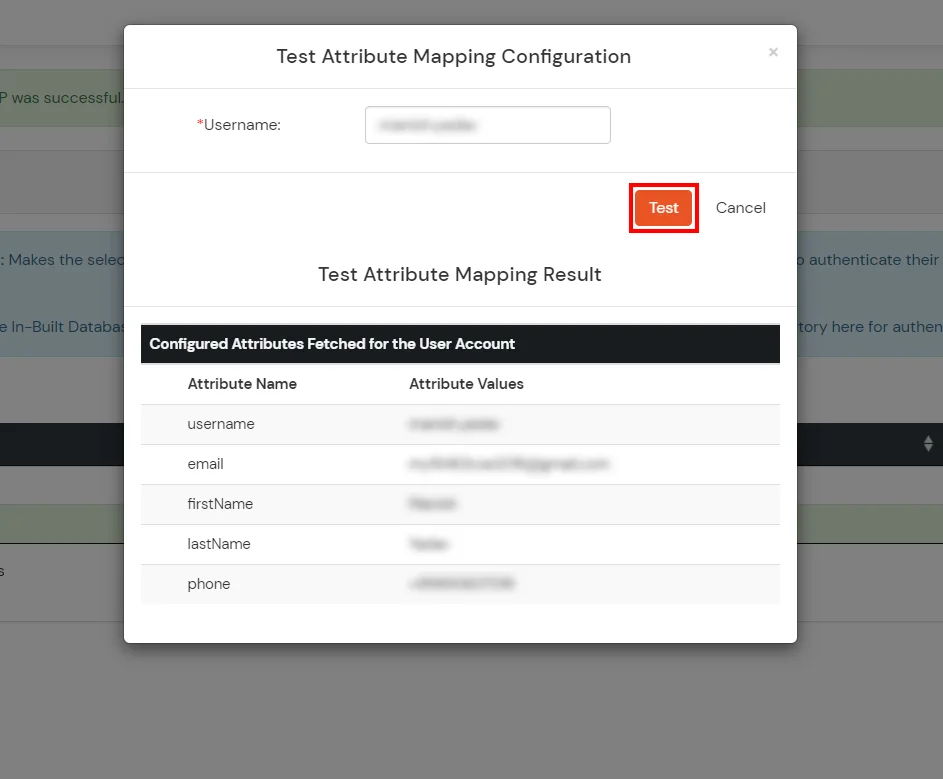
- Click on Test Attribute Mapping.
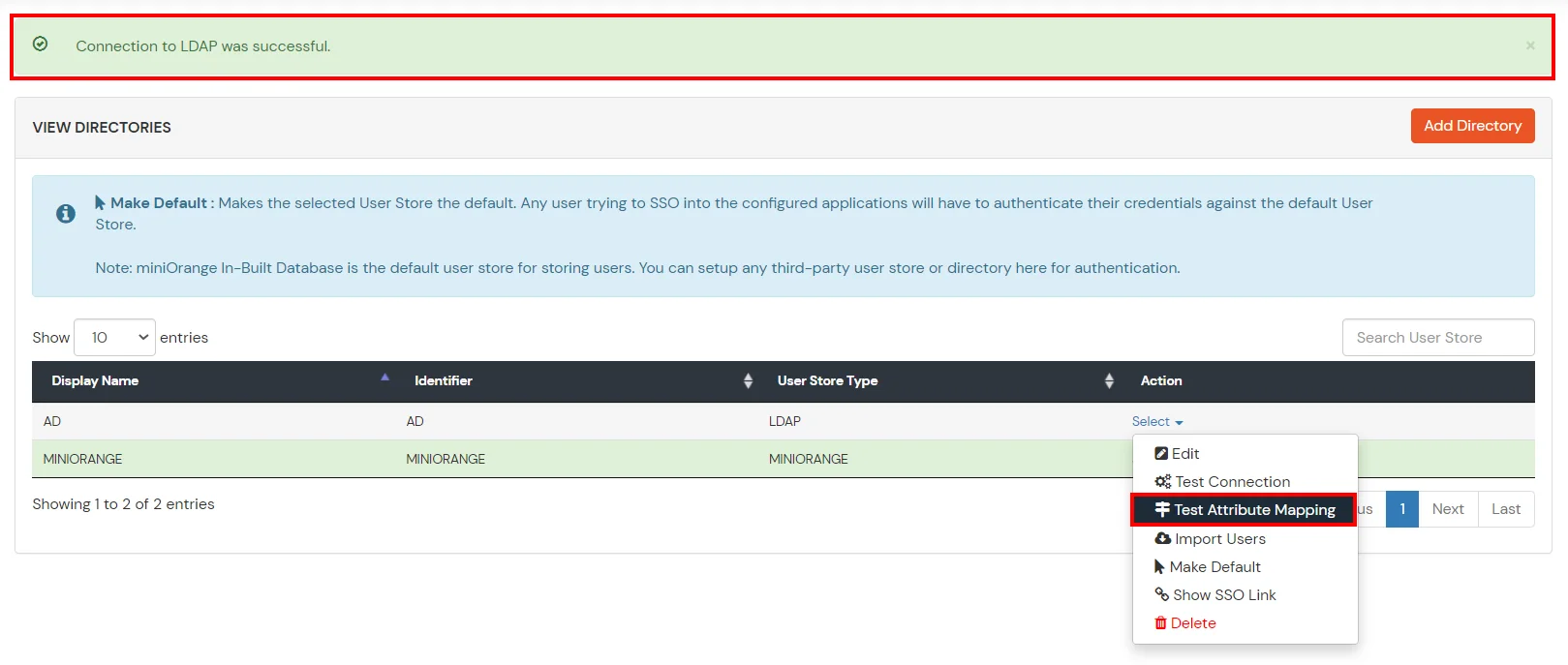
- Enter a valid Username. Then, click on Test. Mapped Attributes corresponding to the user are fetched.
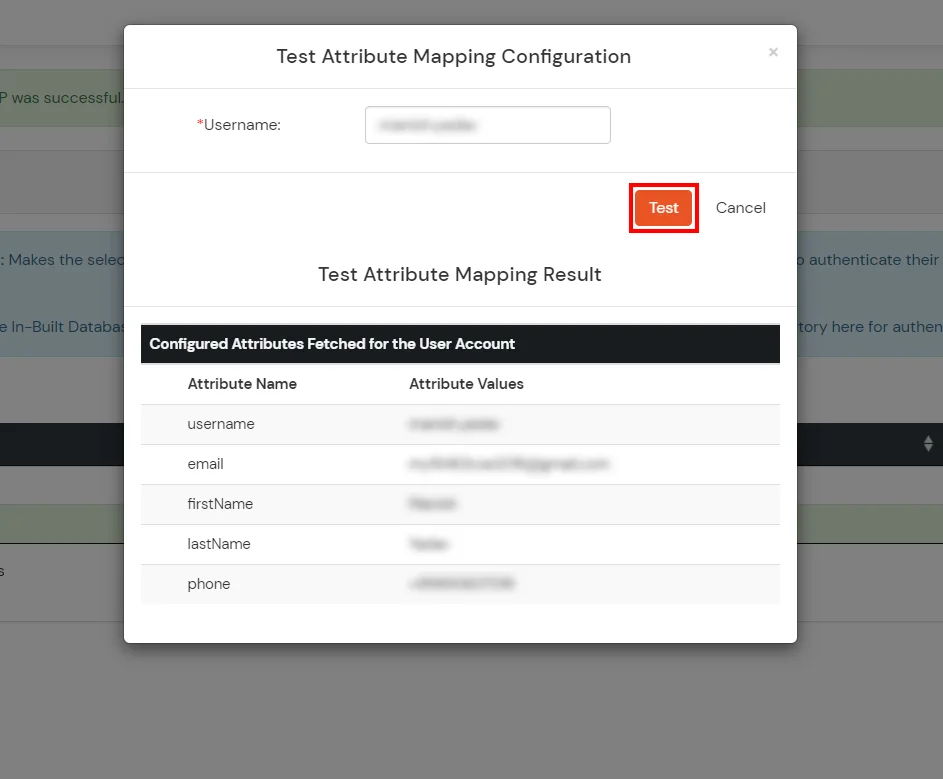
- After successful Attribute Mapping Configuration, go back to the ldap configuration and enable Activate LDAP in order to authenticate users from AD/LDAP.
Refer our guide to setup LDAPS on windows server.
User Import and Provisioning from AD
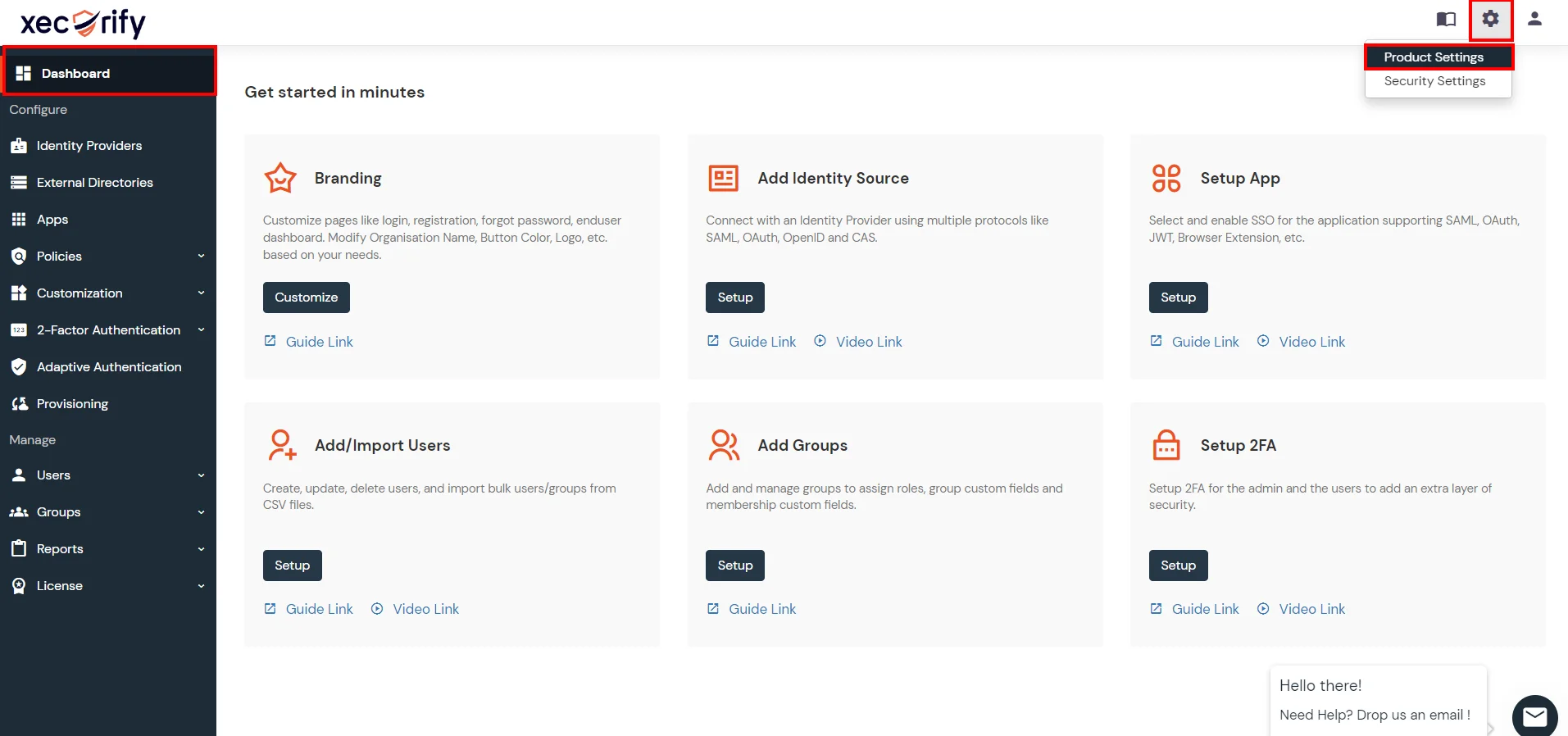
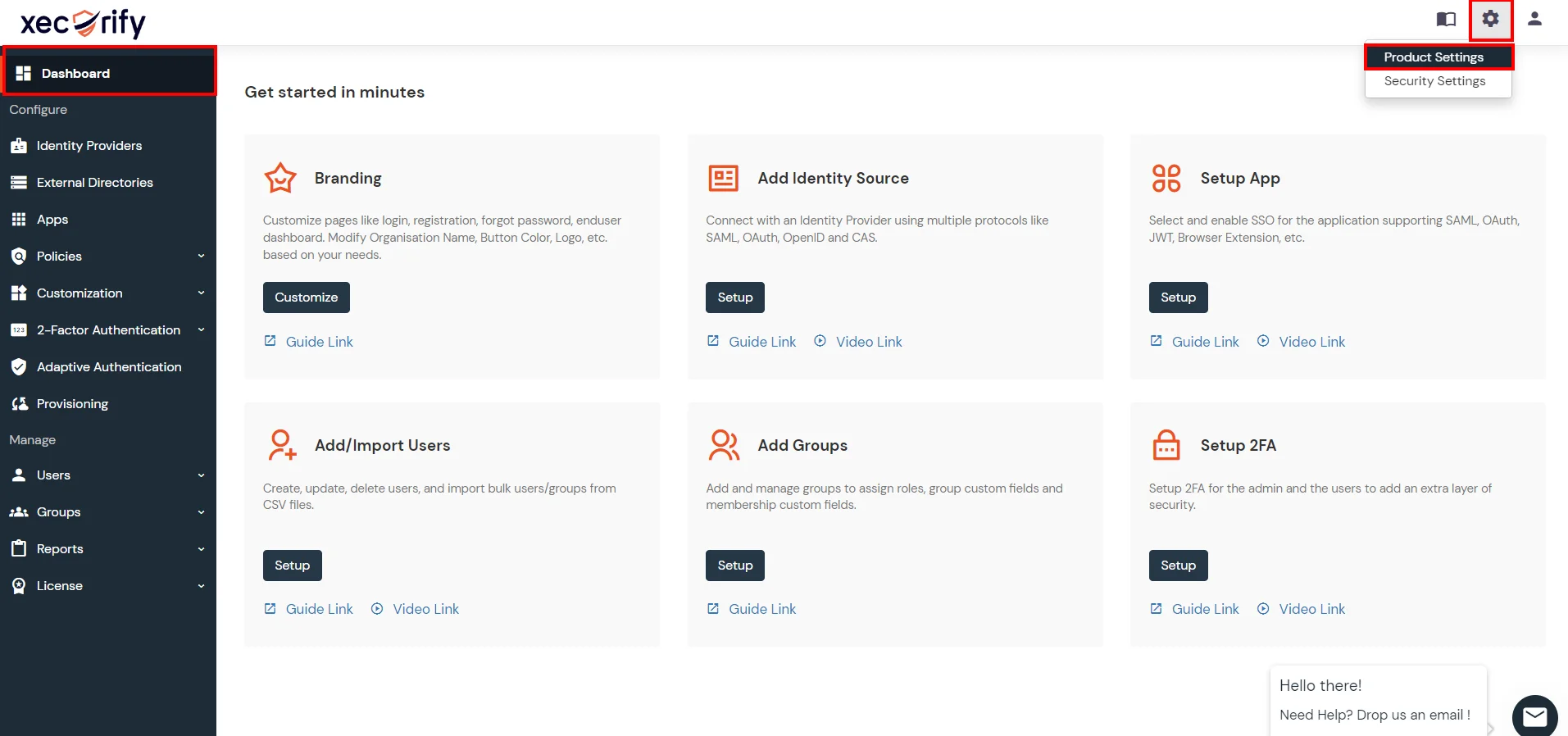
- Go to Settings >> Product Settings in the Customer Admin Account.
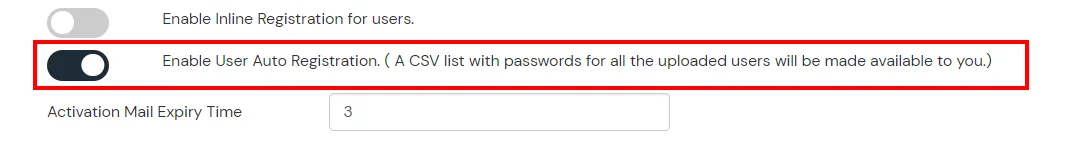
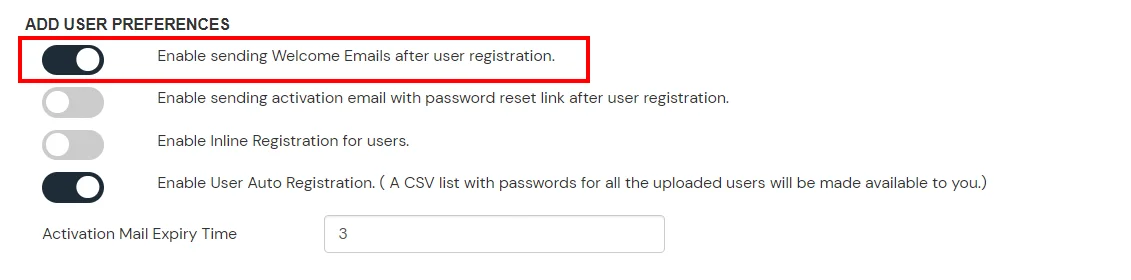
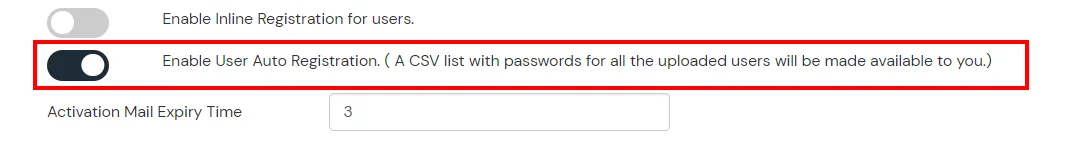
- Enable the "Enable User Auto Registration" option and click Save.
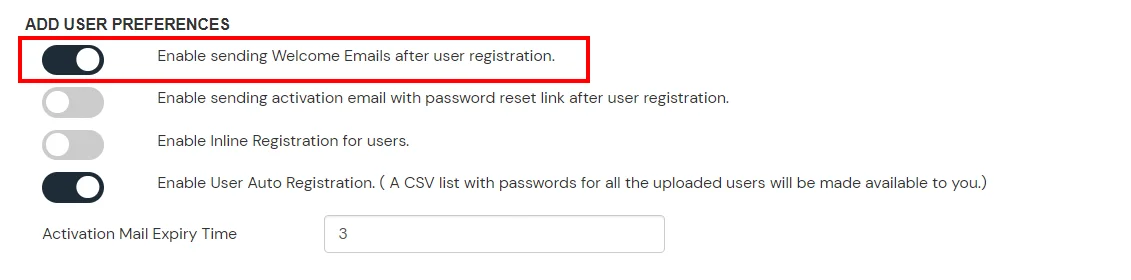
- (Optional) To send a welcome email to all the end users that will be imported, enable the "Enable sending Welcome Emails after user registration" option and click Save.
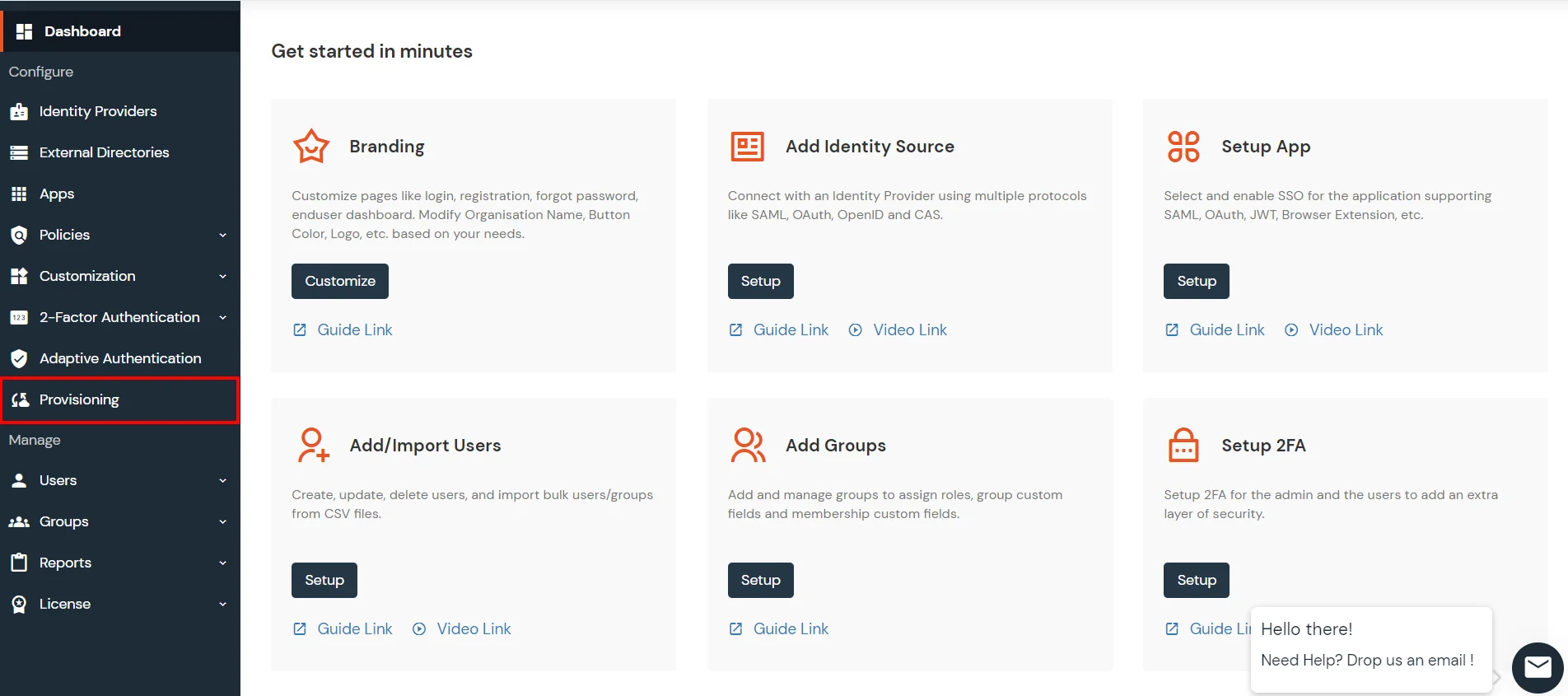
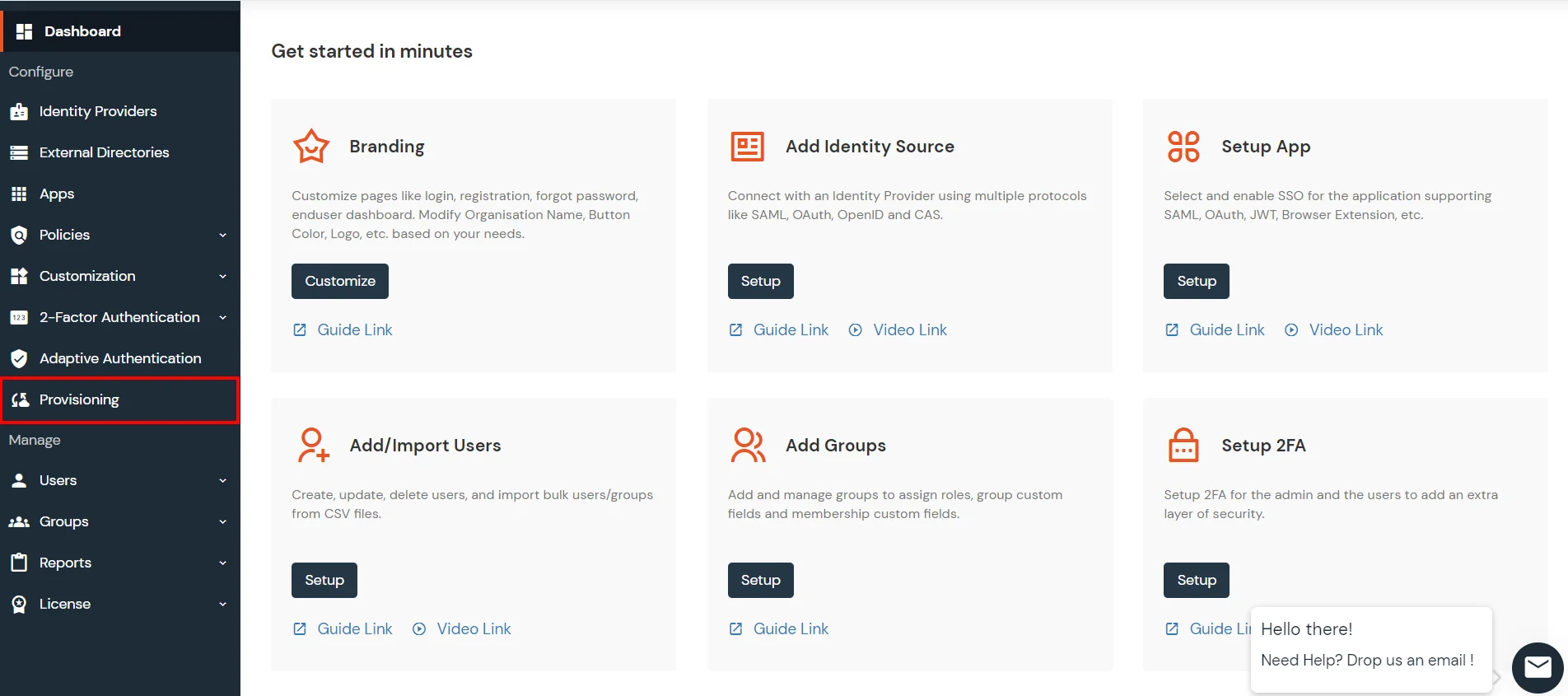
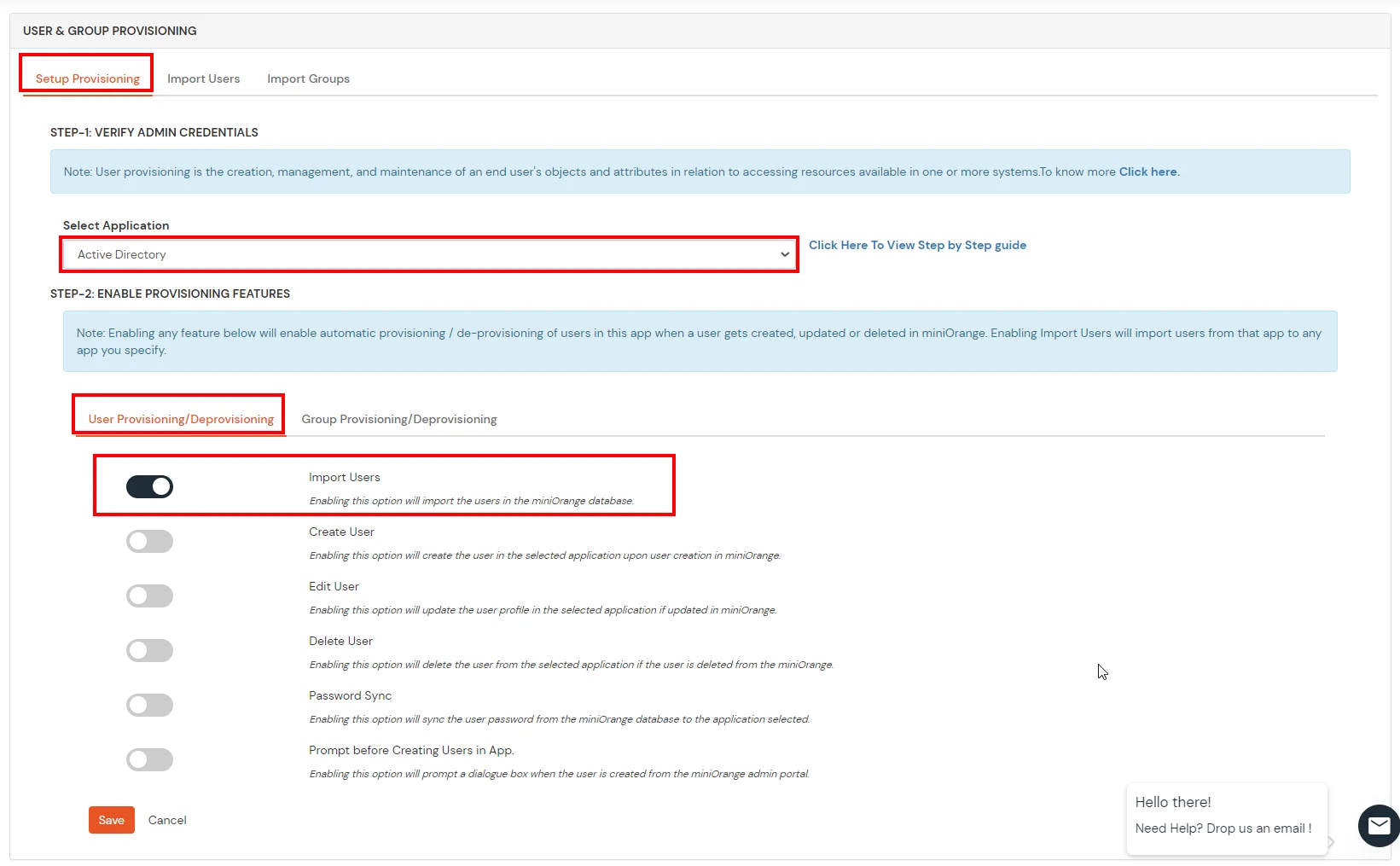
- From the Left-Side menu of the dashboard select Provisioning.
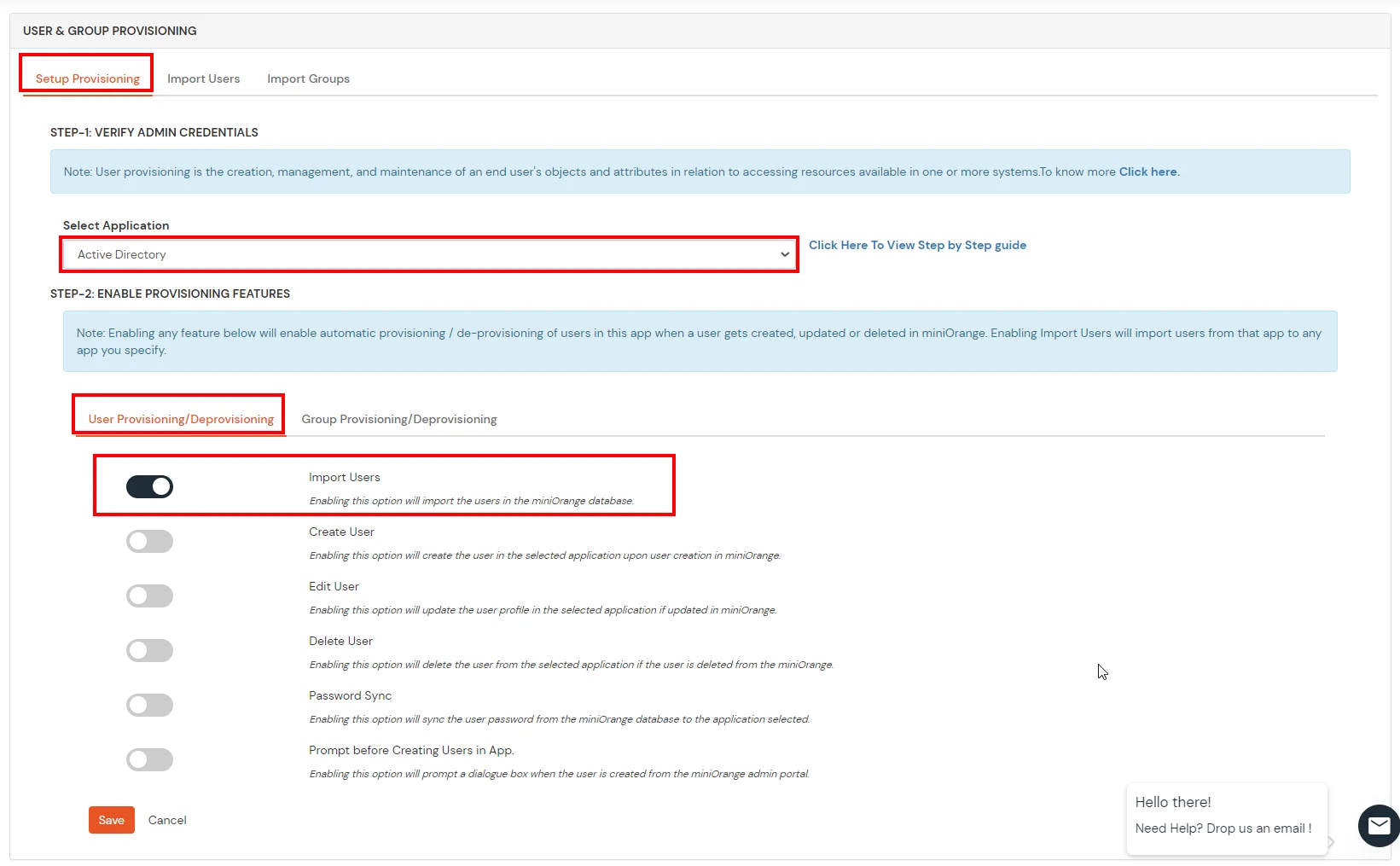
- In Setup Provisioning tab select Active Directory in the Select Application drop-down.
- Toggle the Import Users tab, click on Save button.
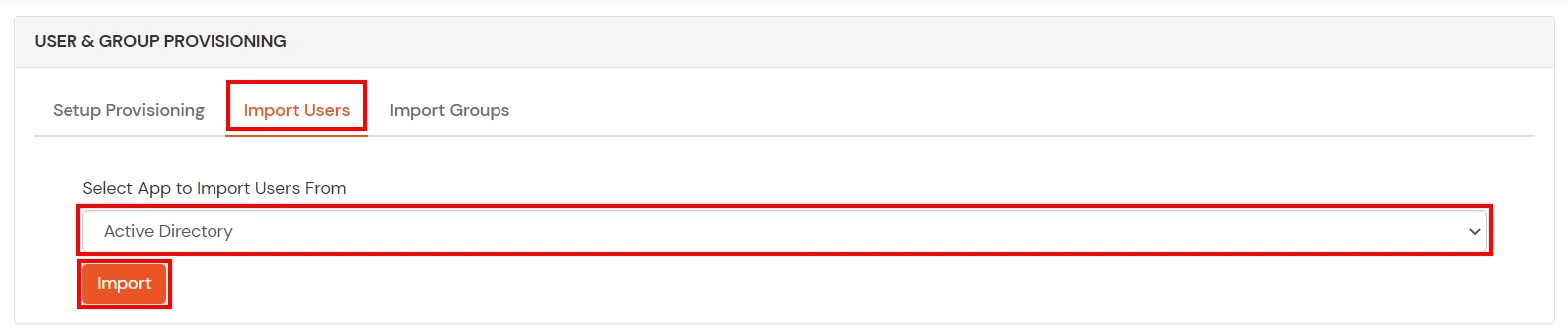
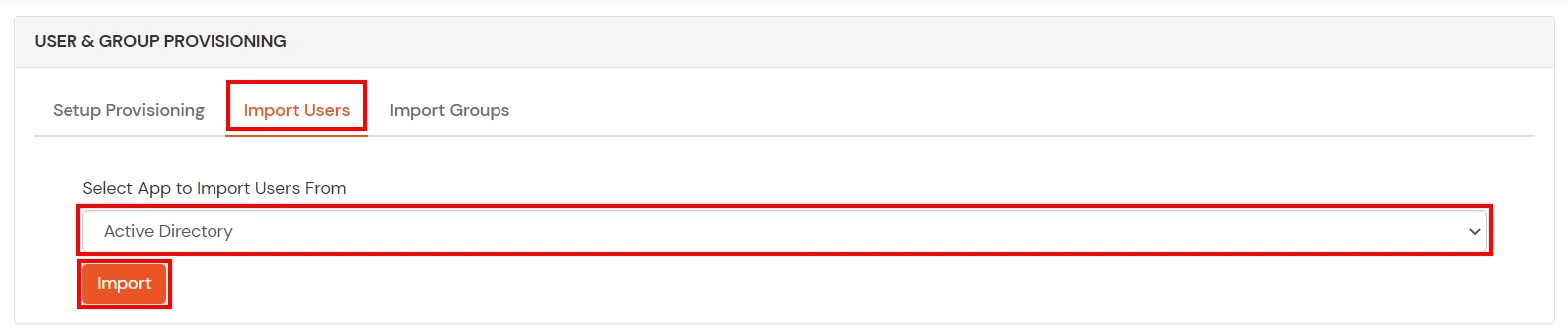
- On the same section, switch to Import Users section.
- Select Active Directory from the dropdown and click on the Import Users tab, to import all the users from Active Directory to miniOrange.
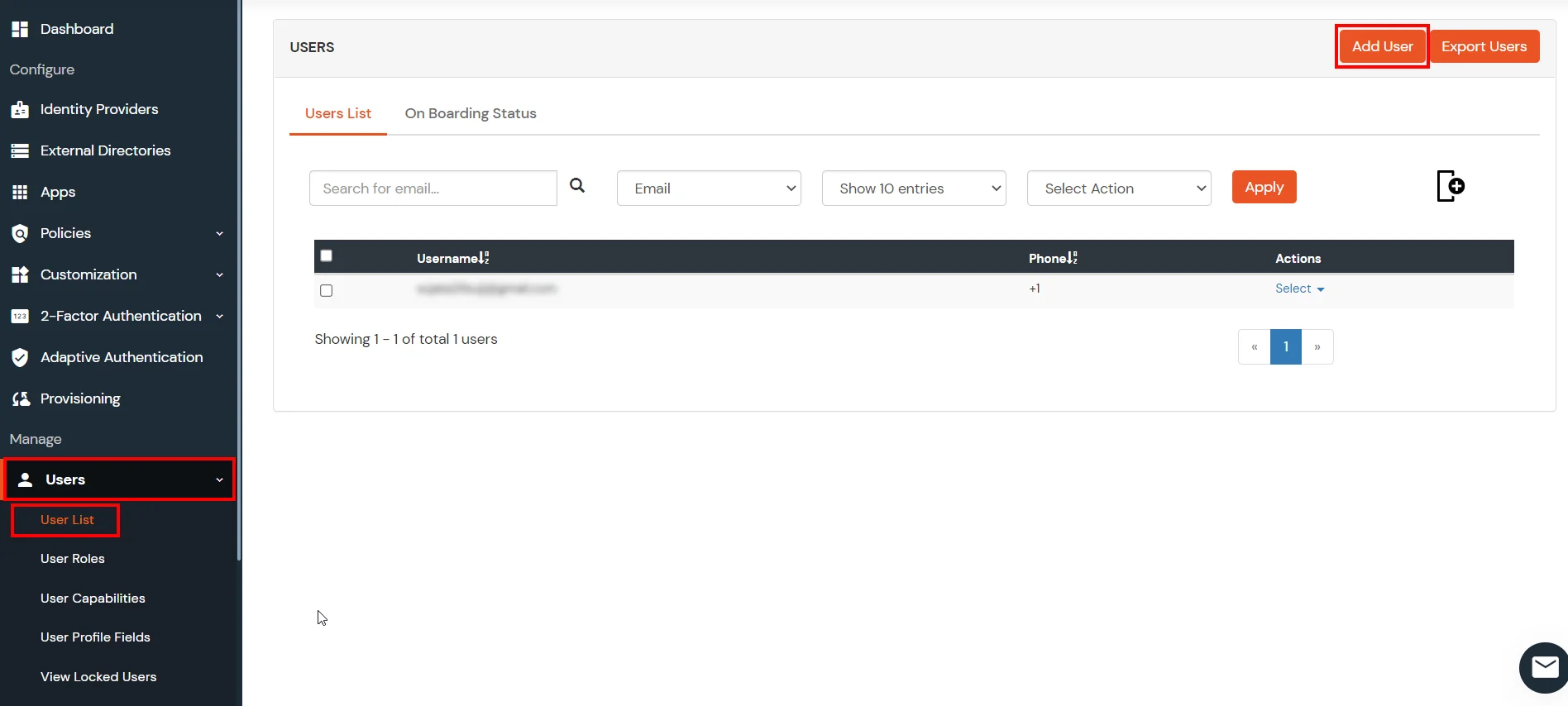
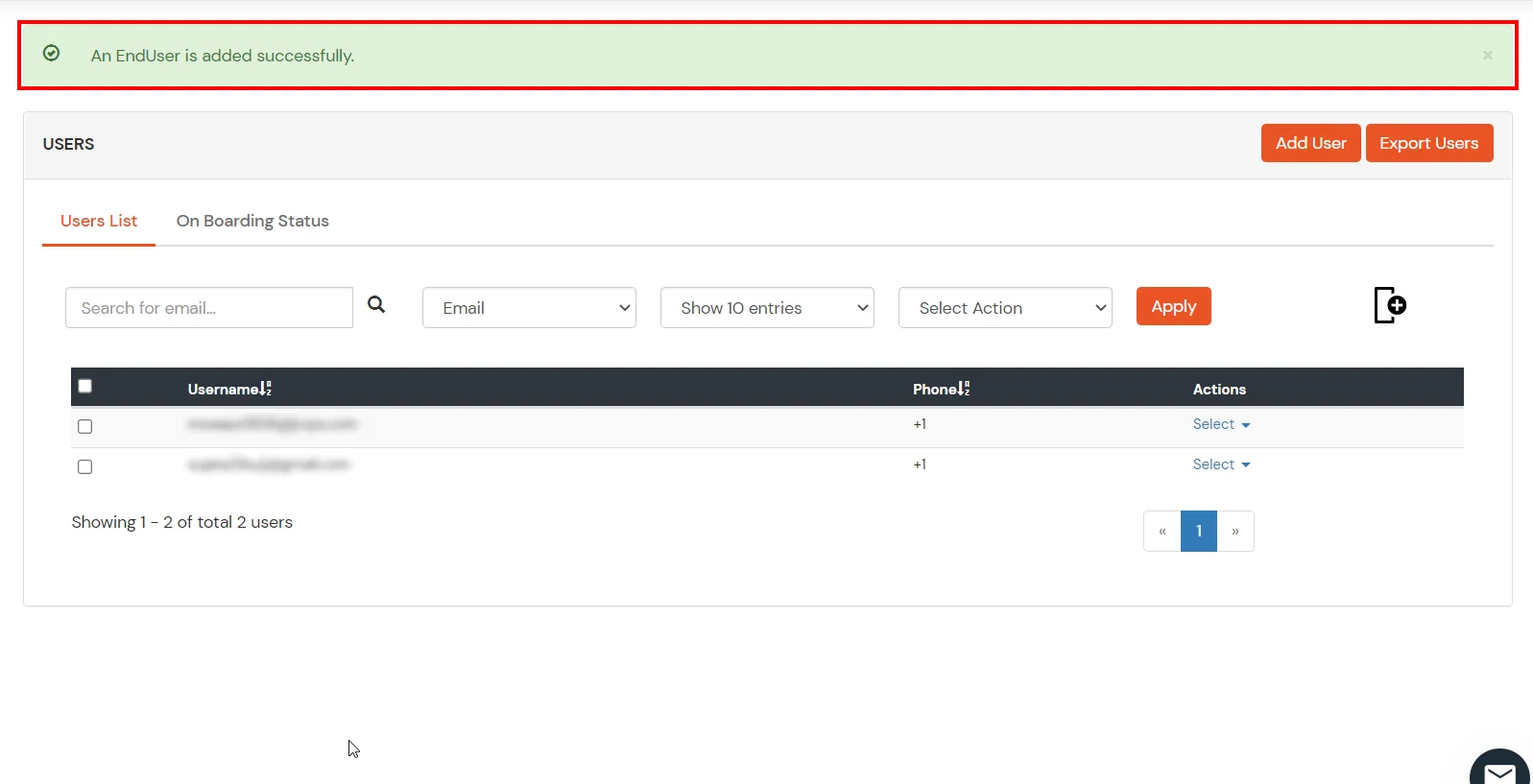
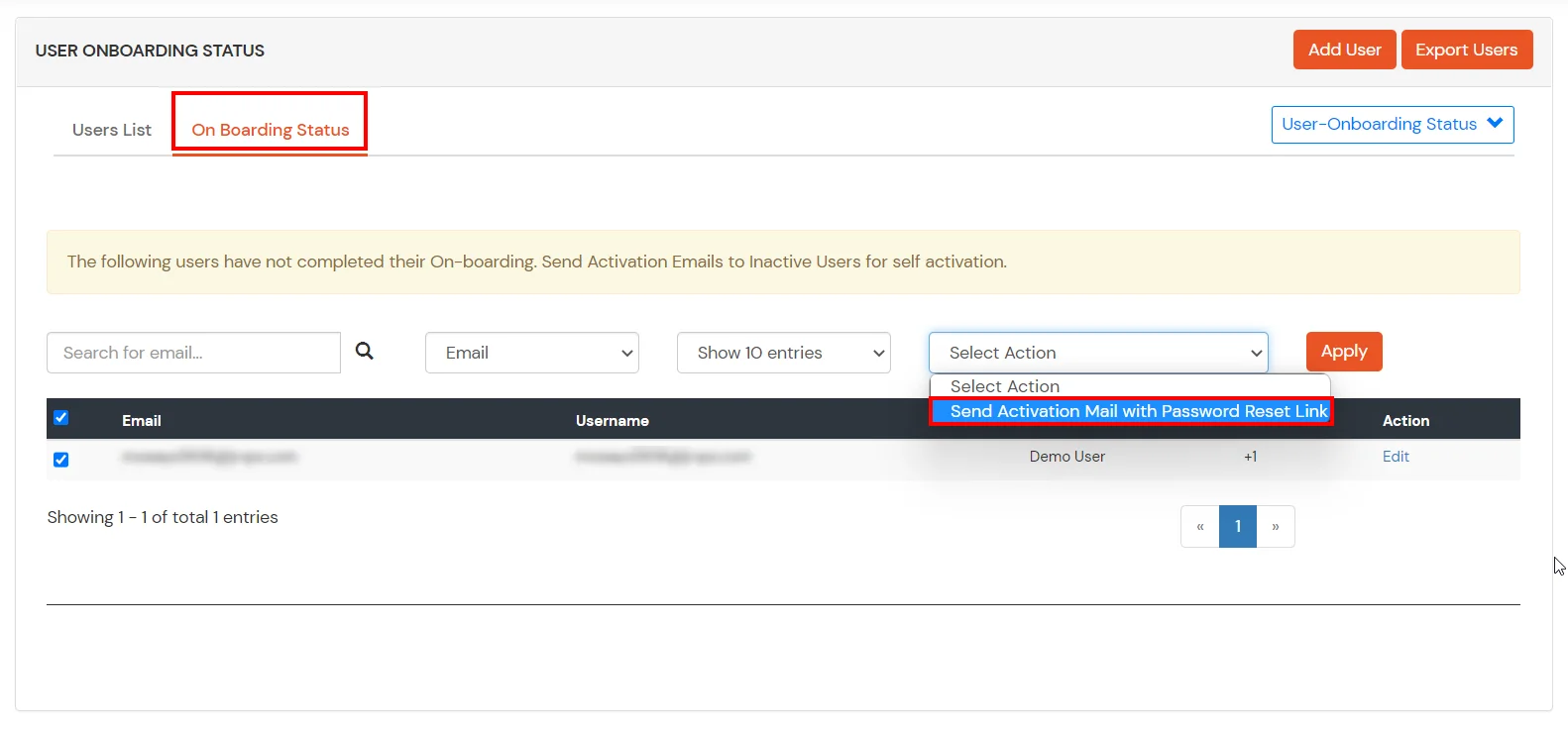
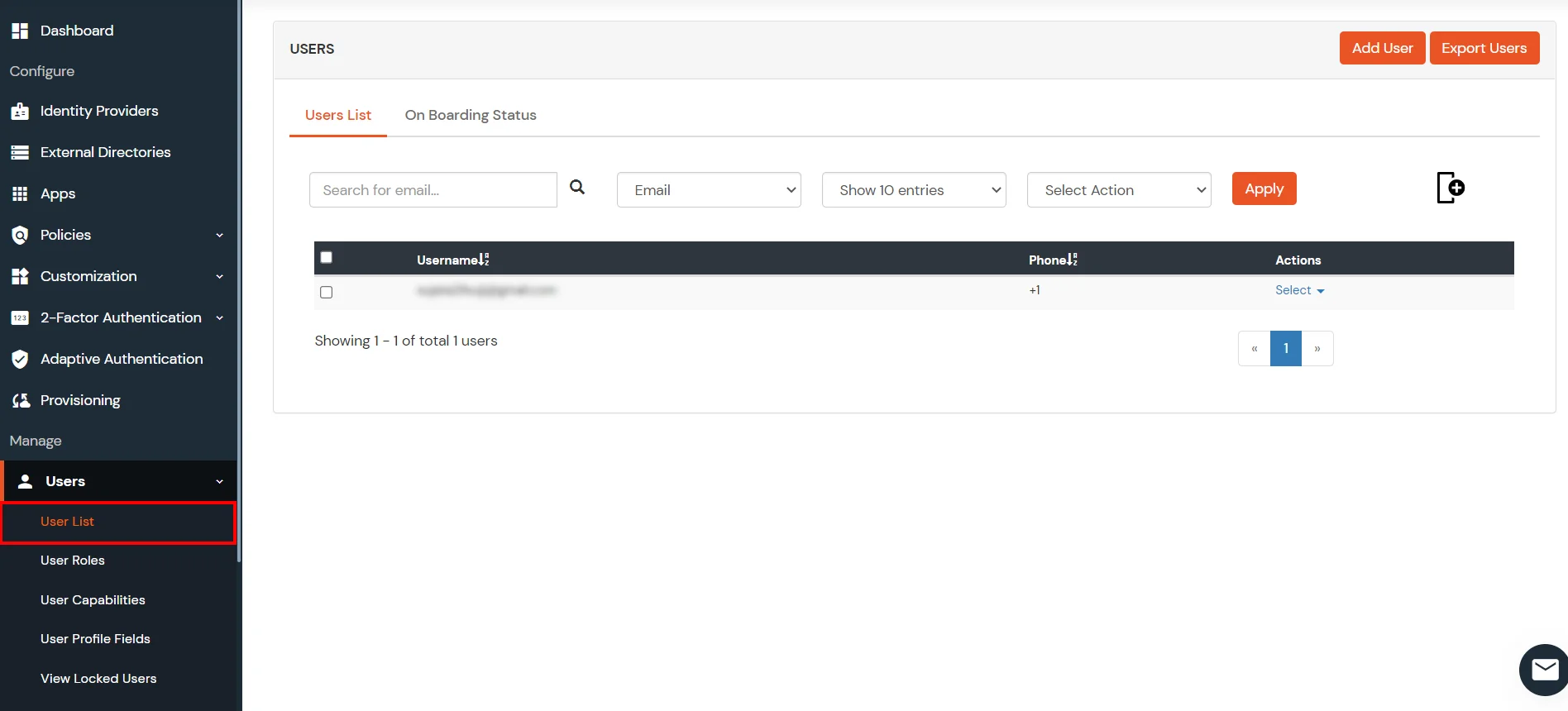
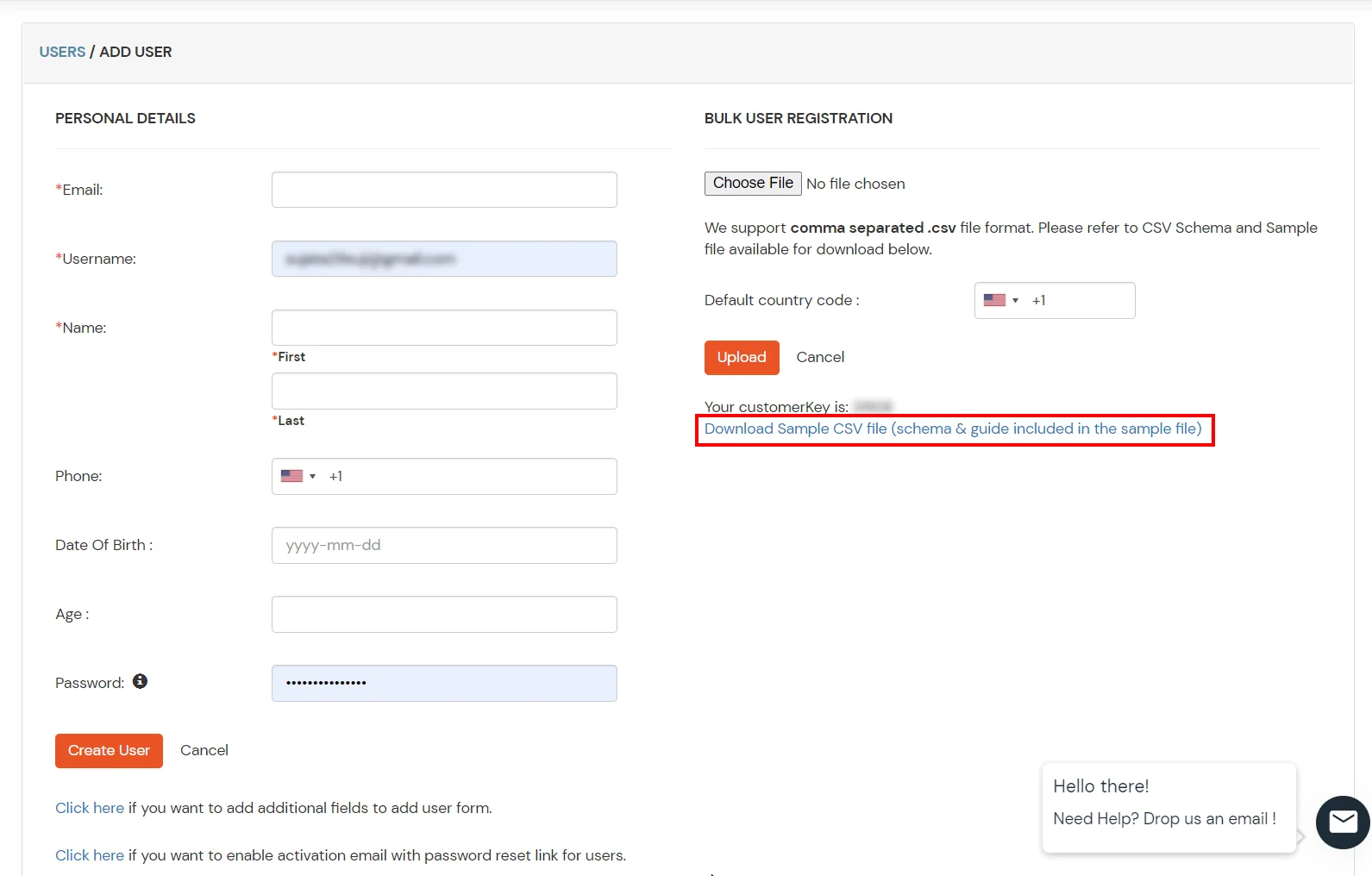
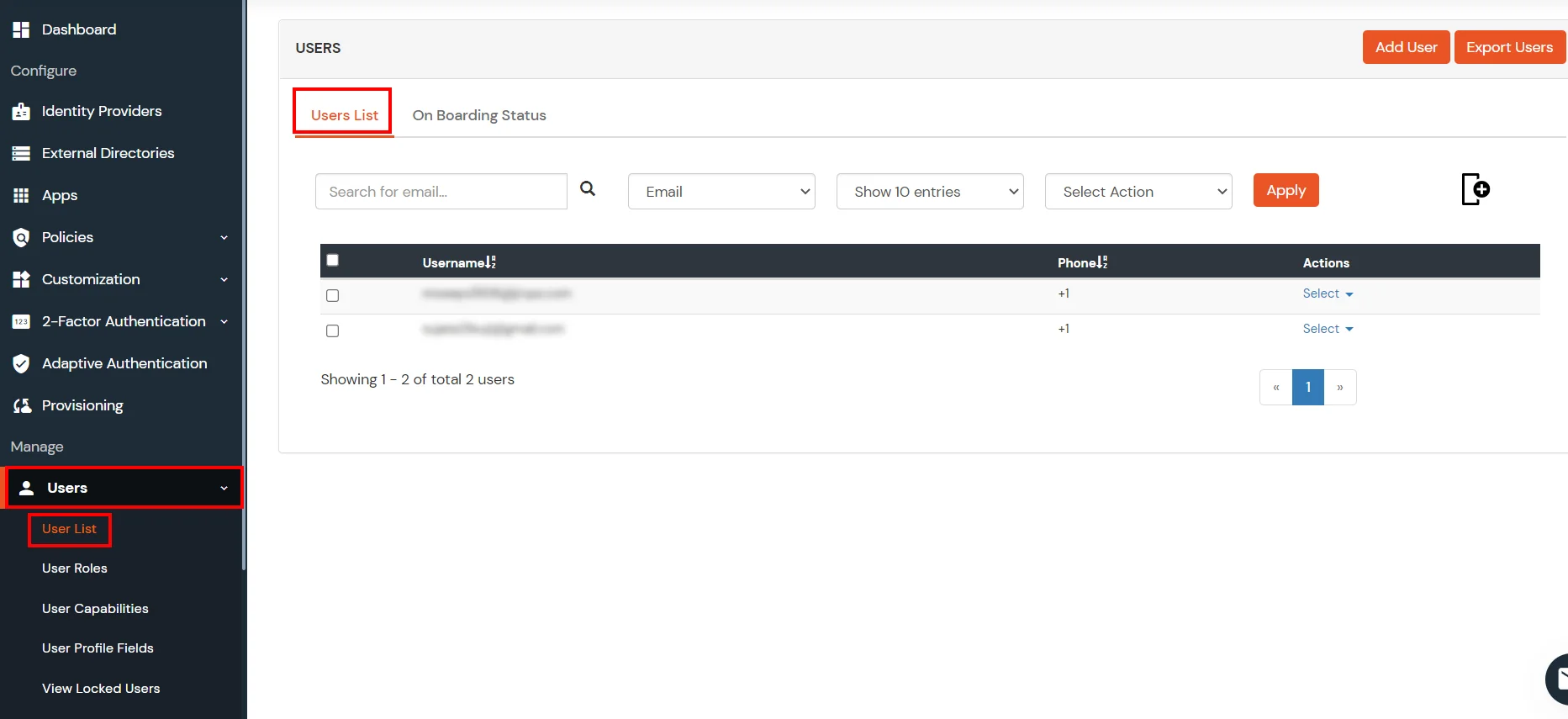
- You can view all the Users you have imports by selecting Users >> User List from Left Panel.
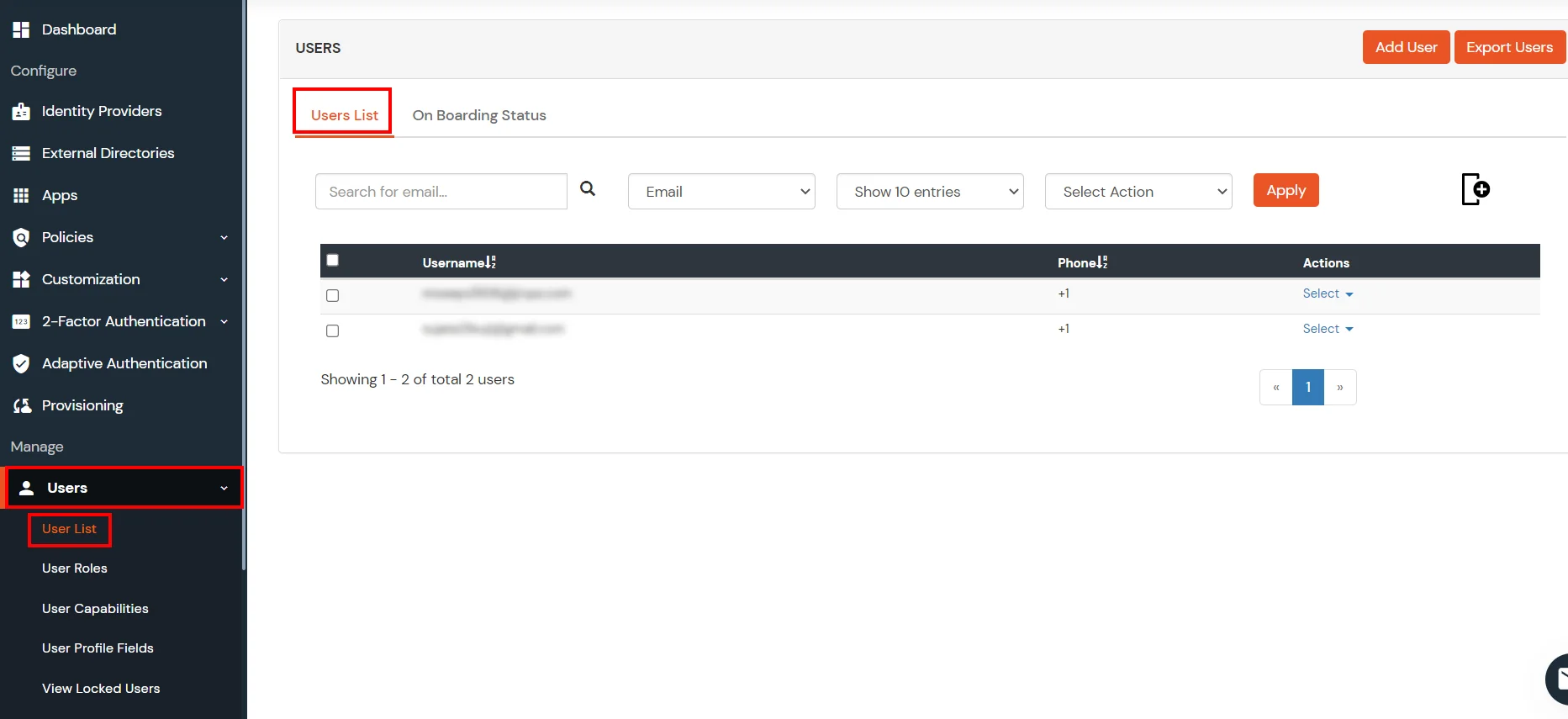
- All the imported users will be auto registered.
- These groups will be helpful in adding multiple 2FA policies on the applications.
miniOrange integrates with various external user sources such as directories, identity providers, and etc.
5. Adaptive Authentication with Salesforce
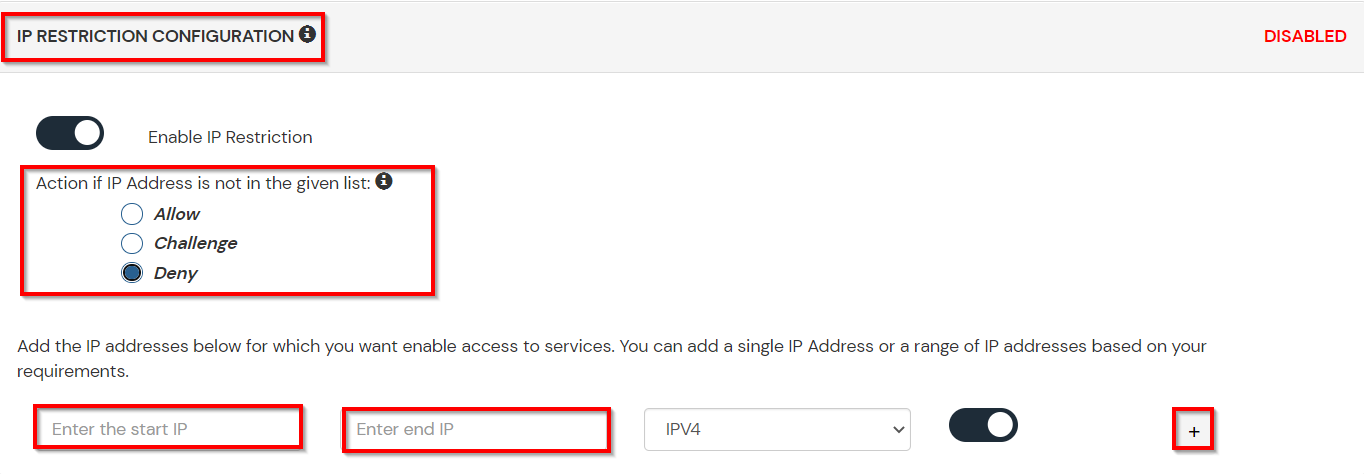
A. Restricting access to Salesforce with IP Blocking
B. Adaptive Authentication with Limiting number of devices.
Using Adaptive Authentication you can also restrict the number of devices the end user can access the Services on. You can allow end users to access services on a fixed no. of devices. The end users will be able to access services provided by us on this fixed no. of devices.
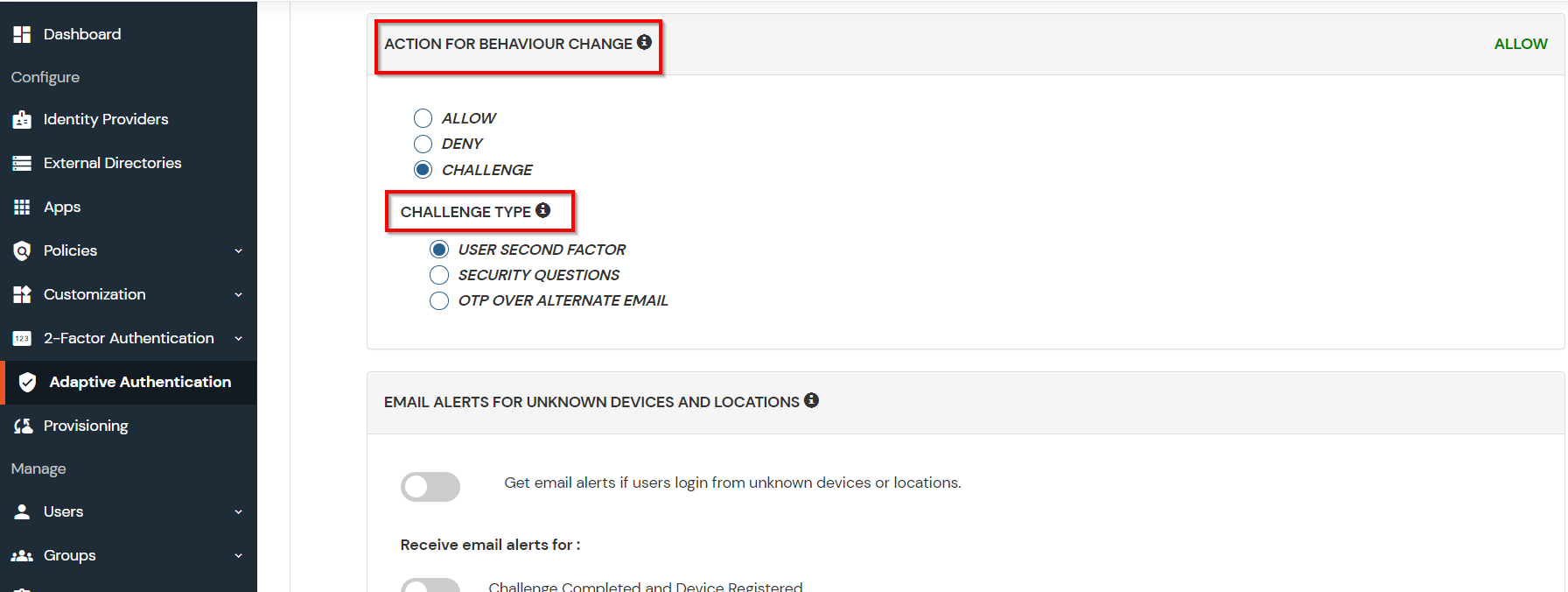
You can configure Adaptive Authentication with Device Restriction in following way
- Login to Self Service Console >> Adaptive Authentication.
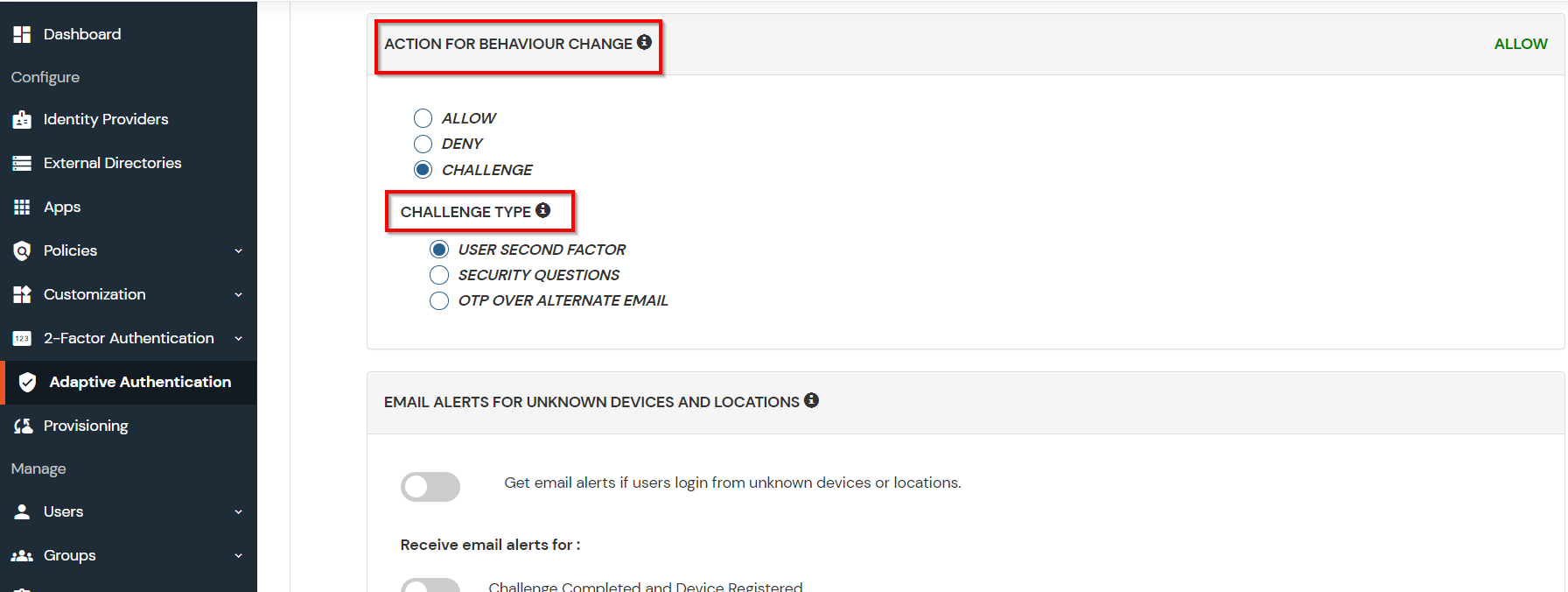
- Add a Policy Name for your Adaptive Authentication Policy.
- Select your Action for behavior Change and Challenge Type for user from the Action for behavior Change Section.
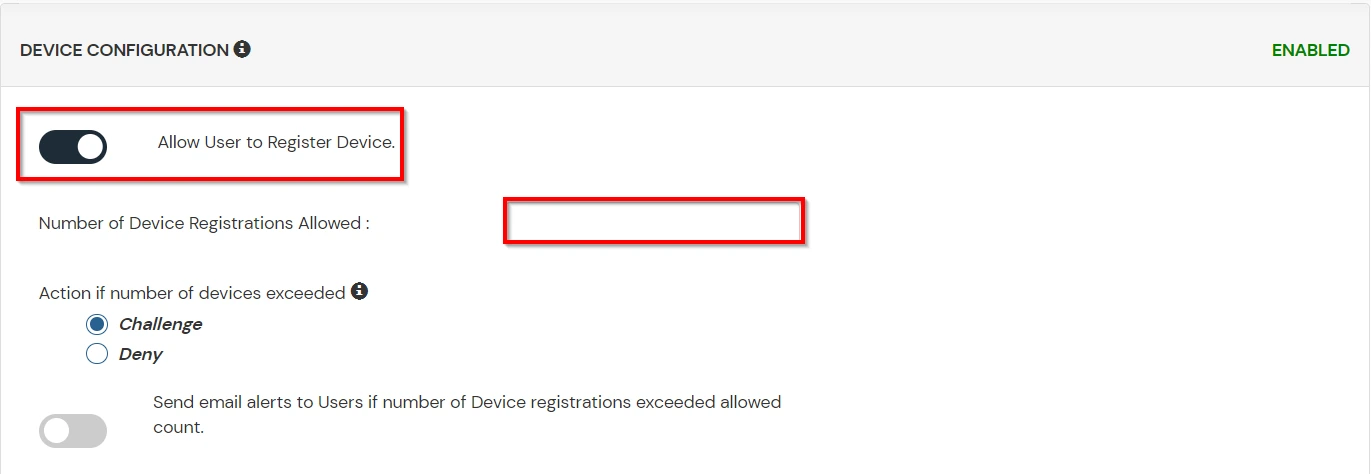
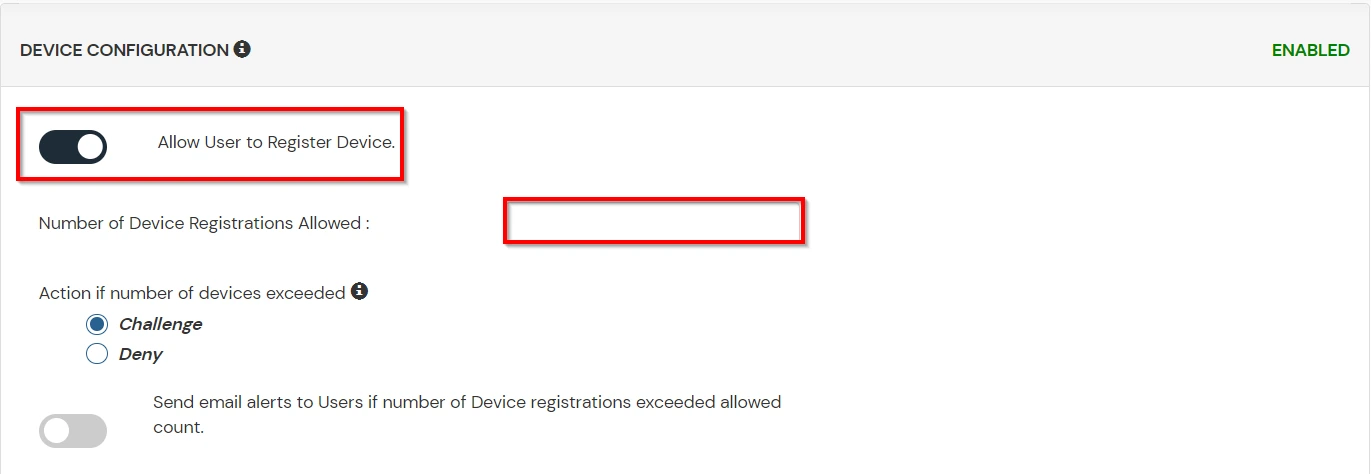
- Scroll down to Device Configuration section and enable Allow User to Register Device option to allow users to register their devices.
- Enter the Number of Devices which are allowed to register in field next to Number of Device Registrations Allowed
- Choose Action if number of devices exceeded (This will override your setting for Action for behavior Change.)
- Challenge: The user needs to verify himself using any of the three methods mentioned in table in step 5.1
- Deny : Deny users access to the system
- Enable option Send email alerts to Users if number of Device registrations exceeded allowed count if you want to alert the user about no of devices exceeding the limit. Save the configuration.
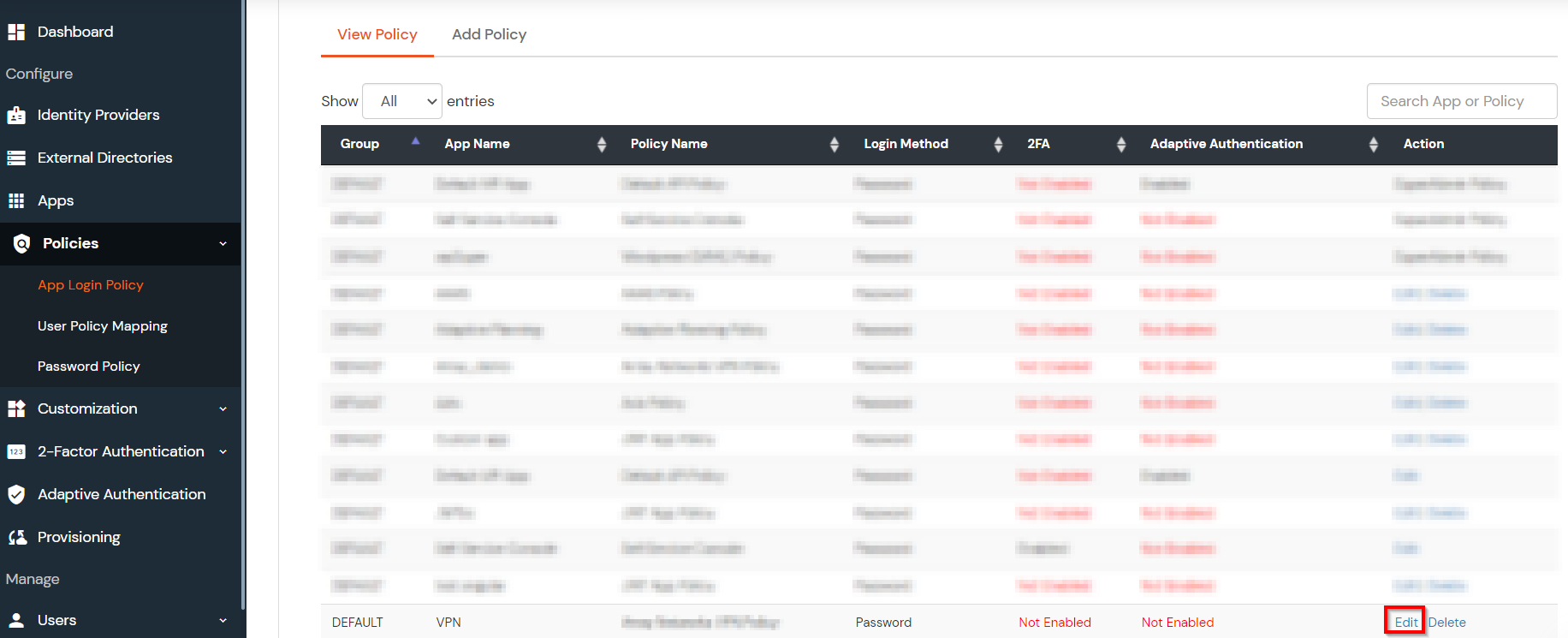
C. Add Adaptive Authentication policy to Salesforce.
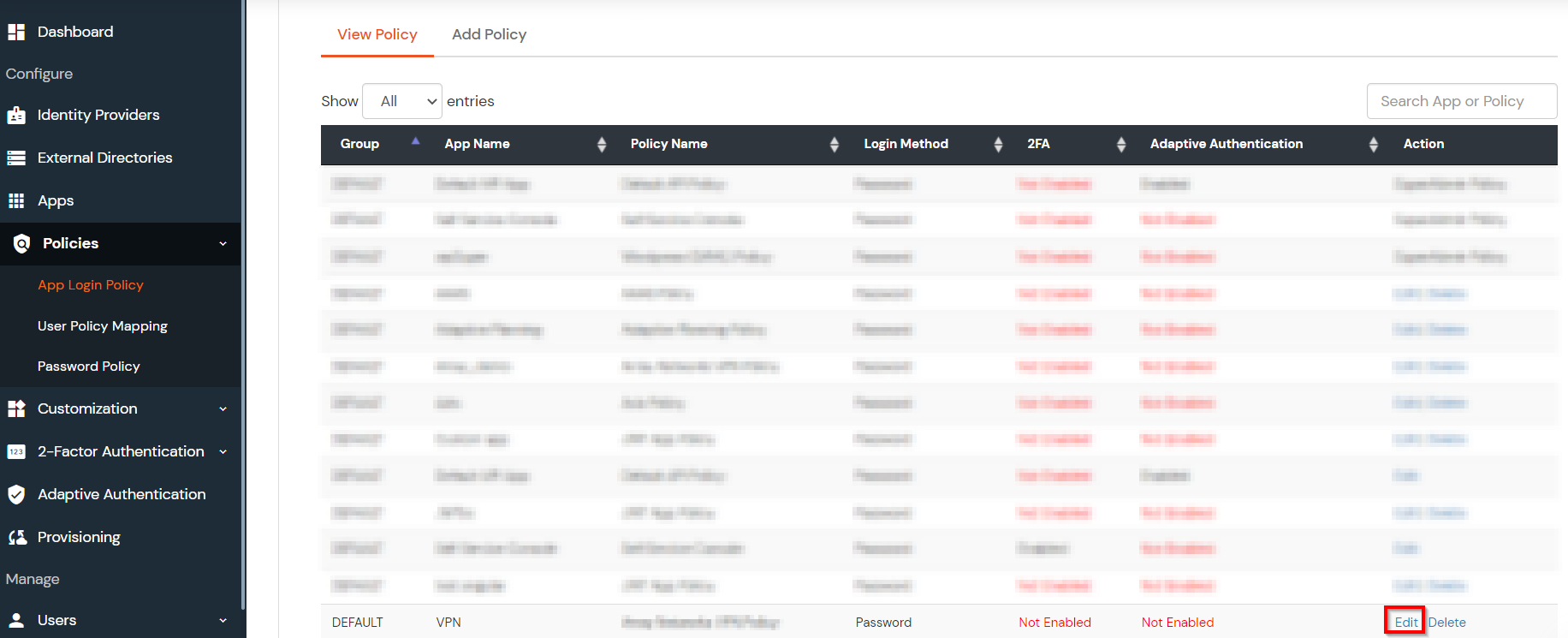
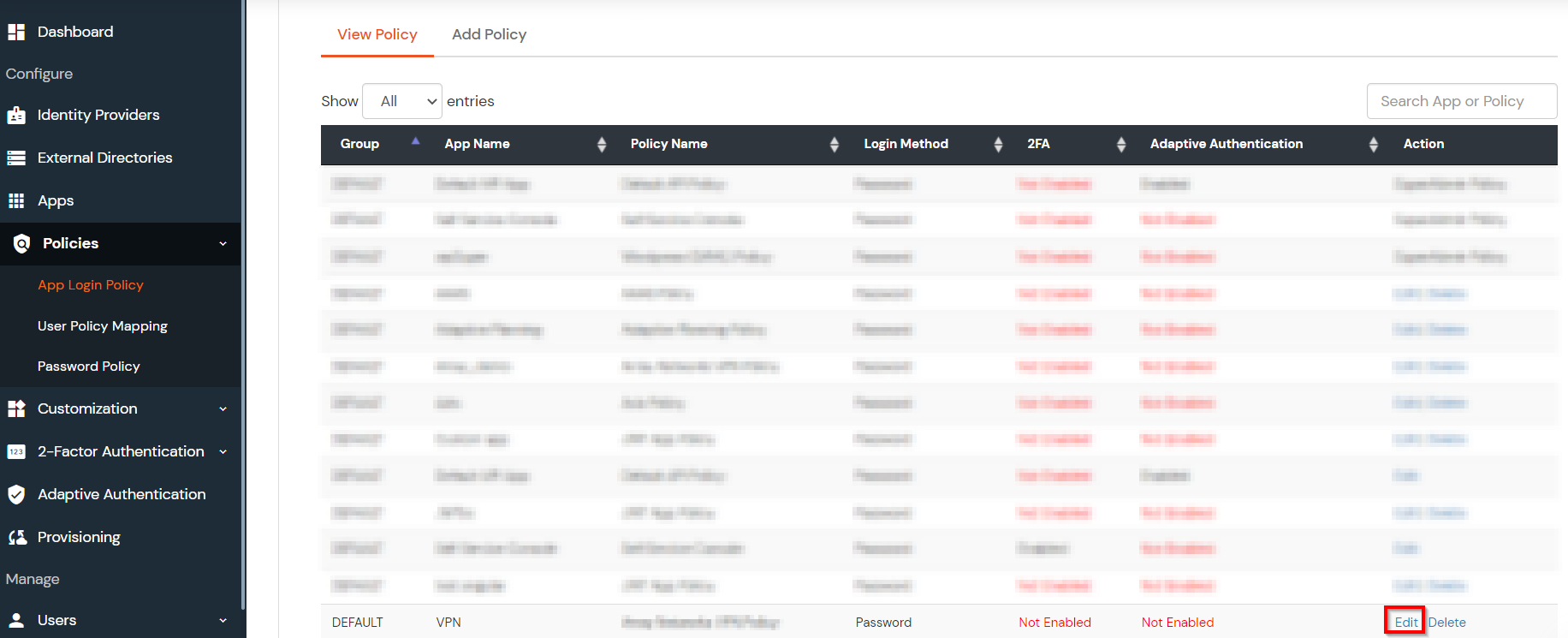
- Login to Self Service Console >> Policies.
- Click on Edit option for predefined app policy.
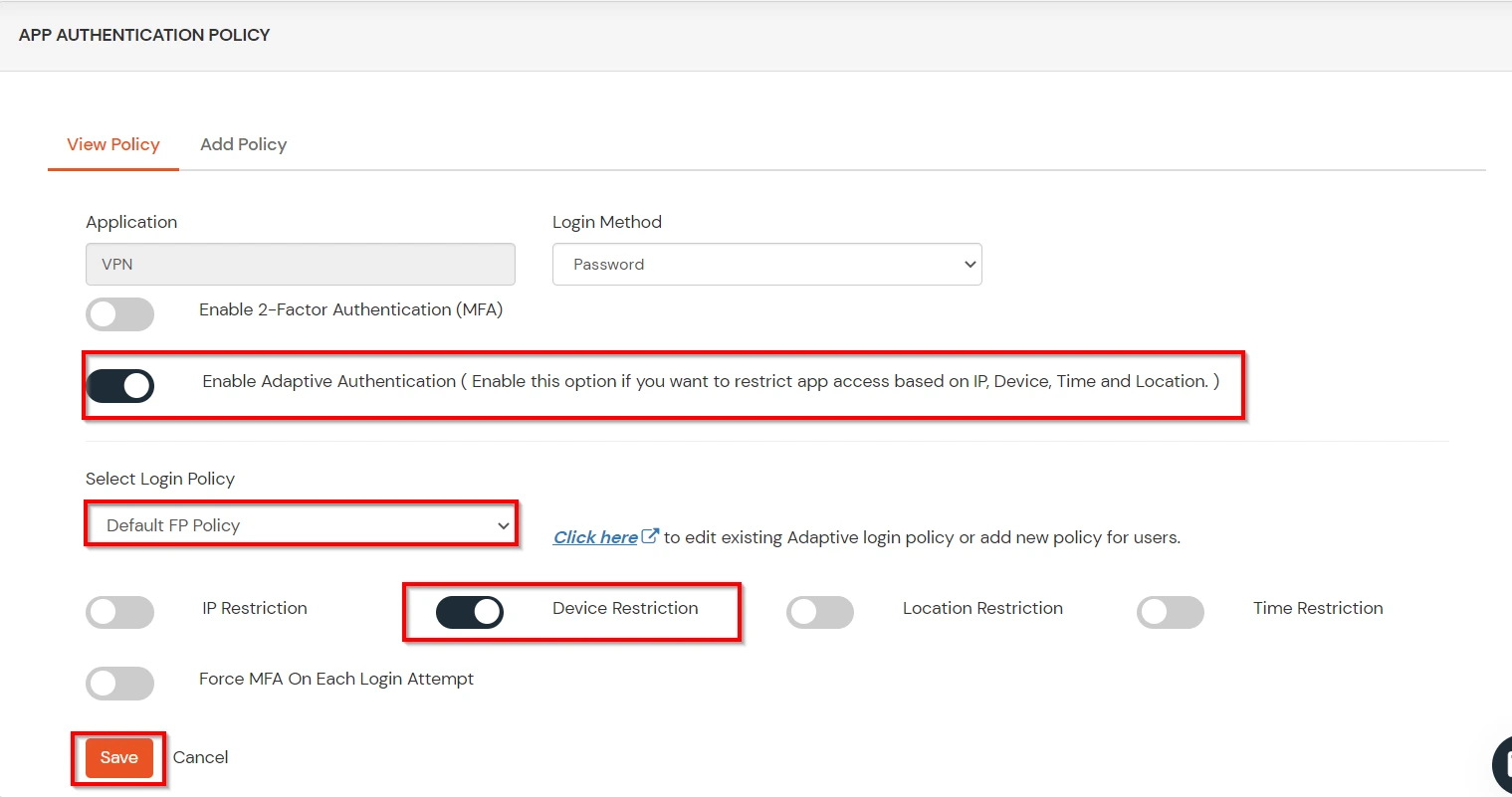
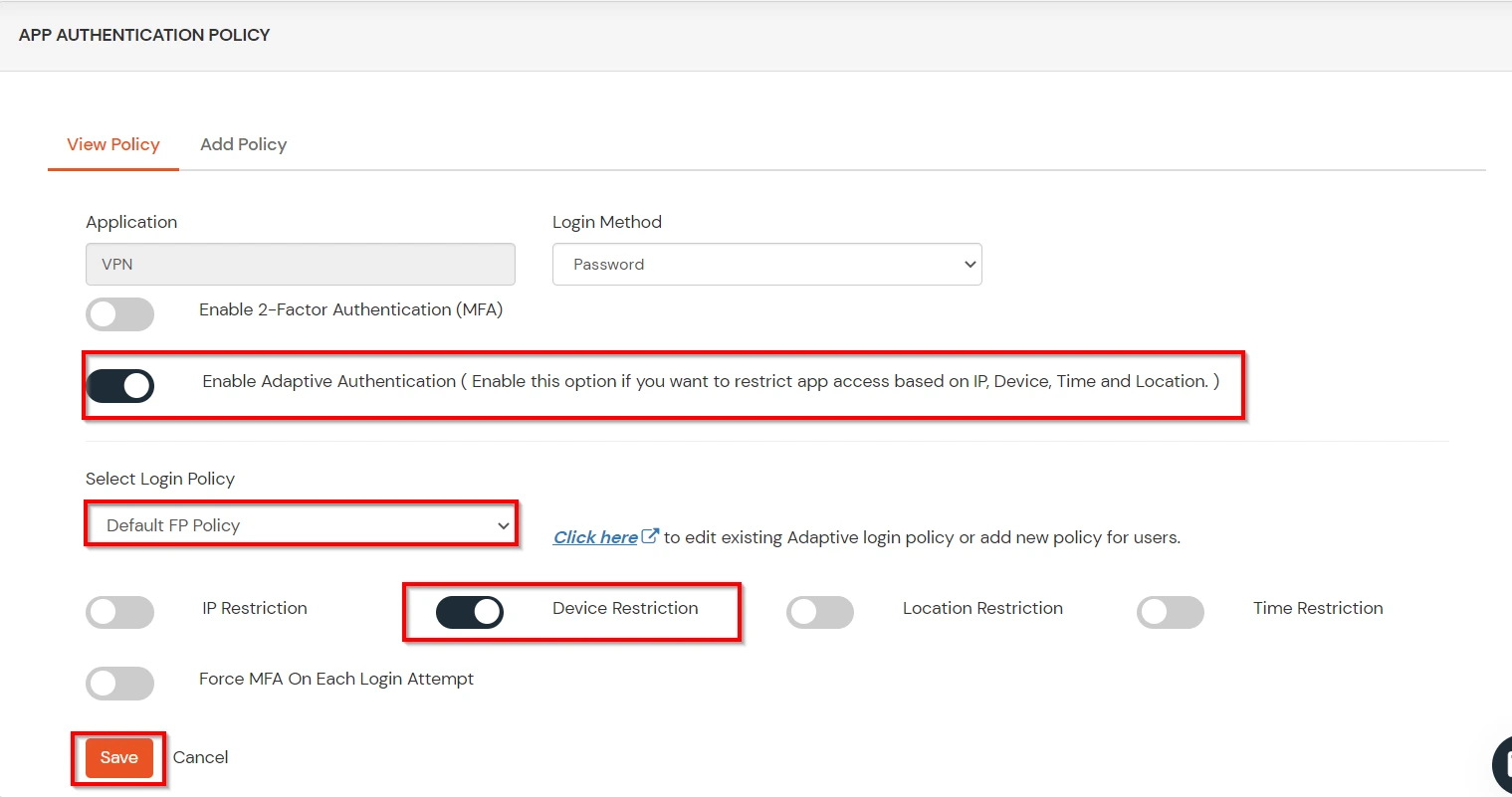
- Set your application name in the Application and select password as Login Method.
- Enable Adaptive Authentication on Policy page and select the required restriction method as an option.
- From Select Login Policy dropdown select the policy we created in last step and click on save.
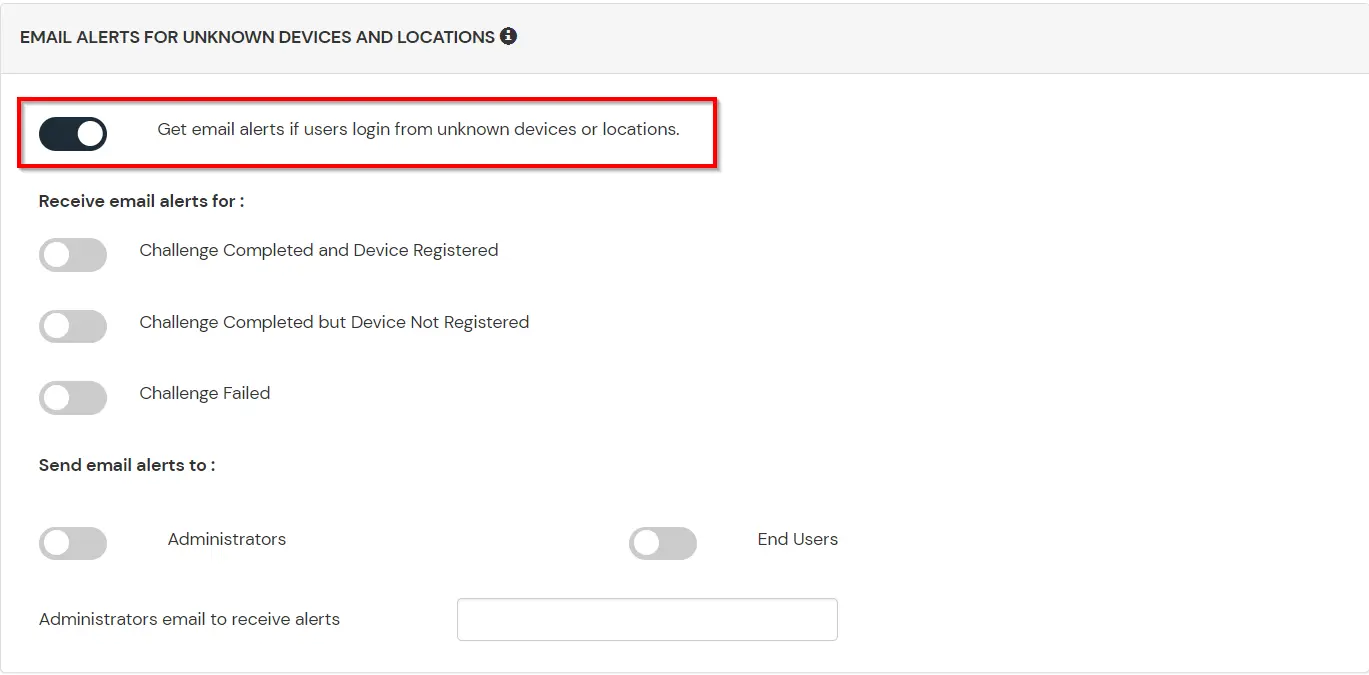
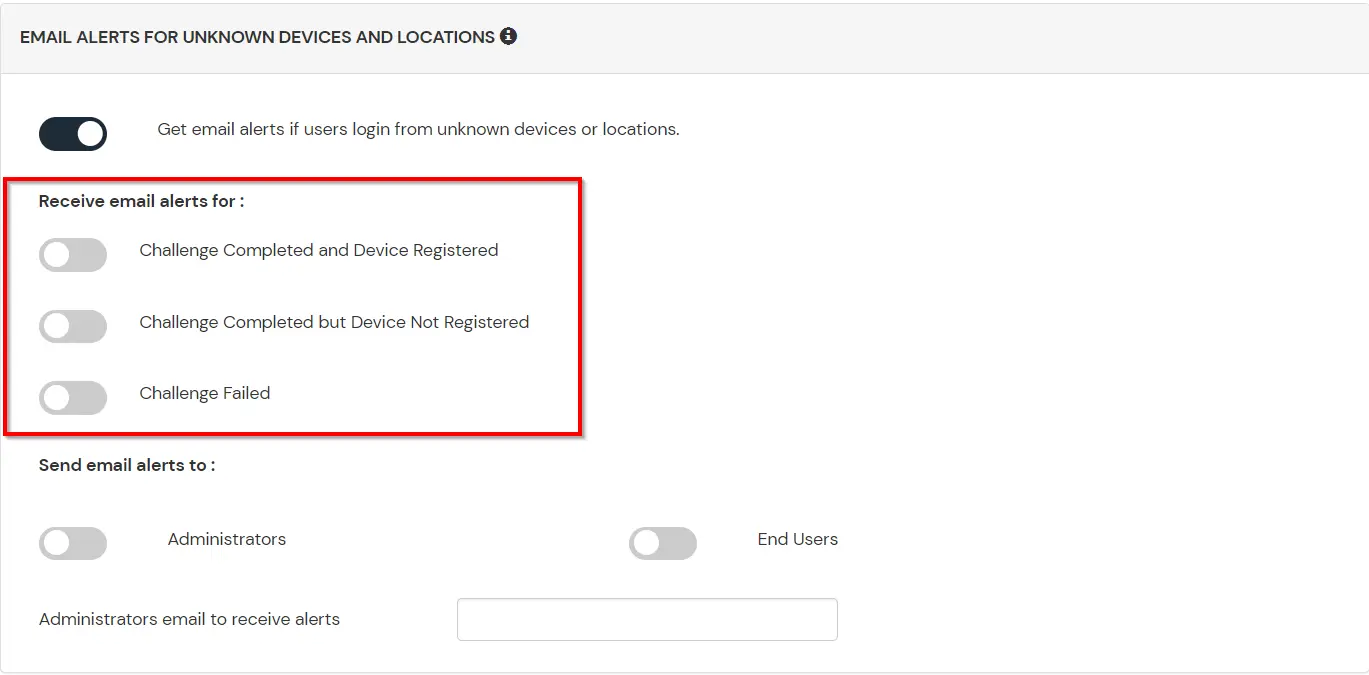
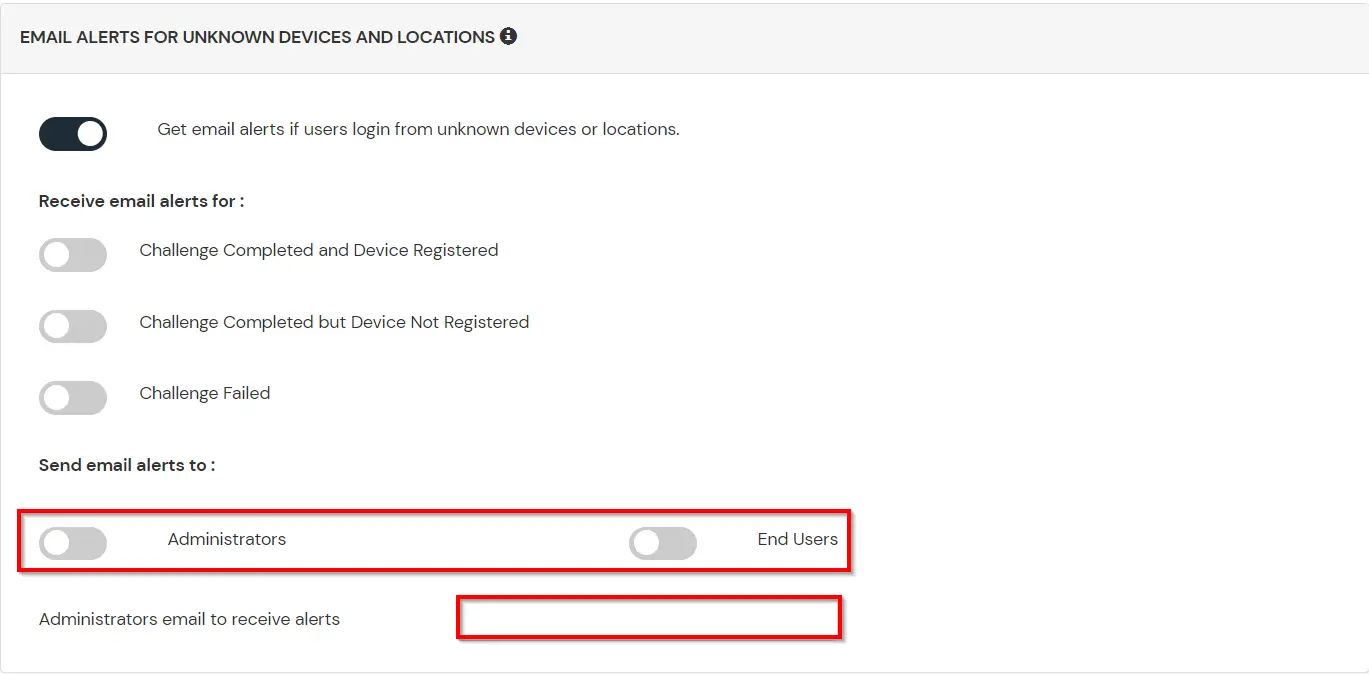
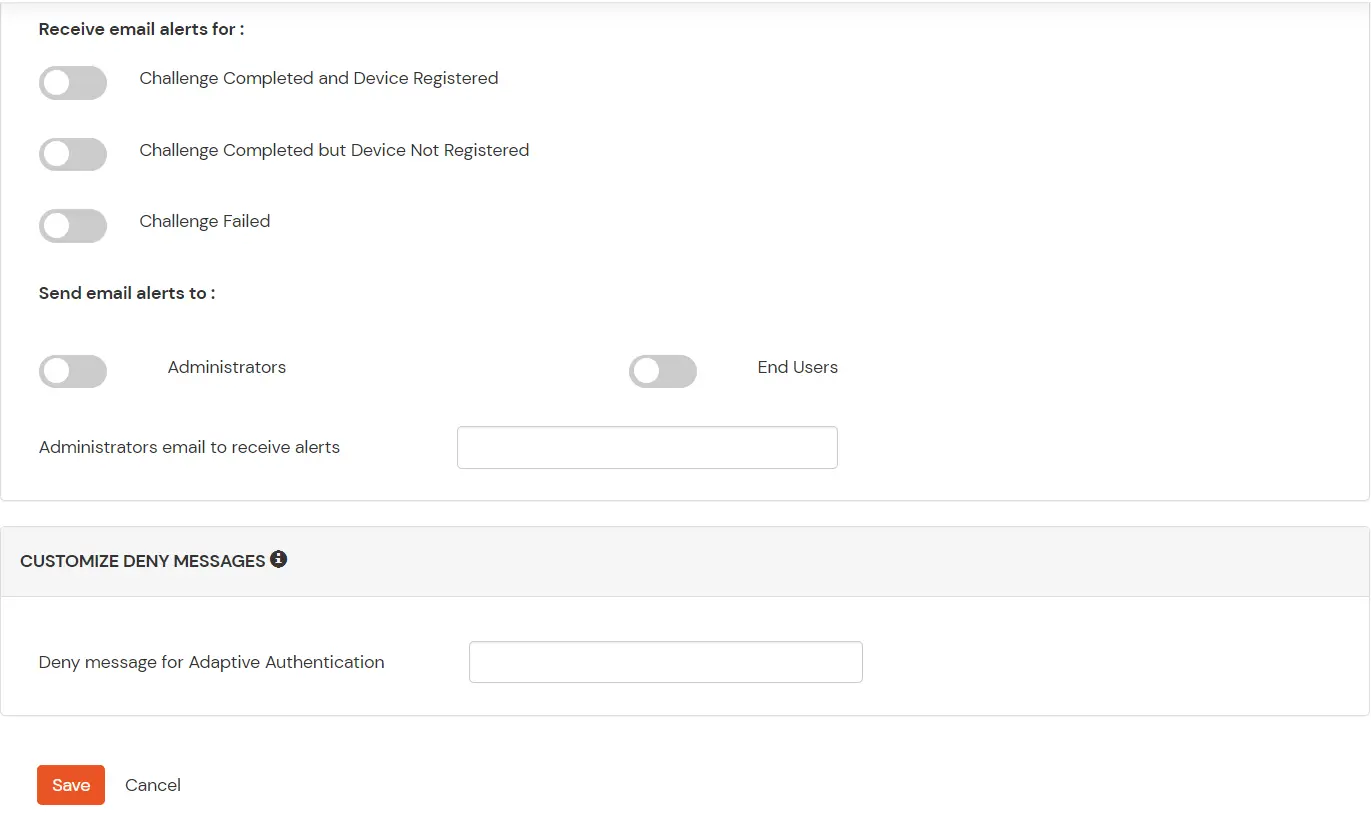
D.Notification and Alert Message.
How to add a trusted Device
- When End-user log in to the self service console after the policy for device restriction is on, he is provided the option to add the current device as a trusted device.
Troubleshooting
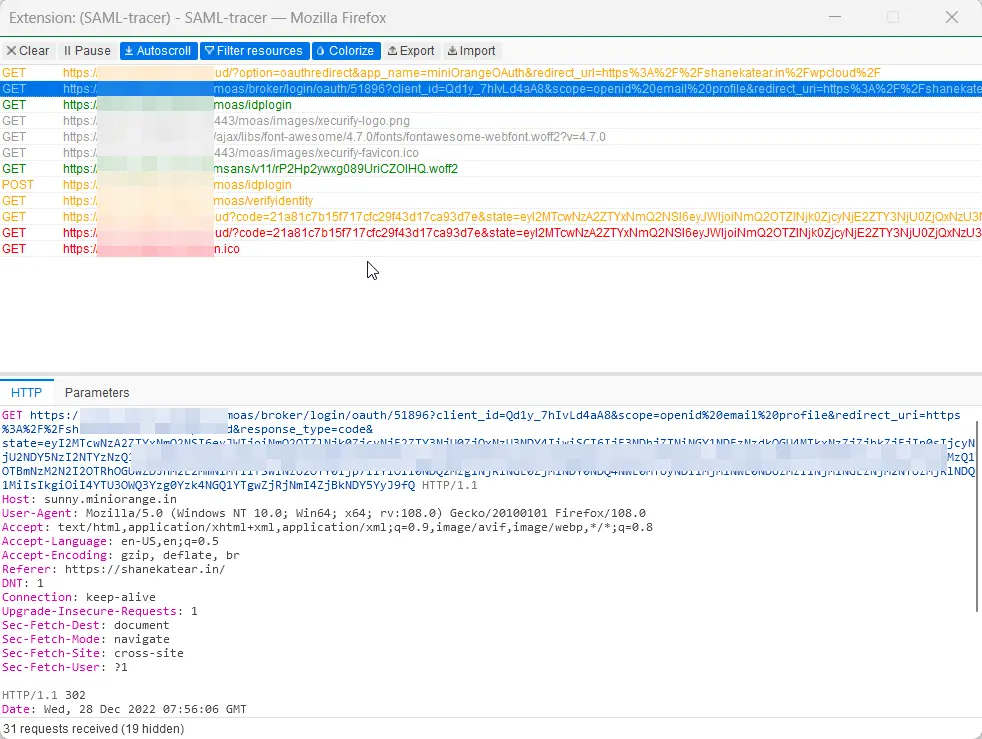
How to identify errors in SAML assertions sent by your IDP?
- Use the SAML Assertion Validator to troubleshoot single sign-on (SSO) login problems and identify errors in SAML assertions sent by your identity provider. Click on this link know more about the error identification in SAML Assertions.
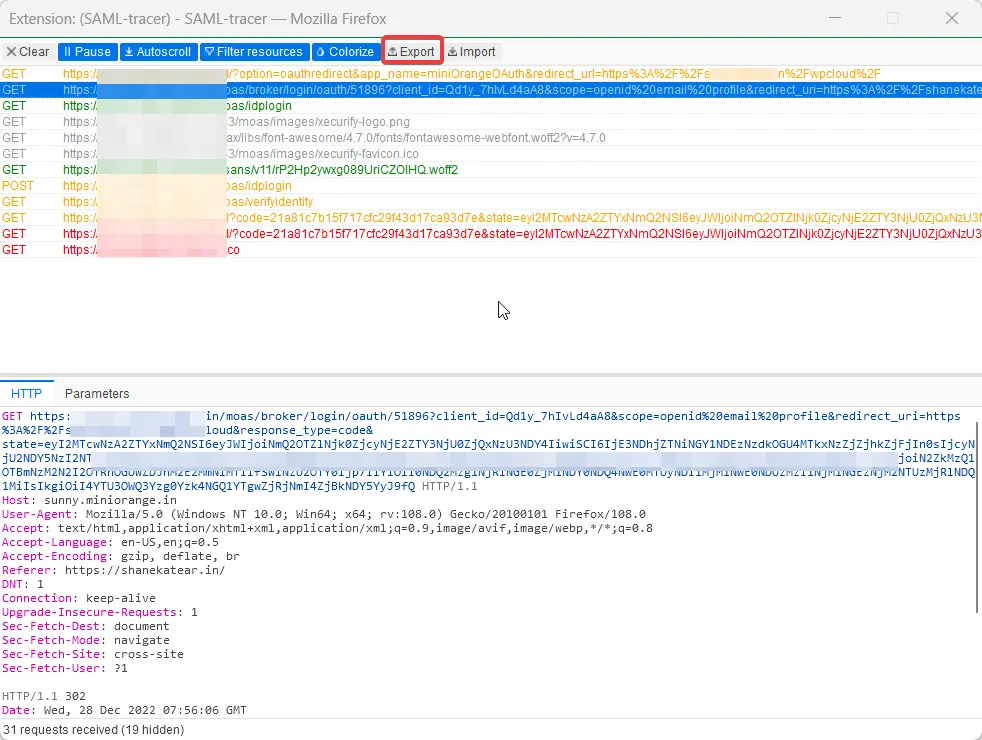
How can I trace and export the SAML tracer logs?
External References